* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Foundations of Information Security Webcast - ABA
Post-quantum cryptography wikipedia , lookup
Next-Generation Secure Computing Base wikipedia , lookup
Wireless security wikipedia , lookup
Unix security wikipedia , lookup
Computer and network surveillance wikipedia , lookup
Airport security wikipedia , lookup
IT risk management wikipedia , lookup
Mobile security wikipedia , lookup
Security printing wikipedia , lookup
Distributed firewall wikipedia , lookup
Information security wikipedia , lookup
Cyber-security regulation wikipedia , lookup
Cybercrime countermeasures wikipedia , lookup
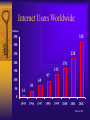
ABA WEBCAST BRIEFING Foundations of Information Security Presented by: Peter S. Browne Principal Manager Peter Browne & Associates, LLC Projected B2B eCommerce Growth 2004 Predictions In Billions $8,000 Gartner $7,000 7.3 Trillion $6,000 Forrester 6.3 Trillion $5,000 Goldman $4,000 3.2 Trillion $3,000 emarketer $2,000 2.8 Trillion $1,000 Ovum $0 2001 1.4 Trillion 2002 2003 2004 Internet Users Worldwide (Millions) 350 320 300 228 250 200 170 132 150 97 100 50 69 14 38 0 1995 1996 1997 1998 1999 2000 2001 2002 Source: IDC Risk Management In Perspective - Drivers New Technologies – Web presence – Online transactions – Delivery of professional services via the Internet New Risks – Cyber-extortion – Network security breaches – Litigation – Loss of “intangible” information Dependence on third party service providers The Problem 85% of Companies report at least one Computer Security Breaches last year 90% report Vandalism attacks 78% report Denial of Service attacks 64% Acknowledged financial losses due to these attacks Average loss: $2,000,000 – Melissa = $80 million total – Denial of Service (Mafia Boy) = $1.2 billion – Love Bug - $10 billion Statistical data provided by CSI/FBI 2001 report The Computer Attack Risks Loss or damage to Data Legal Liability to Others Loss or damage to Reputation Loss of Market capitalization and resulting Shareholder lawsuits Foundations Managing risk includes the following components: – Accept – Mitigate – Transfer a portion of the risk to an insurance underwriter Electronic Commerce: A Paradigm Shift Traditional Commerce Centralized systems in glass house Economy of scale Managed risk Security says NO Electronic Commerce Distributed systems everywhere Economy of dispersion Distributed risk Security is an enabler Business Drivers for Security The effect of the Internet on banking and financial services Movement from information “silos” to information integration Holistic view of risk management Increasing global regulatory oversight – Effect of GLBA – Increasingly proactive regulatory agencies and audits More pervasive and complex technologies The Four Foundations of Protection People – Board and management commitment, dedicated technical personnel, crisis management team all in place and active! Process – Enterprise ISO7799 ready, on-going management, employee education and regular training, patch management. Technology – Monitoring/log review, DMZ zones, firewall, anti-virus software, intrusion detection systems, remote access two factor authentication, audit trails. The Overriding Objective Security should be at the table whenever the technology or the business strategy changes, whether the technology is managed in-house or it is outsourced to third parties 11 People Success Factors 1. Set up the right organization Organizational Placement of IT Security Report separately from IT (Audit, Security, Legal, Finance) Report directly to CIO/Head of Technology Report into CTO/Operations Part time function Split function Roles and Responsibilities Set policy/standards/guidance Act as internal consultant Perform system/security operations Provide oversight over outsourced/third party technology providers Conduct/manage assessments and audits Ownership What to centralize: – Policy, standards, guidance – Test and validation of security – Cross-enterprise coordination – System-wide administration What to decentralize: – Accountability – Risk acceptance – User access administration People Success Factors 1. Set up the right organization 2. Get good people and train them adequately Security Must Add Value Facilitate, don’t obfuscate Be a perpetual student Provide solutions to business needs Communicate, communicate, communicate Be an agent of change Focus on operational excellence Treat risk as part of the business equation Clearly articulate what is expected What Is the Scope? Make security enterprise-wide… and coordinated with all business units Focus early in the product/software life cycle Enlist allies: – – – – Business units Legal Operations Risk management Earn your budget! Preach Security Awareness Educated management Understand risk – To the enterprise – To the given business – To the individual Application of security standards – In the software development life cycle – In the management of platforms People Success Factors 1. Set up the