Journal Information Sheet - Society for Industrial and Applied
... of computer science and nonnumerical computing. Topics include but are not limited to analysis and design of algorithms, algorithmic game theory, data structures, computational complexity, computational algebra, computational aspects of combinatorics and graph theory, computational biology, computat ...
... of computer science and nonnumerical computing. Topics include but are not limited to analysis and design of algorithms, algorithmic game theory, data structures, computational complexity, computational algebra, computational aspects of combinatorics and graph theory, computational biology, computat ...
Symbian - T-Dose
... Ensure Understandability • Users are the weakest point of secure systems • Users don’t understand technology • DON’T offload decisions to them – No IE-like prompts ...
... Ensure Understandability • Users are the weakest point of secure systems • Users don’t understand technology • DON’T offload decisions to them – No IE-like prompts ...
Chapter 10: Electronic Commerce Security
... Person or device that can listen in on and copy Internet transmissions ...
... Person or device that can listen in on and copy Internet transmissions ...
Orange Book Summary - UMBC Center for Information Security and
... Username and Password protection and secure authorisations database (ADB). Protected operating system and system operations mode. Periodic integrity checking of TCB. Tested security mechanisms with no obvious bypasses. Documentation for User Security. Documentation for Systems Administration Securit ...
... Username and Password protection and secure authorisations database (ADB). Protected operating system and system operations mode. Periodic integrity checking of TCB. Tested security mechanisms with no obvious bypasses. Documentation for User Security. Documentation for Systems Administration Securit ...
Soft Computing
... approximation. In effect, the role model for soft computing is the human mind. Soft Computing became a formal area of study in Computer Science in the early 1990s. The soft computing solutions are unpredictable, uncertain, Earlier computational approaches could model and precisely analyze only relat ...
... approximation. In effect, the role model for soft computing is the human mind. Soft Computing became a formal area of study in Computer Science in the early 1990s. The soft computing solutions are unpredictable, uncertain, Earlier computational approaches could model and precisely analyze only relat ...
4. Database Administration - Midlands State University
... On completion of work related learning placement a student should have gained satisfactory practical exposure in at least three (3) of the following areas (exposure in all areas would be to the student’s advantage): NB: The external supervisor should indicate those areas a student would gain exposur ...
... On completion of work related learning placement a student should have gained satisfactory practical exposure in at least three (3) of the following areas (exposure in all areas would be to the student’s advantage): NB: The external supervisor should indicate those areas a student would gain exposur ...
Preventing Social Engineering
... More of a nuisance than a threat Spread using social engineering techniques Productivity and resource cost ...
... More of a nuisance than a threat Spread using social engineering techniques Productivity and resource cost ...
Types of Surveillance Technology Currently Used by Governments
... At present, users obtain various online identities (“IDs”) from ...
... At present, users obtain various online identities (“IDs”) from ...
Network Security
... PGP (short for Pretty Good Privacy), created by Philip Zimmermann, is the de facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digit ...
... PGP (short for Pretty Good Privacy), created by Philip Zimmermann, is the de facto standard program for secure e-mail and file encryption on the Internet. Its public-key cryptography system enables people who have never met to secure transmitted messages against unauthorized reading and to add digit ...
Operating Systems 4
... If a process is allowed to alter the timer that controls the system’s multiprogramming system, that process can extend its time slice and dominate the machine. If a process is allowed to access peripheral devices directly, then it can read files without supervision by the system’s file manager. If a ...
... If a process is allowed to alter the timer that controls the system’s multiprogramming system, that process can extend its time slice and dominate the machine. If a process is allowed to access peripheral devices directly, then it can read files without supervision by the system’s file manager. If a ...
Document
... • Push-button, drop-in co-processor for every application o 10,000X speedup over general-purpose for $10K • Push-button, application specific reconfiguration o 1000X speedup in a commodity node • Stay within today's power envelope, chip area, system form factor • Scalable o All form factors -- handh ...
... • Push-button, drop-in co-processor for every application o 10,000X speedup over general-purpose for $10K • Push-button, application specific reconfiguration o 1000X speedup in a commodity node • Stay within today's power envelope, chip area, system form factor • Scalable o All form factors -- handh ...
Enhanced Security Models for Operating Systems: A Cryptographic
... control (DAC) where each user determines security policy. However, Mandatory Access control(MAC) involves a “security administrator” who determines security policy. ...
... control (DAC) where each user determines security policy. However, Mandatory Access control(MAC) involves a “security administrator” who determines security policy. ...
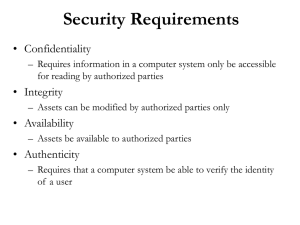
The Need for Security
... 95 percent of software security bugs come from 19 ‘common, well-understood’ programming mistakes Software can be correct without being secure. There is an imbalance between our abilities as developers and the abilities and resources of the attacker. ...
