LVRJ Case study
... Challenges: Limited visibility into user activity and controlling access to resources through ACLs and static IP addresses has gotten too complex to manage. Solution: Deploying the ConSentry Networks™ CS2400 Secure LAN Controller™ and InSight Manager™ to provide complete visibility into user activit ...
... Challenges: Limited visibility into user activity and controlling access to resources through ACLs and static IP addresses has gotten too complex to manage. Solution: Deploying the ConSentry Networks™ CS2400 Secure LAN Controller™ and InSight Manager™ to provide complete visibility into user activit ...
Hackers and the Internet Seid Alimostafa Sanglakhi
... in a dark room in some corner and eating pizza the whole day. [2] A hacker is also not somebody who is good at acts and breaking wood and creating very good furniture. Surprisingly, a hacker is also not always a computer wizard and also not somebody who can break and crack passwords to all websites ...
... in a dark room in some corner and eating pizza the whole day. [2] A hacker is also not somebody who is good at acts and breaking wood and creating very good furniture. Surprisingly, a hacker is also not always a computer wizard and also not somebody who can break and crack passwords to all websites ...
Protecting against spear-phishing
... solutions; it doesn’t depend on definition updates. Crucially, this means that mutating viruses and executable threats that would normally bypass your anti-virus protection and attack your networks, are now stopped in the second line of defence. Another critical, and final, defence layer is a method ...
... solutions; it doesn’t depend on definition updates. Crucially, this means that mutating viruses and executable threats that would normally bypass your anti-virus protection and attack your networks, are now stopped in the second line of defence. Another critical, and final, defence layer is a method ...
HIPAA Security Standards
... There are several types of firewall techniques: • Packet filter: Looks at each packet entering or leaving the network and accepts or rejects it based on user-defined rules. Packet filtering is fairly effective and transparent to users, but it is difficult to configure. In addition, it is susceptible ...
... There are several types of firewall techniques: • Packet filter: Looks at each packet entering or leaving the network and accepts or rejects it based on user-defined rules. Packet filtering is fairly effective and transparent to users, but it is difficult to configure. In addition, it is susceptible ...
PCI Compliance - Aug 2009 - Commonwealth Business Travel
... All fraud losses incurred from the use of the compromised account numbers from the date of compromise forward. Cost of re-issuing cards associated with the compromise. Cost of any additional fraud prevention/detection activities required by the card associations (i.e. a forensic audit) or costs incu ...
... All fraud losses incurred from the use of the compromised account numbers from the date of compromise forward. Cost of re-issuing cards associated with the compromise. Cost of any additional fraud prevention/detection activities required by the card associations (i.e. a forensic audit) or costs incu ...
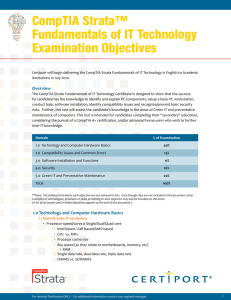
CompTIA Strata™ Fundamentals of IT Technology
... conduct basic software installation, identify compatibility issues and recognize/prevent basic security risks. Further, this test will assess the candidate’s knowledge in the areas of Green IT and preventative maintenance of computers. This test is intended for candidates completing their “secondary ...
... conduct basic software installation, identify compatibility issues and recognize/prevent basic security risks. Further, this test will assess the candidate’s knowledge in the areas of Green IT and preventative maintenance of computers. This test is intended for candidates completing their “secondary ...
ITC_2013_13-02
... System networking involves the connection of computers and computer networks such that users in distant locations may share information. Protocols were established to connect different systems with predictable results. As systems networking evolved and applications became more complex, developing ne ...
... System networking involves the connection of computers and computer networks such that users in distant locations may share information. Protocols were established to connect different systems with predictable results. As systems networking evolved and applications became more complex, developing ne ...
New Law Requires Businesses in California to Report Electronic Break-Ins
... legislation occurred in April 2002, when California’s Steven P. Teale data center in Rancho Cordova suffered a security breach of the state’s payroll application system, resulting in the compromise of confidential information, including names, social security numbers, and payroll information, of ove ...
... legislation occurred in April 2002, when California’s Steven P. Teale data center in Rancho Cordova suffered a security breach of the state’s payroll application system, resulting in the compromise of confidential information, including names, social security numbers, and payroll information, of ove ...
Network Security Network Attacks and Mitigation
... The threat of IP spoofing can be reduced, but not eliminated, using these measures: • Access control configuration • Encryption • RFC 3704 filtering • Additional authentication requirement that does not use IP address-based authentication; examples are: ...
... The threat of IP spoofing can be reduced, but not eliminated, using these measures: • Access control configuration • Encryption • RFC 3704 filtering • Additional authentication requirement that does not use IP address-based authentication; examples are: ...
Chp. 8 - Cisco Networking Academy
... of network monitoring. Syslog is an Application Layer protocol used for logging system events. Syslog enables devices to send information to a syslog daemon that is installed and running on a management station. A syslog system is composed of syslog servers and syslog clients Syslog servers ...
