* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download MT311-14
Computer security wikipedia , lookup
Information security wikipedia , lookup
Security-focused operating system wikipedia , lookup
Quantum key distribution wikipedia , lookup
Web of trust wikipedia , lookup
Secret sharing wikipedia , lookup
Mobile security wikipedia , lookup
Unix security wikipedia , lookup
Commitment scheme wikipedia , lookup
Block cipher wikipedia , lookup
Cryptanalysis of the Lorenz cipher wikipedia , lookup
Cryptographic hash function wikipedia , lookup
Public-key cryptography wikipedia , lookup
Diffie–Hellman key exchange wikipedia , lookup
Post-quantum cryptography wikipedia , lookup
Digital signature wikipedia , lookup
One-time pad wikipedia , lookup
Cryptanalysis wikipedia , lookup
MT311 Java Application
Development and Programming
Languages
Li Tak Sing (李德成)
Security
For Java applications, there are two main areas
of security issues:
1 system security
2 information security.
System security
System security refers to the safety and
stability of the computing environment. The
safety and stability can be breached in a
number of ways.
When a malicious application (such as a
virus) executes itself, it can cause damage to
the system — for example, by deleting some
critical files and rendering the computer
inoperable.
Information security
Or, the malicious application can intentionally
or unintentionally consume too many
resources, such as computing time, disk
space, or network bandwidth, thereby
causing the system to perform improperly.
Information security
Information security, however, refers to the
secrecy and integrity of data. For example,
when you send an email, how do you ensure
that only the targeted recipients can read the
message? When you receive an email, how
do you ensure that the message has not
been tampered with and that it is from the
supposed sender?
System security
In the security policy model, resources can
be granted or denied different types of
access independently. For example, a file
can be a resource, and the read action can
be differentiated from the write action. So,
you can easily grant read-only access to a
particular file. You can do the same with
objects, allowing you to create security
policies for runtime objects as well.
System security
Java makes things even more interesting by
allowing different policies to apply to different
applications, or to different invocations of the
same application.
Security policy
As you know by now, applets are small
applications that can be embedded in
webpages. When Java was first introduced,
applets were sensational because they
provided a cross-platform solution for making
a webpage more interesting. To safeguard
users from malicious applets, applets are run
in a sandbox, which imposes rather stringent
restrictions on what the applets can do.
Applet security
If you run an applet through a browser and
then the applet tries to read a local file, an
error message would appear.
You can try the following link:
http://plbpc001.ouhk.edu.hk/~mt311f/2005mt311f/lecture/test/build/classes/test.html
Allowing an applet to access a
local file
To remove the restriction, we need to specify a
different policy. The format of the policy file is
quite simple, and you can create one using a
text editor. For example, below is a simple
file that grants rights for applets from
plbpc001.ouhk.edu.hk ‘.java.policy’:
Changing the policy
grant codeBase "http://plbpc001.ouhk.edu.hk/-"
{
permission java.security.AllPermission;
};
You should put this file in the "My Documents"
directory. As this would grant permission to
applets from the host to do everything, you
should remove this file after testing it.
Cryptography
Information security is save guarded by
cryptography.
Cryptography
Cryptography has four main objectives:
–
–
Confidentiality — the information cannot be
understood by anyone for whom it was not
intended.
Integrity — the information cannot be altered in
storage or transit between sender and intended
receiver without the alteration being detected.
Cryptography
–
–
Non-repudiation — the creator/sender of the
information cannot deny at a later stage his or her
intentions in the creation or transmission of the
information.
Authentication — the sender and receiver can
confirm each other’s identity and the
origin/destination of the information.
Secret Key method
In the secret key method, the sender and the
receiver share the same secret key. Then,
the sender first encrypts the message with
the key and sends the encrypted message to
the receiver who decrypts the message with
the same key.
