Chapter 2 – Operating System Overview
... 1. T / F – An operating system controls the execution of applications and acts as an interface between applications and the computer hardware. 2. T / F – The operating system maintains information that can be used for billing purposes on multi-user systems. 3. T / F – The operating system typically ...
... 1. T / F – An operating system controls the execution of applications and acts as an interface between applications and the computer hardware. 2. T / F – The operating system maintains information that can be used for billing purposes on multi-user systems. 3. T / F – The operating system typically ...
Linux system
... The core Linux operating system kernel is entirely original, but it can run much existing free UNIX software, resulting in an entire UNIX-compatible operating system free from proprietary code ...
... The core Linux operating system kernel is entirely original, but it can run much existing free UNIX software, resulting in an entire UNIX-compatible operating system free from proprietary code ...
Unix – Linux
... environment that is separated from other users sharing the computer’s resources. – Access is through a verification process known as logging-in: Enter a user-id and password. – The OS creates an environment known as the “shell” for the user after the login is complete. ...
... environment that is separated from other users sharing the computer’s resources. – Access is through a verification process known as logging-in: Enter a user-id and password. – The OS creates an environment known as the “shell” for the user after the login is complete. ...
Document
... (hardware token) in addition to something you know (username + password) Over 1700 employees currently using ArchPass to access these systems ...
... (hardware token) in addition to something you know (username + password) Over 1700 employees currently using ArchPass to access these systems ...
TMDE Web Site
... Pacific since late March ’03 • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
... Pacific since late March ’03 • Stable – Infrequent minor problems have been dealt with quickly • Reliable – Site off-line briefly (< 10 minutes each occurrence) 2 times in last 6 months • Secure – Strictly follows current Navy security requirements regarding access ...
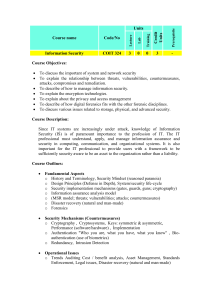
01 Computer security overview
... – Integrity — only authorized modification of data and system configuration – Availability — no denial of service, business continuity ...
... – Integrity — only authorized modification of data and system configuration – Availability — no denial of service, business continuity ...
Course name Code/No Units Credit Units Prerequisite Lecture Lab
... List some different protocol attacks to which TCP/IP is susceptible. Describe how the different protocol attacks (e.g. TCP/IP) works against an organization’s network. Give examples of shared concerns across a specified set of security domains. Give examples of concerns that are specific to specifie ...
... List some different protocol attacks to which TCP/IP is susceptible. Describe how the different protocol attacks (e.g. TCP/IP) works against an organization’s network. Give examples of shared concerns across a specified set of security domains. Give examples of concerns that are specific to specifie ...
Operating System Principle (DKT 221) Tutorial 1 1. Describe how
... 1. Describe how does kernel mode and user mode provide protection to operating system. 2. In a multiprogramming and time-sharing environment, several users share the system simultaneously. This situation can result in various security problems. a. Give two examples of the problems. b. Explain if we ...
... 1. Describe how does kernel mode and user mode provide protection to operating system. 2. In a multiprogramming and time-sharing environment, several users share the system simultaneously. This situation can result in various security problems. a. Give two examples of the problems. b. Explain if we ...
Part IV: Longer Answer: Use your knowledge of operating systems to
... 2. _______________ is a Microsoft operating systems with a graphical user interface; versions include 3.1, 95, 98, Me, NT, 2000, XP 3. _______________ is a Microsoft Windows standard for automating and simplifying the installation and configuration of device drivers after a hardware device has been ...
... 2. _______________ is a Microsoft operating systems with a graphical user interface; versions include 3.1, 95, 98, Me, NT, 2000, XP 3. _______________ is a Microsoft Windows standard for automating and simplifying the installation and configuration of device drivers after a hardware device has been ...
Chapter 1: Introduction to security
... Why is it necessary to have InfoSec? Why is it difficult to address? How does interconnectivity pose a security risk for internet users? • Why is total internet security impossible? • What can users do to secure their information? ...
... Why is it necessary to have InfoSec? Why is it difficult to address? How does interconnectivity pose a security risk for internet users? • Why is total internet security impossible? • What can users do to secure their information? ...
coms3995 - Computer Science, Columbia University
... – what exactly is shared? – what’s predictable? – what can I rely on? ...
... – what exactly is shared? – what’s predictable? – what can I rely on? ...
History of Unix OS - Seneca
... than one person to directly communicate with the computer. Although the OS can only work on one task at a time, a small piece of time (time slice) is dedicated to each task or user - this is referred to as “time-sharing”. Time sharing gives the illusion that the CPU is giving all the users its full ...
... than one person to directly communicate with the computer. Although the OS can only work on one task at a time, a small piece of time (time slice) is dedicated to each task or user - this is referred to as “time-sharing”. Time sharing gives the illusion that the CPU is giving all the users its full ...
Operating Systems EDA092, DIT400 Why study Operating Systems
... • Where there are computers, there are operating systems.... ...
... • Where there are computers, there are operating systems.... ...
Agenda - Seneca - School of Information & Communications
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
Foundations of Technology
... On back of student info survey, List at least 2 topics that are interesting to you. Briefly, explain why. These reasons may be: ...
... On back of student info survey, List at least 2 topics that are interesting to you. Briefly, explain why. These reasons may be: ...
Introduction to Database Systems
... It allows the user of computer system to use application software – email, Web, word processors language libraries, system calls Hardware resources which include, keyboard, display, memory, drives and CPU . AUI – application user interface API- application programmers interface ...
... It allows the user of computer system to use application software – email, Web, word processors language libraries, system calls Hardware resources which include, keyboard, display, memory, drives and CPU . AUI – application user interface API- application programmers interface ...
Operating Systems - Cardiff University
... – Complex design – each functionality has to be divided into parts to fit into different layers. ...
... – Complex design – each functionality has to be divided into parts to fit into different layers. ...
Security at the Operating System Level (Microsoft)
... Allows Windows 2000 users to encrypt their files and folders. Encrypting a folder encrypts all the subfolders and files in that folder. Cannot be used to encrypt system files. A user needs to know the key to decrypt a file, log-in password not enough. ...
... Allows Windows 2000 users to encrypt their files and folders. Encrypting a folder encrypts all the subfolders and files in that folder. Cannot be used to encrypt system files. A user needs to know the key to decrypt a file, log-in password not enough. ...
HIPAA Security Standards
... There are several types of firewall techniques: • Packet filter: Looks at each packet entering or leaving the network and accepts or rejects it based on user-defined rules. Packet filtering is fairly effective and transparent to users, but it is difficult to configure. In addition, it is susceptible ...
... There are several types of firewall techniques: • Packet filter: Looks at each packet entering or leaving the network and accepts or rejects it based on user-defined rules. Packet filtering is fairly effective and transparent to users, but it is difficult to configure. In addition, it is susceptible ...
Netscape: System Commander in Patagonia
... system security. Also some unsophisticated users might not understand the system enough to realize when they are doing something harmful or cause permanent damage to the installation. An educational or dual-use system must therefore protect itself from unwanted changes of state in the operating syst ...
... system security. Also some unsophisticated users might not understand the system enough to realize when they are doing something harmful or cause permanent damage to the installation. An educational or dual-use system must therefore protect itself from unwanted changes of state in the operating syst ...
Operating Systems
... Using the OS? (con’t) • When you log in to the Linux system here, a user prompt will be displayed: linux#[1]% _ ...
... Using the OS? (con’t) • When you log in to the Linux system here, a user prompt will be displayed: linux#[1]% _ ...