2-7 The Mathematics Models and an Actual Proof Experiment
... 2 IP traceback 2.1 Functions of IP traceback IP traceback methods are designed to track down the sources of attacks mainly within a single autonomous system (AS). In most cases, however, DDoS attack packets pass across several ASs to reach a victim. Therefore, in addition to performing traceback wi ...
... 2 IP traceback 2.1 Functions of IP traceback IP traceback methods are designed to track down the sources of attacks mainly within a single autonomous system (AS). In most cases, however, DDoS attack packets pass across several ASs to reach a victim. Therefore, in addition to performing traceback wi ...
Elliptic Integrals, Elliptic Functions and Theta Functions Outline
... The first reported study of elliptical integrals was in 1655 when John Wallis began to study the arc length of an ellipse. Both John Wallis (1616-1703) and Isaac Newton (1643-1727) published an infinite series expansion for the arc length of the ellipse. But it was not until the late 1700’s that Legen ...
... The first reported study of elliptical integrals was in 1655 when John Wallis began to study the arc length of an ellipse. Both John Wallis (1616-1703) and Isaac Newton (1643-1727) published an infinite series expansion for the arc length of the ellipse. But it was not until the late 1700’s that Legen ...
Intruders and password protection
... Proactive password checker techniques Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another rep ...
... Proactive password checker techniques Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another rep ...
Datasäkerhet/Data security EDA625 – Lect2 CRYPTOGRAPHY
... to the last block h0 fixed value. Recursive applications of h by hi = h(xi|| hi-1) for i=1..m Finally, hm is the hash result. ...
... to the last block h0 fixed value. Recursive applications of h by hi = h(xi|| hi-1) for i=1..m Finally, hm is the hash result. ...
Public-Key Cryptosystems Based on Hard Problems
... important thing. Later the sender can not deny that the message was sent by him. In addition, the recipient can not modify the message. An electronic message can be signed in the following way. Let's use the same situation as before. 1. First, Bob has to compute his digital signature for the message ...
... important thing. Later the sender can not deny that the message was sent by him. In addition, the recipient can not modify the message. An electronic message can be signed in the following way. Let's use the same situation as before. 1. First, Bob has to compute his digital signature for the message ...
Smooth Tradeoffs between Insert and Query Complexity in
... perturbations Sq + v j hash to, and return the closest point found (see Fig. 2) . The magnitude of the perturbation v j is proportional to 1 − α. While our algorithm is inspired by [Pan], our analysis is fundamentally different. In [Pan] correctness of hashing schemes is argued using an entropy bas ...
... perturbations Sq + v j hash to, and return the closest point found (see Fig. 2) . The magnitude of the perturbation v j is proportional to 1 − α. While our algorithm is inspired by [Pan], our analysis is fundamentally different. In [Pan] correctness of hashing schemes is argued using an entropy bas ...
Cryptanalysis of Stream Cipher
... larger state: 5 x 128 bits but simpler operation: 1 AES round still easy to analyze create stream cipher from MAC ...
... larger state: 5 x 128 bits but simpler operation: 1 AES round still easy to analyze create stream cipher from MAC ...
Crawling the Web Web Crawling
... – while crawling versus for search results – crawling larger problem – search results demand faster results • Duplicates versus near duplicates ...
... – while crawling versus for search results – crawling larger problem – search results demand faster results • Duplicates versus near duplicates ...
Longest Common Substring with Approximately k Mismatches
... is not robust. Consider, for example, two pairs of strings: an , an−1 b and a(n−1)/2 ba(n−1)/2 , an−1 b. (Assume for simplicity that n − 1 ≥ 2 is even.) The longest common substring of the first pair of strings is twice as long as the longest common substring of the second pair of strings, although ...
... is not robust. Consider, for example, two pairs of strings: an , an−1 b and a(n−1)/2 ba(n−1)/2 , an−1 b. (Assume for simplicity that n − 1 ≥ 2 is even.) The longest common substring of the first pair of strings is twice as long as the longest common substring of the second pair of strings, although ...
ppt
... One-way functions are essential to the two guards password problem • Are we done? Given a noninteracive identification protocol want to define a one-way function • Define function f(r) as the mapping that Alice does in the setup phase between her random bits r and the information y given to Bob and ...
... One-way functions are essential to the two guards password problem • Are we done? Given a noninteracive identification protocol want to define a one-way function • Define function f(r) as the mapping that Alice does in the setup phase between her random bits r and the information y given to Bob and ...
