SonicWALL GMS/UMA 6.0 Administrator`s Guide
... Except for the warranties provided hereunder, to the maximum extent permitted by applicable law, in no event shall SonicWALL or its suppliers/licensors be liable for any special, incidental, indirect, or consequential damages for lost business profits, business interruption, loss of business informa ...
... Except for the warranties provided hereunder, to the maximum extent permitted by applicable law, in no event shall SonicWALL or its suppliers/licensors be liable for any special, incidental, indirect, or consequential damages for lost business profits, business interruption, loss of business informa ...
National IPv6 Deployment Roadmap ver II
... The Internet Protocol (IP) is basically a communications protocol used for relaying packets of data across a network. The most part of present day Internet, which has today become indispensable for socio economic activities, runs on IPv4 i.e. Internet Protocol version 4.It is about 27 year old proto ...
... The Internet Protocol (IP) is basically a communications protocol used for relaying packets of data across a network. The most part of present day Internet, which has today become indispensable for socio economic activities, runs on IPv4 i.e. Internet Protocol version 4.It is about 27 year old proto ...
Ec-council.Examsheets.312-50.v2014-02-04.by.Batista
... Anonymizer sites access the Internet on your behalf, protecting your personal information from disclosure. An anonymizer protects all of your computer's identifying information while it surfs for you, enabling you to remain at least one step removed from the sites you visit. You can visit Web sites ...
... Anonymizer sites access the Internet on your behalf, protecting your personal information from disclosure. An anonymizer protects all of your computer's identifying information while it surfs for you, enabling you to remain at least one step removed from the sites you visit. You can visit Web sites ...
BrainDumps.CISA_1178.QA Isaca CISA Certified
... A firewall is a set of related programs, located at a network gateway server, that protects the resources of a private network from users of other networks. An enterprise with an intranet that allows its workers access to the wider Internet installs a firewall to prevent outsiders from accessing its ...
... A firewall is a set of related programs, located at a network gateway server, that protects the resources of a private network from users of other networks. An enterprise with an intranet that allows its workers access to the wider Internet installs a firewall to prevent outsiders from accessing its ...
Programs Panel
... The main portion of the Programs panel is the Program List. This is the list of programs installed on your machine that have attempted to connect to the Internet. Use this panel to control the connection behavior of any program on the list or to add programs to the Program List before they try to co ...
... The main portion of the Programs panel is the Program List. This is the list of programs installed on your machine that have attempted to connect to the Internet. Use this panel to control the connection behavior of any program on the list or to add programs to the Program List before they try to co ...
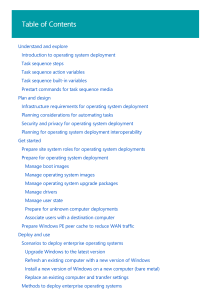
Deployment Solution 6.5 Reference Guide
... Client Connectivity and Network Adapters . . . . . . . . . . . . . Installing the Deployment Agent on Windows . . . . . . . . . . Remote Agent Installer . . . . . . . . . . . . . . . . . . . . . . . . . . Enter administrator account information . . . . . . . . . . . Specify install directory . . . . ...
... Client Connectivity and Network Adapters . . . . . . . . . . . . . Installing the Deployment Agent on Windows . . . . . . . . . . Remote Agent Installer . . . . . . . . . . . . . . . . . . . . . . . . . . Enter administrator account information . . . . . . . . . . . Specify install directory . . . . ...
PASS4sure 312-50 .910q
... A. There are two external DNS Servers for Internet domains. Both are AD integrated. This is the correct answer. Having an AD integrated DNS external server is a serious cause for alarm. There is no need for this and it causes vulnerability on the network. B. All external DNS is done by an ISP. This ...
... A. There are two external DNS Servers for Internet domains. Both are AD integrated. This is the correct answer. Having an AD integrated DNS external server is a serious cause for alarm. There is no need for this and it causes vulnerability on the network. B. All external DNS is done by an ISP. This ...
Pass4sure.312-50v8.892.QA
... But he still receives hundreds of thousands brute-force attempts generated from various IP addresses around the world. After some investigation he realizes that the intruders are using a proxy somewhere else on the Internet which has been scripted to enable the random usage of various proxies on eac ...
... But he still receives hundreds of thousands brute-force attempts generated from various IP addresses around the world. After some investigation he realizes that the intruders are using a proxy somewhere else on the Internet which has been scripted to enable the random usage of various proxies on eac ...
Pass4sure.312-50v8.870.QA
... text= If an attacker can trick a victim user to click a link like this, and the Web application does not validate input, then the victim's browser will pop up an alert showing the users current set of cookies. An attacker can do much more damage, including stea ...
... text= If an attacker can trick a victim user to click a link like this, and the Web application does not validate input, then the victim's browser will pop up an alert showing the users current set of cookies. An attacker can do much more damage, including stea ...
HP Officejet Pro 8600 User Guide– ENWW
... Install the accessories..............................................................................................................29 Install the automatic two-sided printing accessory (duplexer)............................................29 Install Tray 2.......................................... ...
... Install the accessories..............................................................................................................29 Install the automatic two-sided printing accessory (duplexer)............................................29 Install Tray 2.......................................... ...
HP Officejet Pro 8600 (N911) Printer - ENWW
... Install the accessories..............................................................................................................29 Install the duplexer.............................................................................................................29 Install Tray 2.................. ...
