Proposal Presentation
... Product will be open source and will integrate several available technologies ...
... Product will be open source and will integrate several available technologies ...
Network - Missouri State University
... • Virtual private network (VPN) - a way to use the public telecommunication infrastructure (e.g., Internet) to provide secure access to an organization’s network • Valued-added network (VAN) - a private network, provided by a ______ party, for exchanging information through a high capacity connectio ...
... • Virtual private network (VPN) - a way to use the public telecommunication infrastructure (e.g., Internet) to provide secure access to an organization’s network • Valued-added network (VAN) - a private network, provided by a ______ party, for exchanging information through a high capacity connectio ...
SBG940 SS.qxp - Adams Cable Equipment
... The SBG940 merges the advantages of a Motorola cable modem with the mobility of a wireless LAN (WLAN). It includes an integrated 802.11 b/g access point that allows users to roam around the home or small business and remain connected to the network. Now subscribers can place computers and periphera ...
... The SBG940 merges the advantages of a Motorola cable modem with the mobility of a wireless LAN (WLAN). It includes an integrated 802.11 b/g access point that allows users to roam around the home or small business and remain connected to the network. Now subscribers can place computers and periphera ...
Homework #5 was due April 3
... 1. Which document is arguably the most famous of all security policies as this is one document that pretty much everyone who works for any organization is required to read, and in many cases sign, before they can start work? A. Material safeties data sheet (MSDS) B. Forensics report C. Acceptable us ...
... 1. Which document is arguably the most famous of all security policies as this is one document that pretty much everyone who works for any organization is required to read, and in many cases sign, before they can start work? A. Material safeties data sheet (MSDS) B. Forensics report C. Acceptable us ...
Pathways and the Pioneering Spirit
... vary, and students are restricted to those sections of the intranet that are relevant to them. A three-layer approach, including Authentication Authorisation Accounting (AAA) is in use. Like in most systems of this type, authentication is by means of entering a user name and password. Based on the ...
... vary, and students are restricted to those sections of the intranet that are relevant to them. A three-layer approach, including Authentication Authorisation Accounting (AAA) is in use. Like in most systems of this type, authentication is by means of entering a user name and password. Based on the ...
What Is Highly Critical Wireless Networking (HCWN)
... beginning to dominate our communications infrastructure and reshape our industrial base. Variations on these TCPIP communications protocols, using high or low power signals, have names such as Wi-Fi, Bluetooth, ZigBee, Z-Wave, cellular mobile radio, or mesh networks. Highly Critical Wireless Network ...
... beginning to dominate our communications infrastructure and reshape our industrial base. Variations on these TCPIP communications protocols, using high or low power signals, have names such as Wi-Fi, Bluetooth, ZigBee, Z-Wave, cellular mobile radio, or mesh networks. Highly Critical Wireless Network ...
cisco.camre.ac.uk
... In the management of a security system, these features should be present: CCTV, intrusion detection systems, staff and visitor identification, access control (sign in /out) system security personnel, cable and communication shielding and ...
... In the management of a security system, these features should be present: CCTV, intrusion detection systems, staff and visitor identification, access control (sign in /out) system security personnel, cable and communication shielding and ...
Computer Confluence 6/e
... • Node: Any device on the network such as computers or peripherals (printers, routers, etc) is called a node. • Nodes are typically connected to hubs (or ...
... • Node: Any device on the network such as computers or peripherals (printers, routers, etc) is called a node. • Nodes are typically connected to hubs (or ...
Network Security Analysis Prepared By: cowave Communication
... 2. Security solutions should be one of the best who ...
... 2. Security solutions should be one of the best who ...
IEEE CONFERENCE ON COMMUNICATION TECHNOLOGIES
... planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Conference Co-Chair: Dr.Asif Masood DEADLINES ...
... planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Conference Co-Chair: Dr.Asif Masood DEADLINES ...
Assignment # 3 - UNT Class Server
... based is used to keep a network secure. The primary goal of a firewall is to analyze all incoming traffic and to analyze the data packets to make sure they are not harmful. The firewall is like a bridge between the users network which assumed to be secure and also another network like the internet t ...
... based is used to keep a network secure. The primary goal of a firewall is to analyze all incoming traffic and to analyze the data packets to make sure they are not harmful. The firewall is like a bridge between the users network which assumed to be secure and also another network like the internet t ...
