William Stallings, Cryptography and Network Security 5/e
... Defines a single choke point that keeps unauthorized users out of the protected network, prohibits potentially vulnerable services from entering or leaving the network, and provides protection from various kinds of IP spoofing and routing ...
... Defines a single choke point that keeps unauthorized users out of the protected network, prohibits potentially vulnerable services from entering or leaving the network, and provides protection from various kinds of IP spoofing and routing ...
Exploration CCNA4 - Collin College Faculty Website Directory
... uses to ensure that only authorized personnel have access to its data. • Internet access policy - Defines what the company will and will not tolerate with respect to the use of its Internet connectivity by employees and guests. • Campus access policy - Defines acceptable use of campus technology res ...
... uses to ensure that only authorized personnel have access to its data. • Internet access policy - Defines what the company will and will not tolerate with respect to the use of its Internet connectivity by employees and guests. • Campus access policy - Defines acceptable use of campus technology res ...
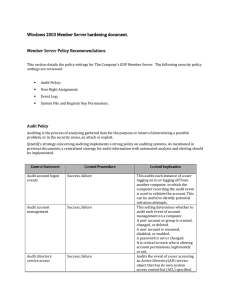
Server hardening - Cisco Security Solutions
... Audits each instance of a user logging on to, logging off from, or making a network connection to the computer recording the audit event. Useful for forensics purposes. Audits the event of a user accessing an object that has its own system ACLs specified. The object also requires auditing settings t ...
... Audits each instance of a user logging on to, logging off from, or making a network connection to the computer recording the audit event. Useful for forensics purposes. Audits the event of a user accessing an object that has its own system ACLs specified. The object also requires auditing settings t ...
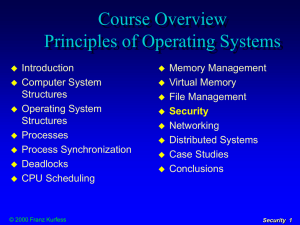
Security
... systems may be of considerable value and must be protected from damage hardware, software, and stored data may be essential for the performance of tasks and need to be available when needed system objects need to be protected from inadvertent unauthorized access or use there is the possibility ...
... systems may be of considerable value and must be protected from damage hardware, software, and stored data may be essential for the performance of tasks and need to be available when needed system objects need to be protected from inadvertent unauthorized access or use there is the possibility ...
Linux+ Guide to Linux Certification
... where data is put into a secret code – To communicate with another system, data is encrypted, transmitted, decrypted, and processed – Sender inserts public key with the message – Message receiver required to have private key to decode the message ...
... where data is put into a secret code – To communicate with another system, data is encrypted, transmitted, decrypted, and processed – Sender inserts public key with the message – Message receiver required to have private key to decode the message ...
Chapter 11 Outline
... The lack of a physical cable does not change security requirements—the wireless solution has to face a tougher standard. Offering wireless connectivity is equivalent to giving an outsider a network drop, and it must be assumed that an intruder is connected at all times. ...
... The lack of a physical cable does not change security requirements—the wireless solution has to face a tougher standard. Offering wireless connectivity is equivalent to giving an outsider a network drop, and it must be assumed that an intruder is connected at all times. ...
CCNPv5 Module 5 Lesson 1
... SNMP asks agents embedded in network devices for information or tells the agents to do something. ...
... SNMP asks agents embedded in network devices for information or tells the agents to do something. ...
Chapter 8
... Defines format of messages exchanged by management systems and agents. Specifies the Get, GetNext, Set, and Trap operations Security and administration capabilities The addition of these capabilities represents the major enhancement in SNMPv3 over SNMPv2 ...
... Defines format of messages exchanged by management systems and agents. Specifies the Get, GetNext, Set, and Trap operations Security and administration capabilities The addition of these capabilities represents the major enhancement in SNMPv3 over SNMPv2 ...
Chapter 8
... Defines format of messages exchanged by management systems and agents. Specifies the Get, GetNext, Set, and Trap operations Security and administration capabilities The addition of these capabilities represents the major enhancement in SNMPv3 over SNMPv2 ...
... Defines format of messages exchanged by management systems and agents. Specifies the Get, GetNext, Set, and Trap operations Security and administration capabilities The addition of these capabilities represents the major enhancement in SNMPv3 over SNMPv2 ...
Teaching Computer Security using Minix
... Set-UID escalates a process’s privilege Set-Nobody restricts a process’s privilege Set the effective user to “nobody” ...
... Set-UID escalates a process’s privilege Set-Nobody restricts a process’s privilege Set the effective user to “nobody” ...
MAC Address Authentication - Faculty Website Directory
... Six categories of attackers: Hackers - Not malicious; expose security flaws, “ethical attackers” Crackers – Violates system security with malicious intent Script kiddies- Break into computers to create damage Spies – Hired to break in and steal information Employees-Unhappy employees that steal, dam ...
... Six categories of attackers: Hackers - Not malicious; expose security flaws, “ethical attackers” Crackers – Violates system security with malicious intent Script kiddies- Break into computers to create damage Spies – Hired to break in and steal information Employees-Unhappy employees that steal, dam ...
Information Assurance (IA) Framework
... on traditional guard-like approaches, meaning that they generally have components such as a communication handler, a filter orchestrator, the actual filters, and the cross domain component, their security attack surface is extensive. Additionally, because of the many millions of lines of code involv ...
