18th International Conference on Transparent Optical Networks
... COMANDER-FiWiN5G Workshop on “Fiber-Wireless Network Technologies and Architectures towards 5G and Beyond” Fiber-wireless networks that rely on the collaborative use of both fiber-based and wireless communication technologies are currently turning into a highly important research area in view of the ...
... COMANDER-FiWiN5G Workshop on “Fiber-Wireless Network Technologies and Architectures towards 5G and Beyond” Fiber-wireless networks that rely on the collaborative use of both fiber-based and wireless communication technologies are currently turning into a highly important research area in view of the ...
Connecting a Computer/ Smartphone/Tablet to the Wireless Network
... To connect a gaming (Playstation, Xbox, etc) or streaming (Roku, Apple TV, etc) device to the wireless network, open the list of wireless networks and select ccsu-gaming. Your device should connect to the ccsu-gaming wireless network automatically. If it does not, you may need to complete a Gaming/ ...
... To connect a gaming (Playstation, Xbox, etc) or streaming (Roku, Apple TV, etc) device to the wireless network, open the list of wireless networks and select ccsu-gaming. Your device should connect to the ccsu-gaming wireless network automatically. If it does not, you may need to complete a Gaming/ ...
Wireless Network Security
... • Some wireless devices, such as smartphones and tablets, have sophisticated operating systems but limited memory and processing resources with which to counter threats, including denial of service and malware – Accessibility • Some wireless devices, such as sensors and robots, may be left unattende ...
... • Some wireless devices, such as smartphones and tablets, have sophisticated operating systems but limited memory and processing resources with which to counter threats, including denial of service and malware – Accessibility • Some wireless devices, such as sensors and robots, may be left unattende ...
Module 03 Wireless Media Presentation
... signal by the receiver Fibers are used in pairs to provide full duplex communications Light rays obey the laws of reflection and refraction as they travel through a glass fiber, which allows fibers with the property of total internal reflection to be manufactured Total internal reflection makes ligh ...
... signal by the receiver Fibers are used in pairs to provide full duplex communications Light rays obey the laws of reflection and refraction as they travel through a glass fiber, which allows fibers with the property of total internal reflection to be manufactured Total internal reflection makes ligh ...
Ch10aProtectionMechanisms
... – Then periodically samples network activity, based on statistical methods, and compares the samples to the baseline ...
... – Then periodically samples network activity, based on statistical methods, and compares the samples to the baseline ...
Network Security
... repairing cannot be done Quarantine the file: “cover” the file so the virus cannot spread to other files and so the file cannot be accessed by other programs ...
... repairing cannot be done Quarantine the file: “cover” the file so the virus cannot spread to other files and so the file cannot be accessed by other programs ...
Network Planning Technical Sub
... DNS – Current status – Kevin ITSS has completed the implementation of DNSOne and it is now in full operation. Some cleanup of unused domains was done in the process. In coordination with NDUS, the nodak domains hosted at UND have been moved to be authoritative on DNSOne. Kevin inquired about an inte ...
... DNS – Current status – Kevin ITSS has completed the implementation of DNSOne and it is now in full operation. Some cleanup of unused domains was done in the process. In coordination with NDUS, the nodak domains hosted at UND have been moved to be authoritative on DNSOne. Kevin inquired about an inte ...
Top-Down Network Design
... personal firewall and antivirus software • Disable beacons that broadcast the SSID, and require MAC address authentication – Except in cases where the WLAN is used by visitors ...
... personal firewall and antivirus software • Disable beacons that broadcast the SSID, and require MAC address authentication – Except in cases where the WLAN is used by visitors ...
Deployment of Broad Band WMAN using Wi
... Privacy Sublayer uses privacy protocol that is based on the privacy key exchange management (PKM) protocol PKM protocol uses X.509 digital certificates with RSA public key encryption for SS authentication and authorization key exchange. ...
... Privacy Sublayer uses privacy protocol that is based on the privacy key exchange management (PKM) protocol PKM protocol uses X.509 digital certificates with RSA public key encryption for SS authentication and authorization key exchange. ...
Slide 1
... Set up a login page similar to the one of the ISP Wait for clients to connect to rogue access point and authenticate Possibly forward session to ISP network Facilitated by automatic connection defaults ...
... Set up a login page similar to the one of the ISP Wait for clients to connect to rogue access point and authenticate Possibly forward session to ISP network Facilitated by automatic connection defaults ...
Bandwidth Management
... • Security is a major concern – A multitude of operating systems, devices and platforms accessing the network creates specific challenges – Unmanaged devices can become infected off-site and introduce issues when connected to the campus network • Students, staff & faculty with laptops • Clean Access ...
... • Security is a major concern – A multitude of operating systems, devices and platforms accessing the network creates specific challenges – Unmanaged devices can become infected off-site and introduce issues when connected to the campus network • Students, staff & faculty with laptops • Clean Access ...
Security Resume - Kirubha Shankar Murugesan
... Network Design Administrator (TCP/IP, tcpdump, Wireshark): Jan 2015 - Apr 2015 Constructed a network topology with firewalls, switches, VLANS and routers with proper subnet masking and IP addressing for a small firm consisting of four departments. Experience with networking protocols such as BGP ...
