SIP Trunking Benefits and Best Practices
... you extend VoIP outside of the corporate LAN. In terms of infrastructure purchases, SIP trunks provide an immediate cost-savings. They eliminate the need to purchase costly BRIs, PRIs or PSTN gateways. The productivity benefits with SIP and SIP trunking are also significant. By extending the SIP cap ...
... you extend VoIP outside of the corporate LAN. In terms of infrastructure purchases, SIP trunks provide an immediate cost-savings. They eliminate the need to purchase costly BRIs, PRIs or PSTN gateways. The productivity benefits with SIP and SIP trunking are also significant. By extending the SIP cap ...
Contents - Ad
... Contents Using This Guide ............................................................................................................................................................. 5 Purpose and Intended Audience..................................................................................... ...
... Contents Using This Guide ............................................................................................................................................................. 5 Purpose and Intended Audience..................................................................................... ...
Online Help Center Home
... information about the main features of the software. You should read through it prior to installing or using the software. For technical support, please refer to the Technical Support and Troubleshooting chapter for information and contact details. Detailed information about how to use specific feat ...
... information about the main features of the software. You should read through it prior to installing or using the software. For technical support, please refer to the Technical Support and Troubleshooting chapter for information and contact details. Detailed information about how to use specific feat ...
User Manual - D-Link
... 3.4.4. Static and Published ARP Entries ....................................................69 ...
... 3.4.4. Static and Published ARP Entries ....................................................69 ...
Addressing Operational Challenges in Named Data Networking
... page, latest tweets on a particular topic, or a Netflix movie. Many complexities and kludges have been introduced to mitigate this inherent misalignment between the existing Internet architecture and its primary use today, such as DNS-based redirection towards content delivery networks [NSS10], load ...
... page, latest tweets on a particular topic, or a Netflix movie. Many complexities and kludges have been introduced to mitigate this inherent misalignment between the existing Internet architecture and its primary use today, such as DNS-based redirection towards content delivery networks [NSS10], load ...
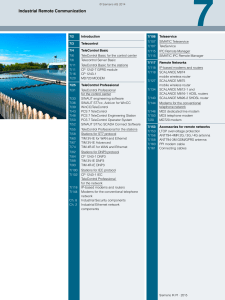
Industrial Remote Communication
... In addition to efficient remote access (Remote Access), Industrial Remote Communication also offers with the network components the option of transparent data links to remote networks via public or private wide area networks (WAN). In this way, for example, a video transmission in real time via mobi ...
... In addition to efficient remote access (Remote Access), Industrial Remote Communication also offers with the network components the option of transparent data links to remote networks via public or private wide area networks (WAN). In this way, for example, a video transmission in real time via mobi ...
Firewalls - Andrew.cmu.edu - Carnegie Mellon University
... Violations are activities or behaviors not permitted in the policy • these can be either explicit or implied ...
... Violations are activities or behaviors not permitted in the policy • these can be either explicit or implied ...
What is network management?
... Provides a basic command-line utility with which to retrieve information from any SNMP agent in your network. This example of a management application was developed using the Management API. ...
... Provides a basic command-line utility with which to retrieve information from any SNMP agent in your network. This example of a management application was developed using the Management API. ...
Root - Near East University
... Almost all Windows 2000 tasks involve working with files and folders. The work you do with files and folders falls into three categories: 1. You can perform basic file and folder tasks, such as creating, deleting, copying, and moving files and folders, and more advanced tasks, such as changing file ...
... Almost all Windows 2000 tasks involve working with files and folders. The work you do with files and folders falls into three categories: 1. You can perform basic file and folder tasks, such as creating, deleting, copying, and moving files and folders, and more advanced tasks, such as changing file ...
Server 2
... Note: This guide is a reference for a series of products. Therefore some features or options in this guide may not be available in your product. Graphics in this book may differ slightly from the product due to differences in operating systems, operating system versions, or if you installed updated ...
... Note: This guide is a reference for a series of products. Therefore some features or options in this guide may not be available in your product. Graphics in this book may differ slightly from the product due to differences in operating systems, operating system versions, or if you installed updated ...
Review Questions
... knowledge as well as gaining exposure to many different environments and cultures along the way. His broad knowledge and easy-to-understand manner, along with a healthy dose of humor, have led to Sean being a regularly requested instructor. Outside of training and consulting, Sean is also a best-sel ...
... knowledge as well as gaining exposure to many different environments and cultures along the way. His broad knowledge and easy-to-understand manner, along with a healthy dose of humor, have led to Sean being a regularly requested instructor. Outside of training and consulting, Sean is also a best-sel ...
The Quest for Artificial Intelligence
... All Dressed Up and Places to Go . . . . . . . . . . . . . . . . . . 143 ...
... All Dressed Up and Places to Go . . . . . . . . . . . . . . . . . . 143 ...
(SIP).
... Solved by doing Authentication User identify must be a valid email address System generates a password for the user identify and sends it to the email address Using MD5 hash function ...
... Solved by doing Authentication User identify must be a valid email address System generates a password for the user identify and sends it to the email address Using MD5 hash function ...
View PDF - CiteSeerX
... embedded and gives meaning to this sytem through its implementation. This feature denotes that ICTs are particularly mobile and mutable compared with other technologies, expressed through the malleability of software languages and source code, and exposed to diverse and changing implementation envir ...
