Midterm Test - 18Jul08 - Solutions
... d. client/server network 5. Most ____ consist of collections of typical end-user PCs linked by a common network medium. a. LANs c. peer-to-peer networks b. internetworks d. client/server networks 6. The emerging standard for WPANs is the IEEE ____ standard. a. 802.3 c. 802.11 b. 802.5 d. 802.15 7. _ ...
... d. client/server network 5. Most ____ consist of collections of typical end-user PCs linked by a common network medium. a. LANs c. peer-to-peer networks b. internetworks d. client/server networks 6. The emerging standard for WPANs is the IEEE ____ standard. a. 802.3 c. 802.11 b. 802.5 d. 802.15 7. _ ...
Hands-On Ethical Hacking and Network Security
... Addresses wireless MANs for mobile users who ...
... Addresses wireless MANs for mobile users who ...
XML: Part
... plaintext, allowing an attacker with a sniffer to see the MAC address of an approved device ...
... plaintext, allowing an attacker with a sniffer to see the MAC address of an approved device ...
Connecting to the RUTH ENLOW LIBRARY Wireless Internet
... Connecting to the Ruth Enlow Library Wireless Internet (WiFi) You must have a wireless adapter installed properly and enabled on your computer to connect. If your laptop computer does not connect to our network automatically, try these steps. Due to different versions of Windows and Mac operating sy ...
... Connecting to the Ruth Enlow Library Wireless Internet (WiFi) You must have a wireless adapter installed properly and enabled on your computer to connect. If your laptop computer does not connect to our network automatically, try these steps. Due to different versions of Windows and Mac operating sy ...
1998-11-19-MIEM-WirelessWANs
... Plugged bridge and fileserver into the same Ethernet hub Had to “bind” a common network address to the wireless network We used the IPX network number “314159” - in other words “the Pi in the sky” Could also have done it as one big network with everyone on it - but why? From this point on, the netwo ...
... Plugged bridge and fileserver into the same Ethernet hub Had to “bind” a common network address to the wireless network We used the IPX network number “314159” - in other words “the Pi in the sky” Could also have done it as one big network with everyone on it - but why? From this point on, the netwo ...
Wireless/Mobile Computing and Networking
... Network Platform (Chiueh) • Exploit commodity IEEE 802.11b WLAN access points (Linksys WRT54G, < $30) as building blocks for indoor wireless sensor network (WSN) applications • Use SNMP as the basic interaction protocol among wireless sensor network nodes • Provide a SQL interface and distributed qu ...
... Network Platform (Chiueh) • Exploit commodity IEEE 802.11b WLAN access points (Linksys WRT54G, < $30) as building blocks for indoor wireless sensor network (WSN) applications • Use SNMP as the basic interaction protocol among wireless sensor network nodes • Provide a SQL interface and distributed qu ...
Networking and System Administration (NaSA) Bachelor of Science in
... Security services, basics of cryptology, historical ciphers, public key paradigms, hardware and software implementations, and standard protocols used for securing mail, web, and electronic commerce. Network monitoring, intrusion detection, sensor deployment, forensics and managing services in hostil ...
... Security services, basics of cryptology, historical ciphers, public key paradigms, hardware and software implementations, and standard protocols used for securing mail, web, and electronic commerce. Network monitoring, intrusion detection, sensor deployment, forensics and managing services in hostil ...
Strawcutter
... distribution generates a new unique encryption key randomly for each client. WPA uses a message integrity code which is sometimes called “Michael” that protects against forgery attempts. When used in enterprise environments WPA can use an authentication server, usually RADIUS (Remote Authentication ...
... distribution generates a new unique encryption key randomly for each client. WPA uses a message integrity code which is sometimes called “Michael” that protects against forgery attempts. When used in enterprise environments WPA can use an authentication server, usually RADIUS (Remote Authentication ...
Test 3 Emerge Terms
... Bluetooth: enables digital devices to communicate directly with each other wirelessly over short distances. Cascading Style Sheets (CSS): allows easy application of visual styles for fonts, colors, layouts, and other page attributes to create visual themes for webpages and sites. Cellular Network: r ...
... Bluetooth: enables digital devices to communicate directly with each other wirelessly over short distances. Cascading Style Sheets (CSS): allows easy application of visual styles for fonts, colors, layouts, and other page attributes to create visual themes for webpages and sites. Cellular Network: r ...
Chapter 7 Networks and the Internet
... Communications and Security Protocols Workstations on network must all speak same language Bandwidth Capacity of transmission media Passwords Assign access rights for each user to increase security Firewalls Prevent unauthorized access ...
... Communications and Security Protocols Workstations on network must all speak same language Bandwidth Capacity of transmission media Passwords Assign access rights for each user to increase security Firewalls Prevent unauthorized access ...