Secret key
key
message
send over an
unsafe channel
encrypted
message
key
encrypted
message
message
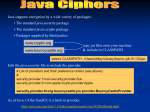
Java secret key APIs
Java’s cryptographic APIs are defined in the
java.security and javax.crypto packages. For
a basic encryption, we need a secret key and
a cryptographic algorithm. The Java classes
for those are:
–
–
SecretKey — this class encapsulates the secret
key for use in encryption and decryption
Cipher — this class provides cryptographic APIs
for encryption and decryption.
Creating a secret key
The following code would create a secret key:
// the key itself as a byte array
byte[] key = new byte[] {'a', 'b', 'c', 'd', 'e', 'f', 'g', 'h'};
// create a KeySpec specifically for DES for our key
DESKeySpec spec = new DESKeySpec(key);
// retrieve a DES SecretKeyFactory
SecretKeyFactory factory = SecretKeyFactory.getInstance("DES");
// generate the actual SecretKey object
SecretKey secret = factory.generateSecret(spec);
Creating a cipher
To create a DES cipher, you first need to find a DES
algorithm provider using Cipher.getInstance:
Cipher c = Cipher.getInstance("DES");
The same Cipher object can be used for either
encryption or decryption, depending on how you
initialize the object:
– Encryption:
c.init(Cipher.ENCRYPT_MODE, secret);
– Decryption
c.init(Cipher.DECRYPT_MODE, secret);
To encrypt or decrypt a message
Now, with Cipher object, you can encrypt or
decrypt any bytes easily with:
c.update(byte[] buf);
You can invoke update as many times as
necessary to encrypt or decrypt the entire
message. To retrieve the encrypted or
decrypted result, you invoke the doFinal
method:
byte[] inEncrypted = c.doFinal();
Overall algorithm
To create a secret key
To create a cipher
Invoke the update method continuously until
the end of data
Invoke the doFinal method to get the final
result.
Conversion to or from byte[]
You should notice that all the cryptography
APIs work on byte[]. So no method what is
the format of your original message, you
must convert it to byte[].
Conversion to or from byte[]
To convert a String to byte[], you can use the
following method of String:
public byte[] getBytes()
To convert a byte[] to a String, you can use
the following constructor of String:
public String(byte[] bytes)
Encryption
The following method would encrypt a
message:
static byte[] encrypt(String st, Cipher c) {
c.update(st.getBytes());
return c.doFinal();
}
Decryption
The following method would decrypt a
message:
public static String decrypt(byte[] message,
Cipher c) {
c.update(message);
byte[] result=c.doFinal();
return new String(result);
}
Message digest
The above method would only be able to
protect the confidentiality of the message. It
cannot protect the integrity of the message
because the receiver would not know
whether the message has been altered in
any way.
To protect the integrity, we need the message
digest.
Hash function
A message digest, typically of fixed length, is
generated using a special mathematical
transformation called a hash function. A hash
function is basically a transformation that
takes any arbitrary input and produces an
output in a finite space.
Hash function
For message digests, we need a hash
function that has two properties:
–
–
It must be extremely difficult to produce the same
message digest from two different messages, i.e.
the hash must be one-to-one.
It must be extremely difficult to produce the
original message from a given message digest,
i.e. the hash must be irreversible.
Message digest
Message digest alone cannot be used to
protect the integrity of message. This is
because anyone can use the same hash
function to protect a message digest of an
altered message.
So the secret key method must be used
together with the message digest.
Secret key method with message
digest
message digest
message digest
produce
sent over
unsafe
channel
key
compare
key
message
message
encrypted message
encrypted message
Message digest
The creation of a MessageDigest is similar to that of
Cipher, using getInstance:
MessageDigest md =
MessageDigest.getInstance("MD5");
Once you have a MessageDigest object, you can
feed data to it using the update method:
md.update(inbuf);
Finally, you can retrieve the final hash using the
digest method:
md.digest();
Message digest
The following method generate the message
digest of a String:
public static byte[] md(String st) {
MessageDigest md =
MessageDigest.getInstance("MD5");
md.update(st.getBytes());
return md.digest();
}
Compare two byte[]
Since message digests are in the format of
byte[], we need to compare two byte[]'s. you
should use a for loop to compare two byte[]'s.