chapter 3
... from Prolexic Technologies claim a new type of distributed denial-of-service (DDoS) attack has not only increased in size, but also reached a new level of sophistication. DDoS attacks have recently caused a lot of problems for organizations; in September, the sites of several financial institutions ...
... from Prolexic Technologies claim a new type of distributed denial-of-service (DDoS) attack has not only increased in size, but also reached a new level of sophistication. DDoS attacks have recently caused a lot of problems for organizations; in September, the sites of several financial institutions ...
Network Security For Distributed Simulation Systems
... 3: MS encrypts data with its private key and returns data to network ...
... 3: MS encrypts data with its private key and returns data to network ...
Leaders` Forum, March 16, 2006 - University of Western Ontario
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
Word
... The functions of an operating system 1. Manages and Interacts with Computer Hardware 2. Provides and Manages System Security 3. Provides the System Interface 4. Provides the Interface for Application Software 1. Manages and Interacts with Computer Hardware Manages the CPU ...
... The functions of an operating system 1. Manages and Interacts with Computer Hardware 2. Provides and Manages System Security 3. Provides the System Interface 4. Provides the Interface for Application Software 1. Manages and Interacts with Computer Hardware Manages the CPU ...
here - Penndel Mental Health Center
... exceptions and report on them upon request. 4.0 Enforcement The IS Security Officer will periodically review Internet use monitoring and filtering systems and processes to ensure they are in compliance with this policy. Any employee found to have violated this policy will be reported to their direct ...
... exceptions and report on them upon request. 4.0 Enforcement The IS Security Officer will periodically review Internet use monitoring and filtering systems and processes to ensure they are in compliance with this policy. Any employee found to have violated this policy will be reported to their direct ...
How to Prevent Unauthorized Access to Laser Beam Printers and
... This guide provides additional information related to the Canon Laser Beam Printers and Small-Office MFPs, and in particular, steps you can take to enhance the secure operation of this device. This document will help you better understand how the device functions and will help you feel confident tha ...
... This guide provides additional information related to the Canon Laser Beam Printers and Small-Office MFPs, and in particular, steps you can take to enhance the secure operation of this device. This document will help you better understand how the device functions and will help you feel confident tha ...
Slide 1
... Changing Threat Landscape Evolution of NAC to Security Automation Intro to Bradford Networks Leveraging Integration and Correlation Rapid Threat Response Business Impact ...
... Changing Threat Landscape Evolution of NAC to Security Automation Intro to Bradford Networks Leveraging Integration and Correlation Rapid Threat Response Business Impact ...
COEN 152 Computer Forensics
... Internet auction fraud Computer is used for intrusion of another system. ...
... Internet auction fraud Computer is used for intrusion of another system. ...
Agenda
... Computer Security Basics – Identification & Authentication – SSL encryption and Internet security – Network Security ...
... Computer Security Basics – Identification & Authentication – SSL encryption and Internet security – Network Security ...
Designing a future Internet: Architecture and requirements
... In a virtual network, facilities (routers, links, etc.) are virtualized and then used by higher-level service providers to implement different networks, possibly using very different architectures. ...
... In a virtual network, facilities (routers, links, etc.) are virtualized and then used by higher-level service providers to implement different networks, possibly using very different architectures. ...
Module F - Columbus State University
... Fraudulent e-mails designed to dupe Internet users out of their credit card details or bank information topped the three billion mark last month, according to one of the largest spam e-mail filtering ...
... Fraudulent e-mails designed to dupe Internet users out of their credit card details or bank information topped the three billion mark last month, according to one of the largest spam e-mail filtering ...
Overview of Knowledge Discovery in Databases Process and Data
... Development of more effective early warning systems (EWSs) for various applications have been possible during the past decade due to advancements in information, detection, data mining (DM) and surveillance technologies. These application areas include economy, banking, finance, health care, bioinfo ...