Locality Preserving Hashing Kang Zhao, Hongtao Lu and Jincheng Mei
... the data covariance matrix with maximum eigenvalues are used as hashing projection matrix. Spectral Hashing (SH) (Weiss, Torralba, and Fergus 2008) formulates the hashing problem as a particular form of graph partition to seek a code with balanced partitioned and uncorrelated bits. After that, some ...
... the data covariance matrix with maximum eigenvalues are used as hashing projection matrix. Spectral Hashing (SH) (Weiss, Torralba, and Fergus 2008) formulates the hashing problem as a particular form of graph partition to seek a code with balanced partitioned and uncorrelated bits. After that, some ...
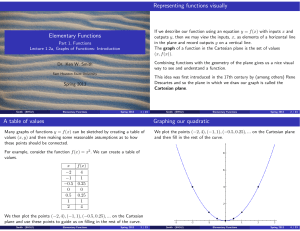
1.2 Functions Graphs (slides 4-to-1)
... In the image below a vertical line (in yellow) corresponding to a particular x-value hits the curve at exactly one point. This should be true for all the elements in the domain of the function. A variety of applications in science require that we understand where a function is rising or falling and ...
... In the image below a vertical line (in yellow) corresponding to a particular x-value hits the curve at exactly one point. This should be true for all the elements in the domain of the function. A variety of applications in science require that we understand where a function is rising or falling and ...
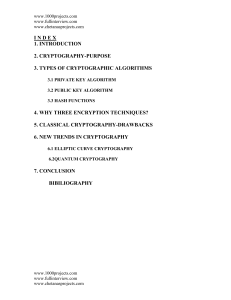
6.1. Elliptic Curve Cryptography
... Cryptography, then, not only protects data from theft or alteration, but can also be used for user authentication. There are, in general, three types of cryptographic schemes typically used to accomplish these goals: secret key (or symmetric) cryptography, publickey (or asymmetric) cryptography, and ...
... Cryptography, then, not only protects data from theft or alteration, but can also be used for user authentication. There are, in general, three types of cryptographic schemes typically used to accomplish these goals: secret key (or symmetric) cryptography, publickey (or asymmetric) cryptography, and ...
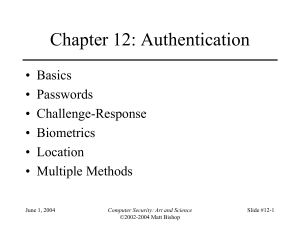
12_Auth_nemo
... C-R and Dictionary Attacks • Same as for fixed passwords – Attacker knows challenge r and response f(r); if f encryption function, can try different keys • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: K ...
... C-R and Dictionary Attacks • Same as for fixed passwords – Attacker knows challenge r and response f(r); if f encryption function, can try different keys • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: K ...
Chapter 4 Measurable Functions
... We remark that in Theorem 4.1.1 it would have sufficed to have Φ defined on a set D ⊆ Rn provided (f1 , . . . , fn ) : X → D. Remark 4.1.1. It follows from Theorem 4.1.1 that such combinations of measurable functions as the following must be measurable. • c1 f1 + c2 f2 where c1 and c2 are constants ...
... We remark that in Theorem 4.1.1 it would have sufficed to have Φ defined on a set D ⊆ Rn provided (f1 , . . . , fn ) : X → D. Remark 4.1.1. It follows from Theorem 4.1.1 that such combinations of measurable functions as the following must be measurable. • c1 f1 + c2 f2 where c1 and c2 are constants ...
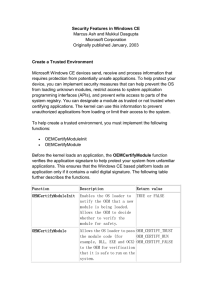
Security Features in Windows CE
... inside a database volume does not give it any additional security. Therefore, this feature is most useful in databases that are stored within the object store. Removing the system file attribute from a database volume that contains a system database will expose that database to access by untrusted a ...
... inside a database volume does not give it any additional security. Therefore, this feature is most useful in databases that are stored within the object store. Removing the system file attribute from a database volume that contains a system database will expose that database to access by untrusted a ...
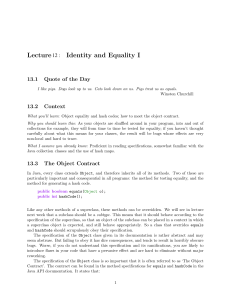
Lecture 12 : Identity and Equality I
... of computer science. A hash table is a representation for a mapping: an abstract data type that maps keys to values. Hash tables offer constant time lookup, so they tend to perform better than trees or lists. Keys don’t have to be ordered, or have any particular property, except for offering equals an ...
... of computer science. A hash table is a representation for a mapping: an abstract data type that maps keys to values. Hash tables offer constant time lookup, so they tend to perform better than trees or lists. Keys don’t have to be ordered, or have any particular property, except for offering equals an ...
