PowerPoint-10b - Community College of Rhode Island
... to broadcast the SSID, so anyone can easily join the wireless network. • Change the default SSID. Wireless AP’s have a default SSID set by the factory. Linksys wireless products use Linksys. Change the network's SSID to something unique, and make sure it doesn't refer to the networking products, you ...
... to broadcast the SSID, so anyone can easily join the wireless network. • Change the default SSID. Wireless AP’s have a default SSID set by the factory. Linksys wireless products use Linksys. Change the network's SSID to something unique, and make sure it doesn't refer to the networking products, you ...
Name: Shaikh Fahad Saeed ID: 200800652
... technology but in some time the network supplier had to shut down this operation because Verizon wireless released the second 3G network which was on October 2003 ...
... technology but in some time the network supplier had to shut down this operation because Verizon wireless released the second 3G network which was on October 2003 ...
ppt
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
... If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission ...
Wi-Fi
... • In the figure, node 2 can communicate with both nodes 1 and 3, but something prevents nodes 1 and 3 from communicating directly. • The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance fro ...
... • In the figure, node 2 can communicate with both nodes 1 and 3, but something prevents nodes 1 and 3 from communicating directly. • The obstacle itself is not relevant; it could be as simple as nodes 1 and 3 being as far away from 2 as possible, so the radio waves cannot reach the full distance fro ...
Wireless LAN Management
... modification • If the attacker spoofs as the default gateway – All machines trying to get to the network will connect to the attacker – To get passwords and necessary information ...
... modification • If the attacker spoofs as the default gateway – All machines trying to get to the network will connect to the attacker – To get passwords and necessary information ...
PowerPoint Presentation - Securing a Wireless 802.11b Network
... How easy is it to attack a wireless LAN? Very easy All an attacker needs is a laptop computer, a wireless card and some software A directional antenna will increase the range over which the attacker can access your network Directional antenna can be made from a Pringles potato chip can! Attack ...
... How easy is it to attack a wireless LAN? Very easy All an attacker needs is a laptop computer, a wireless card and some software A directional antenna will increase the range over which the attacker can access your network Directional antenna can be made from a Pringles potato chip can! Attack ...
COMP10023 - UWS Mahara
... Before a WiFi wireless router is connected to the rest of the existing network, proper configuration of the wireless router is necessary. Router firmware upgrading may also be needed for enhanced performance or functionality. a. ...
... Before a WiFi wireless router is connected to the rest of the existing network, proper configuration of the wireless router is necessary. Router firmware upgrading may also be needed for enhanced performance or functionality. a. ...
PowerPoint - 6S Global
... When the network devices are connected to each other over the Internet, they do not get connected automatically ...
... When the network devices are connected to each other over the Internet, they do not get connected automatically ...
Networking
... wireless networking standards. 802.11b is the original standard (11 Mbps). 802.11g is faster (54 Mbps) and expected to ...
... wireless networking standards. 802.11b is the original standard (11 Mbps). 802.11g is faster (54 Mbps) and expected to ...
Intrusion Prevention Systems
... • Command Line Lab on Thursday: please bring your laptops • Keep up with the reading – Midterm on March 2nd • Computer Networks Basics: OSI stack, subnets, Basic protocols: ARP, ICMP, NAT, DHCP, DNS, TCP/IP • Penetration testing: recon, scanning, exploits (ch. 1-4 of book: ”The basics of Hacking and ...
... • Command Line Lab on Thursday: please bring your laptops • Keep up with the reading – Midterm on March 2nd • Computer Networks Basics: OSI stack, subnets, Basic protocols: ARP, ICMP, NAT, DHCP, DNS, TCP/IP • Penetration testing: recon, scanning, exploits (ch. 1-4 of book: ”The basics of Hacking and ...
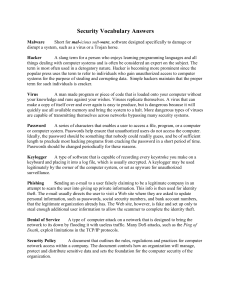
ITS_8_Security Vocab Answers
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...
Chapter 12 Outline
... b) These access points are also typically behind any security measures the companies have in place, such as firewalls and IDSs. ...
... b) These access points are also typically behind any security measures the companies have in place, such as firewalls and IDSs. ...
Chapter 4 Computer Networks – Part 2
... formatted and transmitted, and what actions Web servers and browsers should take in response to various commands HTTPS – sending data over the Internet using the Secure Socket ...
