Quantum DXi6902 User`s Guide
... Quantum DXi6902 User’s Guide, 6-68159-02 Rev A, January 2015, Product of USA. This document is for DXi 3.1.0_69 Software. Quantum Corporation provides this publication “as is” without warranty of any kind, either express or implied, including but not limited to the implied warranties of merchantabi ...
... Quantum DXi6902 User’s Guide, 6-68159-02 Rev A, January 2015, Product of USA. This document is for DXi 3.1.0_69 Software. Quantum Corporation provides this publication “as is” without warranty of any kind, either express or implied, including but not limited to the implied warranties of merchantabi ...
Quantum DXi6902 User`s Guide
... Quantum DXi6902 User’s Guide, 6-68159-01 Rev A, July 2014, Product of USA. This document is for DXi 3.0.0_69 Software. Quantum Corporation provides this publication “as is” without warranty of any kind, either express or implied, including but not limited to the implied warranties of merchantabilit ...
... Quantum DXi6902 User’s Guide, 6-68159-01 Rev A, July 2014, Product of USA. This document is for DXi 3.0.0_69 Software. Quantum Corporation provides this publication “as is” without warranty of any kind, either express or implied, including but not limited to the implied warranties of merchantabilit ...
MLM Law - MLMLegal.com
... MLM Law and MLM Legal issues are recurring topics in running and promoting the successful Direct Sales and Direct Selling company. Learn about important legislation, topical cases and important principles that make or break Network Marketing and Party Plan Companies. Learn about the impact of MLM So ...
... MLM Law and MLM Legal issues are recurring topics in running and promoting the successful Direct Sales and Direct Selling company. Learn about important legislation, topical cases and important principles that make or break Network Marketing and Party Plan Companies. Learn about the impact of MLM So ...
Intruders and password protection
... Use a password manager (PM). It is a utility that creates an encrypted file where your passwords are stored. Try to use "nonsense words." Do not tell anybody your password. ...
... Use a password manager (PM). It is a utility that creates an encrypted file where your passwords are stored. Try to use "nonsense words." Do not tell anybody your password. ...
Customer Best Practices for Teradata Upgrades
... Package Comparison Tool. This is available on the Teradata At Your Service website under the “Tools and Reports” menu. Given two package version numbers, this report displays the DRs (Discrepancy Reports) in the first package but not the second, and the DRs in the second package but not the first. T ...
... Package Comparison Tool. This is available on the Teradata At Your Service website under the “Tools and Reports” menu. Given two package version numbers, this report displays the DRs (Discrepancy Reports) in the first package but not the second, and the DRs in the second package but not the first. T ...
Hewlett Packard Enterprise Co (Form: 425, Received: 01/17/2017
... Micro Focus, HPE and HPE Software that are “forward-looking statements” within the meaning of the U.S. Private Securities Litigation Reform Act of 1995. The forward-looking statements contained in this communication may include statements about the expected effects on Micro Focus, HPE and HPE Softwa ...
... Micro Focus, HPE and HPE Software that are “forward-looking statements” within the meaning of the U.S. Private Securities Litigation Reform Act of 1995. The forward-looking statements contained in this communication may include statements about the expected effects on Micro Focus, HPE and HPE Softwa ...
MIS9eCC08
... removes or quarantines computer viruses Anti-spyware and anti-adware software Spam protection software – identifies and marks and/or deletes Spam Anti-phishing software – lets you know when phishing attempts are being made Firewall – hardware and/or software that protects a computer or network from ...
... removes or quarantines computer viruses Anti-spyware and anti-adware software Spam protection software – identifies and marks and/or deletes Spam Anti-phishing software – lets you know when phishing attempts are being made Firewall – hardware and/or software that protects a computer or network from ...
Lecture - Department of Computing
... two phase locking protocol, then all their possible interleaved executions (schedules) are serialisable • however, not all schedules produce the same result – think of examples ...
