user manual
... Dynamic IP Address: An IP address that is assigned automatically to a client station in a TCP/IP network by a DHCP server. Encryption: A security method that uses a specific algorithm to alter the data transmitted, thus prevent others from knowing the information transmitted. ESS: ESS stands for “Ex ...
... Dynamic IP Address: An IP address that is assigned automatically to a client station in a TCP/IP network by a DHCP server. Encryption: A security method that uses a specific algorithm to alter the data transmitted, thus prevent others from knowing the information transmitted. ESS: ESS stands for “Ex ...
Home Network Basics
... address – Media Access Control address – Unique address for each item on a network • Can be found in System Information under Network Adapter ...
... address – Media Access Control address – Unique address for each item on a network • Can be found in System Information under Network Adapter ...
RICON_GTech Case_Study
... Milli Piyango’s previous network was based on IP ADSL with over five thousand lotto terminal distributed right throughout Turkey. The efficiency of the system was not optimal, with slow transaction speeds on a network that had limited scalability. In order to overcome the above limitations the syste ...
... Milli Piyango’s previous network was based on IP ADSL with over five thousand lotto terminal distributed right throughout Turkey. The efficiency of the system was not optimal, with slow transaction speeds on a network that had limited scalability. In order to overcome the above limitations the syste ...
computer networks
... • Nodes that gather information they sense. • Can be part of cars or phones, etc.. Or may be small separate devices. • Example: car gather data: location, speed, vibration, and fuel efficiency and upload this information to a database. • Those data can help find potholes, plan trips around congested ...
... • Nodes that gather information they sense. • Can be part of cars or phones, etc.. Or may be small separate devices. • Example: car gather data: location, speed, vibration, and fuel efficiency and upload this information to a database. • Those data can help find potholes, plan trips around congested ...
Wireless Networks
... inherently difficult to decipher without knowing the exact hopping sequences or direct sequence codes used • The IEEE 802.11 standard specifies optional security called "Wired Equivalent Privacy" whose goal is that a wireless LAN offer privacy equivalent to that offered by a wired LAN. The standard ...
... inherently difficult to decipher without knowing the exact hopping sequences or direct sequence codes used • The IEEE 802.11 standard specifies optional security called "Wired Equivalent Privacy" whose goal is that a wireless LAN offer privacy equivalent to that offered by a wired LAN. The standard ...
Secure Streaming Media
... storage devices such as a personal video recorder or at any point in the distribution chain without any change to software or hardware of third parties. such as proxies, NATs, firewalls, caches, storage devices, and client hardware/software processes. ...
... storage devices such as a personal video recorder or at any point in the distribution chain without any change to software or hardware of third parties. such as proxies, NATs, firewalls, caches, storage devices, and client hardware/software processes. ...
Security in Wireless Networks and Devices
... module that includes either a bridge or a router. – Cross-building interconnection WLANs are connected to nearby or adjacent backbone fixed LANs in the building by either bridges or routers. – Nomadic access is a wireless link that connects a fixed LAN to a mobile IP device such as a laptop. Most wi ...
... module that includes either a bridge or a router. – Cross-building interconnection WLANs are connected to nearby or adjacent backbone fixed LANs in the building by either bridges or routers. – Nomadic access is a wireless link that connects a fixed LAN to a mobile IP device such as a laptop. Most wi ...
PPT
... framework for sensor network data acquisition, monitoring and command. In order to provide security service inside the sensor network two security protocols are implemented. The first protocol is a key establishment algorithm in which sensor nodes agree on common keys to use for securing communicati ...
... framework for sensor network data acquisition, monitoring and command. In order to provide security service inside the sensor network two security protocols are implemented. The first protocol is a key establishment algorithm in which sensor nodes agree on common keys to use for securing communicati ...
lecture 17
... Convenience and Instant Connectivity: Internetenabled mobile device makes it easy and fast to access the Web, intranets, and other mobile devices without booting up a PC or placing a call. Personalization: information can be customized and sent to individual consumers (e.g., as a short message servi ...
... Convenience and Instant Connectivity: Internetenabled mobile device makes it easy and fast to access the Web, intranets, and other mobile devices without booting up a PC or placing a call. Personalization: information can be customized and sent to individual consumers (e.g., as a short message servi ...
MESH NETWORK SIMULAION Pei Ping Belarusian National
... meetings are held here every year. If there is high-speed wireless network coverage, it could support a lot of school activities. An open area in class room provides a good environmental condition for mesh network. There are two AP – 4900M devices in classroom offering the wireless coverage indoor. ...
... meetings are held here every year. If there is high-speed wireless network coverage, it could support a lot of school activities. An open area in class room provides a good environmental condition for mesh network. There are two AP – 4900M devices in classroom offering the wireless coverage indoor. ...
Reaver
... GNU/Linux on your Android device. The application creates a disk image on the flash card, mount it and install there OS distribution. Applications of the new system are run in a chroot environment and working in parallel with platform Android. All changes made on the device are reversible, ie the ap ...
