Virtual Private Network(VPN)
... VPN Security authentication—ensuring that the data originates at the source that it claims access control—restricting unauthorized users from gaining admission to the network confidentiality—preventing anyone from reading or copying data as it travels across the Internet data integrity—ensu ...
... VPN Security authentication—ensuring that the data originates at the source that it claims access control—restricting unauthorized users from gaining admission to the network confidentiality—preventing anyone from reading or copying data as it travels across the Internet data integrity—ensu ...
IEEE CONFERENCE ON COMMUNICATION TECHNOLOGIES
... domains of Telecommunications, Information Security and Software Engineering, MCS is planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Con ...
... domains of Telecommunications, Information Security and Software Engineering, MCS is planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Con ...
Mod_7-Ch11
... Authentication • Authentication – Identifying users and the actions they are allowed to perform – A user can be identified by: • a unique characteristic of the person (e.g., fingerprints, voiceprints, retina scans and signatures) • ownership of an item (e.g., badges, identification cards, keys and ...
... Authentication • Authentication – Identifying users and the actions they are allowed to perform – A user can be identified by: • a unique characteristic of the person (e.g., fingerprints, voiceprints, retina scans and signatures) • ownership of an item (e.g., badges, identification cards, keys and ...
Review Questions
... a vulnerability. A. attack B. threat C. risk D. exploitation 2. _____ is a systematic and structured approach to managing the potential for loss that is related to a threat. A. Asset management B. Risk assessment (RA) C. Threat mitigation D. Risk management 3. Each of the following is a step in risk ...
... a vulnerability. A. attack B. threat C. risk D. exploitation 2. _____ is a systematic and structured approach to managing the potential for loss that is related to a threat. A. Asset management B. Risk assessment (RA) C. Threat mitigation D. Risk management 3. Each of the following is a step in risk ...
Computer Security, Ethics, and Privacy
... Identify ways to safeguard against computer viruses, worms, Trojan horses, botnets, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against soft ...
... Identify ways to safeguard against computer viruses, worms, Trojan horses, botnets, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against soft ...
Chapter 14 Network Security - Northern Arizona University
... and programs to see how they work. • Crackers - those that break in to computer systems to tamper with, steal, or destroy data. • Virus - it causes some unexpected and usually undesirable event. • Worms - a self-replicating virus that does not alter files but resides in active memory and duplicates ...
... and programs to see how they work. • Crackers - those that break in to computer systems to tamper with, steal, or destroy data. • Virus - it causes some unexpected and usually undesirable event. • Worms - a self-replicating virus that does not alter files but resides in active memory and duplicates ...
Chapter 14 Network Security
... and programs to see how they work. • Crackers - those that break in to computer systems to tamper with, steal, or destroy data. • Virus - it causes some unexpected and usually undesirable event. • Worms - a self-replicating virus that does not alter files but resides in active memory and duplicates ...
... and programs to see how they work. • Crackers - those that break in to computer systems to tamper with, steal, or destroy data. • Virus - it causes some unexpected and usually undesirable event. • Worms - a self-replicating virus that does not alter files but resides in active memory and duplicates ...
recr_presentation_oldest - Computer Science and Engineering
... Computer Architecture • Computer Systems Research Lab – Uses advanced hardware and software design tools to achieve: • Better performance • Lower power requirements • Equipment that is less expensive to manufacture ...
... Computer Architecture • Computer Systems Research Lab – Uses advanced hardware and software design tools to achieve: • Better performance • Lower power requirements • Equipment that is less expensive to manufacture ...
The University of Oklahoma Virtual Private Network
... Abbreviation of Transmission Control Protocol, and TCP is one of the main protocols in TCP/IP networks. Whereas the IP protocol deals only with packets, TCP enables two hosts to establish a connection and exchange streams of data. TCP guarantees delivery of data and also guarantees that packets will ...
... Abbreviation of Transmission Control Protocol, and TCP is one of the main protocols in TCP/IP networks. Whereas the IP protocol deals only with packets, TCP enables two hosts to establish a connection and exchange streams of data. TCP guarantees delivery of data and also guarantees that packets will ...
Slide 1
... Residential Networks: DSL Digital Subscriber Line (DSL) uses the Ordinary Telephone line and is an always-on technology. This means there is no need to dial up each time to connect to the Internet. Because DSL is highly dependent upon noise levels, a subscriber cannot be any more than 5.5 kilometers ...
... Residential Networks: DSL Digital Subscriber Line (DSL) uses the Ordinary Telephone line and is an always-on technology. This means there is no need to dial up each time to connect to the Internet. Because DSL is highly dependent upon noise levels, a subscriber cannot be any more than 5.5 kilometers ...
WiFi Security: Keeping Your Information Private and Safe
... between them, making them believe that they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker. The attacker must be able to intercept all messages going between the two victims and inject new ones, which is straightforwar ...
... between them, making them believe that they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker. The attacker must be able to intercept all messages going between the two victims and inject new ones, which is straightforwar ...
Chapter 19
... 802.11i Architecture • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. • Privacy with message integrity: MAC-level data are encrypted ...