... of network monitoring. Syslog is an Application Layer protocol used for logging system events. Syslog enables devices to send information to a syslog daemon that is installed and running on a management station. A syslog system is composed of syslog servers and syslog clients Syslog servers ...
Lecture 12
... Company wants to keep its IP addresses secret, but wants a consultant to analyze logs for an address scanning attack ...
... Company wants to keep its IP addresses secret, but wants a consultant to analyze logs for an address scanning attack ...
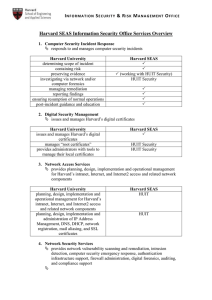
Harvard SEAS Information Security Office Services Overview
... (working with HUIT Security) HUIT Security ...
... (working with HUIT Security) HUIT Security ...
Operating System Security Fundamentals
... RADIUS: used by network devices to provide a centralized authentication mechanism Secure Socket Layer (SSL): authentication information is transmitted over the network in an encrypted form Secure Remote Password (SRP): Password is not stored locally Invulnerable to brute force or dictionary attacks ...
... RADIUS: used by network devices to provide a centralized authentication mechanism Secure Socket Layer (SSL): authentication information is transmitted over the network in an encrypted form Secure Remote Password (SRP): Password is not stored locally Invulnerable to brute force or dictionary attacks ...
Distributed and Embedded Systems (DIES)
... (9) The Caller-ID feature of the Phone system used to inform the recipient of a telephone call who is calling; (10) An Audit log used to collect relevant operational data that can be analyzed when there is an incident; (11) An ISP used to assist its clients in using the information super highway res ...
... (9) The Caller-ID feature of the Phone system used to inform the recipient of a telephone call who is calling; (10) An Audit log used to collect relevant operational data that can be analyzed when there is an incident; (11) An ISP used to assist its clients in using the information super highway res ...
Access Security Requirements
... 2.4 Implement and follow current best security practices for computer anti-Spyware scanning services and procedures: Use, implement and maintain a current, commercially available computer anti-Spyware scanning product on all computers, systems and networks. If you suspect actual or potential Spy ...
... 2.4 Implement and follow current best security practices for computer anti-Spyware scanning services and procedures: Use, implement and maintain a current, commercially available computer anti-Spyware scanning product on all computers, systems and networks. If you suspect actual or potential Spy ...
VPN in the spotlight of IT- Security
... With the help of VPN a smaller net is build up in a bigger net (e.g. the internet). Only the persons who know the right addresses and code words are able to communicate through this secure channel. Using IPsec is one possibility to establish a VPN. Furthermore there are some others, but IPsec is wi ...
... With the help of VPN a smaller net is build up in a bigger net (e.g. the internet). Only the persons who know the right addresses and code words are able to communicate through this secure channel. Using IPsec is one possibility to establish a VPN. Furthermore there are some others, but IPsec is wi ...
SANDS CORP CYBER JOB
... cyber security program. This role is an entry level analyst that is responsible for monitoring various cyber security appliances to identify events that require escalated analysis. The SOC cyber security analyst, Level 1 reports to the Director of the US Security Operations Center. ...
... cyber security program. This role is an entry level analyst that is responsible for monitoring various cyber security appliances to identify events that require escalated analysis. The SOC cyber security analyst, Level 1 reports to the Director of the US Security Operations Center. ...
Bandura® Releases REACT™ Software to Integrate Internal
... “REACT brings security systems to the next level,” said Dave Maestas, chief technology officer and co‐ founder at Bandura. “There are so many security events coming from so many locations in an enterprise network that security engineers can’t analyze and take action fast enough to prevent network ...
... “REACT brings security systems to the next level,” said Dave Maestas, chief technology officer and co‐ founder at Bandura. “There are so many security events coming from so many locations in an enterprise network that security engineers can’t analyze and take action fast enough to prevent network ...
TrendMicro Titanium - A New Concept in Security by Ira Wilsker
... online activity. The System Tuner can clean junk files freeing up hard drive space, manage what loads at boot in order to improve startup performance, clean history files, schedule tune-ups. The System Tuner also includes a comprehensive registry cleaner, and a feature that protects internet privacy ...
... online activity. The System Tuner can clean junk files freeing up hard drive space, manage what loads at boot in order to improve startup performance, clean history files, schedule tune-ups. The System Tuner also includes a comprehensive registry cleaner, and a feature that protects internet privacy ...
The Top Six Risks of Employee Internet Use and How
... can be inadvertently downloaded onto an employee’s computer simply by clicking a link on a web site. Or, when browser security is not configured securely enough, some Malware can be automatically installed without the user’s awareness. Viruses and Worms are particularly insidious because both are ty ...
... can be inadvertently downloaded onto an employee’s computer simply by clicking a link on a web site. Or, when browser security is not configured securely enough, some Malware can be automatically installed without the user’s awareness. Viruses and Worms are particularly insidious because both are ty ...
download
... 5. Non Repudiation • origin, destination • protection against denial by one of the parties in a communication ...
... 5. Non Repudiation • origin, destination • protection against denial by one of the parties in a communication ...
Information Privacy What is information privacy?
... service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against software theft and information theft ...
... service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against software theft and information theft ...