Fatema Nafa`s presentation on "Measures to
... Operating System where all security features are located. works as a part of an operating system to prevent unauthorized access to the system. contains criteria that must be met before specified programs can be accessed ...
... Operating System where all security features are located. works as a part of an operating system to prevent unauthorized access to the system. contains criteria that must be met before specified programs can be accessed ...
gst_115_9
... Up until now we've been happily communicating using the media access control address assigned to our networking devices. Our systems have used this number to contact other systems and transmit information as required. The problem with this scheme is that it does not scale very well. For example, wha ...
... Up until now we've been happily communicating using the media access control address assigned to our networking devices. Our systems have used this number to contact other systems and transmit information as required. The problem with this scheme is that it does not scale very well. For example, wha ...
Audit Considerations of Outsourcing
... PC and PC based server security continues to be improved by their vendors. Recently made available features include full hard disk encryption, application firewall and integrated malicious software features including anti-virus. In security, the weakest link is people, including people’s commitment ...
... PC and PC based server security continues to be improved by their vendors. Recently made available features include full hard disk encryption, application firewall and integrated malicious software features including anti-virus. In security, the weakest link is people, including people’s commitment ...
Chapter 19
... strong security. • Can be implemented in firewalls and routers owned by the organization, giving network managers control over security. ...
... strong security. • Can be implemented in firewalls and routers owned by the organization, giving network managers control over security. ...
Tutorial 1 Answers File
... *Manage network communications, such as for a local network and the Internet *Control input/output for devices such as network interface card *Control information storage and retrieval using various types of disk *Enable multimedia use for voice and video composition or reproduction, such as recordi ...
... *Manage network communications, such as for a local network and the Internet *Control input/output for devices such as network interface card *Control information storage and retrieval using various types of disk *Enable multimedia use for voice and video composition or reproduction, such as recordi ...
Operating systems
... An operating system (OS) is system software that manages computer hardware and software resources and provides common services for computer programs. All computer programs, excluding firmware, require an operating system to function. Time-sharing operating systems schedule tasks for efficient use of ...
... An operating system (OS) is system software that manages computer hardware and software resources and provides common services for computer programs. All computer programs, excluding firmware, require an operating system to function. Time-sharing operating systems schedule tasks for efficient use of ...
Chapter 04 - Regis University: Academic Web Server for Faculty
... Each piece can have its own access rights. A segment has a name and an offset value. Usually one OS segment address table per ...
... Each piece can have its own access rights. A segment has a name and an offset value. Usually one OS segment address table per ...
History of Operating Systems
... They did not run on Operating systems. They ran slowly at took up entire rooms. They needed a team to operate. The calculating engines used vacuum tubes; that were easy to burning out or break. Plug boards were programs inserted in the computer. This took place most of the 1940’s-50’s ...
... They did not run on Operating systems. They ran slowly at took up entire rooms. They needed a team to operate. The calculating engines used vacuum tubes; that were easy to burning out or break. Plug boards were programs inserted in the computer. This took place most of the 1940’s-50’s ...
Principal Security Engineer– PAE4IT A. PRIMARY ROLE Working
... and other information product based on that analysis. Collect, disseminate, and analyze information regarding active network security threats. Respond to requests for security analysis; write reports, papers, or other products as required. 30 Collect, analyze, and distill information regarding curre ...
... and other information product based on that analysis. Collect, disseminate, and analyze information regarding active network security threats. Respond to requests for security analysis; write reports, papers, or other products as required. 30 Collect, analyze, and distill information regarding curre ...
slides - CSE Home
... hierarchical file system; "everything" is a file lots of small programs that work together to solve larger problems security, users, access, and groups human-readable documentation included ...
... hierarchical file system; "everything" is a file lots of small programs that work together to solve larger problems security, users, access, and groups human-readable documentation included ...
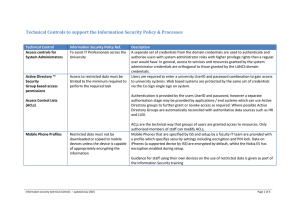
Technical Controls to support the Information
... preference for access level.). With this capability users obtain the correct level of access that their computer/device is registered for in all areas in which the PASS system is deployed (currently the campus wired network). MAC addresses can be easily be changed on many devices however the logging ...
... preference for access level.). With this capability users obtain the correct level of access that their computer/device is registered for in all areas in which the PASS system is deployed (currently the campus wired network). MAC addresses can be easily be changed on many devices however the logging ...
why uclinux? - Wireless Africa
... Until recently developers of small embedded systems based on microprocessors lacking MMU could not take advantage of Linux uCliknux was started by Arcturus networks in 1997 Implements Linux on MMU-less processors Publicly released back into open source as alternative OS for the Palm Pilot in Februar ...