... Network Design Administrator (TCP/IP, tcpdump, Wireshark): Jan 2015 - Apr 2015 Constructed a network topology with firewalls, switches, VLANS and routers with proper subnet masking and IP addressing for a small firm consisting of four departments. Experience with networking protocols such as BGP ...
BigPond ElitE™ WiRElESS
... 300kbps to 1Mbps in other coverage areas. Actual speeds vary due to factors such as distance from the cell, local conditions, user numbers, hardware software and other factors. Speeds vary due to factors such as distance from the cell, local conditions, number of users, download source, associated c ...
... 300kbps to 1Mbps in other coverage areas. Actual speeds vary due to factors such as distance from the cell, local conditions, user numbers, hardware software and other factors. Speeds vary due to factors such as distance from the cell, local conditions, number of users, download source, associated c ...
UGL2454-APXR
... Point) and Bridge (Point to Multi-Point) modes The 2.4GHz 802.11g/b Wireless Access Point with Super-G function boost ...
... Point) and Bridge (Point to Multi-Point) modes The 2.4GHz 802.11g/b Wireless Access Point with Super-G function boost ...
Helicomm Hypercompetes in M2M
... globally for human use. In that same year, over 8 billion embedded microcontrollers shipped for machine use. Machine-to-machine communication relies upon collecting and communicating data with embedded systems, (embedded systems are computer chips within machine devices.) In many remote monitoring a ...
... globally for human use. In that same year, over 8 billion embedded microcontrollers shipped for machine use. Machine-to-machine communication relies upon collecting and communicating data with embedded systems, (embedded systems are computer chips within machine devices.) In many remote monitoring a ...
IEEE 802.11x WiFi Protocol
... can connect to Person C ONLY via a direct connection to Person B. In this example person B is termed the server and persons A & C the clients; in a wireless scenario person B would be some sort of Access Point. ...
... can connect to Person C ONLY via a direct connection to Person B. In this example person B is termed the server and persons A & C the clients; in a wireless scenario person B would be some sort of Access Point. ...
Out Of The Blue - Joshua`s Learning Log
... With a wireless connection each student can have their own laptop which in turn they can use throughout the entire school. Additionally, since wireless means without wires, there is no cost for cables or the installation. Lastly, computers are not the only devices that can make use of a wireless net ...
... With a wireless connection each student can have their own laptop which in turn they can use throughout the entire school. Additionally, since wireless means without wires, there is no cost for cables or the installation. Lastly, computers are not the only devices that can make use of a wireless net ...
Open AirGATE™
... OAG is a member of the AirAWARE™ family of connectivity solutions for mobile computers. OAG system software enables wireless connectivity between mobile computers running AirVU emulators that are AirGATE Enabled and enterprise networks. With OAG, mobile wireless computers appear as stationary TCP/IP ...
... OAG is a member of the AirAWARE™ family of connectivity solutions for mobile computers. OAG system software enables wireless connectivity between mobile computers running AirVU emulators that are AirGATE Enabled and enterprise networks. With OAG, mobile wireless computers appear as stationary TCP/IP ...
Virtualization Group
... Do Sensors need Virtualization? • Just build metanetwork specialized to sensors • Useful for wireless sensor networks? – Same arguments apply as regular IP – Yes for GENI; not operationally? ...
... Do Sensors need Virtualization? • Just build metanetwork specialized to sensors • Useful for wireless sensor networks? – Same arguments apply as regular IP – Yes for GENI; not operationally? ...
Ch10 - Protection Mechanism
... • Network connectivity using external connections – Usually much simpler and less sophisticated than Internet connections – Simple user name and password schemes are usually the only means of authentication ...
... • Network connectivity using external connections – Usually much simpler and less sophisticated than Internet connections – Simple user name and password schemes are usually the only means of authentication ...
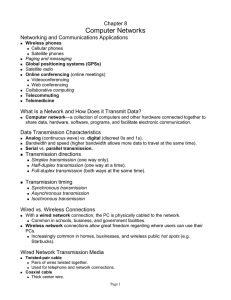
Chapter 7 Part 2 Networks
... – Change your network name (SSID). The default Service Set Identifier is linked to default access codes by the manufacturer. Changing your network name will make it more difficult for hackers to find your access code. – Disable SSID broadcast. Most routers are set up to broadcast their SSIDs so they ...
... – Change your network name (SSID). The default Service Set Identifier is linked to default access codes by the manufacturer. Changing your network name will make it more difficult for hackers to find your access code. – Disable SSID broadcast. Most routers are set up to broadcast their SSIDs so they ...
click here
... Unauthorized network usage represents a financial liability for the school district, with a penalty being the potential loss of E-Rate, ODE, and OSN technology funding; and/or criminal/civil liability under the Family Educational Rights to Privacy Act (FERPA) and HIPAA ...
... Unauthorized network usage represents a financial liability for the school district, with a penalty being the potential loss of E-Rate, ODE, and OSN technology funding; and/or criminal/civil liability under the Family Educational Rights to Privacy Act (FERPA) and HIPAA ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.