E-Surveillance and User Privacy
... persons reasonable expectation of privacy. • In 1968 Congress codified the requirements to obtain court authority for interception of oral and wire communication • In 1986 this Act was amended to include ...
... persons reasonable expectation of privacy. • In 1968 Congress codified the requirements to obtain court authority for interception of oral and wire communication • In 1986 this Act was amended to include ...
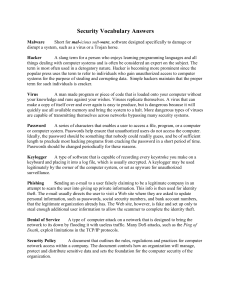
ITS_8_Security Vocab Answers
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...