computer security - GH Raisoni Polytechnic, Nagpur
... A man in the middle attack occurs when attackers are able to place themselves in the middle of two other hosts that are communicating in order to view or modify the traffic. This is done by making sure that all communication going to or from the target host is routed through the attacker’s host. The ...
... A man in the middle attack occurs when attackers are able to place themselves in the middle of two other hosts that are communicating in order to view or modify the traffic. This is done by making sure that all communication going to or from the target host is routed through the attacker’s host. The ...
Chapter. 01
... the computer system's information secure. In broader terms, computer security can be thought of as the protection of the computer and its resources against accidental or intentional disclosure of confidential data, unlawful modification of data or programs, the destruction of data, software or hardw ...
... the computer system's information secure. In broader terms, computer security can be thought of as the protection of the computer and its resources against accidental or intentional disclosure of confidential data, unlawful modification of data or programs, the destruction of data, software or hardw ...
Slide 1
... Static routes can be setup so that “China” is routed to port 23b Control plane attacks (ARP, RIP, OSPF) to advertise “China” is over here ...
... Static routes can be setup so that “China” is routed to port 23b Control plane attacks (ARP, RIP, OSPF) to advertise “China” is over here ...
PPT - CS
... • Securing interfaces between different systems • Different security goals and needs • Attackers seek weakest link in the system • Security people must protect all links in the system ...
... • Securing interfaces between different systems • Different security goals and needs • Attackers seek weakest link in the system • Security people must protect all links in the system ...
18_DataCenter_Security_Overview
... •Shunning or blocking- The IDS can instruct a network device such as a router, switch, or firewall to dynamically apply an ACL to block the traffic coming from an attacker. ...
... •Shunning or blocking- The IDS can instruct a network device such as a router, switch, or firewall to dynamically apply an ACL to block the traffic coming from an attacker. ...
18_DataCenter_Security_Overview
... •Shunning or blocking- The IDS can instruct a network device such as a router, switch, or firewall to dynamically apply an ACL to block the traffic coming from an attacker. ...
... •Shunning or blocking- The IDS can instruct a network device such as a router, switch, or firewall to dynamically apply an ACL to block the traffic coming from an attacker. ...
Applied Cybersecurity
... Decision makers must be familiar with the basic principles and best practices of cybersecurity to best protect their enterprises. In this course, experts from academia, the military, and industry share their knowledge to give participants the principles, the state of the practice, and strategies for ...
... Decision makers must be familiar with the basic principles and best practices of cybersecurity to best protect their enterprises. In this course, experts from academia, the military, and industry share their knowledge to give participants the principles, the state of the practice, and strategies for ...
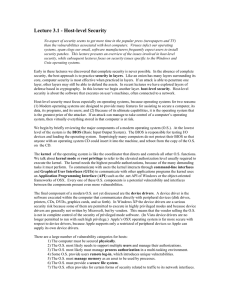
Lecture 3.1 - Host
... core, computer security is most effective when practiced in layers. If an attack is able to penetrate one layer, other layers may still be able to defend the assets. In recent lectures we have explored layers of defense based in cryptography. In this lecture we begin another layer. host-level securi ...
... core, computer security is most effective when practiced in layers. If an attack is able to penetrate one layer, other layers may still be able to defend the assets. In recent lectures we have explored layers of defense based in cryptography. In this lecture we begin another layer. host-level securi ...
Computer Security and Safety, Ethics, and Privacy
... E-mail spoofing occurs when the sender’s address or other components of the e-mail header are altered so that it appears the email originated from a different sender. IP spoofing occurs when an intruder computer fools a network into believing its IP address is associated with a trusted source. ...
... E-mail spoofing occurs when the sender’s address or other components of the e-mail header are altered so that it appears the email originated from a different sender. IP spoofing occurs when an intruder computer fools a network into believing its IP address is associated with a trusted source. ...
DPI as a means of access segregation in a corporate
... - Making brand-new set of network rules is painful. ...
... - Making brand-new set of network rules is painful. ...
Preparation Identification Containment
... connections from the compromised computer; - Select what kind of files can be lost / stolen and restrict the access for confidential files; - Create fake documents with watermarking that could be use as a proof of theft; - Notify targeted business users about what must be done and what is forbidden; ...
... connections from the compromised computer; - Select what kind of files can be lost / stolen and restrict the access for confidential files; - Create fake documents with watermarking that could be use as a proof of theft; - Notify targeted business users about what must be done and what is forbidden; ...
Remote Domain Security Awareness Training
... Attacked millions of Windows computers It started spreading email message with the subject line "ILOVEYOU" and the attachment "LOVE-LETTER-FOR-YOU.txt.vbs". Opening the attachment activated the visual basic script. Damage MP3 files, overwriting image files and automatically send itself to all c ...
