Slide 1
... Apply the algorithms behind some current network security protocols. Understand firewalls and their applications.. Demonstrate detailed knowledge of TCP/IP. ...
... Apply the algorithms behind some current network security protocols. Understand firewalls and their applications.. Demonstrate detailed knowledge of TCP/IP. ...
• Universal N300 Wireless Range Extender
... Connect to any wireless router & extend wireless coverage and enhance wireless signal at the poor signal or low data rate area of your existing wireless network, allowing more users enjoying high bandwidth wireless connection without cable burden & any interruption. EUROSTAR Wireless Range Extender ...
... Connect to any wireless router & extend wireless coverage and enhance wireless signal at the poor signal or low data rate area of your existing wireless network, allowing more users enjoying high bandwidth wireless connection without cable burden & any interruption. EUROSTAR Wireless Range Extender ...
Pervasive Computing - Winlab
... The first wave of telecom connected places/devices rather than people Cellular phones changed the paradigm to connecting people anytime-anywhere Consumers demonstrate a strong preference for cellular over wired services – cellular long-distance call minutes now >> wired telephones The Internet conne ...
... The first wave of telecom connected places/devices rather than people Cellular phones changed the paradigm to connecting people anytime-anywhere Consumers demonstrate a strong preference for cellular over wired services – cellular long-distance call minutes now >> wired telephones The Internet conne ...
Computer Networks
... 4.3 billion addresses with some reserved Usefulness of static addresses ...
... 4.3 billion addresses with some reserved Usefulness of static addresses ...
CEIM-Wavefront collaboration announcement
... companies in information technology, new media, clean and industrial technologies and life sciences industries. CEIM’s ’s team of consultants and coaches is multidisciplinary, with hands hands-on on business expertise. CEIM provides start-ups ups and early stage SMEs with the services they need, tai ...
... companies in information technology, new media, clean and industrial technologies and life sciences industries. CEIM’s ’s team of consultants and coaches is multidisciplinary, with hands hands-on on business expertise. CEIM provides start-ups ups and early stage SMEs with the services they need, tai ...
Skating on Stilts
... • Basic, key security measures are not widely adopted – Fewer than 60% patched and updated software on a regular schedule – User name and password the most common form of login/authentication – more than three-quarters of SCADA/ICS systems are connected to an IP network or the Internet • nearly half ...
... • Basic, key security measures are not widely adopted – Fewer than 60% patched and updated software on a regular schedule – User name and password the most common form of login/authentication – more than three-quarters of SCADA/ICS systems are connected to an IP network or the Internet • nearly half ...
Acceptable Use Policy (AUP)
... ... use moral and ethical guidelines ... regarding network use. Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that pri ...
... ... use moral and ethical guidelines ... regarding network use. Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that pri ...
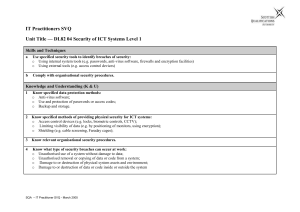
it user svq – level 2
... Know what type of security breaches can occur at work: o Unauthorised use of a system without damage to data; o Unauthorised removal or copying of data or code from a system; o Damage to or destruction of physical system assets and environment; o Damage to or destruction of data or code inside or ou ...
... Know what type of security breaches can occur at work: o Unauthorised use of a system without damage to data; o Unauthorised removal or copying of data or code from a system; o Damage to or destruction of physical system assets and environment; o Damage to or destruction of data or code inside or ou ...
Cisco Discovery 1 Module 08 Quiz Picture Descriptions
... 9. What are three security features commonly found on an ISR? Choose three: DMZ NAT SPI HTTP ...
... 9. What are three security features commonly found on an ISR? Choose three: DMZ NAT SPI HTTP ...
DoS Attacks On Wireless Voice Over IP Systems
... • wVoIP is extremely vulnerable to DoS attacks because access to the transmission medium is open to anybody with 802.11 hardware. • Because real-time traffic such as VoIP and video conferencing media is intolerable of even small delays it is relatively easy to disrupt the service long enough to make ...
... • wVoIP is extremely vulnerable to DoS attacks because access to the transmission medium is open to anybody with 802.11 hardware. • Because real-time traffic such as VoIP and video conferencing media is intolerable of even small delays it is relatively easy to disrupt the service long enough to make ...
Wireless Solutions for Developing Countries
... directional grid antenna Central site:5.58dBi or more Omni-directional antenna ...
... directional grid antenna Central site:5.58dBi or more Omni-directional antenna ...
