Operating System Security Rules
... as the administration account will force the hacker to find another legitimate username. Do not delete the system account since it may be needed by various system functions. Finding a legitimate username may not be difficult because most companies use very similar username naming conventions (e.g., ...
... as the administration account will force the hacker to find another legitimate username. Do not delete the system account since it may be needed by various system functions. Finding a legitimate username may not be difficult because most companies use very similar username naming conventions (e.g., ...
Collaborative reasoning - School of Computing
... Tracing or Formal Inspection School of Computing Clemson University ...
... Tracing or Formal Inspection School of Computing Clemson University ...
How to Detect Zero-Day Malware And Limit Its Impact
... network, as opposed to relying on SIEMs systems and threat intelligence systems collecting information about every process and analyzing the data for patterns. If the machine configuration has changed, or an anomaly is detected when the computer boots up, administrators can be alerted that something ...
... network, as opposed to relying on SIEMs systems and threat intelligence systems collecting information about every process and analyzing the data for patterns. If the machine configuration has changed, or an anomaly is detected when the computer boots up, administrators can be alerted that something ...
Chapter12-Security
... • Not possible to break code given public key • If you want someone to send you secure data, give them your public key, you keep the private key • Secure Sockets Layer on the Internet is a common example of public key cryptography Data Communications and Computer Networks: A Business User's Approach ...
... • Not possible to break code given public key • If you want someone to send you secure data, give them your public key, you keep the private key • Secure Sockets Layer on the Internet is a common example of public key cryptography Data Communications and Computer Networks: A Business User's Approach ...
An Immucor Technical Support Solution
... Yes, blud_direct utilizes the Secure Socket Layer (SSL) protocol, commonly used for secure transactions over the web. Additionally, the application uses 256-bit AES encryption to further secure the communication. Is there software loaded on our instrument computer? No. There is no software to load o ...
... Yes, blud_direct utilizes the Secure Socket Layer (SSL) protocol, commonly used for secure transactions over the web. Additionally, the application uses 256-bit AES encryption to further secure the communication. Is there software loaded on our instrument computer? No. There is no software to load o ...
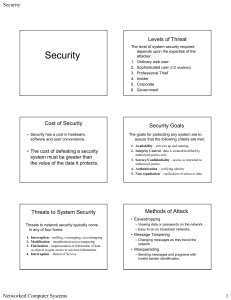
Slides on Security
... • Cryptography in general represents the process of encrypting a plain-text message into an unreadable cipher so that it can be sent through a network to be decrypted/deciphered by the intended recipient. • Cryptography is an important tool for security. Key Plaintext ...
... • Cryptography in general represents the process of encrypting a plain-text message into an unreadable cipher so that it can be sent through a network to be decrypted/deciphered by the intended recipient. • Cryptography is an important tool for security. Key Plaintext ...
Agile Software Development
... Important: Database refactorings are a subset of schema transformations, but they do not add functionality. ...
... Important: Database refactorings are a subset of schema transformations, but they do not add functionality. ...
Chapter 12
... • Not possible to break code given public key • If you want someone to send you secure data, give them your public key; you keep the private key • Secure Sockets Layer on the Internet is a common example of public key cryptography ...
... • Not possible to break code given public key • If you want someone to send you secure data, give them your public key; you keep the private key • Secure Sockets Layer on the Internet is a common example of public key cryptography ...
PowerPoint
... What are example types of application programs What do operating systems do How do compilers work The relationship between hardware and software ...
... What are example types of application programs What do operating systems do How do compilers work The relationship between hardware and software ...
Release-Notes-new-June-2014-and-later-for
... 4. In Product Code Maintenance, you can now add Product Codes to any and all Branches where they do not currently exist. From the main Product Code Maintenance screen, highlight and right-click on a Product Code you would like to copy. The system will prompt the new option as follows: Copy Code to a ...
... 4. In Product Code Maintenance, you can now add Product Codes to any and all Branches where they do not currently exist. From the main Product Code Maintenance screen, highlight and right-click on a Product Code you would like to copy. The system will prompt the new option as follows: Copy Code to a ...
chapter13
... Securing Systems with Firewalls • A firewall is software or hardware that acts as a protective filter between an internal computer system and an external network such as the Internet – Only allows authorized entrants – A proxy firewall establishes a new link between each packet of information and i ...
... Securing Systems with Firewalls • A firewall is software or hardware that acts as a protective filter between an internal computer system and an external network such as the Internet – Only allows authorized entrants – A proxy firewall establishes a new link between each packet of information and i ...
Transparent Reality: Using Eye Gaze Focus Depth as
... the HMD just below the lenses to capture the user’s eyes. The HMD’s lenses were modified to provide more space for the cameras without interfering with the user’s comfort. The lenses were cut about one third of its total height at the bottom to achieve this. The result are shown in Figure 1(b). Sinc ...
... the HMD just below the lenses to capture the user’s eyes. The HMD’s lenses were modified to provide more space for the cameras without interfering with the user’s comfort. The lenses were cut about one third of its total height at the bottom to achieve this. The result are shown in Figure 1(b). Sinc ...
PHP Security
... • Most security issues have to do with: – hacker attacks • denial of service • server hijacking ...
... • Most security issues have to do with: – hacker attacks • denial of service • server hijacking ...
