Hack Attacks Revealed
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
Hack Attacks Revealed
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
... We are the technologically inclined and normality spurned, or at least, this is how we perceive (or perhaps want) things to be. We are adept at dealing with machines, and manipulating things. Everything comes easy to us, and when things always come to you without any failure, you begin to feel nothi ...
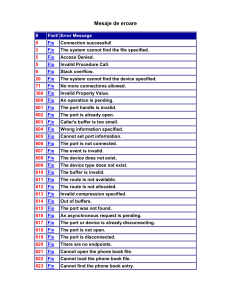
Mesaje de eroare
... You cannot dial using this connection at logon time, because it is configured to use a user name different than the one on 784 N/A the smart card. If you want to use it at logon time, you must configure it to use the user name on the smart card You cannot dial using this connection at logon ti ...
... You cannot dial using this connection at logon time, because it is configured to use a user name different than the one on 784 N/A the smart card. If you want to use it at logon time, you must configure it to use the user name on the smart card You cannot dial using this connection at logon ti ...
Chapter 02: The Need for Security
... both for legitimate network management functions and for stealing information from a network. Unauthorized sniffers can be extremely dangerous to a network’s security, because they are virtually impossible to detect and can be inserted almost anywhere. This makes them a favorite weapon in the hacker ...
... both for legitimate network management functions and for stealing information from a network. Unauthorized sniffers can be extremely dangerous to a network’s security, because they are virtually impossible to detect and can be inserted almost anywhere. This makes them a favorite weapon in the hacker ...
Intruders and password protection
... Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another represents the probability that one lette ...
... Markov model: generation of guessable passwords, this model shows a language consisting of an alphabet of three characters. The state of the system at any time is the identity of the most recent letter. The value on the transition from one state to another represents the probability that one lette ...
Computer Center, CS, NCTU
... We can allocate continuous ClassC network to organization – Reflect physical network topology – Reduce the size of routing table ...
... We can allocate continuous ClassC network to organization – Reflect physical network topology – Reduce the size of routing table ...
Ethical Hacking and Countermeasures- v6
... o Expired Domains o DomainKing o Domain Name Analyzer o DomainInspect o MSR Strider URL Tracer o Mozzle Domain Name Pro o Domain Research Tool (DRT) o Domain Status Reporter ...
... o Expired Domains o DomainKing o Domain Name Analyzer o DomainInspect o MSR Strider URL Tracer o Mozzle Domain Name Pro o Domain Research Tool (DRT) o Domain Status Reporter ...
COmpUter ANd iNFOrmAtiON SYStemS Natural and Appled Sciences Division Jamie Alonzo, Division Dean
... (IT) industry in general, and more specifically in computer networking and system administration. Courses include the underlying networking concepts and theory, administering the network infrastructure including the Cisco Systems CCNA/CCNP courses, system and network administration using UNIX/Linux ...
... (IT) industry in general, and more specifically in computer networking and system administration. Courses include the underlying networking concepts and theory, administering the network infrastructure including the Cisco Systems CCNA/CCNP courses, system and network administration using UNIX/Linux ...
Growing University in Namibia Moves to Next-Generation
... however, was the trend he saw - prevalent in universities worldwide - toward hackers using the university as a conduit to launch external attacks – the well-known botnets. “Universities in general are not known for securing themselves well, and we have a lot of equipment available to serve very dive ...
... however, was the trend he saw - prevalent in universities worldwide - toward hackers using the university as a conduit to launch external attacks – the well-known botnets. “Universities in general are not known for securing themselves well, and we have a lot of equipment available to serve very dive ...
Here - Bkav Corporation
... Center, Kenh Liem Intersection and Hon Gai Post Office. According to information from mass media, users can use free WiFi to access some portals of the province, but they will be charged when accessing other websites. However, at the time of the survey, we could not access free WiFi although WiFi sp ...
... Center, Kenh Liem Intersection and Hon Gai Post Office. According to information from mass media, users can use free WiFi to access some portals of the province, but they will be charged when accessing other websites. However, at the time of the survey, we could not access free WiFi although WiFi sp ...
CCNPv5 Module 5 Lesson 1
... Port scans and ping sweeps cannot be prevented without compromising network capabilities. However, damage can be mitigated using intrusion prevention systems at network and host levels. ...
... Port scans and ping sweeps cannot be prevented without compromising network capabilities. However, damage can be mitigated using intrusion prevention systems at network and host levels. ...
CSCE 790 – Secure Database Systems
... against a Member of the United Nations, until the Security Council has taken measures necessary to maintain international peace and security. Measures taken by Members in the exercise of this right of self-defense shall be immediately reported to the Security Council and shall not in any way affect ...
... against a Member of the United Nations, until the Security Council has taken measures necessary to maintain international peace and security. Measures taken by Members in the exercise of this right of self-defense shall be immediately reported to the Security Council and shall not in any way affect ...
