* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Remote Access Policy
Security-focused operating system wikipedia , lookup
Trusted Computing wikipedia , lookup
Mobile security wikipedia , lookup
Computer security wikipedia , lookup
Distributed firewall wikipedia , lookup
Access control wikipedia , lookup
Wireless security wikipedia , lookup
Computer and network surveillance wikipedia , lookup
Unix security wikipedia , lookup
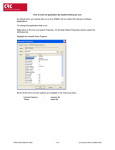
Remote Access Policy What is Remote Access??? The ability to access a computer or a network from a remote site. Communication with a distant computer system or computer network. May require the user to type or enter an authorized username and password, and special software or hardware, such as a modem. Examples of Remote Access Go to My PC Allows User to connect to any PC in his/her online account. Tight VNC- A program similar to Go to My PC, but not readily accessible through a webpage. Tight VNC- What is VNC? VNC (an abbreviation for Virtual Network Computing) is a great client/server software package allowing remote network access to graphical desktops. With VNC, you can access your machine from everywhere provided that your machine is connected to the Internet. VNC is free (released under the GNU General Public License) and it's available on most platforms. Original VNC distribution can be obtained at this site. Tight VNC is… A program that runs a VNC server and allows you to connect through other computers Via VNC. More Examples FTP The Internet Wireless Network Access/Ethernet Accessing Company Intranet from outside company. Vulnerabilities/Security Risks In class we have gone over the security risks of the internet- viruses, hackers, etc. Running things like a Win VNC Server increase the risk of your computer getting hacked, especially if there is a listener and the password is easy to crack. SANS Policy of Remote Access The purpose of this policy is to define standards for connecting to a company’s network from any host. These standards are designed to minimize the potential exposure to the company from damages which may result from unauthorized use of resources. Damages include the loss of sensitive or company confidential data, intellectual property, damage to public image, damage to critical the company’s internal systems, etc. The Rules to Follow Basically, the rules follow the same standard for connect to pretty much any network, and basic computer care. SANS asks that you also review the: Acceptable Encryption, Virtual Private Network (VPN), Wireless Communications, & Acceptable Use Policies Some of them: Secure remote access must be strictly controlled. Control will be enforced via one-time password authentication or public/private keys with strong passphrases At no time should any employee provide their login or email password to anyone, not even family members. … Use the most up-to-date anti-virus software Do not check non-corporate e-mail Conduct no illegal activities