... Attacked millions of Windows computers It started spreading email message with the subject line "ILOVEYOU" and the attachment "LOVE-LETTER-FOR-YOU.txt.vbs". Opening the attachment activated the visual basic script. Damage MP3 files, overwriting image files and automatically send itself to all c ...
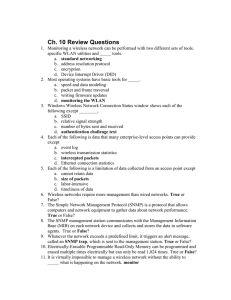
Ch10
... 12. _____ is an SNMP-based tool that is used to monitor LANs that are connected through a wide area network (WAN). Remote Network Monitoring (RMON) 13. _____ is software that is embedded into hardware in order to control the device. Firmware 14. Once an AP’s firmware has been upgraded there are sev ...
... 12. _____ is an SNMP-based tool that is used to monitor LANs that are connected through a wide area network (WAN). Remote Network Monitoring (RMON) 13. _____ is software that is embedded into hardware in order to control the device. Firmware 14. Once an AP’s firmware has been upgraded there are sev ...
Part 1
... this system using your CPSC Email address and your CPSC Login Password. For your reference, here are some selected headers from the email: ...
... this system using your CPSC Email address and your CPSC Login Password. For your reference, here are some selected headers from the email: ...
Factsheet - KFSensor
... Intrusion detection plays a vital role in ensuring the integrity of a network's security. Network intrusion detection systems (NIDS) have long been seen as the most effective means of detecting attacks. However they do have significant weaknesses. The increasing quantity and diversity of legitimate ...
... Intrusion detection plays a vital role in ensuring the integrity of a network's security. Network intrusion detection systems (NIDS) have long been seen as the most effective means of detecting attacks. However they do have significant weaknesses. The increasing quantity and diversity of legitimate ...
ppt in chapter 11
... for security are based on a some recipe of internal and perimeter routers plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, and they do this using access lists. You can see where each of these ...
... for security are based on a some recipe of internal and perimeter routers plus firewall devices. Internal routers provide additional security to the network by screening traffic to various parts of the protected corporate network, and they do this using access lists. You can see where each of these ...
PowerPoint Presentation - IF-MAP
... Security and Privacy Considerations • MAP = Storehouse of Sensitive Data, Critical Nerve Center – MUST • TLS with mutual auth for IF-MAP clients • publisher-id and timestamp to track changes ...
... Security and Privacy Considerations • MAP = Storehouse of Sensitive Data, Critical Nerve Center – MUST • TLS with mutual auth for IF-MAP clients • publisher-id and timestamp to track changes ...
Addressing security threats and vulnerabilities
... Identifying attacks Replay attack – Intercepting and recording a connection setup and replaying at a later time to gain authorised access ...
... Identifying attacks Replay attack – Intercepting and recording a connection setup and replaying at a later time to gain authorised access ...
Confidentiality Undertaking - College of Pharmacists of British
... Operations and Drug Scheduling Act and the Bylaws of the College of Pharmacists of BC made pursuant to these Acts, or as required in my capacity as a physician in the rendering of medical care to the patient. 2. I agree at all times to treat as confidential all information referred to in paragraph ( ...
... Operations and Drug Scheduling Act and the Bylaws of the College of Pharmacists of BC made pursuant to these Acts, or as required in my capacity as a physician in the rendering of medical care to the patient. 2. I agree at all times to treat as confidential all information referred to in paragraph ( ...
Preface
... situation gradually changed with the expanding telecommunication industry. Communication systems that were completely controlled by computers demanded new techniques to protect the information flowing through the network. In 1976, the paper “New Directions in Cryptography”, by Whitfield Diffie and M ...
... situation gradually changed with the expanding telecommunication industry. Communication systems that were completely controlled by computers demanded new techniques to protect the information flowing through the network. In 1976, the paper “New Directions in Cryptography”, by Whitfield Diffie and M ...
Network Traffic Monitoring and Analysis
... • The Managed Devices contain the SNMP Agent and can consist of routers, switches, hubs, printers. They are responsible for collecting information and making it available to the NMSs. • The Agents contain software that have knowledge of management information and translates this information into a ...
... • The Managed Devices contain the SNMP Agent and can consist of routers, switches, hubs, printers. They are responsible for collecting information and making it available to the NMSs. • The Agents contain software that have knowledge of management information and translates this information into a ...
Intrusion Detection Prevention Systems
... confidentiality, integrity, availability, or to bypass the security mechanisms of a computer system or network( illegal access). • Intrusions have many causes, such as malware (worms, spyware, etc…), attackers gaining unauthorized access to systems from the Internet, and authorized users of systems ...
... confidentiality, integrity, availability, or to bypass the security mechanisms of a computer system or network( illegal access). • Intrusions have many causes, such as malware (worms, spyware, etc…), attackers gaining unauthorized access to systems from the Internet, and authorized users of systems ...