... Until recently developers of small embedded systems based on microprocessors lacking MMU could not take advantage of Linux uCliknux was started by Arcturus networks in 1997 Implements Linux on MMU-less processors Publicly released back into open source as alternative OS for the Palm Pilot in Februar ...
Virtual Cyber Security Lab - Celtic-Plus
... Develops ICT software solutions for more than 200 global operators ...
... Develops ICT software solutions for more than 200 global operators ...
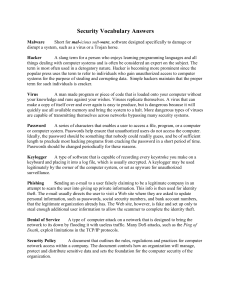
ITS_8_Security Vocab Answers
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...
... network to its down by flooding it with useless traffic. Many DoS attacks, such as the Ping of Death, exploit limitations in the TCP/IP protocols. Security Policy A document that outlines the rules, regulations and practices for computer network access within a company. The document controls how an ...
Chapter 1 Introduction
... services it requires. If it only interacts with the hardware in a small number of well-defined ways, it might be worthwhile. [Section 1.1] 3. Most single user, personal computers are now multitasking – there is more than one program running at the same time. There is a need to provide virtual memory ...
... services it requires. If it only interacts with the hardware in a small number of well-defined ways, it might be worthwhile. [Section 1.1] 3. Most single user, personal computers are now multitasking – there is more than one program running at the same time. There is a need to provide virtual memory ...
History of Unix OS - Seneca
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
Operating Systems
... Operating System as a Resource Manager Operating systems allow multiple programs to run at the same time Resource management includes multiplexing (sharing) resources Allocating disk space and keeping track of who is using which disk blocks is a typical operating system resource management task. ...
... Operating System as a Resource Manager Operating systems allow multiple programs to run at the same time Resource management includes multiplexing (sharing) resources Allocating disk space and keeping track of who is using which disk blocks is a typical operating system resource management task. ...
Chapter 21: The Linux System Objectives 21.1 History (不考) Linux 2.0
... Linus Torvalds, with the major design goal of UNIX compatibility ...
... Linus Torvalds, with the major design goal of UNIX compatibility ...
Name: Logan Foraker3-1 INTERNET REASEARCH ASSIGNMENT
... 13. In any device that has an____________ _____________, there's usually a way to make changes to how the device works. 14. Real-time operating systems are used to control machinery, ______________ ______________ and industrial systems. 15. A very important part of an ________is managing the resourc ...
... 13. In any device that has an____________ _____________, there's usually a way to make changes to how the device works. 14. Real-time operating systems are used to control machinery, ______________ ______________ and industrial systems. 15. A very important part of an ________is managing the resourc ...
Chapter 6 Introduction to Network Operating Systems
... • Linux is an operating system similar to UNIX. It runs on many different computers and was first released in 1991. • Linux is portable, which means versions can be found running on name brand or clone PCs. • Linux offers many features adopted from other versions of UNIX. ...
... • Linux is an operating system similar to UNIX. It runs on many different computers and was first released in 1991. • Linux is portable, which means versions can be found running on name brand or clone PCs. • Linux offers many features adopted from other versions of UNIX. ...
A User Mode L4 Environment
... operating system personalities is still difficult, requires more manpower, and additional hardware for testing. But as often in the early stage of a project, the additional testing hardware is either very expensive or not sufficiently available. Under the conditions of university research for practi ...
... operating system personalities is still difficult, requires more manpower, and additional hardware for testing. But as often in the early stage of a project, the additional testing hardware is either very expensive or not sufficiently available. Under the conditions of university research for practi ...
Information Security - National University of Sciences and
... someone else to access/take control of your system • Facilitates hacking of system • Hacking: To enter somebody system/account in an illegal way ...
... someone else to access/take control of your system • Facilitates hacking of system • Hacking: To enter somebody system/account in an illegal way ...
diebold nixdorf software terminal security intrusion protection
... No financial services provider is safe from the viruses, malware and Trojans that infiltrate or are covertly installed on self-service environments. In fact, reports on new variants of ATM malware are published every few months. Recently, security experts discovered that the infamous Ploutus malware ...
... No financial services provider is safe from the viruses, malware and Trojans that infiltrate or are covertly installed on self-service environments. In fact, reports on new variants of ATM malware are published every few months. Recently, security experts discovered that the infamous Ploutus malware ...
CS4023_-_lecture_02_..
... Decade of personal computers and workstations. Computing distributed to sites at which it was needed. IBM PC released in 1981. Personal computers proved relatively easy to learn and use. Apple releases the Macintosh PC in 1984, GUI embedded in the operating system. Richard Stallman launched the GNU ...
... Decade of personal computers and workstations. Computing distributed to sites at which it was needed. IBM PC released in 1981. Personal computers proved relatively easy to learn and use. Apple releases the Macintosh PC in 1984, GUI embedded in the operating system. Richard Stallman launched the GNU ...