... Install the accessories..............................................................................................................29 Install the duplexer.............................................................................................................29 Install Tray 2.................. ...
Deployment and Installation Center
... Every effort has been made to ensure the accuracy of this manual. However, Websense Inc. makes no warranties with respect to this documentation and disclaim any implied warranties of merchantability and fitness for a particular purpose. Websense Inc. shall not be liable for any error or for incident ...
... Every effort has been made to ensure the accuracy of this manual. However, Websense Inc. makes no warranties with respect to this documentation and disclaim any implied warranties of merchantability and fitness for a particular purpose. Websense Inc. shall not be liable for any error or for incident ...
Design PDF
... CM to provide rich telepresence services, and also supports on-premises and cloud applications, as well as interoperability with third-party unified communications, IP telephony networks, and VoIP systems. The Cisco TelePresence EX Series is an all-in-one tool that streamlines the desktop so you can ...
... CM to provide rich telepresence services, and also supports on-premises and cloud applications, as well as interoperability with third-party unified communications, IP telephony networks, and VoIP systems. The Cisco TelePresence EX Series is an all-in-one tool that streamlines the desktop so you can ...
Introduction to operating system deployment | Microsoft Docs
... available in the Software Center. Configuration Manager clients can initiate the operating system installation from Software Center. For more information, see Replace an existing computer and transfer settings. Multicast deployments: Multicast deployments conserve network bandwidth by concurrently s ...
... available in the Software Center. Configuration Manager clients can initiate the operating system installation from Software Center. For more information, see Replace an existing computer and transfer settings. Multicast deployments: Multicast deployments conserve network bandwidth by concurrently s ...
Configuring an alert filter
... Copyright © 2000–2010 by TriGeo® Network Security, Inc. TriGeo® is a registered trademark of TriGeo Network Security, Inc. TriGeo SIM™, nDepth™, nSight™, and USB-Defender™ are trademarks of TriGeo Network Security, Inc. All other company names, products, services, trademarks, or registered trademark ...
... Copyright © 2000–2010 by TriGeo® Network Security, Inc. TriGeo® is a registered trademark of TriGeo Network Security, Inc. TriGeo SIM™, nDepth™, nSight™, and USB-Defender™ are trademarks of TriGeo Network Security, Inc. All other company names, products, services, trademarks, or registered trademark ...
SolarWinds NetFlow Traffic Analyzer Administrator Guide
... If you need to know how and by whom your bandwidth is being used, SolarWinds NTA provides a simple, integrated answer. You can quickly trace and monitor the bandwidth usage of a particular application or type of traffic. For example, if you see excessive bandwidth use on a particular interface, you ...
... If you need to know how and by whom your bandwidth is being used, SolarWinds NTA provides a simple, integrated answer. You can quickly trace and monitor the bandwidth usage of a particular application or type of traffic. For example, if you see excessive bandwidth use on a particular interface, you ...
Welcome to WinGate by Qbik
... MANAGING CLIENT RESERVATIONS ...........................................................................................................88 ADDING A CLIENT RESERVATION ...............................................................................................................90 ASSIGNING DHCP CONF ...
... MANAGING CLIENT RESERVATIONS ...........................................................................................................88 ADDING A CLIENT RESERVATION ...............................................................................................................90 ASSIGNING DHCP CONF ...
MCSE: Windows 2000 Professional Study Guide Second Edition
... So what “new and improved” material will you find in this new edition? We have confidence in the core instructional material in the books, so the authors have made only minor modifications to this content. They have, however, made the chapter review questions and bonus exam questions more challengin ...
... So what “new and improved” material will you find in this new edition? We have confidence in the core instructional material in the books, so the authors have made only minor modifications to this content. They have, however, made the chapter review questions and bonus exam questions more challengin ...
Check Point Embedded NGX CLI Reference Guide
... intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users. This General Public License applies to most of the Free Software Foundation's software and to any other program whose authors commit to using it. (Some other Free Software Found ...
... intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users. This General Public License applies to most of the Free Software Foundation's software and to any other program whose authors commit to using it. (Some other Free Software Found ...
PVS 4.2 User Guide - Tenable Network Security
... Operating Systems Section ................................................................................................................................................................................47 Connections Section ........................................................................... ...
... Operating Systems Section ................................................................................................................................................................................47 Connections Section ........................................................................... ...
TRITON - Web Security Help, v7.7
... Security threats: Content security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 193 Security threats: File analysis . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 194 ...
... Security threats: Content security . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 193 Security threats: File analysis . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 194 ...
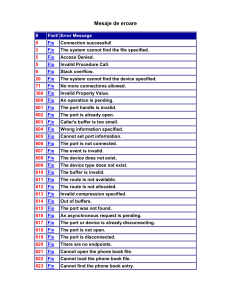
Mesaje de eroare
... Network Address Translation (NAT) is currently installed as a 782 N/A routing protocol, and must be removed before enabling Internet Connection Sharing Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disc ...
... Network Address Translation (NAT) is currently installed as a 782 N/A routing protocol, and must be removed before enabling Internet Connection Sharing Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disc ...
Implementing, Managing, and Maintaining a Microsoft
... United States and/or other countries. Other product and company names mentioned herein may be the trademarks of their ...
... United States and/or other countries. Other product and company names mentioned herein may be the trademarks of their ...