... formatted and transmitted, and what actions Web servers and browsers should take in response to various commands HTTPS – sending data over the Internet using the Secure Socket ...
ppt - CSE
... Layer 2, Layer 3 communication systems Install, test and commission voice and data communications networks in medium to large enterprises using Next Generation Networks (NGN) technologies Cover local area networks (LAN) and wide area networks (WAN), IP based protocol networks, 3G/4G cellular mobile ...
... Layer 2, Layer 3 communication systems Install, test and commission voice and data communications networks in medium to large enterprises using Next Generation Networks (NGN) technologies Cover local area networks (LAN) and wide area networks (WAN), IP based protocol networks, 3G/4G cellular mobile ...
Data Link Layer & Wireless Networking
... exceeds # wired phone subscribers! computer nets: laptops, palmtops, PDAs, Internet-enabled phone promise anytime untethered Internet access two important (but different) challenges ...
... exceeds # wired phone subscribers! computer nets: laptops, palmtops, PDAs, Internet-enabled phone promise anytime untethered Internet access two important (but different) challenges ...
tr-5a series - Baltic Networks
... EN404 Dual Radio Outdoor Wireless Mesh Router NOW AVAILABLE IN OUR IP67 / NEMA 4X CASE!! The EN404: the most cost-effective solution for delivering broadband wireless applications in outdoor environments. The EN404 uses public safety 4.9 Ghz networking for maximum range and interoperability with WiF ...
... EN404 Dual Radio Outdoor Wireless Mesh Router NOW AVAILABLE IN OUR IP67 / NEMA 4X CASE!! The EN404: the most cost-effective solution for delivering broadband wireless applications in outdoor environments. The EN404 uses public safety 4.9 Ghz networking for maximum range and interoperability with WiF ...
CH07 - Cameron School of Business
... • Local area network (LAN) - is designed to connect a group of computers in close proximity to each other such as in an office building, a school, or a home. • Wide area network (WAN) - spans a large geographic area, such as a state, province, or country • Metropolitan area network (MAN) - a large c ...
... • Local area network (LAN) - is designed to connect a group of computers in close proximity to each other such as in an office building, a school, or a home. • Wide area network (WAN) - spans a large geographic area, such as a state, province, or country • Metropolitan area network (MAN) - a large c ...
cisco.camre.ac.uk
... critical in ensuring that data is safe and secure. Having centrally managed backup system, where all the data is safely copied in case of system failure, with everyone following the same standards, is essential. Backing up data is a critical role of a network administrator. The frequency of a backup ...
... critical in ensuring that data is safe and secure. Having centrally managed backup system, where all the data is safely copied in case of system failure, with everyone following the same standards, is essential. Backing up data is a critical role of a network administrator. The frequency of a backup ...
Chapter 6: Wireless and Mobile Networks
... Background: # wireless (mobile) phone subscribers now ...
... Background: # wireless (mobile) phone subscribers now ...
Download the bC Wireless datasheet here
... (available as an option) provides retailers new freedom in their fresh food sales. The factory-installed WLAN module ensures a secure wireless connection of the bC scale to an existing network. Set up, switch on – and right away you are in the network. Vendor carts and sales stands with the METTLER ...
... (available as an option) provides retailers new freedom in their fresh food sales. The factory-installed WLAN module ensures a secure wireless connection of the bC scale to an existing network. Set up, switch on – and right away you are in the network. Vendor carts and sales stands with the METTLER ...
Wireless Digital System and its application in EMI
... Storage Oscilloscopes(DSO), and Computers Fibre Analog System ...
... Storage Oscilloscopes(DSO), and Computers Fibre Analog System ...
Wireless LAN Management
... Network hijacking and modification Denial of Service and flooding attacks ...
... Network hijacking and modification Denial of Service and flooding attacks ...
Wireless Technology
... •An access point (AP) is a WLAN device that can act as the center point of a stand-alone wireless network. •An AP can also be used as the connection point between wireless and wired networks. •In large installations, the roaming functionality provided by multiple APs allows wireless users to move fr ...
... •An access point (AP) is a WLAN device that can act as the center point of a stand-alone wireless network. •An AP can also be used as the connection point between wireless and wired networks. •In large installations, the roaming functionality provided by multiple APs allows wireless users to move fr ...
Computer Networking
... –It is not the frequency, but the wattage, the power. •Any electromagnetic wave can be dangerous with too much power. •A 25 watt light bulb is safe, but it wouldn’t be safe at 250,000 watts –Wireless access points generate signals at 1/10th of a watt. •Like all electromagnetic waves, the signal does ...
... –It is not the frequency, but the wattage, the power. •Any electromagnetic wave can be dangerous with too much power. •A 25 watt light bulb is safe, but it wouldn’t be safe at 250,000 watts –Wireless access points generate signals at 1/10th of a watt. •Like all electromagnetic waves, the signal does ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.