Client/Server Networks
... • Client - a computer that is designed to request information from a server • Server - a computer that is dedicated to providing information in response to external requests – Client/server network - model for applications in which the bulk of the back-end processing takes place on a server, while t ...
... • Client - a computer that is designed to request information from a server • Server - a computer that is dedicated to providing information in response to external requests – Client/server network - model for applications in which the bulk of the back-end processing takes place on a server, while t ...
Course Learning Objectives:
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
Cradlepoint 4G LTE Parallel Networking
... Limit risk: If an employee device or third-party network is compromised, there is no risk that attackers could pivot to other servers and networks, including those that hold sensitive data. Reduce soft costs: Parallel networks often reduce an enterprise’s soft costs, including the need for complex n ...
... Limit risk: If an employee device or third-party network is compromised, there is no risk that attackers could pivot to other servers and networks, including those that hold sensitive data. Reduce soft costs: Parallel networks often reduce an enterprise’s soft costs, including the need for complex n ...
glossary - Homework Market
... accept output or both. A device can be any electronic element with some computing ability that supports the installation of firmware or third-party software. Digital Subscriber Line or Digital Subscriber Loop. Refers to the variety of different types of Digital Subscriber Line protocols – high-speed ...
... accept output or both. A device can be any electronic element with some computing ability that supports the installation of firmware or third-party software. Digital Subscriber Line or Digital Subscriber Loop. Refers to the variety of different types of Digital Subscriber Line protocols – high-speed ...
Wireless Security Update
... Cisco; LEAP provides authentication based on the Windows username and password logon (certificates are not required) EAP-TunneledTLS (EAP-TTLS) - Supports advanced authentication methods such as using tokens Protected EAP (PEAP) - Uses certificates similar to Secure Sockets Layer (SSL) with Web brow ...
... Cisco; LEAP provides authentication based on the Windows username and password logon (certificates are not required) EAP-TunneledTLS (EAP-TTLS) - Supports advanced authentication methods such as using tokens Protected EAP (PEAP) - Uses certificates similar to Secure Sockets Layer (SSL) with Web brow ...
Network hunt - Barefoot Computing
... network. Services include letting people log in to the network, running programs for you, letting you save to a shared area, and letting you print and access the internet. We don’t use this computer on a daily basis. ...
... network. Services include letting people log in to the network, running programs for you, letting you save to a shared area, and letting you print and access the internet. We don’t use this computer on a daily basis. ...
Using a Single IPv4 Global Address in DSTM
... – Recently, broadband wireless access network is emerging for wireless communication for user requirements such as high quality data/voice service, fast mobility, wide coverage, etc. – The draft extends [bb-deployment- scenarios] and uses its structure and common terminology. – Useful for IPv6 ISPs ...
... – Recently, broadband wireless access network is emerging for wireless communication for user requirements such as high quality data/voice service, fast mobility, wide coverage, etc. – The draft extends [bb-deployment- scenarios] and uses its structure and common terminology. – Useful for IPv6 ISPs ...
Network Security: It`s Time to Take It Seriously
... Security devices and measures(continued) • 2. Network intrusion detection devices This kind of devices try to detect and call attention to odd and suspicious behavior --Anomaly detection devices uses statistical methods to generate logs and alert system administrator when they detect suspicious ...
... Security devices and measures(continued) • 2. Network intrusion detection devices This kind of devices try to detect and call attention to odd and suspicious behavior --Anomaly detection devices uses statistical methods to generate logs and alert system administrator when they detect suspicious ...
Video-surveillance Citizen Network
... to save costs in time and resources and, at the same time, take advantage of the equipment to provide other services such as voice and data in future network extensions. Tarapoto has a tropical climate with high levels of humidity and severe storms, so the project also demanded rugged and robust equ ...
... to save costs in time and resources and, at the same time, take advantage of the equipment to provide other services such as voice and data in future network extensions. Tarapoto has a tropical climate with high levels of humidity and severe storms, so the project also demanded rugged and robust equ ...
PowerPoint - Community College of Rhode Island
... • ESS stations must have the same SSID • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
... • ESS stations must have the same SSID • The BSSID is the “name” of the BSS (not same as SSID) • APs can be positioned so that cells overlap to facilitate roaming – Wireless devices choose AP based on signal strength – Stations going from one BSS to another will deal with Handoff Wired LAN ...
Wireless Network Security
... ►Detect and correlate anomalies (providing visualization) ►Mitigate threats ...
... ►Detect and correlate anomalies (providing visualization) ►Mitigate threats ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.