ws-security-framewor..
... App specific authentication messages App specific credential headers in other messages App maintains its own security domain ...
... App specific authentication messages App specific credential headers in other messages App maintains its own security domain ...
Slide 1
... • Allows a single user to work on two or more applications that reside in memory at the same time ...
... • Allows a single user to work on two or more applications that reside in memory at the same time ...
Security
... • Try modifying complex OS structures • Try to do specified DO NOTs • Convince a system programmer to add a trap door • Beg admin's sec’y to help a poor user who forgot password ...
... • Try modifying complex OS structures • Try to do specified DO NOTs • Convince a system programmer to add a trap door • Beg admin's sec’y to help a poor user who forgot password ...
Course Introduction - Department of Computer Science
... RPI2 kernel compile time: approx 90 minutes! Spend more time thinking through code before writing Huge established codebase to digest Our goal is that your “hands-on” time is similar to other courses Start early, fail early. ...
... RPI2 kernel compile time: approx 90 minutes! Spend more time thinking through code before writing Huge established codebase to digest Our goal is that your “hands-on” time is similar to other courses Start early, fail early. ...
History of Unix OS
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
... improved and distributed often Many users can spot bugs in the operating system or application if source code is “open” ...
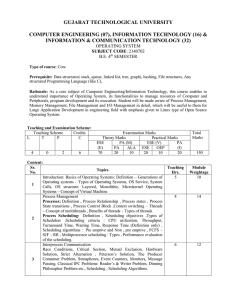
2140702
... 10. Display today’s date and time 11. Display usernames those are currently logged in the system 12. Display your name at given x, y position 13. Display your terminal number 14. Exit 15. Write a shell script to read n numbers as command arguments and sort them in descending order. 16. Write a shell ...
... 10. Display today’s date and time 11. Display usernames those are currently logged in the system 12. Display your name at given x, y position 13. Display your terminal number 14. Exit 15. Write a shell script to read n numbers as command arguments and sort them in descending order. 16. Write a shell ...
How does it get written up?
... • Who’s affected: which operating system or application, which version • What’s the threat • What do you do (including URLs if appropriate) • Basis of email distribution ...
... • Who’s affected: which operating system or application, which version • What’s the threat • What do you do (including URLs if appropriate) • Basis of email distribution ...
Windows Server 2003 security
... Blocks unused ports Allows further address or security restrictions for ports that are left open Prohibits unnecessary Internet Information Services (IIS) Web extensions, if applicable Reduces protocol exposure to server message block (SMB), NTLM, LanMan, and Lightweight Directory Access Protocol (L ...
... Blocks unused ports Allows further address or security restrictions for ports that are left open Prohibits unnecessary Internet Information Services (IIS) Web extensions, if applicable Reduces protocol exposure to server message block (SMB), NTLM, LanMan, and Lightweight Directory Access Protocol (L ...
Overview of Database Security
... Users must be prevented from tracking back to information on individual entities starting from statistical aggregated information ...
... Users must be prevented from tracking back to information on individual entities starting from statistical aggregated information ...
CH 4 – Review - WordPress.com
... Windows 8 is a major redesign that present apps on the Start Screen shown in – tiles Network operating systems support both network servers and user computers, which are referred to as – clients Multitasking involves – handling several requests at one time Network operating systems must keep data se ...
... Windows 8 is a major redesign that present apps on the Start Screen shown in – tiles Network operating systems support both network servers and user computers, which are referred to as – clients Multitasking involves – handling several requests at one time Network operating systems must keep data se ...
PPT - pantherFILE
... • If the condition is time-related, such programs could also be termed time bombs. • Some examples of logic bombs: – Introduction of a deliberate error in a program, say, by a disgruntled employee, that will result in disaster in the future — usually after the employee is gone. – A program that dele ...
... • If the condition is time-related, such programs could also be termed time bombs. • Some examples of logic bombs: – Introduction of a deliberate error in a program, say, by a disgruntled employee, that will result in disaster in the future — usually after the employee is gone. – A program that dele ...
Operating Systems - IET-DAVV
... Unit V I/O management and other issues Kernel, I/O hardware, I/O interfacing, I/O requesting and interrupts. Disk management: Disk Structure and Scheduling. Protection and Security. Linux: Kernel Organization, Process and resource management, Memory management, Introduction to Linux File System. Ove ...
... Unit V I/O management and other issues Kernel, I/O hardware, I/O interfacing, I/O requesting and interrupts. Disk management: Disk Structure and Scheduling. Protection and Security. Linux: Kernel Organization, Process and resource management, Memory management, Introduction to Linux File System. Ove ...
Security
... Antivirus and Anti-Antivirus Techniques • Integrity checkers • Behavioral checkers • Virus avoidance ...
... Antivirus and Anti-Antivirus Techniques • Integrity checkers • Behavioral checkers • Virus avoidance ...
COS 318: Operating Systems Introduction Kai Li Computer Science Department
... Pair up with a partner for project 1, 2, 3 Different partner for 4, 5 Do yourself for 6 Each project takes 2-3 weeks Design review at the end of week one All projects due Sundays 11:59pm ...
... Pair up with a partner for project 1, 2, 3 Different partner for 4, 5 Do yourself for 6 Each project takes 2-3 weeks Design review at the end of week one All projects due Sundays 11:59pm ...
Security - Glasnost
... Antivirus and Anti-Antivirus Techniques • Integrity checkers • Behavioral checkers • Virus avoidance ...
... Antivirus and Anti-Antivirus Techniques • Integrity checkers • Behavioral checkers • Virus avoidance ...
Computer Security and Penetration Testing Chapter 16 Windows
... to access resources on another domain, without being authenticated by it ...
... to access resources on another domain, without being authenticated by it ...
20121101
... • Next the attackers just sat back and digitally listened to what was going on with the system • The initial system/user didn’t have adequate access for their needs so they needed to take a step to another system to go further. ...
... • Next the attackers just sat back and digitally listened to what was going on with the system • The initial system/user didn’t have adequate access for their needs so they needed to take a step to another system to go further. ...
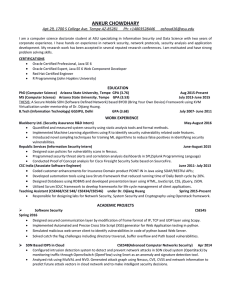
Curriculum Vitae - ASU People Search
... Designed secured communication layer by modification of frame format of IP, TCP and UDP layer using Scapy. Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of pyt ...
... Designed secured communication layer by modification of frame format of IP, TCP and UDP layer using Scapy. Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of pyt ...
Computersikkerhed
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
Rocket® Blue Zone Security Server
... access to host systems, increasing data stream privacy, and strengthening authentication. Rocket® BlueZone Security Server secures confidential information, authenticates users and reinforces network and perimeter security. ...
... access to host systems, increasing data stream privacy, and strengthening authentication. Rocket® BlueZone Security Server secures confidential information, authenticates users and reinforces network and perimeter security. ...