20121101
... • Next the attackers just sat back and digitally listened to what was going on with the system • The initial system/user didn’t have adequate access for their needs so they needed to take a step to another system to go further. ...
... • Next the attackers just sat back and digitally listened to what was going on with the system • The initial system/user didn’t have adequate access for their needs so they needed to take a step to another system to go further. ...
Malware - UTK-EECS
... A worm is a piece of malware that, like a virus, replicates itself to spread to other systems. The difference between a worm and a virus is that a worm doesn’t need to inject into an existing program to be executed. Worms can have payloads, such as installing backdoors to create zombie machines for ...
... A worm is a piece of malware that, like a virus, replicates itself to spread to other systems. The difference between a worm and a virus is that a worm doesn’t need to inject into an existing program to be executed. Worms can have payloads, such as installing backdoors to create zombie machines for ...
PPT - pantherFILE
... – documents (whose loading is likely to cause embedded code execution at some point) – even additionally hide elsewhere in the operating system, including the kernel. ...
... – documents (whose loading is likely to cause embedded code execution at some point) – even additionally hide elsewhere in the operating system, including the kernel. ...
Safeguarding of Unclassified Controlled Technical Information (UCTI)
... Contractors that don’t have all of the NIST controls implemented must submit a written explanation of how 1) the required security control(s) is not applicable, or 2) an alternative control or protective measure is used to achieve equivalent protection. This means all 51 controls must be addressed, ...
... Contractors that don’t have all of the NIST controls implemented must submit a written explanation of how 1) the required security control(s) is not applicable, or 2) an alternative control or protective measure is used to achieve equivalent protection. This means all 51 controls must be addressed, ...
Security and Ethical Challenges
... Hacking into a computer system and reading files, but neither stealing nor damaging anything Cracker A malicious or criminal hacker who maintains knowledge of vulnerabilities found for private advantage ...
... Hacking into a computer system and reading files, but neither stealing nor damaging anything Cracker A malicious or criminal hacker who maintains knowledge of vulnerabilities found for private advantage ...
CS 494/594 Computer and Network Security - UTK-EECS
... • Worm: a program that replicates itself on other machines across a network • Trapdoor: an undocumented entry point in a program • Logic bomb: malicious instructions that trigger on some event in the future • Zombie: malicious instructions on comprised machines that are used to launch attacks • Spyw ...
... • Worm: a program that replicates itself on other machines across a network • Trapdoor: an undocumented entry point in a program • Logic bomb: malicious instructions that trigger on some event in the future • Zombie: malicious instructions on comprised machines that are used to launch attacks • Spyw ...
CS 494/594 Computer and Network Security - UTK-EECS
... • Worm: a program that replicates itself on other machines across a network • Trapdoor: an undocumented entry point in a program • Logic bomb: malicious instructions that trigger on some event in the future • Zombie: malicious instructions on comprised machines that are used to launch attacks • Spyw ...
... • Worm: a program that replicates itself on other machines across a network • Trapdoor: an undocumented entry point in a program • Logic bomb: malicious instructions that trigger on some event in the future • Zombie: malicious instructions on comprised machines that are used to launch attacks • Spyw ...
Seminar Announcement - CS/NVC Home
... queries are useful in many application domains, including Network Management and Intrusion Detection, Web Monitoring, Sensor Network applications, and various financial and business applications. In this talk, we will first briefly discuss some of these applications and general technical challenges ...
... queries are useful in many application domains, including Network Management and Intrusion Detection, Web Monitoring, Sensor Network applications, and various financial and business applications. In this talk, we will first briefly discuss some of these applications and general technical challenges ...
Attacks and Mitigations
... get in. That's just the first step. Worms usually carry an installer for malware, such as spyware or botware as their payload. The worm's work is done when the payload is installed and running on the computer. ...
... get in. That's just the first step. Worms usually carry an installer for malware, such as spyware or botware as their payload. The worm's work is done when the payload is installed and running on the computer. ...
Hacker Ethics presentation
... The hackers should share information with others within the group. They cannot brag, expose their knowledge to the outside world, spy on users, or trash systems. ...
... The hackers should share information with others within the group. They cannot brag, expose their knowledge to the outside world, spy on users, or trash systems. ...
Computersikkerhed
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
... Denial of Service Distributed Denial of Service Threats in Active or Mobile Code Complex Attacks ...
Chapter 5 Protecting Information Resources
... existence exceeded one million Consists of self-propagating program code that’s triggered by a specified time or event Seriousness of viruses varies Transmitted through a network & e-mail attachments Indications of a computer infected by a virus Best measure against viruses ◦ Installing and updating ...
... existence exceeded one million Consists of self-propagating program code that’s triggered by a specified time or event Seriousness of viruses varies Transmitted through a network & e-mail attachments Indications of a computer infected by a virus Best measure against viruses ◦ Installing and updating ...
