Configuring portal authentication
... The information contained herein is subject to change without notice. The only warranties for Hewlett Packard Enterprise products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional wa ...
... The information contained herein is subject to change without notice. The only warranties for Hewlett Packard Enterprise products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional wa ...
Secure Mobile Access 12.0
... Copyright© 2016 Dell™ SonicWALL™ All rights reserved. This product is protected by U.S. and international copyright and intellectual property laws. Dell™, SonicWALL™ and the Dell logo are trademarks of Dell in the United States and/or other jurisdictions. All other marks and names mentioned herein ...
... Copyright© 2016 Dell™ SonicWALL™ All rights reserved. This product is protected by U.S. and international copyright and intellectual property laws. Dell™, SonicWALL™ and the Dell logo are trademarks of Dell in the United States and/or other jurisdictions. All other marks and names mentioned herein ...
Cisco SAFE Reference Guide
... CCDE, CCENT, Cisco Eos, Cisco Lumin, Cisco Nexus, Cisco StadiumVision, Cisco TelePresence, Cisco WebEx, the Cisco logo, DCE, and Welcome to the Human Network are trademarks; Changing the Way We Work, Live, Play, and Learn and Cisco Store are service marks; and Access Registrar, Aironet, AsyncOS, Bri ...
... CCDE, CCENT, Cisco Eos, Cisco Lumin, Cisco Nexus, Cisco StadiumVision, Cisco TelePresence, Cisco WebEx, the Cisco logo, DCE, and Welcome to the Human Network are trademarks; Changing the Way We Work, Live, Play, and Learn and Cisco Store are service marks; and Access Registrar, Aironet, AsyncOS, Bri ...
HotView Pro 10.17.0.0
... Applying a management license to a mesh node .................................................. 82 Installing license keys on an existing mesh ....................................................... 84 Modifying the HotPort List........................................................................ ...
... Applying a management license to a mesh node .................................................. 82 Installing license keys on an existing mesh ....................................................... 84 Modifying the HotPort List........................................................................ ...
Configuring Security Access Control Lists
... All ACLs have an implicit deny entry at the end of the ACL, so, unless you explicitly permit it, traffic cannot pass. For example, if you want to allow all users to access a network through the ACE except for those users with particular IP addresses, then you must deny the particular IP addresses in ...
... All ACLs have an implicit deny entry at the end of the ACL, so, unless you explicitly permit it, traffic cannot pass. For example, if you want to allow all users to access a network through the ACE except for those users with particular IP addresses, then you must deny the particular IP addresses in ...
Lock-and-key security : evaluation of Telnet as an - Archipel
... I would like to thank Mr. Cloutier, the director of the Management Information Systems master program, who made this work possible to happen, allowing me to continue my studies and giving me the chance to earn my degree after many years away from school. My thanks also go for Mrs. Côté, the secretar ...
... I would like to thank Mr. Cloutier, the director of the Management Information Systems master program, who made this work possible to happen, allowing me to continue my studies and giving me the chance to earn my degree after many years away from school. My thanks also go for Mrs. Côté, the secretar ...
PLCsecurity_@_ABT-ABOC_20070122 - Indico
... ► I can stop any PLC at CERN. ► I can modify its contents. ► I just need an Ethernet connection to it. ► I (engineer, operator) might have finger-trouble. ► I (virus) do not care that it’s a PLC. ► I (attacker) might do this on purpose. ...
... ► I can stop any PLC at CERN. ► I can modify its contents. ► I just need an Ethernet connection to it. ► I (engineer, operator) might have finger-trouble. ► I (virus) do not care that it’s a PLC. ► I (attacker) might do this on purpose. ...
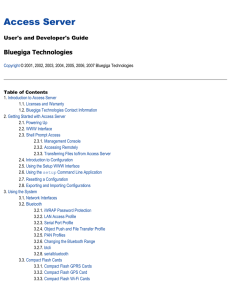
Access Server - SemiconductorStore.com
... Bluetooth OBEX (Object Push and File Transfer Profiles) to/from directory /tmp/obex in Access Server NFS (mount an NFS share from a remote computer as a part of Access Server's file system) SSHFS (mount an Access Server directory over SSH as a part of any other Linux host file system) To download an ...
... Bluetooth OBEX (Object Push and File Transfer Profiles) to/from directory /tmp/obex in Access Server NFS (mount an NFS share from a remote computer as a part of Access Server's file system) SSHFS (mount an Access Server directory over SSH as a part of any other Linux host file system) To download an ...
AdderView CATxIP 5000
... provide full enterprise level security to restrict access to authorised personnel. Through the use of Console CAMs the AdderView CATxIP 5000 also allows global users to make console connections to one or more specialist servers or network devices; thus extending the flexibility of the remote managem ...
... provide full enterprise level security to restrict access to authorised personnel. Through the use of Console CAMs the AdderView CATxIP 5000 also allows global users to make console connections to one or more specialist servers or network devices; thus extending the flexibility of the remote managem ...
Exam Topics in This Chapter
... You must review the FTD software version release notes to become familiar with the supported features, because Cisco continues to add features regularly. ...
... You must review the FTD software version release notes to become familiar with the supported features, because Cisco continues to add features regularly. ...
Intruders and password protection
... Password Protection: The front line of defense against intruders is the password system. Virtually all multiuser systems require that a user provide not only a name or identifier (ID) but also a password. The password serves to authenticate the ID of the individual logging on to the system. In turn, ...
... Password Protection: The front line of defense against intruders is the password system. Virtually all multiuser systems require that a user provide not only a name or identifier (ID) but also a password. The password serves to authenticate the ID of the individual logging on to the system. In turn, ...
