18_DataCenter_Security_Overview
... •Eavesdropping - is the unauthorized interception of information that travels on the network, this information might contain confidential data such as username and password. Another example is packet capturing. •Viruses & Worms – both cases of malicious code, hidden in the system until the damage is ...
... •Eavesdropping - is the unauthorized interception of information that travels on the network, this information might contain confidential data such as username and password. Another example is packet capturing. •Viruses & Worms – both cases of malicious code, hidden in the system until the damage is ...
Security
... 1. Something the user knows 2. Something the user has 3. Something the user is This is done before user can use the system ...
... 1. Something the user knows 2. Something the user has 3. Something the user is This is done before user can use the system ...
ppt
... • Goal – limit attacker’s possibilities by creating layers of hindrance (e.g. access) • Administrative controls should be part of security policy ...
... • Goal – limit attacker’s possibilities by creating layers of hindrance (e.g. access) • Administrative controls should be part of security policy ...
INFORMATION SYSTEMS ENGINEERING
... foundation courses with the same number of other graduate courses and may take these courses after all remaining foundation course requirements have been satisfied. ...
... foundation courses with the same number of other graduate courses and may take these courses after all remaining foundation course requirements have been satisfied. ...
Slides
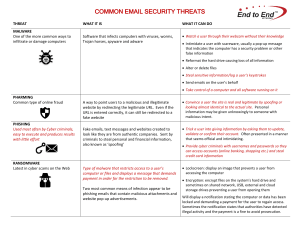
... • triggered when user opens attachment • or worse even when mail viewed by using scripting features in mail agent • usually targeted at Microsoft Outlook mail ...
... • triggered when user opens attachment • or worse even when mail viewed by using scripting features in mail agent • usually targeted at Microsoft Outlook mail ...
E-Commerce Technology Risk and Security
... The cyber thieves obtained the banking account credentials through a phishing email sent to an employee at EMI. The transactions wired funds to bank accounts in Russia, Estonia, Scotland, Finland, China and the US and were withdrawn soon after the deposits were made. Alleges Comerica's security prac ...
... The cyber thieves obtained the banking account credentials through a phishing email sent to an employee at EMI. The transactions wired funds to bank accounts in Russia, Estonia, Scotland, Finland, China and the US and were withdrawn soon after the deposits were made. Alleges Comerica's security prac ...
Information Security in the New Millennium
... Those measures, procedures, or controls which provide an ...
... Those measures, procedures, or controls which provide an ...
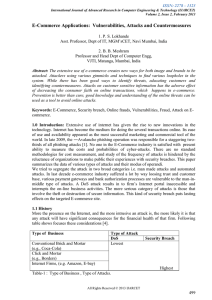
Survey of online attacks on E-Commerce sites
... server or application server products that serve the static and dynamic aspects of the site. Buffer overflows generally resulted in to crashes. Other type of attacks will create the situation like lack of availability are possible, including putting the program into an infinite loop [7]. 2.3 Log For ...
... server or application server products that serve the static and dynamic aspects of the site. Buffer overflows generally resulted in to crashes. Other type of attacks will create the situation like lack of availability are possible, including putting the program into an infinite loop [7]. 2.3 Log For ...
Darktrace Case Study: Human Longevity, Medical Technology
... Given this strategy, Human Longevity decided to trial Darktrace’s Enterprise Immune System, a new approach, inspired by the human immune system. Using machine learning and developed by mathematicians from the University of Cambridge, it establishes a ‘pattern of life’ by analyzing normal behaviors a ...
... Given this strategy, Human Longevity decided to trial Darktrace’s Enterprise Immune System, a new approach, inspired by the human immune system. Using machine learning and developed by mathematicians from the University of Cambridge, it establishes a ‘pattern of life’ by analyzing normal behaviors a ...
Department of Homeland Security
... Safeguard and Secure Cyperspace The Department has the lead for the federal government for securing civilian government computer systems, and works with industry and state, local, tribal and territorial governments to secure critical infrastructure and information systems. The Department works to: ...
... Safeguard and Secure Cyperspace The Department has the lead for the federal government for securing civilian government computer systems, and works with industry and state, local, tribal and territorial governments to secure critical infrastructure and information systems. The Department works to: ...
Siveillance Vantage
... contains general descriptions and/or performance features which may not always specifically reflect those described, or which may undergo modification in the course of further development of the products. The requested performance features are binding only when they are expressly agreed upon in the ...
... contains general descriptions and/or performance features which may not always specifically reflect those described, or which may undergo modification in the course of further development of the products. The requested performance features are binding only when they are expressly agreed upon in the ...
Principal Security Engineer– PAE4IT A. PRIMARY ROLE Working
... Working independently, performs highest level analysis of complicated and disparate technical and data architectures by applying highly specialized training and experiences to identify and rectify technical and information security vulnerabilities. Provides technical leadership on matters of securit ...
