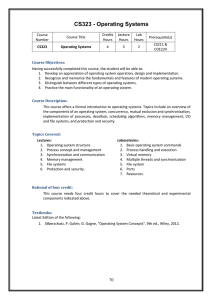
DEREE COLLEGE SYLLABUS FOR: ITC 2293 OPERATING
... The course provides a clear understanding of the fundamental concepts underlying an operating system and relates these to its function, design and evolution. It describes different operating system structural components and demonstrates how they interact to provide a range of user services and resou ...
... The course provides a clear understanding of the fundamental concepts underlying an operating system and relates these to its function, design and evolution. It describes different operating system structural components and demonstrates how they interact to provide a range of user services and resou ...
Operating systems and security
... – /bin/sh is of a type not executable from this domain • And so the buffer overflow can’t fork a shell successfully ...
... – /bin/sh is of a type not executable from this domain • And so the buffer overflow can’t fork a shell successfully ...
Linux Overview
... sure they do not interfere with one another and allowing them to share use of the CPU efficiently. • User interface: This part of the operating system is directing what you see on the screen and reacting to your key presses and other inputs. The user interface could be a basic command line interface ...
... sure they do not interfere with one another and allowing them to share use of the CPU efficiently. • User interface: This part of the operating system is directing what you see on the screen and reacting to your key presses and other inputs. The user interface could be a basic command line interface ...
Operating Systems (Linux), 27/10/08
... Architecture (arch) – a family of microprocessors that can be used to build complete and compatible(!) computer systems. ...
... Architecture (arch) – a family of microprocessors that can be used to build complete and compatible(!) computer systems. ...
Linux Concepts and key ideas
... services such as file systems, device drivers, user interfaces and system services. What is UNIX? UNIX was originally born in 1969 at Bell Labs, and grew and evolved through the years. In the early 1980s, AT&T began to market UNIX, and also distributed it free to universities. UNIX began to be used ...
... services such as file systems, device drivers, user interfaces and system services. What is UNIX? UNIX was originally born in 1969 at Bell Labs, and grew and evolved through the years. In the early 1980s, AT&T began to market UNIX, and also distributed it free to universities. UNIX began to be used ...
Introduction - Personal Web Pages
... From fun to profit (worm self-changing botnet -> target at specific systems) ...
... From fun to profit (worm self-changing botnet -> target at specific systems) ...
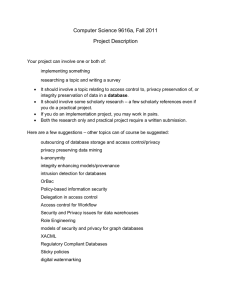
Computer Science 9616a, Fall 2011 Project Description Your project
... It should involve a topic relating to access control to, privacy preservation of, or integrity preservation of data in a database. It should involve some scholarly research – a few scholarly references even if you do a practical project. If you do an implementation project, you may work in pairs. Bo ...
... It should involve a topic relating to access control to, privacy preservation of, or integrity preservation of data in a database. It should involve some scholarly research – a few scholarly references even if you do a practical project. If you do an implementation project, you may work in pairs. Bo ...
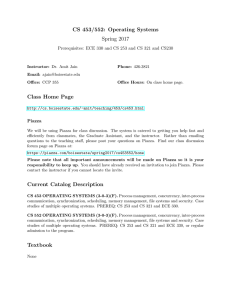
Official Syllabus
... • Shell project, part 1: basic version (2 weeks) • Shell project, part 2: custom memory manager (2 weeks) • One to two Linux kernel projects (modifying source code, rebuilding and testing) (2 weeks) • Multi-threaded project using Microsoft Windows API (2 weeks) ...
... • Shell project, part 1: basic version (2 weeks) • Shell project, part 2: custom memory manager (2 weeks) • One to two Linux kernel projects (modifying source code, rebuilding and testing) (2 weeks) • Multi-threaded project using Microsoft Windows API (2 weeks) ...
and more
... those complicated and tedious work themselves. Later, some of them released their work of collecting the software to the public. These are called “distributions”. Typically, a modern distribution handles the following: Installation of the OS Software Packaging (compiled software instead of s ...
... those complicated and tedious work themselves. Later, some of them released their work of collecting the software to the public. These are called “distributions”. Typically, a modern distribution handles the following: Installation of the OS Software Packaging (compiled software instead of s ...
secure operating system
... systems interact in a variety of ways, and the sharing of data among users is a fundamental use of computer systems. • First, the output of one process may be used by other processes. • Second With the ubiquity of Internet-scale sharing mechanisms, such as e-mail, the web, and instant messaging, use ...
