Slide 1
... Lack authenticity and integrity checking of the data held within the DNS make it not secure. ...
... Lack authenticity and integrity checking of the data held within the DNS make it not secure. ...
PPT - Communications
... Simple Network Management Protocol • SNMP agent is software that runs on a piece of network equipment (host, router, printer, or others) and that maintains information about its configuration and current state in a database • Information in the database is described by Management Information Bases ...
... Simple Network Management Protocol • SNMP agent is software that runs on a piece of network equipment (host, router, printer, or others) and that maintains information about its configuration and current state in a database • Information in the database is described by Management Information Bases ...
Creating high-performance, statically type
... In his 2003 analysis of Internet growth [217], Andrew Odlyzko notes that “Internet traffic continues to grow vigorously, approximately doubling each year, as it has done every year since 1997”. The types of hosts connected are also changing—from computers on fixed links to mobile personal devices su ...
... In his 2003 analysis of Internet growth [217], Andrew Odlyzko notes that “Internet traffic continues to grow vigorously, approximately doubling each year, as it has done every year since 1997”. The types of hosts connected are also changing—from computers on fixed links to mobile personal devices su ...
FREE Sample Here
... 6. The shoulder looking technique is used in public or semipublic settings when individuals gather information they are not authorized to have by looking over another individual’s shoulder or viewing the information from a distance. _________________________ ANS: F, surfing PTS: 1 ...
... 6. The shoulder looking technique is used in public or semipublic settings when individuals gather information they are not authorized to have by looking over another individual’s shoulder or viewing the information from a distance. _________________________ ANS: F, surfing PTS: 1 ...
staff symposium series
... Be cautious if you are asked for personal information Use encryption to protect sensitive data transmitted over public networks and the Internet Install anti-virus, perform scheduled virus scanning and keep virus signature up-to-date Apply security patching timely Backup your system and data, and st ...
... Be cautious if you are asked for personal information Use encryption to protect sensitive data transmitted over public networks and the Internet Install anti-virus, perform scheduled virus scanning and keep virus signature up-to-date Apply security patching timely Backup your system and data, and st ...
Creating High-Performance Statically Type
... continues to grow vigorously, approximately doubling each year, as it has done every year since 1997”. The types of hosts connected are also changing—from computers on fixed links to mobile personal devices such as laptops, PDAs or mobile phones. The trend towards mobility has led to a surge in “wir ...
... continues to grow vigorously, approximately doubling each year, as it has done every year since 1997”. The types of hosts connected are also changing—from computers on fixed links to mobile personal devices such as laptops, PDAs or mobile phones. The trend towards mobility has led to a surge in “wir ...
Distilling Data in a SIM: A Strategy for the Analysis
... vulnerabilities. Relevance depends on whether the asset has been scanned or not and whether the target has the targeted port open or is vulnerable to the attack shown by the event. Asset criticality depends on whatever criticality was assigned when the asset was modeled. Severity depends on what is ...
... vulnerabilities. Relevance depends on whether the asset has been scanned or not and whether the target has the targeted port open or is vulnerable to the attack shown by the event. Asset criticality depends on whatever criticality was assigned when the asset was modeled. Severity depends on what is ...
Principles of system administration Edition 2.1
... Never leave root shells on the console. It is possible to accidentally do something destructive without realizing that one has root privileges. (Put the sledgehammer down when you are not using it, Eugene!) Never leave root shells running so that others might gain access to them in an open room. Nev ...
... Never leave root shells on the console. It is possible to accidentally do something destructive without realizing that one has root privileges. (Put the sledgehammer down when you are not using it, Eugene!) Never leave root shells running so that others might gain access to them in an open room. Nev ...
ICETSH-Part-6
... technologies for vehicular networks. WiMAX and LTE are Fourth-Generation (4G) wireless technologies that have well-defined quality of service (QoS) and security architectures.Existing work QoS-aware distributed security architecture using the elliptic curve Diffie–Hellman (ECDH) protocol that has pr ...
