Slide 1
... with rules identifying known penetration, weakness patterns, or suspicious behavior rules usually machine & O/S specific rules are generated by experts who interview & codify knowledge of security admins quality depends on how well this is done compare audit records or states against rules ...
... with rules identifying known penetration, weakness patterns, or suspicious behavior rules usually machine & O/S specific rules are generated by experts who interview & codify knowledge of security admins quality depends on how well this is done compare audit records or states against rules ...
conklin_4e_PPT_ch11
... • Most operating systems use the concepts of permissions and rights to control and safeguard access to resources. • Windows operating system provides an example. – Uses the concepts of permissions and rights to control access to files, folders, and information resources – Uses user rights or privile ...
... • Most operating systems use the concepts of permissions and rights to control and safeguard access to resources. • Windows operating system provides an example. – Uses the concepts of permissions and rights to control access to files, folders, and information resources – Uses user rights or privile ...
LogMeIn Security – an In-Depth Look
... enable one or more of the extra security options that LogMeIn provides. One of these options is a sheet of printed One-Time-Passwords (OTPs). When the user enables the OTP option, he is required to print out a list of 9-character random passwords generated by the Gateway. Once this is done, subseque ...
... enable one or more of the extra security options that LogMeIn provides. One of these options is a sheet of printed One-Time-Passwords (OTPs). When the user enables the OTP option, he is required to print out a list of 9-character random passwords generated by the Gateway. Once this is done, subseque ...
Why Is PCI ImPortant to my small BusIness?
... configured remote access technologies used in their point-of-sale (POS) applications.—Examples of these technologies include, but are not limited to, the following: PCAnywhere, VNC, GoToMyPC. com, and Windows Remote Access. (Note: While these technologies offer security functionality, they are often ...
... configured remote access technologies used in their point-of-sale (POS) applications.—Examples of these technologies include, but are not limited to, the following: PCAnywhere, VNC, GoToMyPC. com, and Windows Remote Access. (Note: While these technologies offer security functionality, they are often ...
Advanced Operating Systems, CSci555
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
... Base conditions require presentation or availability of credential – Matching the condition brings in additional policy elements. ...
Remote Access—Attack Vectors
... A VPN provides protection, but it also presents an attractive target to attackers for two reasons: First, the VPN transmits sensitive information over public and shared networks. The extension of the network outside the perimeter makes assets much more accessible for attackers. The hackers no longer ...
... A VPN provides protection, but it also presents an attractive target to attackers for two reasons: First, the VPN transmits sensitive information over public and shared networks. The extension of the network outside the perimeter makes assets much more accessible for attackers. The hackers no longer ...
Network Infrastructure Security Good Practice Guide
... Use good practice set. The target audience for the good practice guides are all centers affiliated with CGIAR, and in particular, the IT teams within each center. The good practice set does not contain mandatory requirements that centers are required to implement. Instead, it outlines a number of go ...
... Use good practice set. The target audience for the good practice guides are all centers affiliated with CGIAR, and in particular, the IT teams within each center. The good practice set does not contain mandatory requirements that centers are required to implement. Instead, it outlines a number of go ...
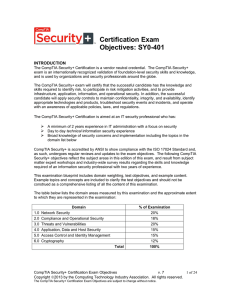
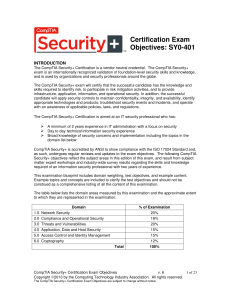
CompTIA Security (SY0-401)
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
OSI Defense in Depth to Increase Application Security
... Access control is in place when only authorized personnel are allowed physical access to computers and the network. This concept includes permitting only authorized personnel to possess logins and passwords and closing unmanaged wall ports which, if open, could provide unauthorized persons access to ...
... Access control is in place when only authorized personnel are allowed physical access to computers and the network. This concept includes permitting only authorized personnel to possess logins and passwords and closing unmanaged wall ports which, if open, could provide unauthorized persons access to ...
Certification Exam Objectives: SY0-401
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... • Risks associated with Cloud Computing and Virtualization • Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
MS Word template for internal docs
... Delivery and loading areas Control Access points such as delivery and loading areas and other points where unauthorized persons may enter the premises shall be controlled and, if possible, isolated from information processing facilities to avoid unauthorized access 2 - Equipment Objective: To prev ...
... Delivery and loading areas Control Access points such as delivery and loading areas and other points where unauthorized persons may enter the premises shall be controlled and, if possible, isolated from information processing facilities to avoid unauthorized access 2 - Equipment Objective: To prev ...
An Introduction to NIST Special Publication 800
... to protect CUI. In those instances, an institution should be prepared to ask for additional time to comply with NIST 8800-171 via the contractual negotiation process. The following paragraphs highlight how some institutions are approaching activities that may require NIST 800-171 compliance. Univers ...
