Network Security
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
networkworld - Sift Security
... As soon as a customer installs the Sift Security software (on premises or on AWS using commodity hardware), the platform begins to ingest data from whatever sources are pointed to it. These can be existing logs or custom or proprietary logs. Since Sift Security's software isn't priced according to d ...
... As soon as a customer installs the Sift Security software (on premises or on AWS using commodity hardware), the platform begins to ingest data from whatever sources are pointed to it. These can be existing logs or custom or proprietary logs. Since Sift Security's software isn't priced according to d ...
Chap 3
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
... The primary purpose of DoS attacks is to steal vital information. (T/F) Name three types of DoS attack. The ping of death works based on using very large ICMP packets that must be fragmented to send and when reassembled are too large for the receiver’s buffer. (T/F) How can a router stop packets fro ...
View Presentation - InfoSec Nashville
... Health Insurance Credentials – Health insurance credentials are $20 each. They include names (more than one for spouse & family coverage), date(s) of birth, contract number, group number, type of plan (Individual/Group, HMO/PPO, deductible and copay information), and insurer contact information for ...
... Health Insurance Credentials – Health insurance credentials are $20 each. They include names (more than one for spouse & family coverage), date(s) of birth, contract number, group number, type of plan (Individual/Group, HMO/PPO, deductible and copay information), and insurer contact information for ...
Operating System Security Fundamentals
... – Employs a challenge/response authentication protocol – No longer used ...
... – Employs a challenge/response authentication protocol – No longer used ...
Computer Science, MSCS - Northeastern University
... Northeastern University’s Master of Science in Computer Science is designed to prepare students for a variety of careers in computer science. The program combines both computing and important application domains—enabling you to increase your broad-based knowledge in the field while focusing on one c ...
... Northeastern University’s Master of Science in Computer Science is designed to prepare students for a variety of careers in computer science. The program combines both computing and important application domains—enabling you to increase your broad-based knowledge in the field while focusing on one c ...
Systems Administrator needed for DoD Griffin Cyberspace Defense
... filter sensor traffic and alerts reporting activity based on Crew CC’s instruction that traffic does not need to be reviewed in a “real-time” operation by 33 NWS analysts. Monitor the effectiveness of the IDS/IPS sensor’s ability to collect and report suspicious network activity on Air Force network ...
... filter sensor traffic and alerts reporting activity based on Crew CC’s instruction that traffic does not need to be reviewed in a “real-time” operation by 33 NWS analysts. Monitor the effectiveness of the IDS/IPS sensor’s ability to collect and report suspicious network activity on Air Force network ...
Figure 6-1
... 2 - Corruption (an attack on integrity): – Unauthorized tampering with an asset 3 - Removal (an attack on availability): – Theft, removal or loss of information and/or other resources 4 - Disclosure (an attack on confidentiality): – Unauthorized access to an asset 5 - Interruption (an attack on avai ...
... 2 - Corruption (an attack on integrity): – Unauthorized tampering with an asset 3 - Removal (an attack on availability): – Theft, removal or loss of information and/or other resources 4 - Disclosure (an attack on confidentiality): – Unauthorized access to an asset 5 - Interruption (an attack on avai ...
Integrity - Andrew.cmu.edu
... of keeping secrets is in knowing the areas that you need to protect. • What knowledge would enable someone to circumvent your system? • You should jealously guard that knowledge and assume that everything else is known to your adversaries. • The more secrets you have, the harder it will be to keep t ...
... of keeping secrets is in knowing the areas that you need to protect. • What knowledge would enable someone to circumvent your system? • You should jealously guard that knowledge and assume that everything else is known to your adversaries. • The more secrets you have, the harder it will be to keep t ...
Cisco on Cisco Chevron Presentation
... an end-to-end secure borderless architecture for on-boarding mobile devices around the globe • Shared our connected workplace strategy enabling ...
... an end-to-end secure borderless architecture for on-boarding mobile devices around the globe • Shared our connected workplace strategy enabling ...
LSD1518 - Control Cloud Data Access Privilege
... schemes based on the attribute-based encryption have been proposed to secure the cloud storage. However, most work focuses on the data contents privacy and the access control, while less attention is paid to the privilege control and the identity privacy. In this paper, we present a semi-anonymous p ...
... schemes based on the attribute-based encryption have been proposed to secure the cloud storage. However, most work focuses on the data contents privacy and the access control, while less attention is paid to the privilege control and the identity privacy. In this paper, we present a semi-anonymous p ...
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... Most customers were large production systems requiring high uptime. 1997 to 1998, Network Security Administrator, StateNET, Sacramento, CA. Audited and secured a small class-C network with 5 servers and about 400 remote/local users Redesigned and re-implemented firewall-1 rule sets Hardened ...
... Most customers were large production systems requiring high uptime. 1997 to 1998, Network Security Administrator, StateNET, Sacramento, CA. Audited and secured a small class-C network with 5 servers and about 400 remote/local users Redesigned and re-implemented firewall-1 rule sets Hardened ...
6.01 RCNET Module
... offending packet(s), or by forcing a reset of the offending TCP/IP session. IPS works in-line, and therefore may introduce latency. Logging- In computing, a logfile is a file that records either events that occur in an operating system or other software runs, or messages between different users of c ...
... offending packet(s), or by forcing a reset of the offending TCP/IP session. IPS works in-line, and therefore may introduce latency. Logging- In computing, a logfile is a file that records either events that occur in an operating system or other software runs, or messages between different users of c ...