right organization 2. Get the good people and train them adequately 3. Get management commitment Articulate Risk in Business Terms Value of the asset Probability of a loss Probability of Occurrence Likely cost over time 0 Value of Fraud Control Analogy: ATM versus Internet Known and limited number of customer entry points Two-factor authentication required (card plus PIN) Camera recording all activity Limited amount of cash available for withdrawal Full audit trail of all activity Physical limits to bulk fraud Customer cannot stop an initiated transaction Settlement and problem resolution processes in place Customer has receipt to verify transaction ATM Internet Yes No Yes No Yes No Yes Maybe Yes Maybe Yes No Yes No Yes Maybe Yes Maybe Management Involvement Top-level steering committee Task force Advisory board Reporting key performance indicators Reporting incidents Compliance checking Process Success Factors 1. Put policy and standards in place Security Life Cycle Steps Ensure compliance with standards Implement guidelines on systems Translate standards into security guidelines Develop and document "baseline" security standard Update policies Assess current security state Top-level Policy Policy Standards Guidelines Procedures Practice Broad statement of intent Sets the expectations for compliance Must acknowledge individual accountability Culture-dependent Must cover appropriate use Must be enforced Standards Policy Standards Guidelines Procedures Practice Describe what to do, not how to do it Explain the application of policy Cover all elements of information security Use existing models (I4 & ISF) Provide the cornerstone for compliance Guidelines Policy Standards Guidelines Procedures Tell how to meet standards Are platform- or technology-specific Provide examples and configuration recommendations Must be kept up to date Practice Process Success Factors 1. Put policy and standards in place 2. Build a robust program Desired State of Security Desired state of security: The level of security controls needs to correspond to the value/sensitivity of the underlying information asset: “risk-based” Security must: – – – – Be incorporated into the development process Be part of the overall architecture Be part of the project management and implementation process Be part of system administrators’ and network planners’ job function – Keep current with technologies because they evolve rapidly. What worked yesterday may not be valuable today (digital certificates, application proxy firewalls, biometrics, IDS) Process Success Factors 1. Put policy and standards in place 2. Build a robust program 3. Track metrics for accountability Platform Compliance Average Percent Compliance to Guidelines 97% 95% 93%93% 98% 96% 94% 90% 90%90%90%90% 92% 90% 88% 89% 86% DEC 86% 84% 82% 80% Compliance Score Jul-98 Aug-98 Goal Sep-98 Oct-98 Nov-98 Dec-98 Security Awareness Month Score Goal Dec Nov Oct Sep Aug Jul Jun May Apr Mar Feb 10 8 6 4 2 0 Jan Average Score on Scale of 1 10 Security Awareness Survey Results Operational Statistics 90% 91% 86% 86% 100% 88% 88% 91% 90% 79% 2,500 2,000 89% 74% 80% 81% 78% 70% 60% 1,500 50% 40% 1,000 30% 20% 500 10% - Month # of rqsts % comp w/in 24 hrs Dec Nov Oct Sept August July June May April March February 0% Percent of requests completed within 24 hours 3,000 January Number of requests Service Level Agreement = 90% of all requests completed within 24 hours Technology Success Factors 1. Protect the perimeter Perimeter Control Firewall technology in place to protect Concept of a DMZ Intrusion Detection – Network based – Host based Standardized system configuration Middleware Call Center AOL Internet Tandem Web Servers Third Party ATM Nets Kiosks VRU Hosts (system of record) Vendors Middleware Home Phone PFM PFM Network Bank Systems Vendors Technology Success Factors 1. Protect the perimeter 2. Provide consistent security services Consistent Security Services Remote access authentication and authorization – Remote dial in access – Internet access – Business to business links System management – Lockdown of access – File protection – Security patches Technology Success Factors 1. Protect the perimeter 2. Provide consistent security services 3. Capture audit data Audit Trails What to capture – All access to systems – All intrusion attempts – Financial transactions – Access to sensitive data Uses – Digital forensics – Monitoring of security – Improving performance Information Security as the Foundation for Electronic Commerce The people are the critical components, but they must be supported by management and trained The process starts with the policy, and concludes with implementation The technology must be put in place to manage and enforce security Management commitment is not difficult… if Metrics: If you can’t measure it, you can’t control it Information security bridges the business and the technology The Future In the future, there’ll be just two kinds of banks — the ones on the Internet and the ones who never saw it coming.