Expanding coverage while preserving beauty in Vail.
... Vail, Colorado, is a picturesque community, famous for its beautiful mountains and ski slopes. That makes it a popular vacation destination for thousands of recreational travelers; however, the challenging topography surrounding the Village and residential neighborhood makes it especially difficult ...
... Vail, Colorado, is a picturesque community, famous for its beautiful mountains and ski slopes. That makes it a popular vacation destination for thousands of recreational travelers; however, the challenging topography surrounding the Village and residential neighborhood makes it especially difficult ...
Apple store and it`s networks
... •The database application and the database are separated into a client/server architecture ...
... •The database application and the database are separated into a client/server architecture ...
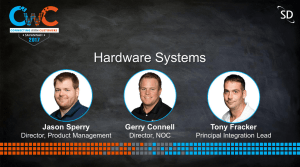
Hardware Systems - Satcom Direct
... Providing WiFi and Ethernet access to the aircraft Local Area Network ...
... Providing WiFi and Ethernet access to the aircraft Local Area Network ...
Test your knowledge
... A firewall is a general term that refers to hardware or software that restricts access to data and information on a network. One use of firewalls is to deny network access to outsiders. ...
... A firewall is a general term that refers to hardware or software that restricts access to data and information on a network. One use of firewalls is to deny network access to outsiders. ...
Enterprise Solutions for Small Business
... offering Professional and Managed Services for small and medium businesses. We understand that the smaller your business, the more pressure you face to implement high-quality and cost-effective technology. So we work with small and medium businesses to provide enterprise-quality solutions customized ...
... offering Professional and Managed Services for small and medium businesses. We understand that the smaller your business, the more pressure you face to implement high-quality and cost-effective technology. So we work with small and medium businesses to provide enterprise-quality solutions customized ...
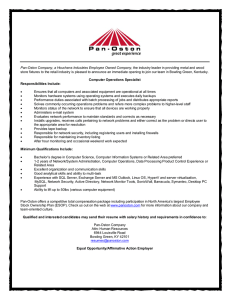
Pan-Oston Company, a Houchens Industries Employee Owned
... Computer Operations Specialist Responsibilities Include: ...
... Computer Operations Specialist Responsibilities Include: ...
Wireless Networks: Things I Wish I Had Learned in
... but Need to Explore Better Alternatives No wired-equivalent for wireless networks ...
... but Need to Explore Better Alternatives No wired-equivalent for wireless networks ...
WiFi Robocar with Network Camera
... performances on an automatic wireless robot using IEEE 802.11g standard and infrared sensors. In this paper, a study of performances on an automatic wireless robot is presented through the use of IEEE 802.11g standard. The Robocar controlling equipments (e.g. motors) through a PIC microcontroller an ...
... performances on an automatic wireless robot using IEEE 802.11g standard and infrared sensors. In this paper, a study of performances on an automatic wireless robot is presented through the use of IEEE 802.11g standard. The Robocar controlling equipments (e.g. motors) through a PIC microcontroller an ...
Introduction
... Another benefit of inSSIDer is that it displays the encryption type used on a specific network. This is important information if you are doing a penetration test or a security audit. If your company is using wired equivalent privacy (WEP), it would be wise to switch to Wi-Fi protected access (WPA) o ...
... Another benefit of inSSIDer is that it displays the encryption type used on a specific network. This is important information if you are doing a penetration test or a security audit. If your company is using wired equivalent privacy (WEP), it would be wise to switch to Wi-Fi protected access (WPA) o ...
инструкция
... able to control session time and received data volume. To finish your session press “Logoff” reference at the top of the page. Please note that, till you press “Logoff”, your cash will be charged off from your card. If you did not manage to press “Logoff” and the statistics window closed, you can op ...
... able to control session time and received data volume. To finish your session press “Logoff” reference at the top of the page. Please note that, till you press “Logoff”, your cash will be charged off from your card. If you did not manage to press “Logoff” and the statistics window closed, you can op ...
Wireless Network Security
... something, allows your computer to connect to the Internet using magic. -Motel 6 commercial ...