... GNU/Linux on your Android device. The application creates a disk image on the flash card, mount it and install there OS distribution. Applications of the new system are run in a chroot environment and working in parallel with platform Android. All changes made on the device are reversible, ie the ap ...
Fy `08 NETWORK PLANNING TASK FORCE
... Bluesocket devices are over 4 years old The replacement costs were not embedded in the CSF. (One-time monies provided by ISC centrally.) We anticipated using a different authentication method prior to replacement. 95% of non-residential wireless users still use web-based authentication. Bluesock ...
... Bluesocket devices are over 4 years old The replacement costs were not embedded in the CSF. (One-time monies provided by ISC centrally.) We anticipated using a different authentication method prior to replacement. 95% of non-residential wireless users still use web-based authentication. Bluesock ...
Networks
... Network servers that manage the networks and host applications that are shared with client computers Two types: Two-tiered Three-tiered ...
... Network servers that manage the networks and host applications that are shared with client computers Two types: Two-tiered Three-tiered ...
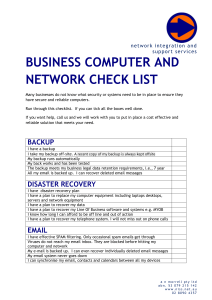
business computer and network check list
... Many businesses do not know what security or systems need to be in place to ensure they have secure and reliable computers. Run through this checklist. If you can tick all the boxes well done. If you want help, call us and we will work with you to put in place a cost effective and reliable solution ...
... Many businesses do not know what security or systems need to be in place to ensure they have secure and reliable computers. Run through this checklist. If you can tick all the boxes well done. If you want help, call us and we will work with you to put in place a cost effective and reliable solution ...
Acceptable Use Policy (AUP)
... ... use moral and ethical guidelines ... regarding network use. Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that pri ...
... ... use moral and ethical guidelines ... regarding network use. Students are expected to use moral and ethical guidelines in making appropriate decisions regarding network use. Use of the district network is not a right, but a privilege, and inappropriate use will result in cancellation of that pri ...
Ad-Hoc Wireless Networks
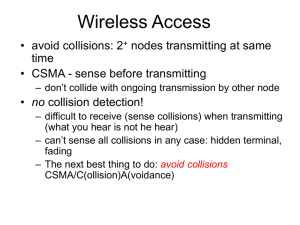
... IEEE 802.11 Wireless LAN The principles of Wireless Local Area Network (WLAN) are defined in IEEE 802.11 standard • It defines two different topologies: ad-hoc network and infrastructure network ...
... IEEE 802.11 Wireless LAN The principles of Wireless Local Area Network (WLAN) are defined in IEEE 802.11 standard • It defines two different topologies: ad-hoc network and infrastructure network ...
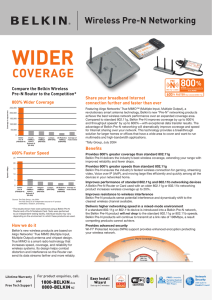
coverage
... Source: The Tolly Group, July 2004. The Tolly Group is an independent source for IT product certification, research, and testing. ...
... Source: The Tolly Group, July 2004. The Tolly Group is an independent source for IT product certification, research, and testing. ...
Cryptography and Network Security
... With effect from the academic year 2015-16 UNIT-V Applications: Kerberos, Web Security Protocols ( SSL ), IPSec, Electronic Payments, E-cash, Secure Electronic Transaction (SET), Micro Payments, Case Studies of Enterprise Security (.NET and J2EE). ...
... With effect from the academic year 2015-16 UNIT-V Applications: Kerberos, Web Security Protocols ( SSL ), IPSec, Electronic Payments, E-cash, Secure Electronic Transaction (SET), Micro Payments, Case Studies of Enterprise Security (.NET and J2EE). ...
1.Which of the following are true LAN and WAN differ in area they
... 12.When new improvements are made to software that is being used which of the tools need updates Vulnerability Assessment tools 13.Operating system attack used by hacker uses misconfiguration in systems 14.The controlling mechanism used to hide real location of a machine Routing Control 15.Making fa ...
... 12.When new improvements are made to software that is being used which of the tools need updates Vulnerability Assessment tools 13.Operating system attack used by hacker uses misconfiguration in systems 14.The controlling mechanism used to hide real location of a machine Routing Control 15.Making fa ...
Networks
... Questions What does networking mean to you? What types of networks do you know about? What does PAN, MAN, LAN, WLAN, WAN mean? ...
... Questions What does networking mean to you? What types of networks do you know about? What does PAN, MAN, LAN, WLAN, WAN mean? ...
presentation source
... than one domain. – If A trusts C, users in C can access resources in A (one-way) – two-way trusts : users of both both can access the other ...
... than one domain. – If A trusts C, users in C can access resources in A (one-way) – two-way trusts : users of both both can access the other ...
Crime and Security in the Networked Economy Part 4
... Encrypting Communications Increases Security ...
... Encrypting Communications Increases Security ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.