... 802.11i Architecture • Authentication: protocol used to define an exchange between a user and an AS • Access control: function that enforces the use of the authentication function, routes messages properly and facilitates key exchange. • Privacy with message integrity: MAC-level data are encrypted ...
Network Improvement Project
... Senior Information Security Analyst and Information Security Trainer Salary + benefits - $134,000 Laptop Encryption Phase 1 - $42,000 UTSA President issued a mandate that affects every campus laptop user: all universityowned laptops will be encrypted. This mandate is in response to UT System Secur ...
... Senior Information Security Analyst and Information Security Trainer Salary + benefits - $134,000 Laptop Encryption Phase 1 - $42,000 UTSA President issued a mandate that affects every campus laptop user: all universityowned laptops will be encrypted. This mandate is in response to UT System Secur ...
General Overview of Attacks
... version of UNIX, including installation of “Sniffers” that can steal unencrypted passwords when people log on to the systems. 3. Denial-of-service attacks were particularly troubling for internet service providers. ...
... version of UNIX, including installation of “Sniffers” that can steal unencrypted passwords when people log on to the systems. 3. Denial-of-service attacks were particularly troubling for internet service providers. ...
TMDE Web Site
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
... • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
File
... A virus runs when the user launches an infected program or boots from an infected disk. Viruses keep a low profile, so as to spread widely without being detected. Most of the time, the virus code simply infects new programs or disks. Eventually, often at a predefined date and time, the virus payload ...
... A virus runs when the user launches an infected program or boots from an infected disk. Viruses keep a low profile, so as to spread widely without being detected. Most of the time, the virus code simply infects new programs or disks. Eventually, often at a predefined date and time, the virus payload ...
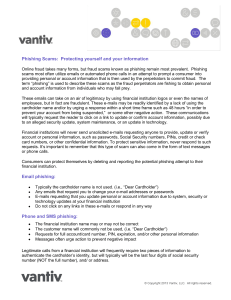
Phishing Scams - Corner Stone Credit Union
... providing personal or account information that is then used by the perpetrators to commit fraud. The term “phishing” is used to describe these scams as the fraud perpetrators are fishing to obtain personal and account information from individuals who may fall prey. These emails can take on an air of ...
... providing personal or account information that is then used by the perpetrators to commit fraud. The term “phishing” is used to describe these scams as the fraud perpetrators are fishing to obtain personal and account information from individuals who may fall prey. These emails can take on an air of ...
5th Chapter - information systems and it audit
... Review network Diagram Identify Network Design Dissemination of policies and standards Experience/knowledge of security operators for internet legislative issues are considered against usage of internet based application Review of service level contract in case of outsourcing. Hardware and software ...
... Review network Diagram Identify Network Design Dissemination of policies and standards Experience/knowledge of security operators for internet legislative issues are considered against usage of internet based application Review of service level contract in case of outsourcing. Hardware and software ...
NITC yearly Work Plan FY2065/66
... Illegal taking of another’s property - physical, electronic, or intellectual The value of information suffers when it is copied and taken away without the owner’s knowledge ...
... Illegal taking of another’s property - physical, electronic, or intellectual The value of information suffers when it is copied and taken away without the owner’s knowledge ...
AccessControlSimulation
... ability to ensure that its financial and taxpayer information is secure from internal threats. This reduces IRS's assurance that its financial statements and other financial information are fairly presented or reliable and that sensitive IRS and taxpayer information is being sufficiently safeguarded ...
... ability to ensure that its financial and taxpayer information is secure from internal threats. This reduces IRS's assurance that its financial statements and other financial information are fairly presented or reliable and that sensitive IRS and taxpayer information is being sufficiently safeguarded ...
Introduction to management of Information Technologies
... between a virus, a worm, and a Trojan horse? How could a stand-alone computer or a network be a victim of an illicit content attack? 3) What is an Open Mail server? How could you protect a standalone computer or a network against illicit content attacks? ...
... between a virus, a worm, and a Trojan horse? How could a stand-alone computer or a network be a victim of an illicit content attack? 3) What is an Open Mail server? How could you protect a standalone computer or a network against illicit content attacks? ...
document
... Open networks violate this assumption Encryption should protect control information, as well as ...
... Open networks violate this assumption Encryption should protect control information, as well as ...
網路犯罪案例 Cyber crime Case
... Network Packet Forensics Analysis Training The knowledge of network packet analysis is important for Forensic Investigators and Lawful Enforcement Agency (LEA) to carry out their daily duty. Network Packet Forensics Analysis Training (NPFAT) provides useful and sufficient knowledge required to anal ...
... Network Packet Forensics Analysis Training The knowledge of network packet analysis is important for Forensic Investigators and Lawful Enforcement Agency (LEA) to carry out their daily duty. Network Packet Forensics Analysis Training (NPFAT) provides useful and sufficient knowledge required to anal ...
The wild world of malware: Keeping your
... traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download applications. As the number and severity of cyber-crimes continues to grow, it’s important to understand th ...
... traditional network security and incorporate protection against malware and exploits that pass through PCs and mobile devices when users browse the Internet, send or receive email and download applications. As the number and severity of cyber-crimes continues to grow, it’s important to understand th ...