... something, allows your computer to connect to the Internet using magic. -Motel 6 commercial ...
Hands-On Ethical Hacking and Network Security
... Per-packet key mixing MAC addresses are used to create a key Each link uses a different key ...
... Per-packet key mixing MAC addresses are used to create a key Each link uses a different key ...
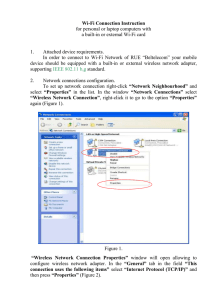
Wired (Ethernet) Instructions for Windows XP
... Click on the Add... button; another window will open. In the Association tab make sure the Network name (SSID) is HuskyNet Wireless WPA. (This must be typed exactly as shown with the same capitalization and spacing.) ...
... Click on the Add... button; another window will open. In the Association tab make sure the Network name (SSID) is HuskyNet Wireless WPA. (This must be typed exactly as shown with the same capitalization and spacing.) ...
Wireless Networking
... (hop) and then send another short burst Since the FHSS devices that are communicating agree on which frequencies to hop to, and use each frequency for a brief period of time (less than 400 milliseconds) before moving on, several independent FHSS networks can exist in the same physical area without i ...
... (hop) and then send another short burst Since the FHSS devices that are communicating agree on which frequencies to hop to, and use each frequency for a brief period of time (less than 400 milliseconds) before moving on, several independent FHSS networks can exist in the same physical area without i ...
NEXWAY Workshop Afternoon session A- Workshop - 14.00
... satellite links, NEXWAY, Tommaso Rossi, University Rome Tor Vegata, Italy 15:00-15:15- White Paper on Key Issues in Emerging Intermediary Infrastructures for Wireless Services. - NEXWAY, Eleni Tsiakkouri, University of Cyprus, Cyprus 15:15-15:30 - White Paper on Blind Channel Equalization Techniques ...
... satellite links, NEXWAY, Tommaso Rossi, University Rome Tor Vegata, Italy 15:00-15:15- White Paper on Key Issues in Emerging Intermediary Infrastructures for Wireless Services. - NEXWAY, Eleni Tsiakkouri, University of Cyprus, Cyprus 15:15-15:30 - White Paper on Blind Channel Equalization Techniques ...
Document
... • 2. use the LAN Network to connect the General PC with the Buffalo (plug the wire into port 1 on the Buffalo AP) • 3. open the command prompt in the General PC • 4. input “ipconfig” to get the network info. Refer to the figure on the next page. ...
... • 2. use the LAN Network to connect the General PC with the Buffalo (plug the wire into port 1 on the Buffalo AP) • 3. open the command prompt in the General PC • 4. input “ipconfig” to get the network info. Refer to the figure on the next page. ...
WRT600N Datasheet
... onto your network using readily available USB 2.0 hard drives -- or plug in a USB flash disk for a convenient way to access your portable data files. The built-in Media Server streams music, video, and photos from the attached storage device to any UPnP compatible media adapter. And you can get to y ...
... onto your network using readily available USB 2.0 hard drives -- or plug in a USB flash disk for a convenient way to access your portable data files. The built-in Media Server streams music, video, and photos from the attached storage device to any UPnP compatible media adapter. And you can get to y ...
Chapter 24 - William Stallings, Data and Computer
... do not support advanced user authentication schemes vulnerable to attacks that take advantage of problems within TCP/IP susceptible to security breaches caused by improper configurations ...
... do not support advanced user authentication schemes vulnerable to attacks that take advantage of problems within TCP/IP susceptible to security breaches caused by improper configurations ...
Chapter 5 Protecting Information Resources
... ◦ Especially in recent years, with “hackers” becoming more numerous and adept at stealing and altering private information ◦ 1. Comprehensive security system ◦ 2. Threats: ...
... ◦ Especially in recent years, with “hackers” becoming more numerous and adept at stealing and altering private information ◦ 1. Comprehensive security system ◦ 2. Threats: ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.