Cyber insurance market set to reach $7.5 billion in annual
... “Many insurers and reinsurers are looking to take advantage of what they see as a rare opportunity to secure high margins in an otherwise soft market,” Mr Britten said. “Yet many others may still be wary of cyber risk due to limited historic data and the challenges in evaluating and pricing the risk ...
... “Many insurers and reinsurers are looking to take advantage of what they see as a rare opportunity to secure high margins in an otherwise soft market,” Mr Britten said. “Yet many others may still be wary of cyber risk due to limited historic data and the challenges in evaluating and pricing the risk ...
Marine Center for Advanced Operational Culture Training
... Allen Corporation of America has won, as a subcontractor to Corps Solutions, a base plus four-year contract to support the Center for Advanced Operational Culture Learning (CAOCL). CAOCL is a directorate within the United States Marine Corps Training and Education Command (TECOM) located at Quantico ...
... Allen Corporation of America has won, as a subcontractor to Corps Solutions, a base plus four-year contract to support the Center for Advanced Operational Culture Learning (CAOCL). CAOCL is a directorate within the United States Marine Corps Training and Education Command (TECOM) located at Quantico ...
Presentation
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
... Crack- (1) To break into a computer system. The term was coined in the mid-80s by hackers who wanted to differentiate themselves from individuals whose sole purpose is to sneak through security systems. Whereas crackers sole aim is to break into secure systems, hackers are more interested in gaini ...
Intrusion Detection Systems
... exhaustive list. For example, an attack on an authentication service by trying all possible passwords; or an attack on encryption by encrypting some known plaintext phrase with all possible keys so that the key for any given encrypted message containing that phrase may be obtained by lookup. ...
... exhaustive list. For example, an attack on an authentication service by trying all possible passwords; or an attack on encryption by encrypting some known plaintext phrase with all possible keys so that the key for any given encrypted message containing that phrase may be obtained by lookup. ...
Phoenix SIEM (Security Information and Event
... organizations I have worked for include BAE Systems, Rapid 7 and 3M. At BAE Systems I worked with NetReveal and Vuma, at Rapid 7 I worked with Nexpose and Metasploit, ...
... organizations I have worked for include BAE Systems, Rapid 7 and 3M. At BAE Systems I worked with NetReveal and Vuma, at Rapid 7 I worked with Nexpose and Metasploit, ...
Darktrace Case Study: Trek, Leading US Bicycle Retailer
... designs of paramount importance. It is vital that the company’s unique products and specific research developments are secure in order for Trek to remain at the forefront of its industry. With a global customer base, the company is also responsible for a large amount of customer data. As such, it wa ...
... designs of paramount importance. It is vital that the company’s unique products and specific research developments are secure in order for Trek to remain at the forefront of its industry. With a global customer base, the company is also responsible for a large amount of customer data. As such, it wa ...
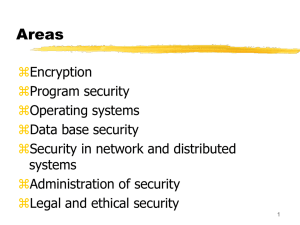
Chapter 1: Security Problems in Computing
... discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time commerce. It has also facilitated a lot of mischief. The first section of the first chapte ...
... discovered the operating system and allowed more than one programmer at a time access to the same computer. Easier access to computers has facilitated much of modern commerce, including e-mail and just-in-time commerce. It has also facilitated a lot of mischief. The first section of the first chapte ...
Internet Techniques
... technologies. Streaming and real-time protocols (RTP, RTCP, RTSP). Multicast (applications, technologies, protocols (PIM)). QoS (models, protocols, technologies). MPLS. Internet security aspects. Intrusion Detection Systems. Anomaly Detection Systems. SSO/AAI techniques. Introduction to IMS. Cyber t ...
... technologies. Streaming and real-time protocols (RTP, RTCP, RTSP). Multicast (applications, technologies, protocols (PIM)). QoS (models, protocols, technologies). MPLS. Internet security aspects. Intrusion Detection Systems. Anomaly Detection Systems. SSO/AAI techniques. Introduction to IMS. Cyber t ...
Information Systems and Networks
... viruses spread like their biological counterparts by infecting other files when human take an action such as sending an email attachment or copying an infected file ...
... viruses spread like their biological counterparts by infecting other files when human take an action such as sending an email attachment or copying an infected file ...
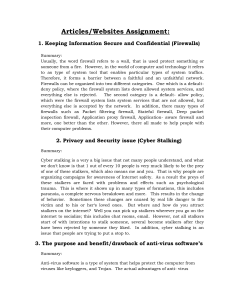
File
... victim and to his or her‘s loved ones. But where and how do you attract stalkers on the internet? Well you can pick up stalkers wherever you go on the internet to socialize; this includes chat rooms, email. However, not all stalkers start of with intentions to stalk someone, several become stalkers ...
... victim and to his or her‘s loved ones. But where and how do you attract stalkers on the internet? Well you can pick up stalkers wherever you go on the internet to socialize; this includes chat rooms, email. However, not all stalkers start of with intentions to stalk someone, several become stalkers ...