Name: Questions: (Total points = 135) Due by 11:59 PM 2/27/2017
... 14 Describe the use and function of the three types of memory in a desktop system. (6) 15 Compare the use of office suites and cloud computing. (4) 16 Describe at least three safeguards (may include actions and/or programs) that should be used to ensure your security when working (or browsing) on th ...
... 14 Describe the use and function of the three types of memory in a desktop system. (6) 15 Compare the use of office suites and cloud computing. (4) 16 Describe at least three safeguards (may include actions and/or programs) that should be used to ensure your security when working (or browsing) on th ...
What is Cookie?
... CoIDE has a more efficient way of sharing within it. Component Platform – Upload with just 5 steps ...
... CoIDE has a more efficient way of sharing within it. Component Platform – Upload with just 5 steps ...
Access Security Requirements
... • For interactive sessions (i.e. non system-to-system) ensure that passwords are changed periodically (every 90 days is recommended) 1.8 Passwords must be changed immediately when: • Any system access software is replaced by another system access software or is no longer used • The hardware on which ...
... • For interactive sessions (i.e. non system-to-system) ensure that passwords are changed periodically (every 90 days is recommended) 1.8 Passwords must be changed immediately when: • Any system access software is replaced by another system access software or is no longer used • The hardware on which ...
BLADE: An Attack-Agnostic Approach for Preventing Drive
... 1. Any new file created by a supervised process is redirected to the secure zone. 2. Any existing file modified by a supervised process is saved as a shadow copy in the secure zone, without change to the original file. 3. I/O redirection is transparent to supervised processes. 4. I/O redirection onl ...
... 1. Any new file created by a supervised process is redirected to the secure zone. 2. Any existing file modified by a supervised process is saved as a shadow copy in the secure zone, without change to the original file. 3. I/O redirection is transparent to supervised processes. 4. I/O redirection onl ...
Release notes for: CVSM version 2.00.05
... CVSM version 2.00.05 adds the following improvements: Prevents a wrench 01 error when over 300 patient records are stored on the device Prevents a wrench 06 error during boot, software update, or shut down Prevents a wrench 14 error when updating FSS module software Prevents a “NIBP Not Func ...
... CVSM version 2.00.05 adds the following improvements: Prevents a wrench 01 error when over 300 patient records are stored on the device Prevents a wrench 06 error during boot, software update, or shut down Prevents a wrench 14 error when updating FSS module software Prevents a “NIBP Not Func ...
Evaluation and Assurance - NYU Polytechnic School of
... • Instead, systems are sometimes built from enclaves of workstations and network elements Within the enclave everything is at one level Commercial Off The Shelf (COTS) products (workstations, network elements) can be used C2 (Orange book) or lower EAL (common criteria) is OK Enclaves can be ...
... • Instead, systems are sometimes built from enclaves of workstations and network elements Within the enclave everything is at one level Commercial Off The Shelf (COTS) products (workstations, network elements) can be used C2 (Orange book) or lower EAL (common criteria) is OK Enclaves can be ...
Creating a PC-based Information System: An Evolutionary/Revolutionary Visionary Approach
... package, we also have found it useful as a powerful pxogramming language for maintaining large databases and producing various !IIunmariud repxts. Our mgor concern in choosing programming languages is the ability to quickly grind out ad-hoc applicatiOllS. Lower 1evellanguages like FORTRAN and COBOL ...
... package, we also have found it useful as a powerful pxogramming language for maintaining large databases and producing various !IIunmariud repxts. Our mgor concern in choosing programming languages is the ability to quickly grind out ad-hoc applicatiOllS. Lower 1evellanguages like FORTRAN and COBOL ...
Introduction to Healthcare Information Technology
... Introduction to Healthcare Information Technology ...
... Introduction to Healthcare Information Technology ...
Auditing (cont'd.) - Elgin Community College
... • Moving and Copying Encrypted Files • Encrypted files behave differently when copied or moved • Rules for moving and copying encrypted files • An unencrypted file copied or moved to an encrypted folder becomes ...
... • Moving and Copying Encrypted Files • Encrypted files behave differently when copied or moved • Rules for moving and copying encrypted files • An unencrypted file copied or moved to an encrypted folder becomes ...
Information Assurance (IA) Framework
... of trustworthiness for the transaction may have to be identified. Thus it may be possible that a transaction may be completed, but not trusted. Or, it may be trusted a small amount, but not completely. The UCDMO was established in July 2006. All DoD and Intelligence Community (IC) cross domain effor ...
... of trustworthiness for the transaction may have to be identified. Thus it may be possible that a transaction may be completed, but not trusted. Or, it may be trusted a small amount, but not completely. The UCDMO was established in July 2006. All DoD and Intelligence Community (IC) cross domain effor ...
pptx
... Definition. A universal user for a goal G = (ENV,R) and a class of servers S is a user strategy s.t. for every server S in S and every initial state of S and ENV, the user achieves G.(w.h.p.) WE WILL SAY THAT THE UNIVERSAL ...
... Definition. A universal user for a goal G = (ENV,R) and a class of servers S is a user strategy s.t. for every server S in S and every initial state of S and ENV, the user achieves G.(w.h.p.) WE WILL SAY THAT THE UNIVERSAL ...