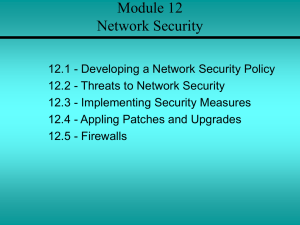
Chapter 14 Network Security
... – Key control lists no longer have to be maintained – Combinations can also be reset when needed • The one drawback to this model is that it is very easy to share a combination with someone not authorized. • Card readers are the most common of the access control mechanisms. • They work by reading a ...
... – Key control lists no longer have to be maintained – Combinations can also be reset when needed • The one drawback to this model is that it is very easy to share a combination with someone not authorized. • Card readers are the most common of the access control mechanisms. • They work by reading a ...
Operating Systems: Principles and Practice, Introduction
... – To the one that needs the least resources to complete? To the one that needs the most resources? – What if you need to allocate memory? ...
... – To the one that needs the least resources to complete? To the one that needs the most resources? – What if you need to allocate memory? ...
Operating Systems
... application program interface (API) allows the operating system to run the same application on different hardware combinations. Second, the operating system interfaces users with the computer system. The interface may be either a command line interface or a graphical user interface (GUI). An interfa ...
... application program interface (API) allows the operating system to run the same application on different hardware combinations. Second, the operating system interfaces users with the computer system. The interface may be either a command line interface or a graphical user interface (GUI). An interfa ...
pdf
... Consider the various definitions of operating system. Next, consider whether the operating system should include applications such as Web browsers and mail programs. Argue both that it should and that it should not, and support your answers. Answer: Point. Applications such as web browsers and email ...
... Consider the various definitions of operating system. Next, consider whether the operating system should include applications such as Web browsers and mail programs. Argue both that it should and that it should not, and support your answers. Answer: Point. Applications such as web browsers and email ...
Operating System
... information • UNIX: –Can be used on many computer system types and platforms • Red Hat Linux: –Can manage a cluster of up to eight servers • Mac OS X Server: ...
... information • UNIX: –Can be used on many computer system types and platforms • Red Hat Linux: –Can manage a cluster of up to eight servers • Mac OS X Server: ...
Operating System Security Fundamentals
... • Naturally leads to security risks and threats • Peer-to-peer programs: allow users to share files over the Internet • Reasons for blocking file sharing: ...
... • Naturally leads to security risks and threats • Peer-to-peer programs: allow users to share files over the Internet • Reasons for blocking file sharing: ...
Lab_1.pdf
... Introduction to Linux OS What is Linux? Linux is an operating system that was created by Linus Torvalds when he was a student at the University of Helsinki. Torvalds started Linux by writing a Kernel – the heart of the OS -, originally working with Minix, (a small UNIX system) decided to create an o ...
... Introduction to Linux OS What is Linux? Linux is an operating system that was created by Linus Torvalds when he was a student at the University of Helsinki. Torvalds started Linux by writing a Kernel – the heart of the OS -, originally working with Minix, (a small UNIX system) decided to create an o ...
Do you know someone may be watching you?
... ◦ networking and system techniques ◦ applied cryptography ◦ machine learning ◦ probability/statistics ◦ information theory ◦ graph theory ...
... ◦ networking and system techniques ◦ applied cryptography ◦ machine learning ◦ probability/statistics ◦ information theory ◦ graph theory ...
COS 598: Advanced Operating System
... What is a page fault? What happens on a page fault? Is paging good or bad? What is the size of the virtual address space for a 32 bit system? A 64-bit system? Is 2^64 a big number? Assume a system with 8 pages each of which is 1K bytes. How many bits are needed to generate addresses? What is interna ...
... What is a page fault? What happens on a page fault? Is paging good or bad? What is the size of the virtual address space for a 32 bit system? A 64-bit system? Is 2^64 a big number? Assume a system with 8 pages each of which is 1K bytes. How many bits are needed to generate addresses? What is interna ...
p2-demo1
... functionality in modules with minimal, clear, and well-defined interaction between components has two effects: • Lowering complexity with the result that fewer errors are introduced by programmers. • Malicious and faulty components can be safely limited in what they can do. The interfaces between co ...