... technologies for vehicular networks. WiMAX and LTE are Fourth-Generation (4G) wireless technologies that have well-defined quality of service (QoS) and security architectures.Existing work QoS-aware distributed security architecture using the elliptic curve Diffie–Hellman (ECDH) protocol that has pr ...
Computer Networks 4th Ed, Andrew S. Tanenbaum, Prentice Hall
... information grows, the demand for ever more sophisticated information processing grows even faster. Although the computer industry is still young compared to other industries (e.g., automobiles and air transportation), computers have made spectacular progress in a short time. During the first two de ...
... information grows, the demand for ever more sophisticated information processing grows even faster. Although the computer industry is still young compared to other industries (e.g., automobiles and air transportation), computers have made spectacular progress in a short time. During the first two de ...
Linksys BEFSR11/BEFSR41 User Guide
... or fitness for any particular purpose. Linksys reserves the right to revise or update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT The Instant Broadband EtherFas ...
... or fitness for any particular purpose. Linksys reserves the right to revise or update its products, software, or documentation without obligation to notify any individual or entity. Please direct all inquiries to: Linksys P.O. Box 18558, Irvine, CA 92623. FCC STATEMENT The Instant Broadband EtherFas ...
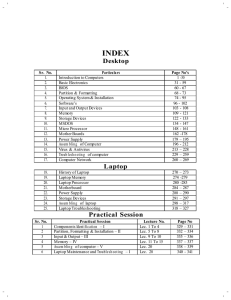
View Hardware - Itech Computer Education
... property of computer to do the g iven task obe diently without asking any question is called diligence. If any calculation has been done a million time s, a computer will do so with sa me accuracy and speed. 4) Storage capacity: Computer c an store large volume of data and information on mag netic m ...
... property of computer to do the g iven task obe diently without asking any question is called diligence. If any calculation has been done a million time s, a computer will do so with sa me accuracy and speed. 4) Storage capacity: Computer c an store large volume of data and information on mag netic m ...
Easy Steps to Cisco Extended Access List
... based on source and destination IP address, port numbers and upper-layer protocols. Standard access list can deny or permit packets by source address only and permit or deny entire TCP/IP protocol suite. Therefore by extended, it means greater functionality and flexibility. Extended access list is a ...
... based on source and destination IP address, port numbers and upper-layer protocols. Standard access list can deny or permit packets by source address only and permit or deny entire TCP/IP protocol suite. Therefore by extended, it means greater functionality and flexibility. Extended access list is a ...
Windows-2000 and system Administration
... portable, and wireless computing and communication devices. This includes devices like laptops with wireless LAN technology, mobile phones, wearable computers and Personal Digital Assistants (PDAs) with Blue tooth or IRDA interfaces, and USB flash drives. Distributed Computing:- This is another way ...
... portable, and wireless computing and communication devices. This includes devices like laptops with wireless LAN technology, mobile phones, wearable computers and Personal Digital Assistants (PDAs) with Blue tooth or IRDA interfaces, and USB flash drives. Distributed Computing:- This is another way ...
Security Warrior
... intermediate- to advanced-level practitioner. But who among us is typical? Each of us approaches infosec with distinctive training and skill. Still, before you spend your hard-earned money on this book, we will try to describe the target reader. As an example, you might enjoy this book if you alread ...
... intermediate- to advanced-level practitioner. But who among us is typical? Each of us approaches infosec with distinctive training and skill. Still, before you spend your hard-earned money on this book, we will try to describe the target reader. As an example, you might enjoy this book if you alread ...
Spear Phishing Attacks—Why They are Successful and How to Stop
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
... The assault began with spear phishing attacks that sent targeted users an email with a Microsoft Excel file attachment that leveraged a zero-day flaw in Adobe Flash. It is clear that not only was RSA the focus of the attack, but only four individuals within RSA were the recipients of the malicious e ...