Network Security
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
... algorithms and protocols underlying network security applications, including encryption, hash functions, digital signatures, and key exchange. • Part Two : Examines the use of cryptographic algorithms and security protocols to provide security over networks and the Internet. Topics covered include u ...
Tool: Spector CNE Tool: Track4Win
... • It obtains proof to support accusations of wrongdoing. • It reduces security breaches. • It detects the use of organization resources to engage in illegal or unethical activities. • It limits legal liability (including sexual and racial harassment). • It enforces PC and Internet acceptable-use pol ...
... • It obtains proof to support accusations of wrongdoing. • It reduces security breaches. • It detects the use of organization resources to engage in illegal or unethical activities. • It limits legal liability (including sexual and racial harassment). • It enforces PC and Internet acceptable-use pol ...
POST MASTER DEGREE IN SECURITY IN COMPUTER SYSTEMS
... this board, - understand the hardware and low level software better (secure boot, communications between the 2 processors, OS on the quark CPU). - find if a user can take ownership of the platform (or has to run code signed by someone else, which has to be trusted) ...
... this board, - understand the hardware and low level software better (secure boot, communications between the 2 processors, OS on the quark CPU). - find if a user can take ownership of the platform (or has to run code signed by someone else, which has to be trusted) ...
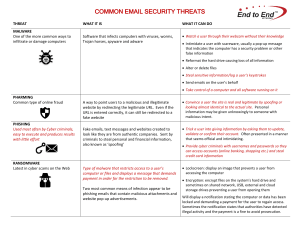
COMMON EMAIL SECURITY THREATS
... computer or files and displays a message that demands payment in order for the restriction to be removed. ...
... computer or files and displays a message that demands payment in order for the restriction to be removed. ...
Disclaimer - euphore home page
... liability or responsibility for the accuracy, completeness, or usefulness of any information, analysis procedure, tools or process descriptions disclosed. Security We inform the users of these Web pages that for site security purposes, as well as to ensure that this service remains available to all ...
... liability or responsibility for the accuracy, completeness, or usefulness of any information, analysis procedure, tools or process descriptions disclosed. Security We inform the users of these Web pages that for site security purposes, as well as to ensure that this service remains available to all ...
set 2 - of Manish Mehta
... • “sniffed” off the wire in real-time by the sensor. (a stand-alone machine or a network device in promiscuous mode) • Detection engine matches the predefined patterns. If matched, Alert is generated and forwarded to central console. • Security officer is notified. ...
... • “sniffed” off the wire in real-time by the sensor. (a stand-alone machine or a network device in promiscuous mode) • Detection engine matches the predefined patterns. If matched, Alert is generated and forwarded to central console. • Security officer is notified. ...
Auditor Senior IT Ad 4 3 2017
... areas: Information Security, Systems Administration, IT Operations, Access Management, Data Backup Restoration, Project Management, Asset Management, Database Management (Oracle and SQL), Change Management, Data Center Security, Data Mining, PCI Compliance, Network Engineering, Application Developme ...
... areas: Information Security, Systems Administration, IT Operations, Access Management, Data Backup Restoration, Project Management, Asset Management, Database Management (Oracle and SQL), Change Management, Data Center Security, Data Mining, PCI Compliance, Network Engineering, Application Developme ...
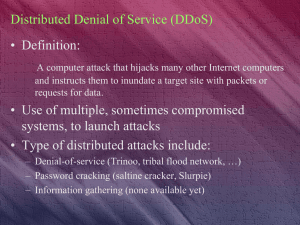
Distributed Denial of Service (DDoS)
... • Employ strong gateway protection (firewall, edge router rules, etc.) • Use intrusion detection tools to detect specific packet attacks • Check for Trojan horse and zombie code – Network vulnerability scans – Host vulnerability scans – Antivirus ...
... • Employ strong gateway protection (firewall, edge router rules, etc.) • Use intrusion detection tools to detect specific packet attacks • Check for Trojan horse and zombie code – Network vulnerability scans – Host vulnerability scans – Antivirus ...
Discovering Computers Fundamentals 4th Edition
... Identify ways to safeguard against computer viruses, worms, Trojan horses, botnets, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against soft ...
... Identify ways to safeguard against computer viruses, worms, Trojan horses, botnets, denial of service attacks, back doors, and spoofing Discuss techniques to prevent unauthorized computer access and use Identify safeguards against hardware theft and vandalism Explain the ways to protect against soft ...
documentstyle[12pt]{article} - Global Knowledge Management
... Students – Lin Lin, Li Ji, and Allis Kuo Graudated members – Lee Dunlap, Richard Farmers, Elvina Hendrata and Dan McDonald, UA-MIS Master Science ...
... Students – Lin Lin, Li Ji, and Allis Kuo Graudated members – Lee Dunlap, Richard Farmers, Elvina Hendrata and Dan McDonald, UA-MIS Master Science ...
Chap 9 - IUP Personal Websites
... through public networks (eg, Internet) Lowest levels of TCP/IP are implemented using existing TCP/IP connection Encrypts either underlying data in a packet or the entire packet itself before wrapping it in another IP packet for delivery Further enhances security by implementing Internet Protocol Sec ...
... through public networks (eg, Internet) Lowest levels of TCP/IP are implemented using existing TCP/IP connection Encrypts either underlying data in a packet or the entire packet itself before wrapping it in another IP packet for delivery Further enhances security by implementing Internet Protocol Sec ...










![documentstyle[12pt]{article} - Global Knowledge Management](http://s1.studyres.com/store/data/002138920_1-bd878a9ad97119a4308a7c0b9304567f-300x300.png)
