* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download ch 5 - sm.luth.se
Cyber-security regulation wikipedia , lookup
Address space layout randomization wikipedia , lookup
Trusted Computing wikipedia , lookup
Computer and network surveillance wikipedia , lookup
Unix security wikipedia , lookup
Mobile security wikipedia , lookup
Next-Generation Secure Computing Base wikipedia , lookup
Computer security wikipedia , lookup
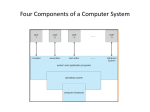
Computer System Security and Management Reference Monitors Three fundamental concepts in computer security: •Reference Monitors: An access control concept that refers to an abstract machine that mediates all accesses to objects by subjects. •Security Kernel: The hardware, firmware, and software elements of a trusted computing base that implement the Reference Monitor concept. •Trusted Computing Base (TCB): The totality of protection mechanisms within a computer system – including hardware, firmware – the combination of which is responsible for enforcing a security policy. Applications Services Operating system OS kernel Hardware Different layers in a computer system Computer System Security and Management Reference Monitors Placing the Reference Monitor The reference monitor can be placed: • In hardware: Access control to mechanisms in microprocessors. • In the operating system: Access control in Linux. • In the services layer: Access control in databases. • In the application: In the application code. Operating system integrity The goal of an attacker is to disable the security control by modifying the operating system. When securing an operating system two requirements have to be addressed: • Users should be able to use the operating system. • Users should not be able to misuse the operating system. In Linux there is 2 modes: • user mode: protected mode. • supervisor mode: root mode. To execute a command in supervisor mode sudo can be used in Linux. Computer System Security and Management Reference Monitors Hardware security features Hardware is the lowest layer in an IT architecture: Applications Services Operating system OS kernel Hardware Protection in the Security Kernel • It may be possible to evaluate security to a higher level of assurance • Putting security mechanisms into the core of the system increase the performance. No overheads caused by security checks. • Access control decisions are removed from applications. Computer System Security and Management Reference Monitors A brief overview of Computer Architecture Input devices: Keyboards Output devices: Monitor I/O CPU Bus CPU components: Registers: • General purpose registers. • Dedicated register. Program counter: Points to memory location that contains the next instruction to be executed. Stack pointe: Points to the top of the system stack. Status register: Allows the CPU to keep essential state information. Arithmetic Logic Unit (ALU): Executes instructions given in a machine level language or sets bits in the status register. To switch between different programs, the CPU perform a context switch and saves the state of the current process. Memory RAM (Random Access Memory): stores data temporarily. ROM (Read Only Memory): Store data permanently. EPROM (Erasable & Programmable Read Only Memory): The data can be erased or kept permanently. WROM (Write Once memory): Freeze the data once for all. Keep the OS or cryptographic keys on ROM or EPROM. RAM: volatile memory. ROM, EPROM, WROM: non-volatile memory. Computer System Security and Management Reference Monitors Processes and Threads A process is a program in execution. A process is an important unit of control for the OS and for the security. A process consists of: • Executable code. • Data. • The execution context. Processes communicate with each other through primitives provided by the OS, IPC. Less secure because of the context switch between processes. Expensive operation in the OS Treads are execute within a process. Share the process address space. More secure. Less expensive operation in the OS. Computer System Security and Management Reference Monitors Interrupts (traps, exceptions) Interrupts are created by processes when: • There is error in the program. • User sends a request. • Hardware failure. A trap is a special input to the CPU which includes an ad Interrupt vector table contains addresses Memory TRAP #n n Interrupt table has to be protected. Viruses can change an entry in the table so that it points to attack code. Redirecting pointer is a very efficient attack method. Interrupt vector Interrupt handler 1 0 Process of an interrupt







![[Lecture 1, part 3] Kernel interaction with the hardware: Interrupt](http://s1.studyres.com/store/data/014183875_1-7af0f6b03bedcfbf8972c6054b446a98-150x150.png)