File
... protect them.They are feel that no one can break their security in the computer. Some dial-up users have victims of major attacks and they lost their files and also a lots of work. ...
... protect them.They are feel that no one can break their security in the computer. Some dial-up users have victims of major attacks and they lost their files and also a lots of work. ...
Monitoring and Auditing AIS - McGraw
... • To ensure the integrity of the system • To control the flow of multiprogramming and tasks of scheduling in the computer • To allocate computer resources to users and applications • To manage the interfaces with the computer ...
... • To ensure the integrity of the system • To control the flow of multiprogramming and tasks of scheduling in the computer • To allocate computer resources to users and applications • To manage the interfaces with the computer ...
Hackers and Attackers
... systems used to control and monitor industrial processes • It is also first known worm to target critical industrial infrastructure • According to news reports infestation by this worm might have damaged Iran's nuclear facilities in Natanz • It has infected computers in China, Iran, Indonesia, India ...
... systems used to control and monitor industrial processes • It is also first known worm to target critical industrial infrastructure • According to news reports infestation by this worm might have damaged Iran's nuclear facilities in Natanz • It has infected computers in China, Iran, Indonesia, India ...
01-Intro
... Saphire worm) Trojan Horse - instructions in an otherwise good program that cause bad things to happen (sending your data or password to an attacker over the net). Logic Bomb - malicious code that activates on an event (e.g., date). ...
... Saphire worm) Trojan Horse - instructions in an otherwise good program that cause bad things to happen (sending your data or password to an attacker over the net). Logic Bomb - malicious code that activates on an event (e.g., date). ...
Leaders` Forum, March 16, 2006 - University of Western Ontario
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
... – Implements and supports the ‘many layers’ of protection – Monitors network activity for anomalies and deals with problems – Responds to security incidents or calls for help – Makes new tools available to campus • ITS Computer Wellness Clinics – Laptops and computers may be brought to the clinic to ...
Part 1
... Program that travels independently over computer networks, seeking uninfected sites Replicates and starts up thousands of processes Overloads a system ...
... Program that travels independently over computer networks, seeking uninfected sites Replicates and starts up thousands of processes Overloads a system ...
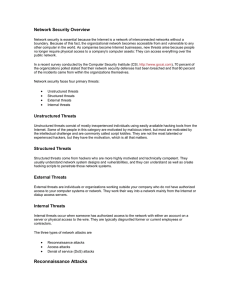
Network Security Overview
... everyone. The intruder has no problem getting to the files. More often than not, the easily accessible information is highly confidential and completely unprotected from prying eyes, especially if the attacker is already an internal user. System access is an intruder's ability to gain access to a ma ...
... everyone. The intruder has no problem getting to the files. More often than not, the easily accessible information is highly confidential and completely unprotected from prying eyes, especially if the attacker is already an internal user. System access is an intruder's ability to gain access to a ma ...
Slides - TAMU Computer Science Faculty Pages
... • “…the Storm cluster has the equivalent of one to 10 million 2.8 GHz Pentium 4 processors with one to 10 million petabytes worth of RAM. ... To put the size of a petabyte into perspective, Google, as of Aug. 2007, uses between 20 and 200 petabytes of disk space,according to Wikipedia.com. In compar ...
... • “…the Storm cluster has the equivalent of one to 10 million 2.8 GHz Pentium 4 processors with one to 10 million petabytes worth of RAM. ... To put the size of a petabyte into perspective, Google, as of Aug. 2007, uses between 20 and 200 petabytes of disk space,according to Wikipedia.com. In compar ...
Jaden Terry CIS 280 Final Network Security From browsing the
... these cyber attacks and the proper functioning of any given computer falls back on network security. There are many types of attacks that a hacker could exploit to break into a system. Some of these include: spoofing, denial of service, buffer overflow, wiretapping, and port scanning. Wiretapping is ...
... these cyber attacks and the proper functioning of any given computer falls back on network security. There are many types of attacks that a hacker could exploit to break into a system. Some of these include: spoofing, denial of service, buffer overflow, wiretapping, and port scanning. Wiretapping is ...
Cisco 642-552
... Internet outlaw's botnet in just a few minutes. A firewall can block malware that could otherwise scan your computer for vulnerabilities and then try to break in at a weak point. The real issue is how to make one 99.9% secure when it is connected to in Internet. At a minimum computers need to have f ...
... Internet outlaw's botnet in just a few minutes. A firewall can block malware that could otherwise scan your computer for vulnerabilities and then try to break in at a weak point. The real issue is how to make one 99.9% secure when it is connected to in Internet. At a minimum computers need to have f ...
How medical device companies can safeguard
... The IP Commission estimates that China is responsible for 50-80% of international IP theft, and is the No. 1 perpetrator of cyber attacks designed to steal IP. One reason is that China’s industrial policy goals encourage IP theft, and an extraordinary number of Chinese business and government entiti ...
... The IP Commission estimates that China is responsible for 50-80% of international IP theft, and is the No. 1 perpetrator of cyber attacks designed to steal IP. One reason is that China’s industrial policy goals encourage IP theft, and an extraordinary number of Chinese business and government entiti ...
Intrusion Detection Prevention Systems
... on application content, rather than IP address or ports as traditional firewalls had done. • Because IDS and IPS technologies offer many of the same capabilities, administrators can usually disable prevention features in IPS products, causing them to function as IDSs. ...
