3.01a_Network Technology - fitslm
... Definition • Able to connect computers to other computers and printers the same way a wired network is, but without wires. Features: • Range (Depends on factors such as wireless card, access point, and obstacles in between) • Cost (Wireless price is dependent upon the complexity of the setup.) • Eas ...
... Definition • Able to connect computers to other computers and printers the same way a wired network is, but without wires. Features: • Range (Depends on factors such as wireless card, access point, and obstacles in between) • Cost (Wireless price is dependent upon the complexity of the setup.) • Eas ...
Wireless Audio Conferencing System (WACS)
... Why we used RTP? TCP is not an appropriate choice for carrying real-time multimedia contents ...
... Why we used RTP? TCP is not an appropriate choice for carrying real-time multimedia contents ...
Remote Access - York Technical College
... Provides low-cost (as compared to leased line) secure network connection Point to point dedicated link over a public IP network Creates a connection between two computers Uses PPP ...
... Provides low-cost (as compared to leased line) secure network connection Point to point dedicated link over a public IP network Creates a connection between two computers Uses PPP ...
Section 5A
... Topology: Physical or logical layout of cables and devices that connect the network nodes Media: wires and cables that carry data from source to destination Bandwidth: amount of data media can ...
... Topology: Physical or logical layout of cables and devices that connect the network nodes Media: wires and cables that carry data from source to destination Bandwidth: amount of data media can ...
CNG 131 – Principles of Information Assurance Provides students
... studied, including remote access, e-mail, the Web, directory and file transfer, and wireless data. Common network attacks are introduced. Cryptography basics are incorporated, and operational/organizational security is discussed as it relates to physical security, disaster recovery, and business con ...
... studied, including remote access, e-mail, the Web, directory and file transfer, and wireless data. Common network attacks are introduced. Cryptography basics are incorporated, and operational/organizational security is discussed as it relates to physical security, disaster recovery, and business con ...
3Com® OfficeConnect® ADSL Wireless 11g Firewall
... Advanced wireless security and multiple firewall features offer the highest levels of protection for the network. To shield wireless connections, the ADSL Wireless 11g Firewall Router implements 256-bit WPA encryption for maximum security, along with 40/64- & 128-bit WEP encryption for legacy client ...
... Advanced wireless security and multiple firewall features offer the highest levels of protection for the network. To shield wireless connections, the ADSL Wireless 11g Firewall Router implements 256-bit WPA encryption for maximum security, along with 40/64- & 128-bit WEP encryption for legacy client ...
Attacking 802.11 Networks
... • “Crunchy on the outside, soft and chewy on the inside” – Mentos Network Design – Common to many organizations with few security resources to manage client devices – Attacker uses stepping-stone attacks ...
... • “Crunchy on the outside, soft and chewy on the inside” – Mentos Network Design – Common to many organizations with few security resources to manage client devices – Attacker uses stepping-stone attacks ...
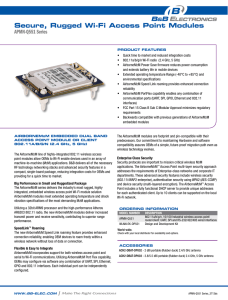
apMn-Q551
... point modules allow OEMs to Wi-Fi enable devices used in an array of machine-to-machine (M2M) applications. B&B delivers all of the necessary RF technology networking stacks and advanced security features in a compact, single-board package, reducing integration costs for OEMs and providing for a qui ...
... point modules allow OEMs to Wi-Fi enable devices used in an array of machine-to-machine (M2M) applications. B&B delivers all of the necessary RF technology networking stacks and advanced security features in a compact, single-board package, reducing integration costs for OEMs and providing for a qui ...
1 Course Outline Computing Science Department Faculty of Science
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
... Students learn about computer network design principles and concepts, network architecture, Open Systems Interconnection (OSI) model, error detection and recovery, local area networks, bridges, routers and gateways, network naming and addressing, routing protocols, internetworking, wireless networks ...
Wireless Network - Optimal Resume at KAPLAN UNIVERSITY
... number of communications links and cost. Multiplexing is used to long-distance phone lines with many phones call and high-speed signal transmitted on a single long-distance phone line It has multiple input switch and single output switch. Network Security The business organization needs to protect t ...
... number of communications links and cost. Multiplexing is used to long-distance phone lines with many phones call and high-speed signal transmitted on a single long-distance phone line It has multiple input switch and single output switch. Network Security The business organization needs to protect t ...
common network terms - Amazon Web Services
... Media Access Control (MAC) address. A standardized address that is required for every device that connects to a LAN. It is used by the connecting switch to allow communication. MAC address is a unique value associated with a network adapter. MAC addresses are also known as hardware addresses or phys ...
... Media Access Control (MAC) address. A standardized address that is required for every device that connects to a LAN. It is used by the connecting switch to allow communication. MAC address is a unique value associated with a network adapter. MAC addresses are also known as hardware addresses or phys ...