... two phase locking protocol, then all their possible interleaved executions (schedules) are serialisable • however, not all schedules produce the same result – think of examples ...
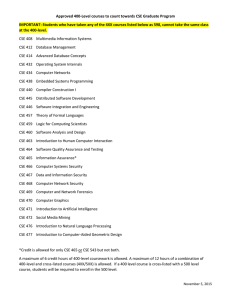
Approved 400-Level courses to count towards CSE Graduate
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
... Approved 400-Level courses to count towards CSE Graduate Program IMPORTANT: Students who have taken any of the 4XX courses listed below as 598, cannot take the same class at the 400-level. CSE 408 Multimedia Information Systems CSE 412 Database Management CSE 414 Advanced Database Concepts CSE 432 O ...
Remote Access—Attack Vectors
... sufficient to breach a system. Organizations with internal networks that store highly sensitive data increase their risk of exposure when they use VPNs to communicate. Hackers are drawn to the vulnerability VPNs present when private information is transmitted and, thus, made more accessible. Second, ...
... sufficient to breach a system. Organizations with internal networks that store highly sensitive data increase their risk of exposure when they use VPNs to communicate. Hackers are drawn to the vulnerability VPNs present when private information is transmitted and, thus, made more accessible. Second, ...
Aspects of Biological Evolution and Their
... .rhost file can either contain a list of machine-user name pairs, one per line, of systems and users that have access to the machine or simply a line containing the machine name. In the first case the rights that these users have access to are based on the position of the .rhost file in the director ...
... .rhost file can either contain a list of machine-user name pairs, one per line, of systems and users that have access to the machine or simply a line containing the machine name. In the first case the rights that these users have access to are based on the position of the .rhost file in the director ...
VMAX DVR Manual
... After connecting peripheral devices such as cameras, monitors and a mouse to the DVR, power up the DVR by connecting DC12V 5A adaptor to the power jack on the rear panel. Login with ‘User Name’ at the login screen will appear as shown below. There is only one Administrator Account configurable in th ...
... After connecting peripheral devices such as cameras, monitors and a mouse to the DVR, power up the DVR by connecting DC12V 5A adaptor to the power jack on the rear panel. Login with ‘User Name’ at the login screen will appear as shown below. There is only one Administrator Account configurable in th ...
Introduction to Information Security Chapter 2
... Test for evaluating the strengths and effectiveness of all security controls on system Also called tiger team attack or red team attack Goal: violate site security policy Not a replacement for careful design, implementation, and ...
... Test for evaluating the strengths and effectiveness of all security controls on system Also called tiger team attack or red team attack Goal: violate site security policy Not a replacement for careful design, implementation, and ...
Statistical Models for Steganography - uni
... Information hiding takes place if the encoder or the decoder encounters a block y such that ty ≥ 1/ρ ...
... Information hiding takes place if the encoder or the decoder encounters a block y such that ty ≥ 1/ρ ...
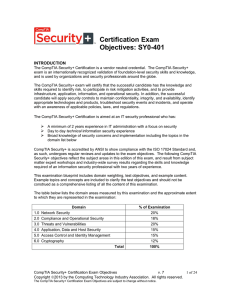
CompTIA Security (SY0-401)
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
HAVEGE HArdware Volatile Entropy Gathering and Expansion
... buffers: write buffers, victim buffers, prefetch buffers, .. pipeline status ...
... buffers: write buffers, victim buffers, prefetch buffers, .. pipeline status ...
Optimal Recommendation Sets: Covering Uncertainty
... constraint violations. Neither approach explicitly takes into account diversity in the set of possible user preferences. And for both approaches, one could easily end up with a recommendation set containing ten editions of the same book. The problem is that including an alternative in a set that alr ...
... constraint violations. Neither approach explicitly takes into account diversity in the set of possible user preferences. And for both approaches, one could easily end up with a recommendation set containing ten editions of the same book. The problem is that including an alternative in a set that alr ...
