Distributed System Concepts and Architectures
... Objects to be protected are associated with servers managing objects Each object has a set of allowable well formed operations that can be invoked by the client processes ...
... Objects to be protected are associated with servers managing objects Each object has a set of allowable well formed operations that can be invoked by the client processes ...
Discovering Computers Fundamentals 3rd Edition
... Program that protects personal computer and its data from unauthorized intrusions Monitors transmissions to and from computer Informs you of attempted intrusion ...
... Program that protects personal computer and its data from unauthorized intrusions Monitors transmissions to and from computer Informs you of attempted intrusion ...
Chapter 4
... Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003 (CAN-SPAM) — A U.S. law passed in 2003 to limit the effect of spam. default password — A standard password that is configured on all equipment. denial-of-service (DoS) — An attack designed to prevent a device from ...
... Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003 (CAN-SPAM) — A U.S. law passed in 2003 to limit the effect of spam. default password — A standard password that is configured on all equipment. denial-of-service (DoS) — An attack designed to prevent a device from ...
VirtuWind–Security in a Virtual and Programmable Industrial
... for north-/southbound and inter-controller interfaces, securing the controller can prevent adversaries from applying Denial of Service (DoS) attacks. Design principles followed by VirtuWind will guarantee that secure communication for all interfaces (north-/south-/east/west-/bound) is possible. The ...
... for north-/southbound and inter-controller interfaces, securing the controller can prevent adversaries from applying Denial of Service (DoS) attacks. Design principles followed by VirtuWind will guarantee that secure communication for all interfaces (north-/south-/east/west-/bound) is possible. The ...
Database Security - University of Scranton: Computing Sciences Dept.
... by means of a cipher or a code so that it becomes unreadable to all other people except those who hold a key to the information. Various Types of encryption offered by SQL : ...
... by means of a cipher or a code so that it becomes unreadable to all other people except those who hold a key to the information. Various Types of encryption offered by SQL : ...
Computer Hacking
... that someone gained access to the computer, intending to hack it without permission. ...
... that someone gained access to the computer, intending to hack it without permission. ...
D efe ns iv
... of advanced techniques used by the most sophisticated attackers to maintain stealth and security while minimizing their footprint and identity. Locating the Cyber Ninja ...
... of advanced techniques used by the most sophisticated attackers to maintain stealth and security while minimizing their footprint and identity. Locating the Cyber Ninja ...
STUXNET - Clemson
... Michael Chertoff has called on countries to develop doctrines to deal with cyber warfare in the same way cold war doctrines were developed for nuclear conflict. He told delegates at the conference that over 100 countries are now actively involved in cyber espionage and cyber attacks and that clear r ...
... Michael Chertoff has called on countries to develop doctrines to deal with cyber warfare in the same way cold war doctrines were developed for nuclear conflict. He told delegates at the conference that over 100 countries are now actively involved in cyber espionage and cyber attacks and that clear r ...
Workstar iGuard
... 3. Contactless SmartCard: With this feature, your workforce can gain access to the iGuard faster and smarter, by using the Philips Mifare Contactless Smart Card. Each user would have his / her own smart card, which stores the user information including the name, company & branch code, and the finger ...
... 3. Contactless SmartCard: With this feature, your workforce can gain access to the iGuard faster and smarter, by using the Philips Mifare Contactless Smart Card. Each user would have his / her own smart card, which stores the user information including the name, company & branch code, and the finger ...
PASS4TEST
... A. Publish the desired policies to all employees directing them to implement according to policy. B. Configure each computer to adhere to the standard policies. C. When installing new workstations or servers, image a machine that has proper security settings install the new machine with that image. ...
... A. Publish the desired policies to all employees directing them to implement according to policy. B. Configure each computer to adhere to the standard policies. C. When installing new workstations or servers, image a machine that has proper security settings install the new machine with that image. ...
Beyond Data Breach Cyber Trends and Exposures â Mr. Jason Kelly
... commercial, institutional, and individual customers through one of the most extensive worldwide property-casualty networks of any insurer. In addition, AIG companies are leading providers of life insurance and retirement services in the United States. AIG common stock is listed on the New York Stock ...
... commercial, institutional, and individual customers through one of the most extensive worldwide property-casualty networks of any insurer. In addition, AIG companies are leading providers of life insurance and retirement services in the United States. AIG common stock is listed on the New York Stock ...
Network and Systems Security
... Firstly to work with all relevant University constituents to implement proactive measures aimed at reducing the risk and or impact of a computer or network security incident Secondly to manage, direct and assist University constituencies in responding to such incidents ...
... Firstly to work with all relevant University constituents to implement proactive measures aimed at reducing the risk and or impact of a computer or network security incident Secondly to manage, direct and assist University constituencies in responding to such incidents ...
Click here to access the presentation.
... − Modular application framework can be utilized to develop entire new applications. − 3rd party developers have added/extended applications ...
... − Modular application framework can be utilized to develop entire new applications. − 3rd party developers have added/extended applications ...