... 95 percent of software security bugs come from 19 ‘common, well-understood’ programming mistakes Software can be correct without being secure. There is an imbalance between our abilities as developers and the abilities and resources of the attacker. ...
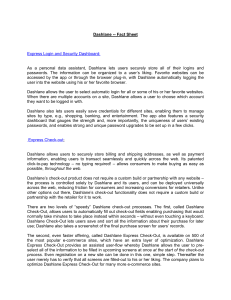
Dashlane -- Fact Sheet Express Login and Security Dashboard: As a
... information, enabling users to transact seamlessly and quickly across the web. Its patented click-to-pay technology – no typing required! – allows consumers to make buying as easy as possible, throughout the web. Dashlane’s check-out product does not require a custom build or partnership with any we ...
... information, enabling users to transact seamlessly and quickly across the web. Its patented click-to-pay technology – no typing required! – allows consumers to make buying as easy as possible, throughout the web. Dashlane’s check-out product does not require a custom build or partnership with any we ...
ppt
... Situation at UNI Novi Sad Software engineering curriculum: -Bachelor Informatics 3 years’ -Master in Informatics (a module - Master in ...
... Situation at UNI Novi Sad Software engineering curriculum: -Bachelor Informatics 3 years’ -Master in Informatics (a module - Master in ...
Malware - UTK-EECS
... A rootkit is a type of nefarious software that is installed through privilege escalation to perform malicious activities on a compromised system, cloaking its presence in the process. Rootkits can only be detected when there is some flaw in their cloaking mechanisms. Because they can intercept opera ...
... A rootkit is a type of nefarious software that is installed through privilege escalation to perform malicious activities on a compromised system, cloaking its presence in the process. Rootkits can only be detected when there is some flaw in their cloaking mechanisms. Because they can intercept opera ...
Computer Science, MSCS - Northeastern University
... Computer Science, MSCS Northeastern University’s Master of Science in Computer Science is designed to prepare students for a variety of careers in computer science. The program combines both computing and important application domains—enabling you to increase your broad-based knowledge in the field ...
... Computer Science, MSCS Northeastern University’s Master of Science in Computer Science is designed to prepare students for a variety of careers in computer science. The program combines both computing and important application domains—enabling you to increase your broad-based knowledge in the field ...
Security - NYU Stern School of Business
... • Stern approach: Every time the user logs in to his machine the computer downloads the most current version of antivirus software from the network ...
... • Stern approach: Every time the user logs in to his machine the computer downloads the most current version of antivirus software from the network ...
Document
... Provide this feedback to IT. This feedback was key to implementing a program with University-wide acceptance. The User community was part of the decision-making and the overall process. ...
... Provide this feedback to IT. This feedback was key to implementing a program with University-wide acceptance. The User community was part of the decision-making and the overall process. ...
TechQual+ - Information Technology
... – Having adequate capacity (speed, bandwidth) on the wired network – Having adequate capacity (speed, bandwidth) on the wireless network – Having wireless network coverage that covers all the areas in which I work and learn – Having access to critical campus resources from off-campus (at home, trave ...
... – Having adequate capacity (speed, bandwidth) on the wired network – Having adequate capacity (speed, bandwidth) on the wireless network – Having wireless network coverage that covers all the areas in which I work and learn – Having access to critical campus resources from off-campus (at home, trave ...
Access Control, Operations Security, and Computer Forensics
... • Provides access control for routers, network access servers and other networked computing devices via one or more centralized servers. • Provides separate authentication, authorization and accounting services. • Two factor Authentication • User can change password • Ability to use secure tokens • ...
... • Provides access control for routers, network access servers and other networked computing devices via one or more centralized servers. • Provides separate authentication, authorization and accounting services. • Two factor Authentication • User can change password • Ability to use secure tokens • ...
slides [pdf]
... 5. “Unlinkability: Challengers should not be able to link two different attestation sessions.” 6. “Availability: When modifying a platform configuration without changing the provided properties, access to sealed data should be possible.” 7. “Privacy: Users should be able to control which property th ...
... 5. “Unlinkability: Challengers should not be able to link two different attestation sessions.” 6. “Availability: When modifying a platform configuration without changing the provided properties, access to sealed data should be possible.” 7. “Privacy: Users should be able to control which property th ...
William Stallings, Cryptography and Network Security 3/e
... one of the most famous security models implemented as mandatory policies on system has two key policies: no read up (simple security property) – a subject can only read/write an object if the current security level of the subject dominates (>=) the classification of the object ...
... one of the most famous security models implemented as mandatory policies on system has two key policies: no read up (simple security property) – a subject can only read/write an object if the current security level of the subject dominates (>=) the classification of the object ...











![slides [pdf]](http://s1.studyres.com/store/data/003737230_1-2696b7865b4160afff3b6862ae017bef-300x300.png)