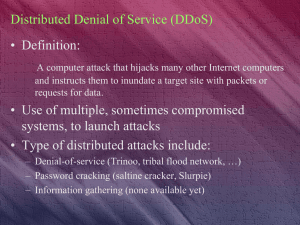
Chapter 2: Attackers and Their Attacks
... Operating systems are intended to be dynamic As users’ needs change, new hardware is introduced, and more sophisticated attacks are unleashed, operating systems must be updated on a regular basis However, vendors release a new version of an operating system every two to four years Vendors use certai ...
... Operating systems are intended to be dynamic As users’ needs change, new hardware is introduced, and more sophisticated attacks are unleashed, operating systems must be updated on a regular basis However, vendors release a new version of an operating system every two to four years Vendors use certai ...
Networking and System Administration (NaSA) Bachelor of Science in
... The Networking and System Administration major is a timely program aimed at preparing graduates for careers and research opportunities in all fields related to reliable and distributed network computing. Career Paths Include: ...
... The Networking and System Administration major is a timely program aimed at preparing graduates for careers and research opportunities in all fields related to reliable and distributed network computing. Career Paths Include: ...
application programs
... some of the details of the underlying hardware for such I/O. All the user sees is that the I/O has been performed, without those details. Communications There are instances where processes need to communicate with each other to exchange information. It may be between processes running on the same ...
... some of the details of the underlying hardware for such I/O. All the user sees is that the I/O has been performed, without those details. Communications There are instances where processes need to communicate with each other to exchange information. It may be between processes running on the same ...
An Introduction to Operating Systems
... OS provides an environment where the user can conveniently run programs. The user does not have to worry about memory allocation or CPU scheduling. ¾ I/O Operations Each program requires input and produces output. The OS hides some of the details of the underlying hardware for such I/O. All the user ...
... OS provides an environment where the user can conveniently run programs. The user does not have to worry about memory allocation or CPU scheduling. ¾ I/O Operations Each program requires input and produces output. The OS hides some of the details of the underlying hardware for such I/O. All the user ...
powerpoint slides for the guest lecture give by Shahrear Iqbal
... QUEEN’S UNIVERSITY, KINGSTON, ONTARIO, CANADA. ...
... QUEEN’S UNIVERSITY, KINGSTON, ONTARIO, CANADA. ...
slides - University of Cambridge Computer Laboratory
... something compels change • But should the government regulate (as with NERC/FERC) or facilitate (as the UK)? • See ‘Security Economics and Critical National Infrastructure’, on my web page, and at the Workshop on the Economics of Information Security, UCL, June 24–25 ...
... something compels change • But should the government regulate (as with NERC/FERC) or facilitate (as the UK)? • See ‘Security Economics and Critical National Infrastructure’, on my web page, and at the Workshop on the Economics of Information Security, UCL, June 24–25 ...
Linux
... Red Hat Linux : One of the original Linux distribution. The commercial, nonfree version is Red Hat Enterprise Linux, which is aimed at big companies using Linux servers and desktops in a big way. (NJIT) Free version: Fedora Project. ...
... Red Hat Linux : One of the original Linux distribution. The commercial, nonfree version is Red Hat Enterprise Linux, which is aimed at big companies using Linux servers and desktops in a big way. (NJIT) Free version: Fedora Project. ...
ENPM 808B: Secure Operating Systems
... may need privileged access – the file system provides this facility. Closely related to security policies is understanding the behavior of attackers and malicious users. For example, one common attacker behavior is to predict target memory addresses of programs. Because of this behavior, one securit ...
... may need privileged access – the file system provides this facility. Closely related to security policies is understanding the behavior of attackers and malicious users. For example, one common attacker behavior is to predict target memory addresses of programs. Because of this behavior, one securit ...
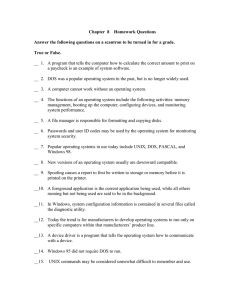
fund8que.doc
... __13. A device driver is a program that tells the operating system how to communicate with a device. __14. Windows 95 did not require DOS to run. __15. UNIX commands may be considered somewhat difficult to remember and use. ...
... __13. A device driver is a program that tells the operating system how to communicate with a device. __14. Windows 95 did not require DOS to run. __15. UNIX commands may be considered somewhat difficult to remember and use. ...