... embedded and gives meaning to this sytem through its implementation. This feature denotes that ICTs are particularly mobile and mutable compared with other technologies, expressed through the malleability of software languages and source code, and exposed to diverse and changing implementation envir ...
Reference - Network Security Administrator/Specialist
... who among us is typical? Each of us approaches infosec with distinctive training and skill. Still, before you spend your hard-earned money on this book, we will try to describe the target reader. As an example, you might enjoy this book if you already have experience with networking and are able to ...
... who among us is typical? Each of us approaches infosec with distinctive training and skill. Still, before you spend your hard-earned money on this book, we will try to describe the target reader. As an example, you might enjoy this book if you already have experience with networking and are able to ...
Hack The Stack Using Snort And Ethereal To Master
... There is no guarantee of any kind, expressed or implied, regarding the Work or its contents.The Work is sold AS IS and WITHOUT WARRANTY.You may have other legal rights, which vary from state to state. In no event will Makers be liable to you for damages, including any loss of profits, lost savings, ...
... There is no guarantee of any kind, expressed or implied, regarding the Work or its contents.The Work is sold AS IS and WITHOUT WARRANTY.You may have other legal rights, which vary from state to state. In no event will Makers be liable to you for damages, including any loss of profits, lost savings, ...
MCSE Traing Guide Networking Essentials
... computers in a distributed computing environment to share processing power in addition to data, resources, and services. In a collaborative computing environment, one computer might borrow processing power by running a program on another computer on the network. Or, processes might be designed so th ...
... computers in a distributed computing environment to share processing power in addition to data, resources, and services. In a collaborative computing environment, one computer might borrow processing power by running a program on another computer on the network. Or, processes might be designed so th ...
computer networking a top down approach pdf - UTH e
... which time we have taught many thousands of students. We have also been active researchers in computer networking during this time. (In fact, Jim and Keith first met each other as master’s students in a computer networking course taught by Mischa Schwartz in 1979 at Columbia University.) We think al ...
... which time we have taught many thousands of students. We have also been active researchers in computer networking during this time. (In fact, Jim and Keith first met each other as master’s students in a computer networking course taught by Mischa Schwartz in 1979 at Columbia University.) We think al ...
NESCOR Team 1 Failure Scenarios
... A number of attack vectors may result in interference with delivery of or compliance with demand response messages. Any of these have the potential to unbalance power generation and load in a system that has been fine-tuned to anticipate power usage in accordance with demand response. ...
... A number of attack vectors may result in interference with delivery of or compliance with demand response messages. Any of these have the potential to unbalance power generation and load in a system that has been fine-tuned to anticipate power usage in accordance with demand response. ...
Unraveling the B2B Process
... This will include acquiring and maintaining the circuit to the B2B gateway and acquiring a Virtual Private Network (VPN) deice compatible with the MHS VPN device. 3. Contractors will comply with DoD guidance regarding allowable ports, protocols and risk mitigation strategies. 4. All cost for VPN har ...
... This will include acquiring and maintaining the circuit to the B2B gateway and acquiring a Virtual Private Network (VPN) deice compatible with the MHS VPN device. 3. Contractors will comply with DoD guidance regarding allowable ports, protocols and risk mitigation strategies. 4. All cost for VPN har ...
Introduction To Networking - Alfagate Infocom Technology.... Main
... dozen or less computers. In a client/server network there is usually an NT Domain Controller, to which all of the computers log on. This server can provide various services, including centrally routed Internet Access, mail (including e-mail), file sharing and printer access, as well as ensuring secu ...
... dozen or less computers. In a client/server network there is usually an NT Domain Controller, to which all of the computers log on. This server can provide various services, including centrally routed Internet Access, mail (including e-mail), file sharing and printer access, as well as ensuring secu ...
Security Analysis of TrueCryptpdfauthor - BSI
... From a security perspective, the fact that TrueCrypt is a purely software solution means that it cannot in principle protect against all relevant threats. Effective protection only exists when an encrypted disk is lost or stolen in a deactivated state. TrueCrypt does not provide any protection again ...
... From a security perspective, the fact that TrueCrypt is a purely software solution means that it cannot in principle protect against all relevant threats. Effective protection only exists when an encrypted disk is lost or stolen in a deactivated state. TrueCrypt does not provide any protection again ...
International Technical Support Organization June 1996 How to Secure
... an external security manager such as Resource Access Control Facility. It also provides a high-level overview of various implementation scenarios that can be used and explains the role of firewalls in these scenarios. The various security threats are discussed in great detail, as well as the auditin ...
... an external security manager such as Resource Access Control Facility. It also provides a high-level overview of various implementation scenarios that can be used and explains the role of firewalls in these scenarios. The various security threats are discussed in great detail, as well as the auditin ...
DNS Security Considerations and the Alternatives to BIND
... firewall can protect your DNS servers, you are probably wrong. You will be surprised when you see the attacks coming to the open TCP or UDP port (port 53). So, you are not wasting your time to take a few simple steps to harden the DNS server, as they are very important. Later this paper is going to ...
... firewall can protect your DNS servers, you are probably wrong. You will be surprised when you see the attacks coming to the open TCP or UDP port (port 53). So, you are not wasting your time to take a few simple steps to harden the DNS server, as they are very important. Later this paper is going to ...