Power Point - Toronto Users Group
... frequently and automatically (“Dynamic WEP” or “Dynamic Key Distribution”) • adds mutual authentication • don’t connect to a rogue Access Point, and don’t let an unknown user onto the network VPN – Virtual Private Network LEAP – Light Extensible Authentication Protocol TKIP – Temporal Key Integrity ...
... frequently and automatically (“Dynamic WEP” or “Dynamic Key Distribution”) • adds mutual authentication • don’t connect to a rogue Access Point, and don’t let an unknown user onto the network VPN – Virtual Private Network LEAP – Light Extensible Authentication Protocol TKIP – Temporal Key Integrity ...
Ground Shaking Criteria 1997 Codes and Beyond
... It communicates wirelessly with both access points and wireless adapters, and is used to connect wireless segments to wireless ...
... It communicates wirelessly with both access points and wireless adapters, and is used to connect wireless segments to wireless ...
Start a wireless network with up to 4X the range and 12X
... The Access Point built into the Router uses the very latest wireless networking technology: Wireless-N (draft 802.11n). By overlaying the signals of multiple radios, Wireless-N’s “Multiple In, Multiple Out” (MIMO) technology multiplies the effective data rate. Unlike ordinary wireless networking tec ...
... The Access Point built into the Router uses the very latest wireless networking technology: Wireless-N (draft 802.11n). By overlaying the signals of multiple radios, Wireless-N’s “Multiple In, Multiple Out” (MIMO) technology multiplies the effective data rate. Unlike ordinary wireless networking tec ...
Wireless LAN Products
... D-Link DWL-900AP Point-to-point bridging capability With a DHCP server, the DWL-900AP will automatically obtain an IP address. 128-bit WEP (Wired Equivalent Privacy) a USB port is provided for flexibility in configuring the device ...
... D-Link DWL-900AP Point-to-point bridging capability With a DHCP server, the DWL-900AP will automatically obtain an IP address. 128-bit WEP (Wired Equivalent Privacy) a USB port is provided for flexibility in configuring the device ...
• Overview of Cyber Security & need of cyber security • Introduction
... COMPUTER SCIENCE AND ENGINEERING DEPARTMENT Name of Course ...
... COMPUTER SCIENCE AND ENGINEERING DEPARTMENT Name of Course ...
SO 2.4.4 - Broadband for all
... Anywhere, Anytime" supported by all system levels from access methods and networks to service platforms and services – a consolidated approach to serving mobile users with enablers for applications and services. – a consolidated European approach to technology, systems and services, notably for stan ...
... Anywhere, Anytime" supported by all system levels from access methods and networks to service platforms and services – a consolidated approach to serving mobile users with enablers for applications and services. – a consolidated European approach to technology, systems and services, notably for stan ...
Ch10b
... Primary and Secondary for Redundancy ASA provides up to 20 individual contexts Allows any VLAN on the switch to be passed through to the device to operate as a firewall port and integrates firewall security inside the ...
... Primary and Secondary for Redundancy ASA provides up to 20 individual contexts Allows any VLAN on the switch to be passed through to the device to operate as a firewall port and integrates firewall security inside the ...
Eric Kha Professor Shin 4/13/15 Chapter 8 PowerPoint Answer
... baseband) as well as protocols (IP addresses, domain name servers, and packetization). ...
... baseband) as well as protocols (IP addresses, domain name servers, and packetization). ...
New 802.11 Security Standards
... MAC (media access control) – Possible to restrict access by MAC address on many AP (access points) by means of an ACL – All standards compliant NIC cards, including WLAN cards, should have unique MAC, some software allow this address to be ‘spoofed’ ...
... MAC (media access control) – Possible to restrict access by MAC address on many AP (access points) by means of an ACL – All standards compliant NIC cards, including WLAN cards, should have unique MAC, some software allow this address to be ‘spoofed’ ...
MPLS Based Web Switching
... Emergence of high-speed 802.11a WLANs (108Mbps) WLANs can operate a varying rates (1,2,..,11, ..,22, ..,54, 108) Reception range decreases with rate Given the above, we can think of a cellular-like architecture for multi-hop wireless networks Start with a large cell; as nodes increase split into ( ...
... Emergence of high-speed 802.11a WLANs (108Mbps) WLANs can operate a varying rates (1,2,..,11, ..,22, ..,54, 108) Reception range decreases with rate Given the above, we can think of a cellular-like architecture for multi-hop wireless networks Start with a large cell; as nodes increase split into ( ...
