Seminar Announcement - CS/NVC Home
... queries are useful in many application domains, including Network Management and Intrusion Detection, Web Monitoring, Sensor Network applications, and various financial and business applications. In this talk, we will first briefly discuss some of these applications and general technical challenges ...
... queries are useful in many application domains, including Network Management and Intrusion Detection, Web Monitoring, Sensor Network applications, and various financial and business applications. In this talk, we will first briefly discuss some of these applications and general technical challenges ...
file - ScholarSphere
... half of the respondents believe they have already been attacked by intruders, most likely initiated by a hostile foreign government. [1] This heightened sense of security is not merely paranoia. In a February meeting of the Senate Intelligence Committee, Dennis Blair, Director of National Intelligen ...
... half of the respondents believe they have already been attacked by intruders, most likely initiated by a hostile foreign government. [1] This heightened sense of security is not merely paranoia. In a February meeting of the Senate Intelligence Committee, Dennis Blair, Director of National Intelligen ...
common network terms - Amazon Web Services
... A server connected to a network that resolves network names into network addresses. Domain Name System (DNS) is a database system that translates a computer's fully qualified domain name into an IP address. Dual Powered In essence, this is a power supply that actually includes two (or more) units wi ...
... A server connected to a network that resolves network names into network addresses. Domain Name System (DNS) is a database system that translates a computer's fully qualified domain name into an IP address. Dual Powered In essence, this is a power supply that actually includes two (or more) units wi ...
Web tracking resolution
... Web tracking allows organisations to monitor almost every single aspect of user behaviour on the Web. The type of information that can be collected through tracking (e.g., IP addresses, device identi?iers, etc.) can lead to the identi?ication of a particular ...
... Web tracking allows organisations to monitor almost every single aspect of user behaviour on the Web. The type of information that can be collected through tracking (e.g., IP addresses, device identi?iers, etc.) can lead to the identi?ication of a particular ...
A Common Language for Computer Security Incidents
... Flexible enough to allow site-specific low-level terms Develop taxonomy for these terms ...
... Flexible enough to allow site-specific low-level terms Develop taxonomy for these terms ...
Jaden Terry CIS 280 Final Network Security From browsing the
... viruses etc. According to Wikipedia, a hacker is defined as, “Someone who seeks and exploits weaknesses in a computer system or computer network.” Some evil hackers may insert a virus or malware that could make a computer unusable. From hackers and viruses, to network privacy, the security of our ne ...
... viruses etc. According to Wikipedia, a hacker is defined as, “Someone who seeks and exploits weaknesses in a computer system or computer network.” Some evil hackers may insert a virus or malware that could make a computer unusable. From hackers and viruses, to network privacy, the security of our ne ...
What is a Network
... has traditionally been handled by either private networking resources or public telephone networks.. ...
... has traditionally been handled by either private networking resources or public telephone networks.. ...
Medical_Informatics_-_Computer_Networks
... Domain names are used to establish a unique identity. Organizations can choose the domain name that corresponds to their name, hoping the Internet users to reach them more quickly and easily. ...
... Domain names are used to establish a unique identity. Organizations can choose the domain name that corresponds to their name, hoping the Internet users to reach them more quickly and easily. ...
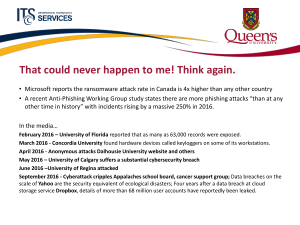
Cybersecurity - Queen`s Wiki
... Promote a security aware culture through awareness campaigns, and community engagement, and process integration. Integrate security throughout Queen’s ...
... Promote a security aware culture through awareness campaigns, and community engagement, and process integration. Integrate security throughout Queen’s ...
Chapter 8 - Chabot College
... • A software report would be used to determine what programs are installed on a particular computer. • Network policy should be used to select network passwords. • User policies refer to documentation that outlines what is and what is not permissible on the network. • Configuration error is NOT used ...