Wireless Networking in the Developing World
... countries and released over 600 pages of documentation under Creative Commons License. More information can be found at http://www.it46.se/ • Carlo Fonda is a member of the Radio Communications Unit at the Abdus Salam International Center for Theoretical Physics in Trieste, Italy. • Jim Forster has ...
... countries and released over 600 pages of documentation under Creative Commons License. More information can be found at http://www.it46.se/ • Carlo Fonda is a member of the Radio Communications Unit at the Abdus Salam International Center for Theoretical Physics in Trieste, Italy. • Jim Forster has ...
Lecture 16: TCP/IP Vulnerabilities and DoS Attacks
... IGMP packets are used for multicasting on the internet. In the jargon of internet communications, a multicast consists of a simultaneous transmission of information to a group of subscribers. The packets stay as a single stream as long as the network topology allows it. An IGMP header includes the I ...
... IGMP packets are used for multicasting on the internet. In the jargon of internet communications, a multicast consists of a simultaneous transmission of information to a group of subscribers. The packets stay as a single stream as long as the network topology allows it. An IGMP header includes the I ...
How to Detect Mainframe Intrusion Attempts
... Abstract and Speaker • The Internet today is a complex entity comprised of diverse networks, users, and resources. Most of the users are oblivious to the design of the Internet and its components and only use the services provided by their operating system or applications. However, there is a smal ...
... Abstract and Speaker • The Internet today is a complex entity comprised of diverse networks, users, and resources. Most of the users are oblivious to the design of the Internet and its components and only use the services provided by their operating system or applications. However, there is a smal ...
Roadmap of the Protocols
... multimedia, whether for media-on-demand from World Wide Web servers, or between users in multimedia conferencing systems is becoming quite pervasive. The Internet has undergone a number of enhancements to make this possible, as have its protocols. There is also a huge investment in middleware, softw ...
... multimedia, whether for media-on-demand from World Wide Web servers, or between users in multimedia conferencing systems is becoming quite pervasive. The Internet has undergone a number of enhancements to make this possible, as have its protocols. There is also a huge investment in middleware, softw ...
A Survey on Automated Dynamic Malware Analysis Techniques and Tools
... Internet-connected computer system. This bot allows an external entity, the socalled bot master, to remotely control this system. The pool of machines that are under control of the bot master is called a botnet. The bot master might rent this botnet to a spammer who misuses the bots to send spam ema ...
... Internet-connected computer system. This bot allows an external entity, the socalled bot master, to remotely control this system. The pool of machines that are under control of the bot master is called a botnet. The bot master might rent this botnet to a spammer who misuses the bots to send spam ema ...
Semantically-enabled Digital Investigations
... specialized subset of the digital forensic collection and analysis needs such as file carving, log analysis tool or network forensics analysis tools. These tools can also become quickly outdated by newly introduced technologies or data formats. All the above can lead the forensic examiner to demandi ...
... specialized subset of the digital forensic collection and analysis needs such as file carving, log analysis tool or network forensics analysis tools. These tools can also become quickly outdated by newly introduced technologies or data formats. All the above can lead the forensic examiner to demandi ...
Final system architecture, programming interfaces
... Figure 1: Architectural framework for Superfluidity with an example mapping into the physical Data Centres .........15 Figure 2: Superfluidity architecture ..................................................................................................................................20 Figure 3: C ...
... Figure 1: Architectural framework for Superfluidity with an example mapping into the physical Data Centres .........15 Figure 2: Superfluidity architecture ..................................................................................................................................20 Figure 3: C ...
available online (PDF document)
... Security, and the Subcommittee on Networking and Information Technology Research and Development (NITRD) of the NSTC’s Committee on Technology. The report is published by the National Coordination Office for Networking and Information Technology Research and Development (NCO/NITRD). The NCO/NITRD su ...
... Security, and the Subcommittee on Networking and Information Technology Research and Development (NITRD) of the NSTC’s Committee on Technology. The report is published by the National Coordination Office for Networking and Information Technology Research and Development (NCO/NITRD). The NCO/NITRD su ...