... Development of more effective early warning systems (EWSs) for various applications have been possible during the past decade due to advancements in information, detection, data mining (DM) and surveillance technologies. These application areas include economy, banking, finance, health care, bioinfo ...
Security+ Guide to Network Security Fundamentals
... 1. Draft a written security policy 2. Design the firewall to implement the policy 3. Implement the design by installing selected hardware and software 4. Test the firewall 5. Review new threats, requirements for additional security, and updates to systems and software; repeat process from first step ...
... 1. Draft a written security policy 2. Design the firewall to implement the policy 3. Implement the design by installing selected hardware and software 4. Test the firewall 5. Review new threats, requirements for additional security, and updates to systems and software; repeat process from first step ...
Viruses - Bozonline
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
... What is a denial of service attack and back door? A denial of service attack is an assault which disrupts access to an Internet service such as the Web or e-mail ...
The Advanced Penetration Testing Boot Camp
... Data leakage filled the headlines in 2008 as corporations and government proved themselves to be lax in protecting their confidential data. • Organizations of all sizes are finding that today’s mobile and collaborative workforce needs access to information inside and outside the office, along with t ...
... Data leakage filled the headlines in 2008 as corporations and government proved themselves to be lax in protecting their confidential data. • Organizations of all sizes are finding that today’s mobile and collaborative workforce needs access to information inside and outside the office, along with t ...
How UTM Solutions Provide the Most Complete
... Reputation Enabled Defense delivers a secure web browsing experience through a reputation service that scores URLs as good, bad, or unknown. URLs with bad reputations are immediately blocked, while URLs with good reputations are passed through without further AV scanning, for substantial gains in we ...
... Reputation Enabled Defense delivers a secure web browsing experience through a reputation service that scores URLs as good, bad, or unknown. URLs with bad reputations are immediately blocked, while URLs with good reputations are passed through without further AV scanning, for substantial gains in we ...
Data Confidentiality
... • to gain authorisation, a user must identify themself • usually by entering a user name (User ID) • other methods of supplying User IDs include: – such as a magnetic stripe on the back of a card, – a smart chip on a card, ...
... • to gain authorisation, a user must identify themself • usually by entering a user name (User ID) • other methods of supplying User IDs include: – such as a magnetic stripe on the back of a card, – a smart chip on a card, ...
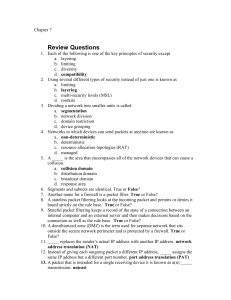
Chapter07
... A rootkit is a set of software tools used by an attacker to break into a computer and obtain special operating system privileges in order to both perform unauthorized functions and also hide all traces of its existence. A rootkit often includes several programs designed to monitor traffic, create a ...
... A rootkit is a set of software tools used by an attacker to break into a computer and obtain special operating system privileges in order to both perform unauthorized functions and also hide all traces of its existence. A rootkit often includes several programs designed to monitor traffic, create a ...
Security+ Guide to Network Security Fundamentals
... Identify major components used in a DDoS attack and how they are installed Understand major types of spoofing attacks Discuss man-in-the-middle attacks, replay attacks, and TCP session hijacking continued… ...
... Identify major components used in a DDoS attack and how they are installed Understand major types of spoofing attacks Discuss man-in-the-middle attacks, replay attacks, and TCP session hijacking continued… ...
How Organizations Are Using Fortscale`s User Behavior Analytics
... Fortscale constantly identifies new users and new machines in an enterprise and generates reports analysts can review to ensure these accounts and machines are valid in the network. On one occasion, Fortscale detected a new user account in the enterprise and began analyzing activity to build a basel ...
... Fortscale constantly identifies new users and new machines in an enterprise and generates reports analysts can review to ensure these accounts and machines are valid in the network. On one occasion, Fortscale detected a new user account in the enterprise and began analyzing activity to build a basel ...