... • A software report would be used to determine what programs are installed on a particular computer. • Network policy should be used to select network passwords. • User policies refer to documentation that outlines what is and what is not permissible on the network. • Configuration error is NOT used ...
Document
... Creating an exception process (both opt-in and opt-out) with appropriate vetting, risk assessment, and functional and technical management approval. Access to systems from off-site locations, especially during emergencies. ...
... Creating an exception process (both opt-in and opt-out) with appropriate vetting, risk assessment, and functional and technical management approval. Access to systems from off-site locations, especially during emergencies. ...
Information Systems and Networks
... Systems malfunction if computer hardware breaks down, is not configured properly, or is damaged by improper use or criminal acts. Errors in programming, improper installation, or unauthorized changes cause computer software to fail. Power failures, floods, fires, or other natural disasters can also ...
... Systems malfunction if computer hardware breaks down, is not configured properly, or is damaged by improper use or criminal acts. Errors in programming, improper installation, or unauthorized changes cause computer software to fail. Power failures, floods, fires, or other natural disasters can also ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
CS 494/594 Computer and Network Security - UTK-EECS
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
... data files, wiretapping to obtain data in a network Interruption: information or resources become lost, unavailable, or unusable, e.g., malicious destruction of a hardware device, erasure of a program or data file ...
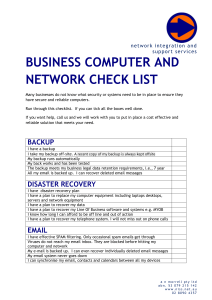
business computer and network check list
... Guest Wifi users can access the internet only and have no access my equipment I have internet website filtering – no computer can access unwanted websites When working remotely my computers remain secure from the internet When staff leave my business I can prevent them from accessing all systems I h ...
... Guest Wifi users can access the internet only and have no access my equipment I have internet website filtering – no computer can access unwanted websites When working remotely my computers remain secure from the internet When staff leave my business I can prevent them from accessing all systems I h ...
Computer Systems Security
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...
Assignment #2 S.Popovic
... At the time of his arrest, Kevin was the most-wanted computer criminal in the USA. Was arrested by the FBI on February 15, 1995. ...
... At the time of his arrest, Kevin was the most-wanted computer criminal in the USA. Was arrested by the FBI on February 15, 1995. ...
TS/SCI cleared Network Administrator for AF JWICS
... - Categorize and resolve network issues by validating, isolating, and correcting faults and verifying service restoral with customers. - Perform installation, troubleshooting, maintenance, and repair of network switches and routers, power, and computer data circuits and related apparatus/peripherals ...
... - Categorize and resolve network issues by validating, isolating, and correcting faults and verifying service restoral with customers. - Perform installation, troubleshooting, maintenance, and repair of network switches and routers, power, and computer data circuits and related apparatus/peripherals ...
Slide 1
... “ Electronic attack through computer network towards critical infrastructure that has big potential to disturb social and economic activity of a nation.” Misused of cyberspace by Terrorist Group for specific goal. ...
... “ Electronic attack through computer network towards critical infrastructure that has big potential to disturb social and economic activity of a nation.” Misused of cyberspace by Terrorist Group for specific goal. ...
COEN 252 Computer Forensics
... Robust implementation of TCP/IP. SSH for remote access. Simple to disable services. Simple to run local firewall. ...
... Robust implementation of TCP/IP. SSH for remote access. Simple to disable services. Simple to run local firewall. ...
Chapter 2: Attackers and Their Attacks
... Know that breaking in to a system is illegal but do not intend on committing a crime ...
... Know that breaking in to a system is illegal but do not intend on committing a crime ...
Security - UTRGV Faculty Web
... When a digital signature is encrypted using a private key – it can be read by anyone with a public key. But the message was sent by only one who has the private key. Digital certificates are used to authenticate the source of a file. ...
... When a digital signature is encrypted using a private key – it can be read by anyone with a public key. But the message was sent by only one who has the private key. Digital certificates are used to authenticate the source of a file. ...