Building a Secure Computer System
... difficult undertaking. Mr. Gasser has accepted this formidable challenge and has succeeded beyond what even we optimists would expect. Although I recognized that Mr. Gasser was unquestionably qualified, I was frankly skeptical about whether or not it was possible to produce a practical, understandab ...
... difficult undertaking. Mr. Gasser has accepted this formidable challenge and has succeeded beyond what even we optimists would expect. Although I recognized that Mr. Gasser was unquestionably qualified, I was frankly skeptical about whether or not it was possible to produce a practical, understandab ...
SNMP Simple Network Management Protocol - CS-UCY
... ACCESS read-only STATUS mandatory DESCRIPTION "The number of input datagrams for which this entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this counter will in ...
... ACCESS read-only STATUS mandatory DESCRIPTION "The number of input datagrams for which this entity was not their final IP destination, as a result of which an attempt was made to find a route to forward them to that final destination. In entities which do not act as IP Gateways, this counter will in ...
Safe & Secure Environment for Students
... – 5 elementary schools, 2 middle schools, 1 high schools – Ensure students, teachers and administrators make the most of its computing technology – while receiving only appropriate Internet content – Previous filtering solution provided inadequate integration with user directories, ...
... – 5 elementary schools, 2 middle schools, 1 high schools – Ensure students, teachers and administrators make the most of its computing technology – while receiving only appropriate Internet content – Previous filtering solution provided inadequate integration with user directories, ...
Binding Authentication to Provisioning
... applications that require authentication before a user can use them. Currently, a common situation is that users who want to access a network, like the internet, need to give their username and password in order to use the network2. This is called Authenticated Access Control: there is control over ...
... applications that require authentication before a user can use them. Currently, a common situation is that users who want to access a network, like the internet, need to give their username and password in order to use the network2. This is called Authenticated Access Control: there is control over ...
Step 5: Securing Routing Protocols
... and also among the most difficult to eliminate. –DoS attacks prevent authorized people from using a service by consuming system resources. ...
... and also among the most difficult to eliminate. –DoS attacks prevent authorized people from using a service by consuming system resources. ...
Exploration CCNA4
... and also among the most difficult to eliminate. –DoS attacks prevent authorized people from using a service by consuming system resources. ...
... and also among the most difficult to eliminate. –DoS attacks prevent authorized people from using a service by consuming system resources. ...
RADIUS Implementation and Deployment Best Practices
... (OTP), MD5-Challenge, Transport Level Security (TLS) for smart card and certificate support, as well as any future authentication technologies. EAP is a critical technology component for secure connections. In addition to support within PPP, EAP is also supported within the IEEE 802 link layer. IEEE ...
... (OTP), MD5-Challenge, Transport Level Security (TLS) for smart card and certificate support, as well as any future authentication technologies. EAP is a critical technology component for secure connections. In addition to support within PPP, EAP is also supported within the IEEE 802 link layer. IEEE ...
InkTag: Secure Applications on an Untrusted Operating System
... Though feasible, efficiently and safely verifying OS behavior remains a significant challenge. The InkTag hypervisor must implement deep introspection into architecture-level primitives, such as page tables, to isolate trusted applications from an untrusted operating system. The range of “normal” op ...
... Though feasible, efficiently and safely verifying OS behavior remains a significant challenge. The InkTag hypervisor must implement deep introspection into architecture-level primitives, such as page tables, to isolate trusted applications from an untrusted operating system. The range of “normal” op ...
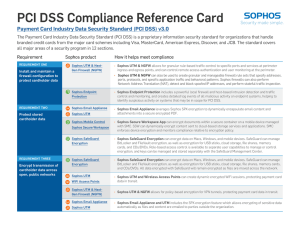
PCI DSS Compliance Reference Card
... Payment Card Industry Data Security Standard (PCI DSS) v3.0 The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, ...
... Payment Card Industry Data Security Standard (PCI DSS) v3.0 The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, ...
Defending the Cloud from the Full Stack Hack
... Use APIs to snapshot the disk, mount snapshots on different system, and extract everything without touching the network or system Zero indication from traditional controls that any access has taken place Same is true of cloud databases, I don’t need your passwords or even SQL Injection, I just need ...
... Use APIs to snapshot the disk, mount snapshots on different system, and extract everything without touching the network or system Zero indication from traditional controls that any access has taken place Same is true of cloud databases, I don’t need your passwords or even SQL Injection, I just need ...
Introduction to Information Security Chapter 2
... Set remainder address to address of process’ level of privilege Compute 25/5 and you have level 0 (kernel) privileges Check for type, format, range of values, access rights, presence (or absence) Slide 42 ...
... Set remainder address to address of process’ level of privilege Compute 25/5 and you have level 0 (kernel) privileges Check for type, format, range of values, access rights, presence (or absence) Slide 42 ...
Introduction to Computer Security
... Controls for Computer Systems” – Originally classified – declassified in 1979 ...
... Controls for Computer Systems” – Originally classified – declassified in 1979 ...
Slide 1
... with rules identifying known penetration, weakness patterns, or suspicious behavior rules usually machine & O/S specific rules are generated by experts who interview & codify knowledge of security admins quality depends on how well this is done compare audit records or states against rules ...
... with rules identifying known penetration, weakness patterns, or suspicious behavior rules usually machine & O/S specific rules are generated by experts who interview & codify knowledge of security admins quality depends on how well this is done compare audit records or states against rules ...
Access control
_before_allowing_a_driver_to_enter_the_gate_at_U.S._Fleet_Activities_Sasebo,_Japan.jpg?width=300)
In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.Locks and login credentials are two analogous mechanisms of access control.