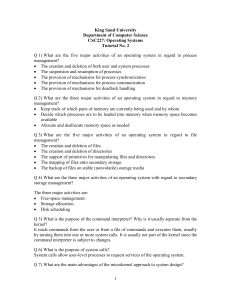
tutorial-02-with
... Benefits typically include the following (a) adding a new service does not require modifying the kernel, (b) it is more secure as more operations are done in user mode than in kernel mode, and (c) a simpler kernel design and functionality typically results in a more reliable operating system. Q 8) ...
... Benefits typically include the following (a) adding a new service does not require modifying the kernel, (b) it is more secure as more operations are done in user mode than in kernel mode, and (c) a simpler kernel design and functionality typically results in a more reliable operating system. Q 8) ...
Comparative Operating Systems Fall 2001 An Examination of
... The Linux operating system is a robust, sophisticated, highly reputable operating system for desktop PC's and servers. Since Linux is so well accepted, and free with open source code, it is no wonder that embedded developers have begun to look for ways to incorporate it into their devices. ...
... The Linux operating system is a robust, sophisticated, highly reputable operating system for desktop PC's and servers. Since Linux is so well accepted, and free with open source code, it is no wonder that embedded developers have begun to look for ways to incorporate it into their devices. ...
Intro and using Linux Commands
... services provide mechanisms for… Execution of a program, Input and output operations performed by programs, ...
... services provide mechanisms for… Execution of a program, Input and output operations performed by programs, ...
Language Based Operating Systems
... abstraction designed to perform some task or execute instructions designed for it rather than the actual environment it is deployed in. It may encapsulate some functionality, or emulate an existing machine. Common examples of VMs in programming are the Java Virtual Machine (JVM), CPython, the Ruby V ...
... abstraction designed to perform some task or execute instructions designed for it rather than the actual environment it is deployed in. It may encapsulate some functionality, or emulate an existing machine. Common examples of VMs in programming are the Java Virtual Machine (JVM), CPython, the Ruby V ...
Phoenix SIEM (Security Information and Event
... more than 10 years experience in cyber security software engineering. Some of the notable organizations I have worked for include BAE Systems, Rapid 7 and 3M. At BAE Systems I worked with NetReveal and Vuma, at Rapid 7 I worked with Nexpose and Metasploit, ...
... more than 10 years experience in cyber security software engineering. Some of the notable organizations I have worked for include BAE Systems, Rapid 7 and 3M. At BAE Systems I worked with NetReveal and Vuma, at Rapid 7 I worked with Nexpose and Metasploit, ...
Ch1 Introduction to the Linux Kernel
... The kernel typically resides in an elevated system state compared to normal user applications This includes a protected memory space and full access to the hardware This system state and memory space is collectively referred to as kernel-space ...
... The kernel typically resides in an elevated system state compared to normal user applications This includes a protected memory space and full access to the hardware This system state and memory space is collectively referred to as kernel-space ...
Protection
... and this development can be seriously impaired if data security is not taken into account when designing urbanized living areas. ...
... and this development can be seriously impaired if data security is not taken into account when designing urbanized living areas. ...
Certifications authenticate Blancco´s high standards
... and Windows Mobile). TÜV-SÜD also endorses Blancco for storage media, noting that it is “appropriate to safely and irrecoverably erase the data on all popular types of hard drives.” The Norwegian National Security Authority The Norwegian National Security Authority (NSM) approved Blancco HMG Softwar ...
... and Windows Mobile). TÜV-SÜD also endorses Blancco for storage media, noting that it is “appropriate to safely and irrecoverably erase the data on all popular types of hard drives.” The Norwegian National Security Authority The Norwegian National Security Authority (NSM) approved Blancco HMG Softwar ...
Operating System Security
... created by high-integrity processes. • high-integrity file cannot be contaminated by information from low-integrity processes. • high-integrity process cannot be subverted by low integrity processes or data. The integrity class label on a file guarantees that the contents came only from sources of a ...
