* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download PPT
Computer network wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Automated airport weather station wikipedia , lookup
Network tap wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Airborne Networking wikipedia , lookup
Distributed firewall wikipedia , lookup
Wireless security wikipedia , lookup
.Sense
A Secure Framework for Sensor Network Data Acquisition, Monitoring and Command
M. Salajegheh, H. Soroush, A. Thomos, T. Dimitriou, I. Krontiris
Algorithms and Security Lab
{msal, hsor, ntom, tdim, ikro}@ait.edu.gr
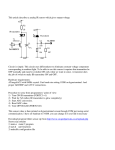
Architecture Overview
Abstract
We present .Sense, an end-to-end security
framework for sensor network data
acquisition, monitoring and command. In
order to provide security service inside the
sensor network two security protocols are
implemented. The first protocol is a key
establishment algorithm in which sensor
nodes agree on common keys to use for
securing communications among them.
The second is a scheme in which the base
station is able to issue commands in
authenticated manner to the network. We
are also using typical security schemes
such as SSL to connect the end-users to the
system.
Primary
.Sense is a distributed
Web server
Back-up
system which acts as a tool
Web server
ation
c
i
t
n
e
for sensor network data
Auth
acquisition and command
Primary
Back-up
Database
Data
IP
Database
A
providing a transparent endcq u i s
ition
NETWORK
to-end security service.
Client
.Sense was designed with
Sensor
the following characteristics Administrator
Command
Network
Base Station
in mind:
Security: The system provides data integrity, confidentiality and authentication.
Fault-tolerance: The system handles potential faults of its various components.
Distributed access to sensed information: The system allows concurrent access to
sensed data according to user privileges.
Friendly GUI: The system can be easily used by non-advanced users.
Scalability: It scales to thousands of sensor nodes. Supports addition/revocation.
Advantages
Security Features
• First sensor network deployment with
emphasis on fault-tolerance and end-to-end
security.
.Sense provides end-to-end security for the user. For the security inside the
sensor network we have designed and implemented a security library that can
be wired and used by any other application.
• Our generic library for security inside the
sensor network can be used by other TinyOS
programmers. It provides key establishment,
encryption and decryption commands.
Key Establishment Each Sensor node establishes three kinds of keys: a NodeBase key that can be used for communication with the base station, pair-wise
keys for immediate communication with neighbors and a group key that
allows secure one to many communications. These keys provide flexibility in
the application level security.
• Two interfaces: A web-based interface for
users, showing real-time and history graphs
and administrator interface showing network
connectivity and allow issuing of commands
and user management.
• Database Resolution: Apart from the sensor
network sample rate, there are two more
virtual sample rates. It increases the end user
GUI performance.
Encryption/Decryption For encryption and decryption, we use Skipjack security
algorithm using CBC mode. In the base station of the WSN, received
encrypted messages are decrypted before being sent to the UART port. This
leads to easier and more efficient implementation. A new secure TOS Base
had to be implemented in order to achieve this goal.
Command Authentication We use hash chains to authenticate commands. Sensors
will be preloaded with the first key of the hash chain. When the base station
needs to issue the next command, it releases the next key of the hash chain
which sensors can check for authenticity.
Screenshots
End User GUI
Administrator GUI