... on traditional guard-like approaches, meaning that they generally have components such as a communication handler, a filter orchestrator, the actual filters, and the cross domain component, their security attack surface is extensive. Additionally, because of the many millions of lines of code involv ...
Document
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
Management Information Systems Chapter 10 Security and Control
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
... • Public key encryption: Uses two different keys, one private and one public. The keys are mathematically related so that data encrypted with one key can be decrypted using only the other key • Message integrity: The ability to be certain that the message being sent arrives at the proper destination ...
Security Features in Windows CE
... inside a database volume does not give it any additional security. Therefore, this feature is most useful in databases that are stored within the object store. Removing the system file attribute from a database volume that contains a system database will expose that database to access by untrusted a ...
... inside a database volume does not give it any additional security. Therefore, this feature is most useful in databases that are stored within the object store. Removing the system file attribute from a database volume that contains a system database will expose that database to access by untrusted a ...
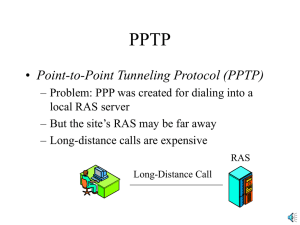
PPTP
... – But the site’s RAS may be far away – Long-distance calls are expensive RAS Long-Distance Call ...
... – But the site’s RAS may be far away – Long-distance calls are expensive RAS Long-Distance Call ...
Permissions
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
... • Users do not have to remember multiple user names and passwords • Logins are controlled by Windows password policies • Logins can be mapped to a single user, or Windows group account • Non-Windows users (i.e. MAC) cannot log in to SQL Server © Wiley Inc. 2006. All Rights Reserved. ...
Expediting Incident Response with Foundstone ERS
... It discovers hosts and network devices, collects data about them, and illustrates this information in easy-toread tables and diagrams. Foundstone ERS also helps the CSIRT understand a device’s context, how it fits within the overall network topology. Although the concept is simple, the value of an u ...
... It discovers hosts and network devices, collects data about them, and illustrates this information in easy-toread tables and diagrams. Foundstone ERS also helps the CSIRT understand a device’s context, how it fits within the overall network topology. Although the concept is simple, the value of an u ...
Vindicator® V5 Intrusion Detection System (IDS)
... solutions. With its built-in support for redundant ...
... solutions. With its built-in support for redundant ...
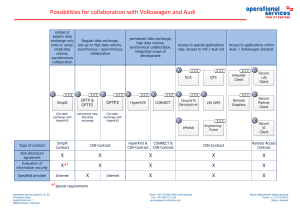
Possibilities for collaboration with Volkswagen
... the contractual relationship with Volkswagen. If users are absent from their workplaces, they have to remove the authorization objects (PKI card or similar) provided to them for performing their activities from the working environment and from the terminal and personally hold them in safe keeping. T ...
... the contractual relationship with Volkswagen. If users are absent from their workplaces, they have to remove the authorization objects (PKI card or similar) provided to them for performing their activities from the working environment and from the terminal and personally hold them in safe keeping. T ...
Junos Pulse Access Control Service
... credentials, and assesses the device’s security state. Junos Pulse leverages and integrates with the native 802.1X supplicant available within Microsoft Windows to deliver comprehensive L2 access control. Junos Pulse Access Control Service can also support native 802.1X supplicants on Apple Mac OS X ...
... credentials, and assesses the device’s security state. Junos Pulse leverages and integrates with the native 802.1X supplicant available within Microsoft Windows to deliver comprehensive L2 access control. Junos Pulse Access Control Service can also support native 802.1X supplicants on Apple Mac OS X ...
Module 7 Active Directory and Account Management
... – Any change on one DC is replicated to all other DCs – If one DC fails, there is no visible network interruption ...
... – Any change on one DC is replicated to all other DCs – If one DC fails, there is no visible network interruption ...
Operating System Security Rules
... login attempts. It is highly unlikely that the user will enter their password incorrectly that many times. When the account is disabled only the administrator will be able to enable the account again. If an attack is actually occurring, the administrator must change the user name of the account and ...
... login attempts. It is highly unlikely that the user will enter their password incorrectly that many times. When the account is disabled only the administrator will be able to enable the account again. If an attack is actually occurring, the administrator must change the user name of the account and ...
protect a system from cyber attacks?
... computer systems and through computer networks. The objective of cyber security is to protect information and physical assets from theft, corruption, or natural disaster, while allowing the information and assets to remain accessible and productive to its intended users. It is composed of procedures ...
... computer systems and through computer networks. The objective of cyber security is to protect information and physical assets from theft, corruption, or natural disaster, while allowing the information and assets to remain accessible and productive to its intended users. It is composed of procedures ...
Sun Microsystems
... Microsystems, Inc. to its position as a leading provider of industrial-strength hardware, software and services that make the Net work. Sun can be found in more than 100 countries and on the World Wide Web at http://sun.com. BUSINESS CHALLENGE The virtual enterprise is quickly becoming a reality as ...
... Microsystems, Inc. to its position as a leading provider of industrial-strength hardware, software and services that make the Net work. Sun can be found in more than 100 countries and on the World Wide Web at http://sun.com. BUSINESS CHALLENGE The virtual enterprise is quickly becoming a reality as ...
Access control
_before_allowing_a_driver_to_enter_the_gate_at_U.S._Fleet_Activities_Sasebo,_Japan.jpg?width=300)
In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.Locks and login credentials are two analogous mechanisms of access control.