... functionality in modules with minimal, clear, and well-defined interaction between components has two effects: • Lowering complexity with the result that fewer errors are introduced by programmers. • Malicious and faulty components can be safely limited in what they can do. The interfaces between co ...
Auditing Java Code in Eclipse - Suif
... Not a complete solution – may miss errors Some errors are hard to analyze Sources and sinks are far apart Often no source code available – only byte code Working on a complete solution Submitted a paper to Usenix Security 2005 Based on a heavy-weight sound static analysis ...
... Not a complete solution – may miss errors Some errors are hard to analyze Sources and sinks are far apart Often no source code available – only byte code Working on a complete solution Submitted a paper to Usenix Security 2005 Based on a heavy-weight sound static analysis ...
Chapter 7A Functions of Operating Systems Types of Operating
... • Windows XP – Microsoft’s newest desktop product – Different look from 2000 – Many different versions – Digital multimedia support was enhanced – Communications was enhanced – Mobile computing became a priority – Can only run on Intel machines ...
... • Windows XP – Microsoft’s newest desktop product – Different look from 2000 – Many different versions – Digital multimedia support was enhanced – Communications was enhanced – Mobile computing became a priority – Can only run on Intel machines ...
Computers: Tools for an Information Age
... Serves as intermediary between hardware and applications software Operating System Systems software Kernel ...
... Serves as intermediary between hardware and applications software Operating System Systems software Kernel ...
Chapter03 - Home - KSU Faculty Member websites
... Serves as intermediary between hardware and applications software Operating System Systems software Kernel ...
... Serves as intermediary between hardware and applications software Operating System Systems software Kernel ...
Course Introduction - Washington University in St. Louis
... Helps to develop a broadly applicable skill set ...
... Helps to develop a broadly applicable skill set ...
Operating System Security Fundamentals
... Quick Quiz ____________________ is a process that decides whether users are permitted to perform the functions they request. A. Identification B. Authentication C. Authorization D. Verification _____________________________ allows you to sign on once to a server (host machine) and then not have to ...
... Quick Quiz ____________________ is a process that decides whether users are permitted to perform the functions they request. A. Identification B. Authentication C. Authorization D. Verification _____________________________ allows you to sign on once to a server (host machine) and then not have to ...
Operating Systems
... • Linux is an operating system distributed along with its source code under the terms of a GPL (General Public License) – A Linux distribution is a download that contains the Linux kernel, system utilities, graphical user interface, applications, and an installation routine. It is free. ...
... • Linux is an operating system distributed along with its source code under the terms of a GPL (General Public License) – A Linux distribution is a download that contains the Linux kernel, system utilities, graphical user interface, applications, and an installation routine. It is free. ...
Greetings Hnoagain. D. O'Dell
... describes a software system designed to support building sophisticated, distributed applications in a network environment. The urgent need for such tools is, I believe, evidenced by the scarcity of large distributed software applications in spite of there being no shortage of large problems needing ...
... describes a software system designed to support building sophisticated, distributed applications in a network environment. The urgent need for such tools is, I believe, evidenced by the scarcity of large distributed software applications in spite of there being no shortage of large problems needing ...
PowerPoint 簡報
... captures data from information packets as they travel over the network. data may include user names, passwords, and proprietary information that travels over the network in clear text. ...
... captures data from information packets as they travel over the network. data may include user names, passwords, and proprietary information that travels over the network in clear text. ...
Assignment 3
... An open distributed system is a system that offers services according to standard rules that describe the syntax and semantics of those services. The benefits does openness provide as follow: Portability: characterizes to what extent an application developed for a distributed system A can be execute ...
... An open distributed system is a system that offers services according to standard rules that describe the syntax and semantics of those services. The benefits does openness provide as follow: Portability: characterizes to what extent an application developed for a distributed system A can be execute ...