Day 2
... • Ethernet requires multiple computers to share access to a single medium • A sender transmits a signal which propagates over the whole LAN • Only one frame of information can be sent at a time – other computers have to wait to send • After one frame is transmitted, the shared cable becomes availabl ...
... • Ethernet requires multiple computers to share access to a single medium • A sender transmits a signal which propagates over the whole LAN • Only one frame of information can be sent at a time – other computers have to wait to send • After one frame is transmitted, the shared cable becomes availabl ...
Ch10aProtectionMechanisms
... • The security manager must be able to see the organization’s systems and networks from the viewpoint of potential attackers • Drawbacks: – Tools do not have human-level capabilities – Most tools function by pattern recognition, so they only handle known issues – Some governments, agencies, institut ...
... • The security manager must be able to see the organization’s systems and networks from the viewpoint of potential attackers • Drawbacks: – Tools do not have human-level capabilities – Most tools function by pattern recognition, so they only handle known issues – Some governments, agencies, institut ...
Next Generation Security Operation Center for NCHC
... – Simulating vulnerable systems for network threats – Collecting malware samples and suspicious exploit traffic for further research – Analyzing Malware behavior for potential threats ...
... – Simulating vulnerable systems for network threats – Collecting malware samples and suspicious exploit traffic for further research – Analyzing Malware behavior for potential threats ...
Computer Crimes - Crime Prevention HQ
... ● Increase in the number of variants of keyloggers, decrease of password stealing malicious code URLs. ● New level of sophistication. ● Vishing (Phone phishing/spoofing) ...
... ● Increase in the number of variants of keyloggers, decrease of password stealing malicious code URLs. ● New level of sophistication. ● Vishing (Phone phishing/spoofing) ...
Mullvad Som Husdjur
... Mullvad Som Husdjur - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while bene ...
... Mullvad Som Husdjur - A virtual private network (VPN) extends a private network across a public network, such as the Internet. It enables a computer or network-enabled device to send and receive data across shared or public networks as if it were directly connected to the private network, while bene ...
Phoenix SIEM (Security Information and Event
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
... Director and CTO at Kenindus Limited . Holds a Bachelor of Science degree in Computer Information Management from Life University in Atlanta, Georgia and a Masters in Small Business and Entrepreneurship from Plymouth State in Plymouth, New Hampshire. I have more than 10 years experience in cyber sec ...
Lecture 1 - WordPress.com
... • Public-key cryptography and message authentication Network security applications • Key distribution and user authentication • Transport-level security • Wireless network security • Electronic mail security • IP security System security • Intruders • Malicious software • Firewalls ...
... • Public-key cryptography and message authentication Network security applications • Key distribution and user authentication • Transport-level security • Wireless network security • Electronic mail security • IP security System security • Intruders • Malicious software • Firewalls ...
SECURITY
... Stop unauthorized users from reading sensitive information. Integrity !!! Every piece of data should be as the last authorized modifier left it. Availability!! The property of being accessible and useable upon demand by an authorized entity. Access Control = Confidentiality + Integrity + Availabilit ...
... Stop unauthorized users from reading sensitive information. Integrity !!! Every piece of data should be as the last authorized modifier left it. Availability!! The property of being accessible and useable upon demand by an authorized entity. Access Control = Confidentiality + Integrity + Availabilit ...
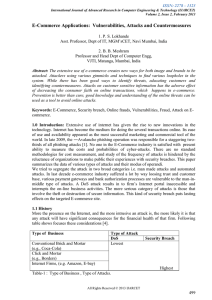
Survey of online attacks on E-Commerce sites
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
... Web based attacks are considered to be the greatest threat to the online business as it is related to confidentiality, availability, and integrity. The motive behind e-commerce attack is significantly different then other attacks; Web based attacks focus on an application itself and functions on lay ...
Emerging Threats to Business Security
... Spyware remains a growing concern for businesses. In light of recently introduced data protection legislation in Europe and the United States, the danger to businesses in terms of liability for data theft/loss will remain high for the foreseeable future. The various versions of "Storm Worm" still pr ...
... Spyware remains a growing concern for businesses. In light of recently introduced data protection legislation in Europe and the United States, the danger to businesses in terms of liability for data theft/loss will remain high for the foreseeable future. The various versions of "Storm Worm" still pr ...
ISEC0511
... application can also be considered as part of the accounting information. These files need security so that adversaries cannot tamper or delete them. ...
... application can also be considered as part of the accounting information. These files need security so that adversaries cannot tamper or delete them. ...
Course Learning Objectives:
... 5. Develop SSL or Firewall based solutions against security threats, employ access control techniques to the existing computer platforms such as Unix and Windows NT. (ABET Outcomes: a, c, e, i, k) 6. Write an extensive analysis report on any existing security product or code, investigate the strong ...
... 5. Develop SSL or Firewall based solutions against security threats, employ access control techniques to the existing computer platforms such as Unix and Windows NT. (ABET Outcomes: a, c, e, i, k) 6. Write an extensive analysis report on any existing security product or code, investigate the strong ...