... on application content, rather than IP address or ports as traditional firewalls had done. • Because IDS and IPS technologies offer many of the same capabilities, administrators can usually disable prevention features in IPS products, causing them to function as IDSs. ...
Homeland Security
... the Department and our highest priority •The Department's efforts to battle terrorism, •detecting explosives in public spaces and transportation networks • helping protect critical infrastructure and cyber networks from attack •detecting agents of biological warfare ...
... the Department and our highest priority •The Department's efforts to battle terrorism, •detecting explosives in public spaces and transportation networks • helping protect critical infrastructure and cyber networks from attack •detecting agents of biological warfare ...
Making your Enterprise Cyber Resilient
... to fail, with adverse consequences such as being unable to communicate with customers, generate transactions or conduct billing. Operational risks also impact brand and reputation, leading to the potential for losses in intangible value as well as actual sales and revenue. ...
... to fail, with adverse consequences such as being unable to communicate with customers, generate transactions or conduct billing. Operational risks also impact brand and reputation, leading to the potential for losses in intangible value as well as actual sales and revenue. ...
chapter 3
... Prolexic: ‘itsoknoproblembro’ DDoS attacks are highly sophisticated. Experts from Prolexic Technologies claim a new type of distributed denial-of-service (DDoS) attack has not only increased in size, but also reached a new level of sophistication. DDoS attacks have recently caused a lot of problems ...
... Prolexic: ‘itsoknoproblembro’ DDoS attacks are highly sophisticated. Experts from Prolexic Technologies claim a new type of distributed denial-of-service (DDoS) attack has not only increased in size, but also reached a new level of sophistication. DDoS attacks have recently caused a lot of problems ...
NITC yearly Work Plan FY2065/66
... When an individual or group designs software to attack systems, they create malicious code/software called malware Designed to damage, destroy, or deny service to the target systems ...
... When an individual or group designs software to attack systems, they create malicious code/software called malware Designed to damage, destroy, or deny service to the target systems ...
Computer Networking and Security
... The course provides an introduction to the computer hardware and software skills as well as introductory networking skills needed to help meet the growing demand for entry-level information and communication technology (ICT) professionals. The curriculum covers the fundamentals of PC technology and ...
... The course provides an introduction to the computer hardware and software skills as well as introductory networking skills needed to help meet the growing demand for entry-level information and communication technology (ICT) professionals. The curriculum covers the fundamentals of PC technology and ...
Shawn Bracken - CISSP103 Chester StMenlo Park, CA 94025
... 2003 to Present, Principal Product Architect, HBGary, Inc., Sunnyvale, CA. Designed and implemented a cyber warfare platform called Predator Made major development contributions to a reverse engineering management system called Inspector. Oversee multiple projects and serve as a technical reso ...
... 2003 to Present, Principal Product Architect, HBGary, Inc., Sunnyvale, CA. Designed and implemented a cyber warfare platform called Predator Made major development contributions to a reverse engineering management system called Inspector. Oversee multiple projects and serve as a technical reso ...
Document
... A computer virus is a specific type of malicious computer code that replicates itself or inserts copies or new versions of itself in other programs. Worm Worms are parasitic computer programs that replicate, but unlike viruses, do not infect other computer program files. Worms can create copies on ...
... A computer virus is a specific type of malicious computer code that replicates itself or inserts copies or new versions of itself in other programs. Worm Worms are parasitic computer programs that replicate, but unlike viruses, do not infect other computer program files. Worms can create copies on ...
CIS 203 Artificial Intelligence
... implementation. With that being said, Network Security is a very important topic and extremely practical. Fortune 500 companies and other large companies rely heavily on Network Security to protect their confidential information and also to keep their computer networks from failing. A poor network s ...
... implementation. With that being said, Network Security is a very important topic and extremely practical. Fortune 500 companies and other large companies rely heavily on Network Security to protect their confidential information and also to keep their computer networks from failing. A poor network s ...
ISEC0511
... application can also be considered as part of the accounting information. These files need security so that adversaries cannot tamper or delete them. ...
... application can also be considered as part of the accounting information. These files need security so that adversaries cannot tamper or delete them. ...
Chapter 10: Electronic Commerce Security
... Often security slows down processors and adds significantly to data storage demands. Too much security can harm profitability; not enough can mean going out of business. ...
... Often security slows down processors and adds significantly to data storage demands. Too much security can harm profitability; not enough can mean going out of business. ...
Chap 3
... Web spoofing TCP session hijacking Information theft Other attacks (denial-of-service attacks, corruption of transmitted data, traffic analysis to gain information about victim’s network) ...
... Web spoofing TCP session hijacking Information theft Other attacks (denial-of-service attacks, corruption of transmitted data, traffic analysis to gain information about victim’s network) ...
Title of Subject
... Under the statute a “protected computer” is any PC attached to the Internet that is used to access files at financial institutions, the U.S. government, or a PC used in interstate commerce. A criminal act against a “protected computer” is the sending of code that causes damage, trafficking in passwo ...
... Under the statute a “protected computer” is any PC attached to the Internet that is used to access files at financial institutions, the U.S. government, or a PC used in interstate commerce. A criminal act against a “protected computer” is the sending of code that causes damage, trafficking in passwo ...