Remote Access Policy
... for connecting to a company’s network from any host. These standards are designed to minimize the potential exposure to the company from damages which may result from unauthorized use of resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to p ...
... for connecting to a company’s network from any host. These standards are designed to minimize the potential exposure to the company from damages which may result from unauthorized use of resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to p ...
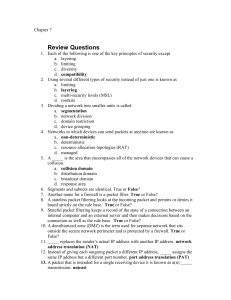
Chapter07
... 14. A(n) _____ is a smaller logical grouping of network devices. virtual local area network (VLAN). 15. The standard for marking VLAN packets is _____ IEEE 802.1q 16. Explain the advantages of the access point separating packets in a VLAN. The flexibility of a wireless VLAN depends on which device ...
... 14. A(n) _____ is a smaller logical grouping of network devices. virtual local area network (VLAN). 15. The standard for marking VLAN packets is _____ IEEE 802.1q 16. Explain the advantages of the access point separating packets in a VLAN. The flexibility of a wireless VLAN depends on which device ...
Security - CS Course Webpages
... Network Threats (cont.) • SMTP backdoor command attacks • Information leakage attacks via finger, echo, ping, and traceroute commands • Attacks via download of Java and ActiveX ...
... Network Threats (cont.) • SMTP backdoor command attacks • Information leakage attacks via finger, echo, ping, and traceroute commands • Attacks via download of Java and ActiveX ...
Networks Now and Future
... Global networking: TCP/IP and ATM • Internetworking: connecting one network to another to get a “network of networks” • TCP/IP, aka “The Internet”, is based on bouncing “packets” around the world, each one finding its’ own route from one place to another. Rather random, but simple. • ATM, asynchron ...
... Global networking: TCP/IP and ATM • Internetworking: connecting one network to another to get a “network of networks” • TCP/IP, aka “The Internet”, is based on bouncing “packets” around the world, each one finding its’ own route from one place to another. Rather random, but simple. • ATM, asynchron ...
rural access in Nepal
... NGOs, schools, and private organizations. Goal is to develop knowledge-based resource network with Internet access for isolated rural communities. RDL shall provide variety of services to different user groups in rural communities relating to: ...
... NGOs, schools, and private organizations. Goal is to develop knowledge-based resource network with Internet access for isolated rural communities. RDL shall provide variety of services to different user groups in rural communities relating to: ...
benefits of a connected world
... IEEE 802.11y-2008 extended operation of 802.11a to the licensed 3.7 GHz band. Increased power limits allow a range up to 5,000 m. As of 2009[update], it is only being licensed in the United States by the FCC. Assumes short guard interval (SGI) enabled otherwise reduces each data rate by 10%. ...
... IEEE 802.11y-2008 extended operation of 802.11a to the licensed 3.7 GHz band. Increased power limits allow a range up to 5,000 m. As of 2009[update], it is only being licensed in the United States by the FCC. Assumes short guard interval (SGI) enabled otherwise reduces each data rate by 10%. ...
Top-Down Network Design
... personal firewall and antivirus software • Disable beacons that broadcast the SSID, and require MAC address authentication – Except in cases where the WLAN is used by visitors ...
... personal firewall and antivirus software • Disable beacons that broadcast the SSID, and require MAC address authentication – Except in cases where the WLAN is used by visitors ...
EFF / TCPA Roundtable - Oxford Internet Institute
... Will the internet escape regulation The reality of inside the beltway Security and privacy may be the wedge The legacy businesses -- will they “give up” ...
... Will the internet escape regulation The reality of inside the beltway Security and privacy may be the wedge The legacy businesses -- will they “give up” ...
Abstract - PG Embedded systems
... In this analysis, we consider Wireless network, where nodes that have decoded the message at the previous hop cooperate in the transmission toward the next hop, realizing a distributed space-time coding scheme. Service delivery in a heterogeneous all-IP wireless network environment requires the sele ...
... In this analysis, we consider Wireless network, where nodes that have decoded the message at the previous hop cooperate in the transmission toward the next hop, realizing a distributed space-time coding scheme. Service delivery in a heterogeneous all-IP wireless network environment requires the sele ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.