... to protect CUI. In those instances, an institution should be prepared to ask for additional time to comply with NIST 8800-171 via the contractual negotiation process. The following paragraphs highlight how some institutions are approaching activities that may require NIST 800-171 compliance. Univers ...
About the Presentations
... File has restricted access Passwords are stored only after being encrypted with the salt value and an encoding algorithm ...
... File has restricted access Passwords are stored only after being encrypted with the salt value and an encoding algorithm ...
Oracle9i Security
... XML standard that facilitates integration among provisioning environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
... XML standard that facilitates integration among provisioning environments by defining the protocol for interaction between provisioning service components and agents representing provisioned services. ...
Final presentation
... Firewall with Modem Pool Firewall can not defend “back door” Collect modems connect to a terminal server Terminal server is a computer design for connecting modem to a network Terminal server provides restriction to connect some system Packet Filtering prevent insider system directly con ...
... Firewall with Modem Pool Firewall can not defend “back door” Collect modems connect to a terminal server Terminal server is a computer design for connecting modem to a network Terminal server provides restriction to connect some system Packet Filtering prevent insider system directly con ...
Easy Steps to Cisco Extended Access List
... based on source and destination IP address, port numbers and upper-layer protocols. Standard access list can deny or permit packets by source address only and permit or deny entire TCP/IP protocol suite. Therefore by extended, it means greater functionality and flexibility. Extended access list is a ...
... based on source and destination IP address, port numbers and upper-layer protocols. Standard access list can deny or permit packets by source address only and permit or deny entire TCP/IP protocol suite. Therefore by extended, it means greater functionality and flexibility. Extended access list is a ...
File
... The SOCKS server, which runs on a UNIX-based firewall The SOCKS client library, which runs on internal hosts protected by the firewall SOCKS-ified versions of several standard client programs such as FTP and TELNET When a TCP-based client wishes to establish a connection to an object that is ...
... The SOCKS server, which runs on a UNIX-based firewall The SOCKS client library, which runs on internal hosts protected by the firewall SOCKS-ified versions of several standard client programs such as FTP and TELNET When a TCP-based client wishes to establish a connection to an object that is ...
Hands-On Ethical Hacking and Network Security
... router (continued) Turn off SSID broadcast You should also change your SSID ...
... router (continued) Turn off SSID broadcast You should also change your SSID ...
PCI Self-Assessment Questionnaire
... Is there a password policy for non-consumer users that Yes enforces the use of strong passwords and prevents the resubmission of previously used passwords? ...
... Is there a password policy for non-consumer users that Yes enforces the use of strong passwords and prevents the resubmission of previously used passwords? ...
Slides - TERENA Networking Conference 2008
... Many Advances in Network Security Coming • Trusted Devices, Access Control, Coordinated Security, Policy TCG Welcomes Your Input Copyright © 2008 Juniper Networks, Inc. ...
... Many Advances in Network Security Coming • Trusted Devices, Access Control, Coordinated Security, Policy TCG Welcomes Your Input Copyright © 2008 Juniper Networks, Inc. ...
Illustrative Examples Threat Mitigation
... maintain under configuration control a current baseline configuration of information technology / operations technology systems ...
... maintain under configuration control a current baseline configuration of information technology / operations technology systems ...
Architecture Intégrée | Sécurité et protection de la propriété
... Physical – limit physical access to authorized personnel Cells/Areas, control panels, devices, cabling, and control room Network – security framework – e.g. firewall policies, access control list (ACL) policies for switches and routers, AAA, intrusion detection and prevention systems (IDS/IPS) ...
... Physical – limit physical access to authorized personnel Cells/Areas, control panels, devices, cabling, and control room Network – security framework – e.g. firewall policies, access control list (ACL) policies for switches and routers, AAA, intrusion detection and prevention systems (IDS/IPS) ...
Hands-On Ethical Hacking and Network Security
... Wireless NICs There are many wireless NICs on the market Choose yours depending on how you plan to use it Some tools require certain specific brands of NICs Cracking WEP requires NICs that can use monitor mode or perform packet injection ...
... Wireless NICs There are many wireless NICs on the market Choose yours depending on how you plan to use it Some tools require certain specific brands of NICs Cracking WEP requires NICs that can use monitor mode or perform packet injection ...
Security and Availability of Client Data
... are updated to include current trends and threats. We strive to conform to OWASP standards for our Web Applications. Architecture security reviews are performed when needed by the Security Team to ensure proper controls are in place and security standards are followed. ...
... are updated to include current trends and threats. We strive to conform to OWASP standards for our Web Applications. Architecture security reviews are performed when needed by the Security Team to ensure proper controls are in place and security standards are followed. ...
Access control
_before_allowing_a_driver_to_enter_the_gate_at_U.S._Fleet_Activities_Sasebo,_Japan.jpg?width=300)
In the fields of physical security and information security, access control is the selective restriction of access to a place or other resource. The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.Locks and login credentials are two analogous mechanisms of access control.