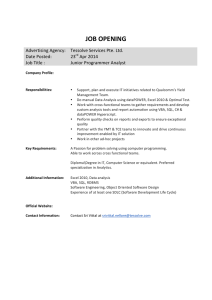
Tessolve Services Pte Ltd - Junior Programmer Analyst
... Do manual Data Analysis using dataPOWER, Excel 2010 & Optimal Test. Work with cross-‐functional teams to gather requirements and develop custom analysis tools and report automation using VBA, SQL, C# & d ...
... Do manual Data Analysis using dataPOWER, Excel 2010 & Optimal Test. Work with cross-‐functional teams to gather requirements and develop custom analysis tools and report automation using VBA, SQL, C# & d ...
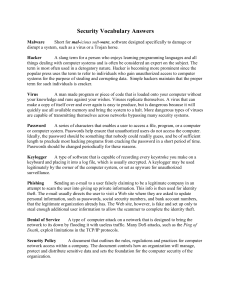
ITS_8_Security Vocab Answers
... the original fails or is destroyed by viruses, natural disaster, or other misfortune happens. One should always back up their files regularly. Physical Security Refers to doors, locks, access control, and other features that physically separate your important data from unauthorized access. Encryptio ...
... the original fails or is destroyed by viruses, natural disaster, or other misfortune happens. One should always back up their files regularly. Physical Security Refers to doors, locks, access control, and other features that physically separate your important data from unauthorized access. Encryptio ...
Security at the Operating System Level (Microsoft)
... New set of features for a future operating system – previously codenamed “Palladium” Promises to provide greater security, enhanced personal privacy, and system integrity. Applications that would make use of “Palladium’s” security features are codenamed “Trusted Agents.” ...
... New set of features for a future operating system – previously codenamed “Palladium” Promises to provide greater security, enhanced personal privacy, and system integrity. Applications that would make use of “Palladium’s” security features are codenamed “Trusted Agents.” ...
Computer Science or Software Engineering?
... Computer Science or Software Engineering? Nearly three out of four new science or engineering jobs in the United States will be in computing, according to the Bureau of Labor Statistics. But what kind of computing job is right for you? If you are interested in majoring in either computer science or ...
... Computer Science or Software Engineering? Nearly three out of four new science or engineering jobs in the United States will be in computing, according to the Bureau of Labor Statistics. But what kind of computing job is right for you? If you are interested in majoring in either computer science or ...
This Article argues that intellectual property law stifles critical
... vulnerabilities. Researchers who discover flaws often face legal threats based on IP claims if they reveal findings to anyone other than the software’s vendor. Externalities and network effects cause vendors’ incentives to diverge from those that are socially optimal. Unlike previous scholarship, th ...
... vulnerabilities. Researchers who discover flaws often face legal threats based on IP claims if they reveal findings to anyone other than the software’s vendor. Externalities and network effects cause vendors’ incentives to diverge from those that are socially optimal. Unlike previous scholarship, th ...
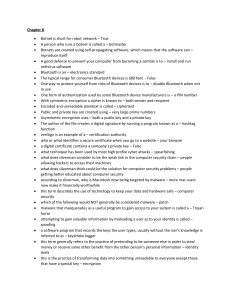
CH 8 – Review - WordPress.com
... Biometrics – devices that scan human features such as the retina to identify an individual Rootkit – a set of programs or utilities designed to allow a hacker to control a victim computer’s hardware and software and permit a hacker to monitor the user’s actions WPA – encryption standard used to prot ...
... Biometrics – devices that scan human features such as the retina to identify an individual Rootkit – a set of programs or utilities designed to allow a hacker to control a victim computer’s hardware and software and permit a hacker to monitor the user’s actions WPA – encryption standard used to prot ...