TNS03%20Introduction%20to%20Network%20Security
... Appears to be benign (良好) software but secretly downloading a virus or other malware. For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
... Appears to be benign (良好) software but secretly downloading a virus or other malware. For a Trojan horse to spread, you must invite these programs onto your computers. For example, by opening an email attachment or downloading and running a file from the Internet. ...
Breach Detection in Healthcare
... Today’s penalties for data breaches increase, notification requirements are more stringent, and enforcement agencies have new incentives for taking action against organizations that fail to protect healthcare privacy. Next to that, the requirement to publicly notify customers about the data breach m ...
... Today’s penalties for data breaches increase, notification requirements are more stringent, and enforcement agencies have new incentives for taking action against organizations that fail to protect healthcare privacy. Next to that, the requirement to publicly notify customers about the data breach m ...
A threat can be any person, object, or event that, if realized, could
... desired destination. This is much cheaper and easier to maintain than providing a direct physical path from every machine to every machine. ...
... desired destination. This is much cheaper and easier to maintain than providing a direct physical path from every machine to every machine. ...
1. CyberCIEGE Identity Database
... of these networks and the virtual users to protect valuable assets from attack by both vandals and well-motivated professionals. The Identity Database scenario requires players to protect an identity database that is used in the generation of smart card IDs. The scenario does not address smart cards ...
... of these networks and the virtual users to protect valuable assets from attack by both vandals and well-motivated professionals. The Identity Database scenario requires players to protect an identity database that is used in the generation of smart card IDs. The scenario does not address smart cards ...
Chapter 4
... An attacker can pretend to be an access point and send a forged disassociation frame to a wireless device. This will cause the device to disassociate from the access point. Sending repeated disassociation frames an attacker can continuously prevent any device from communicating with the AP. 17. Expl ...
... An attacker can pretend to be an access point and send a forged disassociation frame to a wireless device. This will cause the device to disassociate from the access point. Sending repeated disassociation frames an attacker can continuously prevent any device from communicating with the AP. 17. Expl ...
Some Tools for Computer Security Incident Response
... Snort is a free and open source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS). Snort’s has the ability to perform real-time traffic analysis and packet logging on Internet Protocol (IP) networks. Snort performs protocol analysis, content searching, and cont ...
... Snort is a free and open source network intrusion prevention system (NIPS) and network intrusion detection system (NIDS). Snort’s has the ability to perform real-time traffic analysis and packet logging on Internet Protocol (IP) networks. Snort performs protocol analysis, content searching, and cont ...
Campus Network Usage Policy
... (5) Each unit of the University should participate in information security training courses provided by the Computer Center on a regular basis based on the different types of requirements of their work--such as management, business and information--so that all personnel will develop awareness of inf ...
... (5) Each unit of the University should participate in information security training courses provided by the Computer Center on a regular basis based on the different types of requirements of their work--such as management, business and information--so that all personnel will develop awareness of inf ...
ABET - Regis University: Academic Web Server for Faculty
... ▫ Assigning unique name to network’s SSID and not broadcasting SSID ▫ Using it with VPN technology • Wi-Fi Alliance finalized WAP2 specification, replacing WEP with stronger standards ▫ Continually changing keys ▫ Encrypted authentication system with central server ...
... ▫ Assigning unique name to network’s SSID and not broadcasting SSID ▫ Using it with VPN technology • Wi-Fi Alliance finalized WAP2 specification, replacing WEP with stronger standards ▫ Continually changing keys ▫ Encrypted authentication system with central server ...
Monitoring and Auditing AIS - McGraw
... • Wide area networks (WANs) link different sites together, transmit information across geographically and cover a broad geographic area. --to provide remote access to employees or customers --to link two or more sites within the firm --to provide corporate access to the Internet routers and firewall ...
... • Wide area networks (WANs) link different sites together, transmit information across geographically and cover a broad geographic area. --to provide remote access to employees or customers --to link two or more sites within the firm --to provide corporate access to the Internet routers and firewall ...
Cisco 642-552
... Internet outlaw's botnet in just a few minutes. A firewall can block malware that could otherwise scan your computer for vulnerabilities and then try to break in at a weak point. The real issue is how to make one 99.9% secure when it is connected to in Internet. At a minimum computers need to have f ...
... Internet outlaw's botnet in just a few minutes. A firewall can block malware that could otherwise scan your computer for vulnerabilities and then try to break in at a weak point. The real issue is how to make one 99.9% secure when it is connected to in Internet. At a minimum computers need to have f ...
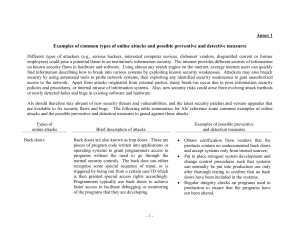
Annex 1
... network connections through these modems can be initiated only from the modems to preapproved remote parties but not the other way round; Use scanning tools or perform penetration testing to identify vulnerability to war dialling risk. Implement adequate network security to prevent unauthorized inte ...
... network connections through these modems can be initiated only from the modems to preapproved remote parties but not the other way round; Use scanning tools or perform penetration testing to identify vulnerability to war dialling risk. Implement adequate network security to prevent unauthorized inte ...