... Working independently, performs highest level analysis of complicated and disparate technical and data architectures by applying highly specialized training and experiences to identify and rectify technical and information security vulnerabilities. Provides technical leadership on matters of securit ...
Slide 1
... Security and performance are tightly coupled concepts Network performance is an asset that needs protection ...
... Security and performance are tightly coupled concepts Network performance is an asset that needs protection ...
coms3995 - Computer Science, Columbia University
... • You will be assigned a particular CLIC machine for virtual machine use • Some CLIC machines are for in-person use; others can only be accessed remotely • No food or drink in CLIC – be considerate -- others are trying to concentrate ...
... • You will be assigned a particular CLIC machine for virtual machine use • Some CLIC machines are for in-person use; others can only be accessed remotely • No food or drink in CLIC – be considerate -- others are trying to concentrate ...
Incident Response and Honeypots
... • Problem: if defenders do not know what attacker is after, reduced protection domain may contain what the attacker is after. – Stoll created document that attacker d/led. – Download took several hours, during which the phone call was traced to Germany. ...
... • Problem: if defenders do not know what attacker is after, reduced protection domain may contain what the attacker is after. – Stoll created document that attacker d/led. – Download took several hours, during which the phone call was traced to Germany. ...
Bandura® Releases REACT™ Software to Integrate Internal
... ST. LOUIS (MARCH 24, 2015) – Bandura, LLC, manufacturer of the U.S. Defense‐tested PoliWall cyber security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providin ...
... ST. LOUIS (MARCH 24, 2015) – Bandura, LLC, manufacturer of the U.S. Defense‐tested PoliWall cyber security technology, today introduced the REACT™ software product that allows customers to integrate real‐time threat information from their own network into the PoliWall® security appliance, providin ...
Curriculum Vitae - ASU People Search
... Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and P ...
... Implemented Automated and Precise Cross Site Script (XSS) generator for Web Application testing in python. Simulated malicious web server client to identify vulnerabilities in code of python based Web Server. Solved catch the flag challenges including directory traversal, buffer overflow and P ...
Cybersecurity for Critical Control Systems in the Power Industry
... PLC code ultimately leads to the destruction of the controlled equipment; the malware is so sophisticated that an operator sitting at the Human Machine Interface (HMI) will not notice the changes at the ...
... PLC code ultimately leads to the destruction of the controlled equipment; the malware is so sophisticated that an operator sitting at the Human Machine Interface (HMI) will not notice the changes at the ...
The United States Secret Service - Federal Reserve Bank of San
... Strong documentation and reporting practices starting at the beginning of the incident. Internal computer forensics and log analysis. Technical briefings for law enforcement during the entire course of the investigation. Contingency planning to bring operations back on ...
... Strong documentation and reporting practices starting at the beginning of the incident. Internal computer forensics and log analysis. Technical briefings for law enforcement during the entire course of the investigation. Contingency planning to bring operations back on ...
Distributed and Embedded Systems (DIES)
... (9) The Caller-ID feature of the Phone system used to inform the recipient of a telephone call who is calling; (10) An Audit log used to collect relevant operational data that can be analyzed when there is an incident; (11) An ISP used to assist its clients in using the information super highway res ...
... (9) The Caller-ID feature of the Phone system used to inform the recipient of a telephone call who is calling; (10) An Audit log used to collect relevant operational data that can be analyzed when there is an incident; (11) An ISP used to assist its clients in using the information super highway res ...
SMALL FIRMS CYBERSECURITY GUIDANCE
... internet such as smartphones, email, social media, and cloud computing services in an effort to increase efficiency and revenues. Through this dependence they become larger targets for cybercriminals looking to exploit technological vulnerabilities. Cybersecurity firm Symantec reports that in 2012, ...
... internet such as smartphones, email, social media, and cloud computing services in an effort to increase efficiency and revenues. Through this dependence they become larger targets for cybercriminals looking to exploit technological vulnerabilities. Cybersecurity firm Symantec reports that in 2012, ...
Intrusion Prevention Systems
... intrusion detection process. The primary responsibility of an IDS is to detect unwanted and malicious activities. • Intrusion prevention system (IPS): is software that has all the capabilities of an intrusion detection system and can also attempt to stop possible incidents. ...
... intrusion detection process. The primary responsibility of an IDS is to detect unwanted and malicious activities. • Intrusion prevention system (IPS): is software that has all the capabilities of an intrusion detection system and can also attempt to stop possible incidents. ...
Computer replacement
... means that spare parts, updates and upgrades are built into the service agreement. Replacing the components that needs to be replaced at the right time. Tailored to suit the specific needs of our customers, and a balance between spareparts, updates, and upgrades. Evergreen Updates is divided into fo ...
... means that spare parts, updates and upgrades are built into the service agreement. Replacing the components that needs to be replaced at the right time. Tailored to suit the specific needs of our customers, and a balance between spareparts, updates, and upgrades. Evergreen Updates is divided into fo ...