Security - UTRGV Faculty Web
... Christopher Padilla Computer & Communications Industry Association ...
... Christopher Padilla Computer & Communications Industry Association ...
6.01 RCNET Module
... Access Points - is a networking hardware device that allows a device to connect to a network. In the sentence, “Conduct a physical security survey and inventory access points at each facility that has a connection to the SCADA system”, refers to any point where a hardware device connects to the SCAD ...
... Access Points - is a networking hardware device that allows a device to connect to a network. In the sentence, “Conduct a physical security survey and inventory access points at each facility that has a connection to the SCADA system”, refers to any point where a hardware device connects to the SCAD ...
Srini Devadas, MIT Computer Science and Artificial Intelligence Lab
... similar to performance and energy • Attackers take a holistic view by attacking any component or interface of system • Diverse threat models dictate different desirable security properties – Viruses and worms: Bug-free programs – Denial-of-Service attacks: Redundant resources – Cyberphysical attacks ...
... similar to performance and energy • Attackers take a holistic view by attacking any component or interface of system • Diverse threat models dictate different desirable security properties – Viruses and worms: Bug-free programs – Denial-of-Service attacks: Redundant resources – Cyberphysical attacks ...
The Need for Information Security
... • Electronic theft is more complex problem; evidence of crime not readily apparent ...
... • Electronic theft is more complex problem; evidence of crime not readily apparent ...
PowerPoint 簡報
... know of holes within systems and the reasons for such holes. Hackers constantly seek further knowledge, freely share what they have discovered, and never, ever intentionally damage data. ...
... know of holes within systems and the reasons for such holes. Hackers constantly seek further knowledge, freely share what they have discovered, and never, ever intentionally damage data. ...
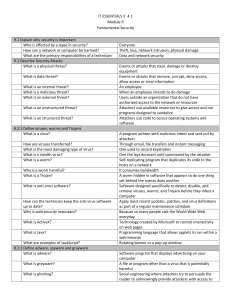
IT ESSENTIALS V. 4.1 Module 9 Fundamental Security 9.1 Explain
... authorized access to the network or resources Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instan ...
... authorized access to the network or resources Attackers use available resources to give access and run programs designed to vandalize Attackers use code to access operating systems and software A program written with malicious intent and sent out by attackers Through email, file transfers and instan ...
Do you know someone may be watching you?
... sources that are hacking into your system by using various techniques in computer science and mathematics. ...
... sources that are hacking into your system by using various techniques in computer science and mathematics. ...
Cyber attack! Could you run services without IT for a week?
... attachment to email (zip file) at about 9.30am • The incident was not reported until 12mid day • Increased activity on network file stores was identified and the true severity of the incident was recognised • The IT systems were shutdown to prevent damage whilst the precise nature of the threat and ...
... attachment to email (zip file) at about 9.30am • The incident was not reported until 12mid day • Increased activity on network file stores was identified and the true severity of the incident was recognised • The IT systems were shutdown to prevent damage whilst the precise nature of the threat and ...
Data Mining BS/MS Project
... • X. Yan. “Early Detection of Cyber Security Threats using Structured Behavior Modeling”. ACM Transactions on Information and System Security, Vol. V, No. N. 2013. ...
... • X. Yan. “Early Detection of Cyber Security Threats using Structured Behavior Modeling”. ACM Transactions on Information and System Security, Vol. V, No. N. 2013. ...
Powerpoint with iClicker Questions
... Nachi was written to clean up damage caused by the Blaster worm, but it got out of control See link Ch 3j ...
... Nachi was written to clean up damage caused by the Blaster worm, but it got out of control See link Ch 3j ...
Responding to Intrusions
... limited to eavesdropping, identity spoofing, sniffer attacks, password-based attacks, and brute force attacks. In detail, eavesdropping is the collecting of data that passes between two active nodes on a network. Identity spoofing, aka IP address spoofing, occurs when an attacker assumes the source ...
... limited to eavesdropping, identity spoofing, sniffer attacks, password-based attacks, and brute force attacks. In detail, eavesdropping is the collecting of data that passes between two active nodes on a network. Identity spoofing, aka IP address spoofing, occurs when an attacker assumes the source ...
Computer Concepts And Applications CIS-107-TE
... a. physical authentication b. token authentication c. dynamic biometrics d. static biometrics 16. A password ________ is a password guessing program. a. hash b. biometric c. cracker d. key 17. Computers as ________ is a form of crime that focuses on a computer system to acquire information stored on ...
... a. physical authentication b. token authentication c. dynamic biometrics d. static biometrics 16. A password ________ is a password guessing program. a. hash b. biometric c. cracker d. key 17. Computers as ________ is a form of crime that focuses on a computer system to acquire information stored on ...
Glenbriar TakeStock! - Glenbriar Technologies Inc.
... distribute Deep-Secure products within Canada Products may be sold on stand-alone basis or incorporated within Glenbriar’s existing products and services ...