RedSocks Malicious Threat Detection
... false sense of security. They believe they have secured their key services against these threats simply by deploying AV devices or firewalls in front of their infrastructure. However, current generation malware has become sophisticated and widespread enough to bypass many, if not all, of these secur ...
... false sense of security. They believe they have secured their key services against these threats simply by deploying AV devices or firewalls in front of their infrastructure. However, current generation malware has become sophisticated and widespread enough to bypass many, if not all, of these secur ...
Lecture 10 - The University of Texas at Dallas
... A person could have multiple identities - A physician could have an identity to access medical resources and another to access his bank accounts Digital identity management is about managing the multiple ...
... A person could have multiple identities - A physician could have an identity to access medical resources and another to access his bank accounts Digital identity management is about managing the multiple ...
ch 5 - sm.luth.se
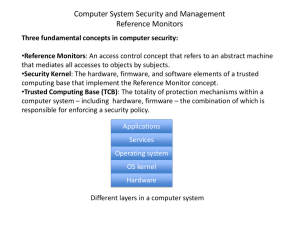
... Three fundamental concepts in computer security: •Reference Monitors: An access control concept that refers to an abstract machine that mediates all accesses to objects by subjects. •Security Kernel: The hardware, firmware, and software elements of a trusted computing base that implement the Referen ...
... Three fundamental concepts in computer security: •Reference Monitors: An access control concept that refers to an abstract machine that mediates all accesses to objects by subjects. •Security Kernel: The hardware, firmware, and software elements of a trusted computing base that implement the Referen ...
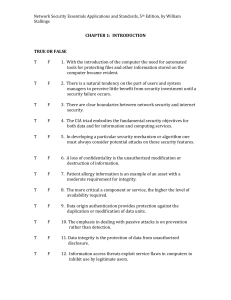
CH01-Testbank-NetSec5e
... 2. Three key objectives that are at the heart of computer security are: confidentiality, availability, and _________ . 3. An intelligent act that is a deliberate attempt to evade security services and violate the security policy of a system is an __________ . 4. A loss of _________ is the disrup ...
... 2. Three key objectives that are at the heart of computer security are: confidentiality, availability, and _________ . 3. An intelligent act that is a deliberate attempt to evade security services and violate the security policy of a system is an __________ . 4. A loss of _________ is the disrup ...
OnLinePrivacy - Cal State LA
... Designed to replicate themselves and potentially cause harmful actions. Often hidden inside innocuous programs. Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves b ...
... Designed to replicate themselves and potentially cause harmful actions. Often hidden inside innocuous programs. Viruses in e-mails often masquerade as games or pictures and use beguiling subject lines (e.g., "My girlfriend nude") to encourage users to open and run them. Try to replicate themselves b ...
2001-10-11-AIC-SecurityForEducation
... considered completely untrustworthy, and the hosts must be hardened. In an ideal situation, *no* hosts will be on this network at all. • DMZ (De-Militarized Zone) – RFC1918 reserved IP addresses that are protected by a firewall and mapped to outside IP addresses. This network is also to be considere ...
... considered completely untrustworthy, and the hosts must be hardened. In an ideal situation, *no* hosts will be on this network at all. • DMZ (De-Militarized Zone) – RFC1918 reserved IP addresses that are protected by a firewall and mapped to outside IP addresses. This network is also to be considere ...
Cybersecurity and Information Assurance PPT
... To guard against sniffing, make sure attacker cannot access a legitimate communication stream ...
... To guard against sniffing, make sure attacker cannot access a legitimate communication stream ...
Report: Intrusion Detection Systems
... Most Simplest Architecture, unable to detect attack made by distributed normal events. ...
... Most Simplest Architecture, unable to detect attack made by distributed normal events. ...
Data Mining BS/MS Project
... Host-Based Results • The “PAD Detector” in the previous graph used probabilistic anomaly detection on the system calls logged by the interceptor • When attempting to identify “malicious” processes (programs that make file accesses they aren’t expected to), PAD achieved 95% accuracy – With only a 2% ...
... Host-Based Results • The “PAD Detector” in the previous graph used probabilistic anomaly detection on the system calls logged by the interceptor • When attempting to identify “malicious” processes (programs that make file accesses they aren’t expected to), PAD achieved 95% accuracy – With only a 2% ...
Networks - ZSIS-ITGS
... details as well as how it is being protected. A good example would be banking. There are probably no banks in existence that keep their customer’s data on paper anymore. This used to happen in the past but it has all since then been transferred to an electronic storage device. Such devices are all p ...
... details as well as how it is being protected. A good example would be banking. There are probably no banks in existence that keep their customer’s data on paper anymore. This used to happen in the past but it has all since then been transferred to an electronic storage device. Such devices are all p ...
here - Online Journal of Space Communication
... Satellite Solution Advantages • Satellites provide instantaneous dissemination of information and a common operating picture – Gets it to the user faster and at low cost. • Satellite systems not susceptible to terrestrial boundaries and costs. Easily becomes part of hybrid solution. ...
... Satellite Solution Advantages • Satellites provide instantaneous dissemination of information and a common operating picture – Gets it to the user faster and at low cost. • Satellite systems not susceptible to terrestrial boundaries and costs. Easily becomes part of hybrid solution. ...