Slide 1
... WEP runs a cyclic redundancy check (CRC) on the plaintext data that is to be encrypted and then appends the Integrity Check Value (ICV) to the end of the plaintext data. A 24-bit cleartext Initialization Vector (IV) is then generated and combined with the static secret key. WEP then uses both the st ...
... WEP runs a cyclic redundancy check (CRC) on the plaintext data that is to be encrypted and then appends the Integrity Check Value (ICV) to the end of the plaintext data. A 24-bit cleartext Initialization Vector (IV) is then generated and combined with the static secret key. WEP then uses both the st ...
Document
... Access point Reminder: in wireless, all equipment that can connect to a wireless network categoriezed into one of three categories: 1. access point, master, sometimes referred to as infrastructure. These are typically boxes that we’ve been configuring that have a combination of radios and wired Eth ...
... Access point Reminder: in wireless, all equipment that can connect to a wireless network categoriezed into one of three categories: 1. access point, master, sometimes referred to as infrastructure. These are typically boxes that we’ve been configuring that have a combination of radios and wired Eth ...
Wide Area Network - Clydebank High School
... A secret code that you would use to gain access to a computer. Must be changes regularly and should not be to easy. ...
... A secret code that you would use to gain access to a computer. Must be changes regularly and should not be to easy. ...
Tsou_2003AAG. ppt - Internet Mapping Services for San Diego
... – Traditional RS and GIS software are very expensive, difficult to use. – Regional program managers and park rangers seldom have the necessary resources or training to access RS/GIS data – There is a strong need to develop an easy-to-use, inexpensive set of field survey tools ...
... – Traditional RS and GIS software are very expensive, difficult to use. – Regional program managers and park rangers seldom have the necessary resources or training to access RS/GIS data – There is a strong need to develop an easy-to-use, inexpensive set of field survey tools ...
CH 8 – Review - WordPress.com
... who or what identifies a secure certificate when you go to a website – your browser a digital certificate contains a company’s private key – False what technique has been used by most high profile cyber attacks – spearfishing what does silverman consider to be the weak link in the computer security ...
... who or what identifies a secure certificate when you go to a website – your browser a digital certificate contains a company’s private key – False what technique has been used by most high profile cyber attacks – spearfishing what does silverman consider to be the weak link in the computer security ...
第2讲无线通信与网络
... Use diffused Infrared, without line-of-sight. Can connect to LAN. Standard not updated for a while. Signal can be swamped by sunlight. Bandwidth is still limited. ...
... Use diffused Infrared, without line-of-sight. Can connect to LAN. Standard not updated for a while. Signal can be swamped by sunlight. Bandwidth is still limited. ...
Mullvad Barnprogram
... Mullvad Barnprogram - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while bene ...
... Mullvad Barnprogram - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while bene ...
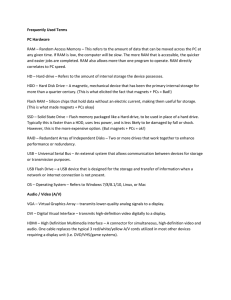
Frequently Used Terms PC Hardware RAM – Random Access
... wireless hot spot projected from a cell phone, which is obtaining internet access from either the WLAN it can receive, its own interior data plan). Bluetooth – Wireless personal area networking technology. Bluetooth is a global wireless communication standard that connects devices together over a fi ...
... wireless hot spot projected from a cell phone, which is obtaining internet access from either the WLAN it can receive, its own interior data plan). Bluetooth – Wireless personal area networking technology. Bluetooth is a global wireless communication standard that connects devices together over a fi ...
Accessing Wireless Networks Safely Brochure
... passcode or key in order to gain access. Some protocols, such as WEP and WPA, will require a password but do not provide adequate security. Make sure to identify what protocol the network is using by checking your wireless settings. ...
... passcode or key in order to gain access. Some protocols, such as WEP and WPA, will require a password but do not provide adequate security. Make sure to identify what protocol the network is using by checking your wireless settings. ...
Wi-Fi
... In the figure, node 2 can communicate with both nodes 1 and 3, but something prevents nodes 1 and 3 from communicating directly. The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance from 1 ...
... In the figure, node 2 can communicate with both nodes 1 and 3, but something prevents nodes 1 and 3 from communicating directly. The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance from 1 ...
Slide 1
... and also protect the network against malicious use. Current approaches include per-user authentication, authorization of authenticated users through access keys, and access control, a number of schemes achieve security and provide authentication at MAC are being deployed in W-Lans WEP is simple ...
... and also protect the network against malicious use. Current approaches include per-user authentication, authorization of authenticated users through access keys, and access control, a number of schemes achieve security and provide authentication at MAC are being deployed in W-Lans WEP is simple ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.