Firewall
... • use an application specific gateway / proxy • has full access to protocol – user requests service from proxy – proxy validates request as legal – then actions request and returns result to user ...
... • use an application specific gateway / proxy • has full access to protocol – user requests service from proxy – proxy validates request as legal – then actions request and returns result to user ...
ppt
... control as a way of saying that the system lacks mandatory access control. On the other hand, systems can be said to implement both MAC and DAC simultaneously, where DAC refers to one category of access controls that subjects can transfer among each other and MAC refers to a second category of acces ...
... control as a way of saying that the system lacks mandatory access control. On the other hand, systems can be said to implement both MAC and DAC simultaneously, where DAC refers to one category of access controls that subjects can transfer among each other and MAC refers to a second category of acces ...
Access Control, Operations Security, and Computer Forensics
... Often used as a stepping stone to TACACS+ Radius Server contains dynamic password and network service access information (Network ACLS) • Radius is a fully open protocol, can be customized for almost any security system • Can be used with Kerberos and provides CHAP remote node authentication • Excep ...
... Often used as a stepping stone to TACACS+ Radius Server contains dynamic password and network service access information (Network ACLS) • Radius is a fully open protocol, can be customized for almost any security system • Can be used with Kerberos and provides CHAP remote node authentication • Excep ...
Access Control, Operations Security, and Computer Forensics
... • Provides access control for routers, network access servers and other networked computing devices via one or more centralized servers. • Provides separate authentication, authorization and accounting services. • Two factor Authentication • User can change password • Ability to use secure tokens • ...
... • Provides access control for routers, network access servers and other networked computing devices via one or more centralized servers. • Provides separate authentication, authorization and accounting services. • Two factor Authentication • User can change password • Ability to use secure tokens • ...
ComView SM
... ComView SM is a cost-effective secure modem for dial-up access to serial or IP network administered equipment. It is also a VPN gateway for secure network access to serial administered equipment from the Internet/ Intranet. ComView SM integrates a high-performance 32-bit security network processor, ...
... ComView SM is a cost-effective secure modem for dial-up access to serial or IP network administered equipment. It is also a VPN gateway for secure network access to serial administered equipment from the Internet/ Intranet. ComView SM integrates a high-performance 32-bit security network processor, ...
SAFEnet Becomes First PACS Platform to
... of federal, state and local governments because they cost-effectively deliver the most flexible, reliable and advanced unified security solution available in the industry. The same holds true with commercial organizations across the nation who regularly do business with the Federal Government and Do ...
... of federal, state and local governments because they cost-effectively deliver the most flexible, reliable and advanced unified security solution available in the industry. The same holds true with commercial organizations across the nation who regularly do business with the Federal Government and Do ...
$doc.title
... entry operators have no access to resources. Which of the following access control models is implemented in the organization? A. Role-based access control (RBAC) B. Network-based access control (NBAC) C. Mandatory Access Control (MAC) D. Discretionary access control (DAC) Answer: A 9. Which of the f ...
... entry operators have no access to resources. Which of the following access control models is implemented in the organization? A. Role-based access control (RBAC) B. Network-based access control (NBAC) C. Mandatory Access Control (MAC) D. Discretionary access control (DAC) Answer: A 9. Which of the f ...
Access Control Policies
... not able to decide which other entities they want to allow to access resources, the system rules apply the system denies users full control over access to the resources they create ...
... not able to decide which other entities they want to allow to access resources, the system rules apply the system denies users full control over access to the resources they create ...
AccessControlSimulation
... During its monthly compliance check in August 2011, the agency identified 16 users who had been granted access to the procurement system without receiving approval from the agency’s authorization system. ...
... During its monthly compliance check in August 2011, the agency identified 16 users who had been granted access to the procurement system without receiving approval from the agency’s authorization system. ...
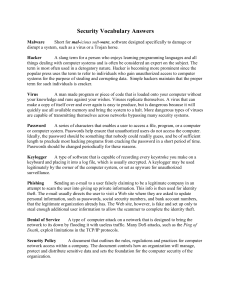
ITS_8_Security Vocab Answers
... the original fails or is destroyed by viruses, natural disaster, or other misfortune happens. One should always back up their files regularly. Physical Security Refers to doors, locks, access control, and other features that physically separate your important data from unauthorized access. Encryptio ...
... the original fails or is destroyed by viruses, natural disaster, or other misfortune happens. One should always back up their files regularly. Physical Security Refers to doors, locks, access control, and other features that physically separate your important data from unauthorized access. Encryptio ...
Q10 Study Guide - FSU Computer Science
... Explain the meaning of the term object as it relates to a computer system. What are the two general types of objects in a system? 2. A process is said to operate within a protection domain which specifies the resources that the process may access. List the ways that a domain can be realized. 3. What ...
... Explain the meaning of the term object as it relates to a computer system. What are the two general types of objects in a system? 2. A process is said to operate within a protection domain which specifies the resources that the process may access. List the ways that a domain can be realized. 3. What ...
$doc.title
... 8. An organization has implemented a hierarchical-based concept of privilege management in which administrators have full access, HR managers have less permission than the administrators, and data entry operators have no access to resources. Which of the following access control models is implemente ...
... 8. An organization has implemented a hierarchical-based concept of privilege management in which administrators have full access, HR managers have less permission than the administrators, and data entry operators have no access to resources. Which of the following access control models is implemente ...
TMDE Web Site
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
Computer Security
... Network architecture – Controlling flow of information – Network devices implemented ...
... Network architecture – Controlling flow of information – Network devices implemented ...
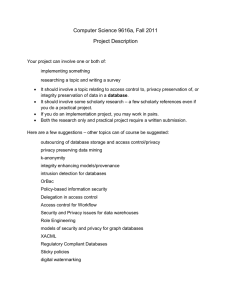
Computer Science 9616a, Fall 2011 Project Description Your project
... Here are a few suggestions – other topics can of course be suggested: outsourcing of database storage and access control/privacy privacy preserving data mining k-anonymity integrity enhancing models/provenance intrusion detection for databases OrBac Policy-based information security Delegation in ac ...
... Here are a few suggestions – other topics can of course be suggested: outsourcing of database storage and access control/privacy privacy preserving data mining k-anonymity integrity enhancing models/provenance intrusion detection for databases OrBac Policy-based information security Delegation in ac ...
DPI as a means of access segregation in a corporate
... - Making brand-new set of network rules is painful. ...
... - Making brand-new set of network rules is painful. ...
Computer Science 9616b, Fall 2016 Project Description Your project
... researching a topic and writing a survey/summary of the ideas ...
... researching a topic and writing a survey/summary of the ideas ...
Access control
_before_allowing_a_driver_to_enter_the_gate_at_U.S._Fleet_Activities_Sasebo,_Japan.jpg?width=300)
In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.Locks and login credentials are two analogous mechanisms of access control.