... systems interact in a variety of ways, and the sharing of data among users is a fundamental use of computer systems. • First, the output of one process may be used by other processes. • Second With the ubiquity of Internet-scale sharing mechanisms, such as e-mail, the web, and instant messaging, use ...
OPERATING SYSTEMS DESIGN AND IMPLEMENTATION Third
... Feature/Kernel type Modularity Flexibility Maintainability Security Compatibility Performance ...
... Feature/Kernel type Modularity Flexibility Maintainability Security Compatibility Performance ...
Proposed Part 73 Fuel Cycle Facility Security Rulemaking
... • 10 CFR Part 73, Physical Protection of Plants and Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
... • 10 CFR Part 73, Physical Protection of Plants and Materials, has been revised subpart-by-subpart over the last 25 years • Lessons learned ((e.g., g threat and implementation)) • Commission directed engagement of a “broad” range of stakeholders ...
Review Exercise 2
... (b)IP address are the input/output locations of a computer where messages should send in or out. (c)If an IP address is analogy to a country, then the Port addresses will be analogy to the ports of that country. (d) They are all correct. (13)Which of the following is a function of operating system? ...
... (b)IP address are the input/output locations of a computer where messages should send in or out. (c)If an IP address is analogy to a country, then the Port addresses will be analogy to the ports of that country. (d) They are all correct. (13)Which of the following is a function of operating system? ...
MCS 022 Term-End Examination June, 2014
... MCS-022 : OPERATING SYSTEM CONCEPTS AND NETWORKING MANAGEMENT ...
... MCS-022 : OPERATING SYSTEM CONCEPTS AND NETWORKING MANAGEMENT ...
Security
... Service theft, unauthorized use of resources. Denial of service (DOS), prevent legitimate system use. In masquerading attack method one participant in a communication pretends to be someone else (another host or another person). Attackers breach authentication, the correctness of identification, gai ...
... Service theft, unauthorized use of resources. Denial of service (DOS), prevent legitimate system use. In masquerading attack method one participant in a communication pretends to be someone else (another host or another person). Attackers breach authentication, the correctness of identification, gai ...
Syllabus - Marwadi University
... Write a shell script to display the digits which are in odd position in a given 5 digit number in Unix / Linux / Ubuntu Write a shell script to read n numbers as command arguments and sort them in descending/ascending order. Write a shell script to check entered string is palindrome or not. Write an ...
... Write a shell script to display the digits which are in odd position in a given 5 digit number in Unix / Linux / Ubuntu Write a shell script to read n numbers as command arguments and sort them in descending/ascending order. Write a shell script to check entered string is palindrome or not. Write an ...
Section for introduction % \section{Introduction} Over the last several
... 88.6\% from the previous year \cite{Canalys11}. These phones are equipped with a rich set of hardware interfaces and software applications that allow personal and corporate users to interact with both the cyber and physical world through Internet access, email, SMS, and location-based services. To s ...
... 88.6\% from the previous year \cite{Canalys11}. These phones are equipped with a rich set of hardware interfaces and software applications that allow personal and corporate users to interact with both the cyber and physical world through Internet access, email, SMS, and location-based services. To s ...
quiz1-s3
... Turn off interrupts. d) Access I/O device. 2. Which of the following would lead you to believe that a given system is an SMP-type system? a) Each processor is assigned a specific task. b) There is a boss–worker relationship between the processors. c) Each processor performs all tasks within the oper ...
... Turn off interrupts. d) Access I/O device. 2. Which of the following would lead you to believe that a given system is an SMP-type system? a) Each processor is assigned a specific task. b) There is a boss–worker relationship between the processors. c) Each processor performs all tasks within the oper ...
Operating Systems CSLO - Barbara Hecker
... writing and cannot include portions cut-n-pasted from the internet or other sources. Topic selections: (Select one) 1. What is an operating system? What functions does an operating system provide? Provide an overview of the history and evolution of operating systems. Discuss the various different ha ...
... writing and cannot include portions cut-n-pasted from the internet or other sources. Topic selections: (Select one) 1. What is an operating system? What functions does an operating system provide? Provide an overview of the history and evolution of operating systems. Discuss the various different ha ...
Fundamentals of Computer Security
... Add an additional layer of software that runs on top of the existing system to provide the new services Redesign the system so that the new services can be executed more efficiently in the kernel mode ...
... Add an additional layer of software that runs on top of the existing system to provide the new services Redesign the system so that the new services can be executed more efficiently in the kernel mode ...
Module3 - ITProGuru Blog
... Dan Stolts, Chief Technology Strategist Twitter: @ITProGuru Blog: http://ITProGuru #InnovateIT ...
... Dan Stolts, Chief Technology Strategist Twitter: @ITProGuru Blog: http://ITProGuru #InnovateIT ...