PDF
... sample purely uniformly from S(w, ℓ, b) using an NP oracle to answer feasibility queries. However, such hash functions involve constructions that are difficult to implement and reason about in existing combinatorial search methods. Instead, we use a more practical algorithm based on pairwise indepen ...
... sample purely uniformly from S(w, ℓ, b) using an NP oracle to answer feasibility queries. However, such hash functions involve constructions that are difficult to implement and reason about in existing combinatorial search methods. Instead, we use a more practical algorithm based on pairwise indepen ...
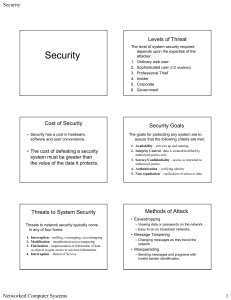
Slides on Security
... • Key servers are computers that have a database of public keys. • Upon receiving a request for a public key, a key server sends the client the desired public key. • The messages from the key server are ...
... • Key servers are computers that have a database of public keys. • Upon receiving a request for a public key, a key server sends the client the desired public key. • The messages from the key server are ...
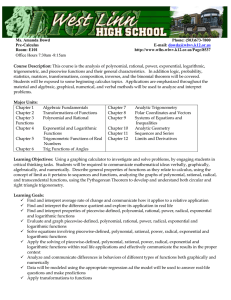
Course Syllabus - wlhs.wlwv.k12.or.us
... learned from your peers and having the opportunities to articulate, challenge, and defend ideas will strengthen every individuals mathematical understanding. We are all in this together, so let’s work together. Electronic Devices o Cell phones, iPods and other electronic devices will NOT be tolera ...
... learned from your peers and having the opportunities to articulate, challenge, and defend ideas will strengthen every individuals mathematical understanding. We are all in this together, so let’s work together. Electronic Devices o Cell phones, iPods and other electronic devices will NOT be tolera ...
FUNCTIONS TEST STUDY GUIDE Test covers
... STUDY GUIDE ANSWERS 2) a) y=|x|; shift down 2, reflect over xaxis; y = -|x|-2 b) y = x ; shift left and up; y = x 1 1 c) y = log x; shift left 1; y = log( x + 1) d) y = x3; shift right 1, up 2, reflect over xaxis; y = -(x-1)3 +2 ...
... STUDY GUIDE ANSWERS 2) a) y=|x|; shift down 2, reflect over xaxis; y = -|x|-2 b) y = x ; shift left and up; y = x 1 1 c) y = log x; shift left 1; y = log( x + 1) d) y = x3; shift right 1, up 2, reflect over xaxis; y = -(x-1)3 +2 ...
Discussion
... ratios, and because calculation with them was so difficult in the days before calculators, names were given to each one and tables constructed for them. The advent of computers has meant that given one of the functions, the others are easily calculated (using trigonometric identities). The secant, c ...
... ratios, and because calculation with them was so difficult in the days before calculators, names were given to each one and tables constructed for them. The advent of computers has meant that given one of the functions, the others are easily calculated (using trigonometric identities). The secant, c ...
for Sublinear Time Maximum Inner Product Search (MIPS)
... system, (ii) large-scale object detection with DPM, and (iii) multi-class label prediction. Recommender systems: Recommender systems are often based on collaborative filtering which relies on past behavior of users, e.g., past purchases and ratings. Latent factor modeling based on matrix factorizati ...
... system, (ii) large-scale object detection with DPM, and (iii) multi-class label prediction. Recommender systems: Recommender systems are often based on collaborative filtering which relies on past behavior of users, e.g., past purchases and ratings. Latent factor modeling based on matrix factorizati ...
Cryptographic hash function
A cryptographic hash function is a hash function which is considered practically impossible to invert, that is, to recreate the input data from its hash value alone. These one-way hash functions have been called ""the workhorses of modern cryptography"". The input data is often called the message, and the hash value is often called the message digest or simply the digest.The ideal cryptographic hash function has four main properties: it is easy to compute the hash value for any given message it is infeasible to generate a message from its hash it is infeasible to modify a message without changing the hash it is infeasible to find two different messages with the same hash.Cryptographic hash functions have many information security applications, notably in digital signatures, message authentication codes (MACs), and other forms of authentication. They can also be used as ordinary hash functions, to index data in hash tables, for fingerprinting, to detect duplicate data or uniquely identify files, and as checksums to detect accidental data corruption. Indeed, in information security contexts, cryptographic hash values are sometimes called (digital) fingerprints, checksums, or just hash values, even though all these terms stand for more general functions with rather different properties and purposes.