Top Five Current Operating System Issues
... As of last year, the contrasts between Windows Vista and OS X Leopard in the area of security were immense. On one side, Microsoft’s latest release of their Windows operating system had everything so locked down the user barely had room to right-click without being warned. Sure, you may never have a ...
... As of last year, the contrasts between Windows Vista and OS X Leopard in the area of security were immense. On one side, Microsoft’s latest release of their Windows operating system had everything so locked down the user barely had room to right-click without being warned. Sure, you may never have a ...
83-381 Syllabus English
... First Semester 2016/17 Weekly hours: 2 lecture + 1 training 1) Course objectives: An operating system is a set of subsystems/programs that manage a computer system composed of hardware and software resources, providing common services/utilities needed to run system and user applications. All compute ...
... First Semester 2016/17 Weekly hours: 2 lecture + 1 training 1) Course objectives: An operating system is a set of subsystems/programs that manage a computer system composed of hardware and software resources, providing common services/utilities needed to run system and user applications. All compute ...
Computer security - University of London International Programmes
... Lead College – Royal Holloway ...
... Lead College – Royal Holloway ...
Richard D - Expert Witness Network
... Establishing a proven record of steadfast leadership, managerial and administrative skills; he has been principally involved in the planning, coordination and management of large scale and discreet security operations, both domestic and foreign, in the most hostile environs. Providing consistent, po ...
... Establishing a proven record of steadfast leadership, managerial and administrative skills; he has been principally involved in the planning, coordination and management of large scale and discreet security operations, both domestic and foreign, in the most hostile environs. Providing consistent, po ...
Modern Operating Systems Modern Operating Systems
... • Process is a collection of one or more threads ...
... • Process is a collection of one or more threads ...
Slide 1
... Multithreading – parts of the same application can run as separate tasks (video and image processing) Multiprocessing – when a computer has multiple CPUs / Cores, a single running application can thread across cores. ...
... Multithreading – parts of the same application can run as separate tasks (video and image processing) Multiprocessing – when a computer has multiple CPUs / Cores, a single running application can thread across cores. ...
7.3.3. Computer System Structures
... The core services layer provides a variety of features, including support for cloud computing and databases. The bottom layer represents the core operating system, which is based on the kernel environment (not fully compatible with Unix). ...
... The core services layer provides a variety of features, including support for cloud computing and databases. The bottom layer represents the core operating system, which is based on the kernel environment (not fully compatible with Unix). ...
new zealand`s cyber security strategy
... Government Systems and Information Key initiatives: • National Cyber Security Centre • Improved government security practices ...
... Government Systems and Information Key initiatives: • National Cyber Security Centre • Improved government security practices ...
Trusted Operating Systems
... • Formal description of the allowable paths of information flow in a secure system • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
... • Formal description of the allowable paths of information flow in a secure system • Set of subjects and another set of objects • Each subject s has a fixed security clearance C(s) • Each object o has a fixed security class C(o) ...
ISA_673-android_presentation_(3) - eee
... • Build Batterymine into Android kernel • Modify code for most-used drivers • Attribute device usage to process where possible • Attribute to “Idle” otherwise. • Pros: Simple, allows for iterative development • Cons: – Requires intimate knowledge of driver code – Hardware dependent – Process ID not ...
... • Build Batterymine into Android kernel • Modify code for most-used drivers • Attribute device usage to process where possible • Attribute to “Idle” otherwise. • Pros: Simple, allows for iterative development • Cons: – Requires intimate knowledge of driver code – Hardware dependent – Process ID not ...
Distributed System Concepts and Architectures
... Fits well with object oriented paradigm Objects to be protected are associated with servers managing objects Each object has a set of allowable well formed operations that can be invoked by the client processes ...
... Fits well with object oriented paradigm Objects to be protected are associated with servers managing objects Each object has a set of allowable well formed operations that can be invoked by the client processes ...
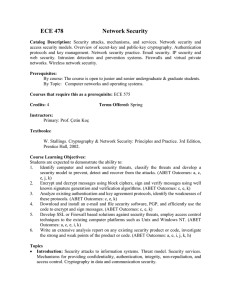
Course Learning Objectives:
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...
... 1. Identify computer and network security threats, classify the threats and develop a security model to prevent, detect and recover from the attacks. (ABET Outcomes: a, c, e, j, k) 2. Encrypt and decrypt messages using block ciphers, sign and verify messages using well known signature generation and ...