IT ESSENTIALS V. 4.1 Module 9 Fundamental Security 9.1 Explain
... Which wireless security protocol was created by Cisco? What do virus, spyware, and adware detection programs look for? What are the code patterns called? ...
... Which wireless security protocol was created by Cisco? What do virus, spyware, and adware detection programs look for? What are the code patterns called? ...
Wireless
... Wireless Networks • Bluetooth: Personal Area Network (PAN) • 802.11 (Wi-Fi): used in • Disadvantages of 802.11 wireless LANs –S wired LANs – One person can point to the detriment of all other wireless users. – Inherently . Software tools are easily available to capture data packets, and thereby “sn ...
... Wireless Networks • Bluetooth: Personal Area Network (PAN) • 802.11 (Wi-Fi): used in • Disadvantages of 802.11 wireless LANs –S wired LANs – One person can point to the detriment of all other wireless users. – Inherently . Software tools are easily available to capture data packets, and thereby “sn ...
What is a Network?
... A Network is a number of electronic devices which are connected so that data is able to be transferred between them. ...
... A Network is a number of electronic devices which are connected so that data is able to be transferred between them. ...
Wireless Networks
... Applications - VoIP phones, Security, AP’s Built into future switches/hubs Standard due 3Q2001 ...
... Applications - VoIP phones, Security, AP’s Built into future switches/hubs Standard due 3Q2001 ...
Federated Wireless Network Authentication
... Focused on 802.1x only? Concentrate group resources on single strategy Focus on standards-based solution that would provide a single interface for users Enables authn, encryption at edge If necessary, infrastructure could likely be used for non-802.1x ...
... Focused on 802.1x only? Concentrate group resources on single strategy Focus on standards-based solution that would provide a single interface for users Enables authn, encryption at edge If necessary, infrastructure could likely be used for non-802.1x ...
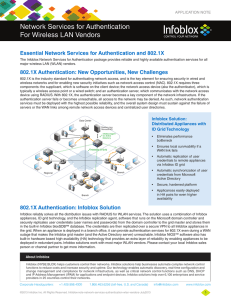
Network Services for Authentication For Wireless LAN
... Infoblox reliably solves all the distribution issues with RADIUS for WLAN services. The solution uses a combination of Infobox appliances, ID grid technology, and the Infoblox replication agent, software that runs on the Microsoft domain controller and securely replicates user credentials (user name ...
... Infoblox reliably solves all the distribution issues with RADIUS for WLAN services. The solution uses a combination of Infobox appliances, ID grid technology, and the Infoblox replication agent, software that runs on the Microsoft domain controller and securely replicates user credentials (user name ...
Chapter 8 Power Point Solutions Define communications including
... Chapter 8 Power Point Solutions 1. Define communications including connectivity, the wireless revolution, and communication systems. Computer communications is the process of sharing data, programs and information between two or more computers. Connectivity uses computer networks to link people and ...
... Chapter 8 Power Point Solutions 1. Define communications including connectivity, the wireless revolution, and communication systems. Computer communications is the process of sharing data, programs and information between two or more computers. Connectivity uses computer networks to link people and ...
15.1 Networking
... 3.1.3 Describe how communication over networks is broken down into different layers. 3. What is the purpose of the OSI Model? ...
... 3.1.3 Describe how communication over networks is broken down into different layers. 3. What is the purpose of the OSI Model? ...
SpeedTouch™ 585(i) v6
... All trademarks are owned by their respective owners. Product specifications subject to change without prior notice. ...
... All trademarks are owned by their respective owners. Product specifications subject to change without prior notice. ...
Presentation Slides
... that spreads automatically through networks Trojan horse - An apparently useful and innocent application containing a hidden malicious program Spyware - A general term for programs that secretly monitor your actions. ...
... that spreads automatically through networks Trojan horse - An apparently useful and innocent application containing a hidden malicious program Spyware - A general term for programs that secretly monitor your actions. ...
Check Your Understanding Chapter 7 Part 1 For a quick review to
... 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a. fiber-optic. b. DSL. c. cable. d. satellite. 4. The part of the network that establishes a communications channel b ...
... 2. The type of network used for communication among a laptop and smartphone using Bluetooth is a a. WAN. b. PAN. c. LAN. d. MAN. 3. The fastest broadband Internet service is usually a. fiber-optic. b. DSL. c. cable. d. satellite. 4. The part of the network that establishes a communications channel b ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.