... distribute Deep-Secure products within Canada Products may be sold on stand-alone basis or incorporated within Glenbriar’s existing products and services ...
Research Scientist – Prague, Czech Republic Cisco Systems
... Cisco Systems, Security Cloud Operations (SCO) develops innovative products in the domain of Network Behavior Analysis (NBA) in order to fight against modern sophisticated attacks in today's cyberspace which include Advanced Persistent Threats (APT), exploit kits, zero-day attacks, polymorphic malwa ...
... Cisco Systems, Security Cloud Operations (SCO) develops innovative products in the domain of Network Behavior Analysis (NBA) in order to fight against modern sophisticated attacks in today's cyberspace which include Advanced Persistent Threats (APT), exploit kits, zero-day attacks, polymorphic malwa ...
OWN YOUR SPACE
... Never open attachments to emails of unknown origin. Be careful of e-mail from people you do know. Some attacks appear to come from people you know. Some worms resend themselves to every person in a victims ...
... Never open attachments to emails of unknown origin. Be careful of e-mail from people you do know. Some attacks appear to come from people you know. Some worms resend themselves to every person in a victims ...
King Saud University College of Computer and Information Sciences
... 5. The guidelines for the morally acceptable use of computers in society are a) computer ethics b) privacy c) morality d) legal systems 6. The issues that deal with the collection and use of data about individuals is a) access ...
... 5. The guidelines for the morally acceptable use of computers in society are a) computer ethics b) privacy c) morality d) legal systems 6. The issues that deal with the collection and use of data about individuals is a) access ...
INTRODUCTION TO INFORMATION SYSTEMS TECHNOLOGY
... NewContoso Inc. network security (cont.) A third malware called SpySheriff disguises itself as an antispyware program, in order to trick the user of the infected computer to buy the program, by repeatedly informing them of false threats to their system. SpySheriff often goes unnoticed by actual ant ...
... NewContoso Inc. network security (cont.) A third malware called SpySheriff disguises itself as an antispyware program, in order to trick the user of the infected computer to buy the program, by repeatedly informing them of false threats to their system. SpySheriff often goes unnoticed by actual ant ...
Networking and System Administration (NaSA) Bachelor of Science in
... The Networking and System Administration major is a timely program aimed at preparing graduates for careers and research opportunities in all fields related to reliable and distributed network computing. Career Paths Include: ...
... The Networking and System Administration major is a timely program aimed at preparing graduates for careers and research opportunities in all fields related to reliable and distributed network computing. Career Paths Include: ...
Introduction - Personal Web Pages
... • Use social network to detect disease breakout • Code during the war – Navajo Code in WWII ...
... • Use social network to detect disease breakout • Code during the war – Navajo Code in WWII ...
Phishing and whaling – Don`t get hooked!
... So how can your organisation stay safe? There is no guaranteed checklist but the following are some key protection measures: 1. Awareness training – Ensure everyone in your team is made aware of the risks. The more people are aware of the dangers, the less likelihood of being fooled by such attacks ...
... So how can your organisation stay safe? There is no guaranteed checklist but the following are some key protection measures: 1. Awareness training – Ensure everyone in your team is made aware of the risks. The more people are aware of the dangers, the less likelihood of being fooled by such attacks ...
NetDay Cyber Security Kit for Schools
... that these records be protected from unauthorized release. As districts begin to store confidential data electronically, these same laws apply – so electronic data security should be a top priority for administrators. 1. Network Security – The guidelines and recommendation above are a very big part ...
... that these records be protected from unauthorized release. As districts begin to store confidential data electronically, these same laws apply – so electronic data security should be a top priority for administrators. 1. Network Security – The guidelines and recommendation above are a very big part ...
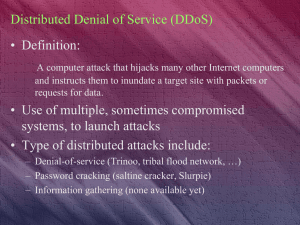
Crime and Security in the Networked Economy Part 4
... Plain Text LetÕ s meet at 11pm at the regular place ...
... Plain Text LetÕ s meet at 11pm at the regular place ...
ITS_8_Security Vocab Answers
... that the legitimate organization already has. The Web site, however, is fake and set up only to steal enough additional user information to allow the scammer to complete the identity theft. Denial of Service A type of computer attack on a network that is designed to bring the network to its down by ...
... that the legitimate organization already has. The Web site, however, is fake and set up only to steal enough additional user information to allow the scammer to complete the identity theft. Denial of Service A type of computer attack on a network that is designed to bring the network to its down by ...
Victims who were Hacked PowerPoint Presentation
... What Is An Anti-Virus Software? A software designed to be used on your computer to find, treat, remove and keep malwares away. It will keep all your computer data safe! ...
... What Is An Anti-Virus Software? A software designed to be used on your computer to find, treat, remove and keep malwares away. It will keep all your computer data safe! ...