Module 2 - Santa Fe College
... Wired Equivalent Privacy was designed to provide wireless connections with the same security as wired connections. WEP has the following weaknesses: ...
... Wired Equivalent Privacy was designed to provide wireless connections with the same security as wired connections. WEP has the following weaknesses: ...
trustees/15.reso.Campus Residence Halls Network Upgrade
... mission and goals.” The upgrade would greatly improve the ISU student experience, which could assist in the recruitment and retention of students. In addition, ISU staff hours spent troubleshooting current network issues caused by outdated and insufficient equipment would be reduced. The underserved ...
... mission and goals.” The upgrade would greatly improve the ISU student experience, which could assist in the recruitment and retention of students. In addition, ISU staff hours spent troubleshooting current network issues caused by outdated and insufficient equipment would be reduced. The underserved ...
www.sunvistacomputerclub.com
... capability, which can be very handy; however, always remember that the device is a radio. Whatever it broadcasts can be seen by any receiver tuned to that channel. This presentation will cover how to protect your own (private) network, and how to protect yourself when you use a public network. ...
... capability, which can be very handy; however, always remember that the device is a radio. Whatever it broadcasts can be seen by any receiver tuned to that channel. This presentation will cover how to protect your own (private) network, and how to protect yourself when you use a public network. ...
ppt in chapter 11
... to large enterprise networks, the various strategies Internal Routers for security are based on a some recipe of internal and perimeter routers plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, ...
... to large enterprise networks, the various strategies Internal Routers for security are based on a some recipe of internal and perimeter routers plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, ...
Ethernet switches, hubs, etc
... • Reconstruct the ‘real’ bits from selected chips – Allows multiple stations to ‘talk’ at the same time • By using different ‘chips’ they don’t interfere with each others’ transmissions – 54 Mbps/2.4 GHz carrier signal = 44 separate ‘channels’ ...
... • Reconstruct the ‘real’ bits from selected chips – Allows multiple stations to ‘talk’ at the same time • By using different ‘chips’ they don’t interfere with each others’ transmissions – 54 Mbps/2.4 GHz carrier signal = 44 separate ‘channels’ ...
Summary of the project: About Bajaj Capital
... They were using mix switching product line i.e. Linksys and Dlink for their network. No Security Gateway device was used at perimeter level and no restrictions were there for inbound and outbound traffic as, they were using Public IP on the servers to access the applications over internet for remote ...
... They were using mix switching product line i.e. Linksys and Dlink for their network. No Security Gateway device was used at perimeter level and no restrictions were there for inbound and outbound traffic as, they were using Public IP on the servers to access the applications over internet for remote ...
Slides for lecture 26
... – E.g., consider a user connecting to a website from a café (over a wireless network) – End-to-end encryption might be unavailable (e.g., if website does not support encryption) – Eavesdropping on Internet backbone less likely than eavesdropping on wireless link in café – Encrypt link from user to w ...
... – E.g., consider a user connecting to a website from a café (over a wireless network) – End-to-end encryption might be unavailable (e.g., if website does not support encryption) – Eavesdropping on Internet backbone less likely than eavesdropping on wireless link in café – Encrypt link from user to w ...
Wireless and Mobile Networks Part I
... base station typically connected to wired network relay - responsible for sending packets between wired network and wireless host(s) in its “area” e.g., cell towers 802.11 access points ...
... base station typically connected to wired network relay - responsible for sending packets between wired network and wireless host(s) in its “area” e.g., cell towers 802.11 access points ...
Slides: Chap6
... exceeds # wired phone subscribers! computer nets: laptops, palmtops, PDAs, Internet-enabled phone promise anytime untethered Internet access two important (but different) challenges ...
... exceeds # wired phone subscribers! computer nets: laptops, palmtops, PDAs, Internet-enabled phone promise anytime untethered Internet access two important (but different) challenges ...
[PDF]
... effective scope and the client can receive the SSID by scanning, and immediately get access to wireless LAN. At present, a user usually owns his or her own client system. Since a lot of people know SSID, it is easy to be shared by illegal users. Meanwhile, many public wireless routers or AP set the ...
... effective scope and the client can receive the SSID by scanning, and immediately get access to wireless LAN. At present, a user usually owns his or her own client system. Since a lot of people know SSID, it is easy to be shared by illegal users. Meanwhile, many public wireless routers or AP set the ...
file - ScholarSphere
... and mitigate the risks to an organization’s digital assets, and provide strategies for sustaining the security of those assets. [5] Risk assessment involves the use of an evaluative and often functional methodology to assess the type and level of risks that an organization must mitigate. How many of ...
... and mitigate the risks to an organization’s digital assets, and provide strategies for sustaining the security of those assets. [5] Risk assessment involves the use of an evaluative and often functional methodology to assess the type and level of risks that an organization must mitigate. How many of ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.














![[PDF]](http://s1.studyres.com/store/data/008812149_1-3b4a796a6bb782026ebeb65f734ec49f-300x300.png)