Network Vulnerability Scanning - Texas Tech University Departments
... Dept. of Computer Science Texas Tech University, USA [email protected] ...
... Dept. of Computer Science Texas Tech University, USA [email protected] ...
The Blaster Worm: Then and Now
... little, suggesting that it had little effect on the infected population at large. Simply put, these persistent infections are due to people who either don’t know or don’t care enough that their machines are infected. One way to gain insight into the Blaster’s persistence is to compare the infected p ...
... little, suggesting that it had little effect on the infected population at large. Simply put, these persistent infections are due to people who either don’t know or don’t care enough that their machines are infected. One way to gain insight into the Blaster’s persistence is to compare the infected p ...
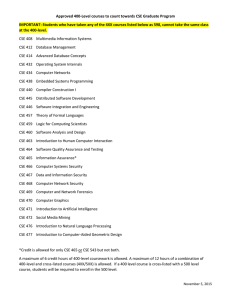
Approved 400-Level courses to count towards CSE Graduate
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
(Ch.7, Part 2): Security in Networks – Part 2 – LONG version
... Comparison of link vs. e2e encryption Encryption of msgs/packets (whether link or e2e encryption) is no silver bullet No guarantees of msg/packet security 1) Link encryption — encrypts all traffic over physical link Typically host H has one link into network => link encryption encrypts all H’s ...
... Comparison of link vs. e2e encryption Encryption of msgs/packets (whether link or e2e encryption) is no silver bullet No guarantees of msg/packet security 1) Link encryption — encrypts all traffic over physical link Typically host H has one link into network => link encryption encrypts all H’s ...
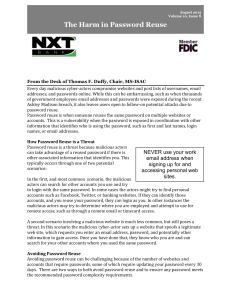
Password Security
... choosing a sentence that incorporates something unique about the website or account, and then using the first letter of each word as your password. For example the sentence: "This is my August password for the Center for Internet Security website." would become "TimAp4tCfISw." Since a strong passwor ...
... choosing a sentence that incorporates something unique about the website or account, and then using the first letter of each word as your password. For example the sentence: "This is my August password for the Center for Internet Security website." would become "TimAp4tCfISw." Since a strong passwor ...
Chapter 10
... (cont’d.) • E-commerce site security policy points – Authentication: Who is trying to access site? – Access control: Who is allowed to log on to and access site? – Secrecy: Who is permitted to view selected ...
... (cont’d.) • E-commerce site security policy points – Authentication: Who is trying to access site? – Access control: Who is allowed to log on to and access site? – Secrecy: Who is permitted to view selected ...
conklin_4e_PPT_ch11
... accounting, referred to as AAA. • Authentication is the matching of user-supplied credentials to previously stored credentials on a host machine, and it usually involves an account username and password. • Authorization is the granting of specific permissions based on the privileges held by the acco ...
... accounting, referred to as AAA. • Authentication is the matching of user-supplied credentials to previously stored credentials on a host machine, and it usually involves an account username and password. • Authorization is the granting of specific permissions based on the privileges held by the acco ...
A Study of the Novel Approaches Used in Intrusion Detection and
... The aim of this paper [5] is to address the issues of information security because most of the organizations are depending on the internet to communicate with the people or with the systems to provide them news, online shopping, email, credit card detail and personal information. This paper [5] desc ...
... The aim of this paper [5] is to address the issues of information security because most of the organizations are depending on the internet to communicate with the people or with the systems to provide them news, online shopping, email, credit card detail and personal information. This paper [5] desc ...
NP8-1
... What kind of resources are available on the Internet? • Web Sites – various locations in cyberspace that correspond to a corporation, a store, a magazine, and more • Search engines – help catalog a huge portion of the data stored on Web sites • Downloads and uploads ...
... What kind of resources are available on the Internet? • Web Sites – various locations in cyberspace that correspond to a corporation, a store, a magazine, and more • Search engines – help catalog a huge portion of the data stored on Web sites • Downloads and uploads ...
Physical Security
... provide. Other servers (domain controllers and remote access servers, for example) may not require any antivirus software, as they do not allow users to place files on them. – File servers need protection, as do certain types of application servers. ...
... provide. Other servers (domain controllers and remote access servers, for example) may not require any antivirus software, as they do not allow users to place files on them. – File servers need protection, as do certain types of application servers. ...
quinn_2e_ppt06
... Impact on Morris Suspended from Cornell 3 years’ probation + 400 hours community service $150,000 in legal fees and fines ...
... Impact on Morris Suspended from Cornell 3 years’ probation + 400 hours community service $150,000 in legal fees and fines ...
Introduction to Computer Security
... Some resurgence with wireless networks Has always been a problem with wireless transmission! Electromagnetic emanations (TEMPEST security) ...
... Some resurgence with wireless networks Has always been a problem with wireless transmission! Electromagnetic emanations (TEMPEST security) ...