... created by high-integrity processes. • high-integrity file cannot be contaminated by information from low-integrity processes. • high-integrity process cannot be subverted by low integrity processes or data. The integrity class label on a file guarantees that the contents came only from sources of a ...
ROOTKIT VIRUS
... system in order to conceal the altering of files, or processes being executed by the third party without the user's knowledge. ...
... system in order to conceal the altering of files, or processes being executed by the third party without the user's knowledge. ...
Design and Implementation of Security Operating System based on
... Analyzes and reviews relative work of security ...
... Analyzes and reviews relative work of security ...
Lecture 10 - The University of Texas at Dallas
... A person could have multiple identities - A physician could have an identity to access medical resources and another to access his bank accounts Digital identity management is about managing the multiple ...
... A person could have multiple identities - A physician could have an identity to access medical resources and another to access his bank accounts Digital identity management is about managing the multiple ...
OVERVIEW: Linux and Unix
... OS Structure File System Directories Structure Common Control Keys Unix Shells ...
... OS Structure File System Directories Structure Common Control Keys Unix Shells ...
Operating Systems
... movement, storage, and processing of data. • The OS is responsible for managing these resources. ...
... movement, storage, and processing of data. • The OS is responsible for managing these resources. ...
TrendMicro Titanium - A New Concept in Security by Ira Wilsker
... vulnerable to new threats, but it actually is an advantage with this new product since it uses "Cloud Technology" to continuously keep the signatures updated without the need for periodic signature updates. This also acts to enhance protection since there is minimal lag time between detection of ne ...
... vulnerable to new threats, but it actually is an advantage with this new product since it uses "Cloud Technology" to continuously keep the signatures updated without the need for periodic signature updates. This also acts to enhance protection since there is minimal lag time between detection of ne ...
Appendix A-Linux_cs3
... These layers provide the human-oriented graphical user interface (GUI) that enables users to easily work with applications in the operating system and third-party applications to be installed on the operating system. There are tools and code libraries available that let application developers to mor ...
... These layers provide the human-oriented graphical user interface (GUI) that enables users to easily work with applications in the operating system and third-party applications to be installed on the operating system. There are tools and code libraries available that let application developers to mor ...
Calhoun: The NPS Institutional Archive
... provide the usual range of capabilities: memory management services, process management, UO device management, and file system services. The purpose of this paper is to examine how one of these services, a multilevel file system, can be designed to utilize the trust that has been achieved in the sec ...
... provide the usual range of capabilities: memory management services, process management, UO device management, and file system services. The purpose of this paper is to examine how one of these services, a multilevel file system, can be designed to utilize the trust that has been achieved in the sec ...
IT Security, SQL Server and You!
... Store critical data on systems located in secure rooms or datacenters. ...
... Store critical data on systems located in secure rooms or datacenters. ...
The Top Ten of Security
... • ‘Best Practices’ are recognized measures you can take to secure your computers. • If you don’t use these ‘Best Practices’ and your systems are used against someone else as in a DDOS attack, you could be liable. • Using industry Best Practices can protect you from lawsuits. ...
... • ‘Best Practices’ are recognized measures you can take to secure your computers. • If you don’t use these ‘Best Practices’ and your systems are used against someone else as in a DDOS attack, you could be liable. • Using industry Best Practices can protect you from lawsuits. ...
UNIX/LINUX
... BSD(Berkeley Software Distribution), Solaris (Sun Microsystems, and XENIX (Microsoft). ...
... BSD(Berkeley Software Distribution), Solaris (Sun Microsystems, and XENIX (Microsoft). ...
Hobby Operating System
... You essentially have a lot of freedom as a programmer, generally that includes freedom from business pressures, software politics and to a degree implementation standards if you so desire it. I also think you can make a more agile system by designing it around current architectures and components. I ...
... You essentially have a lot of freedom as a programmer, generally that includes freedom from business pressures, software politics and to a degree implementation standards if you so desire it. I also think you can make a more agile system by designing it around current architectures and components. I ...