LogMeIn Security – an In-Depth Look
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
... installing a remote access product. Remote access products are perceived as high risk factors, but mainly for psychological reasons. When a user first sees a remote access solution in action, their first negative reaction is usually with regard to the security implications. This is perfectly normal, ...
2. Interference Mitigation for Closed User Group Femtocells
... Figure 2 UL Interference Scenario 2.1 Proposed Interference Mitigation In order to reduce/avoid interference between closed user group femtocells and cells under the network operator’s control, it is proposed that BSs under the network operator’s control can impose scheduling restrictions on closed ...
... Figure 2 UL Interference Scenario 2.1 Proposed Interference Mitigation In order to reduce/avoid interference between closed user group femtocells and cells under the network operator’s control, it is proposed that BSs under the network operator’s control can impose scheduling restrictions on closed ...
New Intel® Atom™ Processor-Based Platform for
... Arium announced its LX-1000 JTAG debugger with trace memory. The LX-1000 is the next generation of Arium In-Target Probes (ITP) supporting a full range of Intel devices. A modular design, the LX-1000 currently supports Intel devices, with other architecture support available soon.The LX-1000 was des ...
... Arium announced its LX-1000 JTAG debugger with trace memory. The LX-1000 is the next generation of Arium In-Target Probes (ITP) supporting a full range of Intel devices. A modular design, the LX-1000 currently supports Intel devices, with other architecture support available soon.The LX-1000 was des ...
Organizations That Use TLS/SSL
... authority that can attest to the identity of the certificate owner. Organizations will also need a system or network administrator who is familiar with whichever client-server applications need to be secured to enable TLS/SSL encryption. If an organization purchases a certificate from a trusted CA, ...
... authority that can attest to the identity of the certificate owner. Organizations will also need a system or network administrator who is familiar with whichever client-server applications need to be secured to enable TLS/SSL encryption. If an organization purchases a certificate from a trusted CA, ...
Understanding the Methods of Network Attacks
... consider a situation in which an outside attacker calls a receptionist. The attacker pretends to be a member of the company’s IT department, and he convinces the receptionist to tell him her username and password. The attacker then can use those credentials to log into the network. To prevent a sing ...
... consider a situation in which an outside attacker calls a receptionist. The attacker pretends to be a member of the company’s IT department, and he convinces the receptionist to tell him her username and password. The attacker then can use those credentials to log into the network. To prevent a sing ...
Forensic Analysis Reveals Data Leaks in HIPAA
... Due to the presence of searchable SSNs in the transaction logs, Kivu suspected other sources of PII/PHI related to the EMR application could be present on the compromised server. The search for PII/PHI was extended in order to examine the entire server for other potential sources of PII/PHI. Due to ...
... Due to the presence of searchable SSNs in the transaction logs, Kivu suspected other sources of PII/PHI related to the EMR application could be present on the compromised server. The search for PII/PHI was extended in order to examine the entire server for other potential sources of PII/PHI. Due to ...
hosted application provider case study
... support all of their customers from a single, in-house, EMEAbased data centre. However, their worldwide customer base was experiencing latency issues, as well as decreased quality of service, and the software company didn’t have the right resources lined up to address these issues. Supporting their ...
... support all of their customers from a single, in-house, EMEAbased data centre. However, their worldwide customer base was experiencing latency issues, as well as decreased quality of service, and the software company didn’t have the right resources lined up to address these issues. Supporting their ...
Exploring Microsoft Office 2003
... program that can erase data and/or alter the way your computer works Worms and Trojan horses are other types of infectious programs, but all are bad Computer viruses are spread through email, and/or infected floppy disks Windows does not include an antivirus program; i.e., you must buy it separately ...
... program that can erase data and/or alter the way your computer works Worms and Trojan horses are other types of infectious programs, but all are bad Computer viruses are spread through email, and/or infected floppy disks Windows does not include an antivirus program; i.e., you must buy it separately ...