* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Assignment #2 S.Popovic
Survey
Document related concepts
Transcript
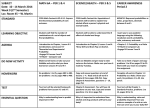
Steven Popovic 03/02/10 Computer Science 316 Computer Host Security 1. Using the web, find out who Kevin Mitnick was. What did he do? Who caught him? Write a short summary of his activities and why he is famous. Compromised the LA bus transfer system to get free bus rides. Evading the FBI Gaining full admin privileges to a IBM minicomputer at the computer learning center in LA in order to win a bet. Hacked Motorola, NEC, Nokia, and Sun Microsystems. At the time of his arrest, Kevin was the most-wanted computer criminal in the USA. Was arrested by the FBI on February 15, 1995. 2. Consider the statement: an individual threat, like a hacker, can be represented in more than one threat category. If a hacker hacks into a network, copies a few files, defaces the Web page, and steals credit card numbers, how many different threat categories does this attack cover? Harrassment for defacing a website. Property damage for defacing the website. Idenity theft if he uses the credit card numbers. Trespassing onto a unautheroized network. Riskware 3. Assume that a user has the chance to pick letters for passwords from a set of 82 different characters. Compute the average time that a brute force program takes to guess a 9-character password. Assume that each trial needs four machine language instructions and each instruction is executed in 35 nanoseconds. Ignore any other overhead. 140 nanoseconds per each trial. 82^9 = 167,619,550,409,708,032 unique combinations. 82^9 * 140 = Amount of nanoseconds required to check all possible combinations. 23,466,737,057,359,124,480 nanoseconds to check all possible combinations. Divided by two to get the average which is 11,733,368,528,679,562,240 nsec. 11,733,368,529 sec = 195,556,142 min = 3,259,269 hours = 135,803 days http://en.wikipedia.org/wiki/Nanosecond http://en.wikipedia.org/wiki/Kevin_Mitnick http://www.f-secure.com/en_EMEA/security/security-lab/learn-more/threatcategories/