Securing the Network - Austin Community College
... Security is a fundamental component of every network design. When planning, building, and operating a network, you should understand the importance of a strong security policy. How important is it to have a strong network security policy? The application of an effective security policy is the most i ...
... Security is a fundamental component of every network design. When planning, building, and operating a network, you should understand the importance of a strong security policy. How important is it to have a strong network security policy? The application of an effective security policy is the most i ...
General Assembly 1 Background Guide
... attacks against the United States or to directly to launch an attack. Cyber-attacks may specifically target computer and cyber networks to release sensitive information or disrupt essential infrastructure. For example, in 2010, an attack code virus directed against a uranium-processing facility in I ...
... attacks against the United States or to directly to launch an attack. Cyber-attacks may specifically target computer and cyber networks to release sensitive information or disrupt essential infrastructure. For example, in 2010, an attack code virus directed against a uranium-processing facility in I ...
Faculty of Correspondence, Evening and Distance
... Today BSUIR is a large scientific and educational center in Belarus. It has highly qualified staff, considerable scientific and methodological potential, advanced laboratory and informational infrastructure, all necessary conditions to organize teaching and educational process, scientific research, ...
... Today BSUIR is a large scientific and educational center in Belarus. It has highly qualified staff, considerable scientific and methodological potential, advanced laboratory and informational infrastructure, all necessary conditions to organize teaching and educational process, scientific research, ...
Key To Personal Information Security
... DoS - Viruses/Worms • Viruses or worms, which replicate across a network in various ways, can be viewed as denial-of-service attacks where the victim is not usually specifically targeted but simply a host unlucky enough to get the virus. • Available bandwidth can become saturated as the virus/worm ...
... DoS - Viruses/Worms • Viruses or worms, which replicate across a network in various ways, can be viewed as denial-of-service attacks where the victim is not usually specifically targeted but simply a host unlucky enough to get the virus. • Available bandwidth can become saturated as the virus/worm ...
12_hSecurityRequirements
... requirements (confidentiality, data integrity and availability). Description of threats to network security in terms of passive (monitoring of transmission) and active (modification of the data stream or the creation of a false stream) attacks. ...
... requirements (confidentiality, data integrity and availability). Description of threats to network security in terms of passive (monitoring of transmission) and active (modification of the data stream or the creation of a false stream) attacks. ...
Lect 1 - Intro
... features on your system, which allows it to travel unaided. The biggest danger with a worm is its capability to replicate itself on your system (e.g., sending itself to all of the e-mail list in your computer) Trojan horse: A program that at first glance will appear to be useful software but will a ...
... features on your system, which allows it to travel unaided. The biggest danger with a worm is its capability to replicate itself on your system (e.g., sending itself to all of the e-mail list in your computer) Trojan horse: A program that at first glance will appear to be useful software but will a ...
Document
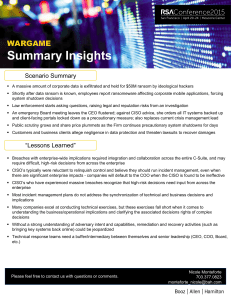
... cybersecurity professional and inform them that their machine is generating copious beacons – Panic ensues! • Instead, approach reporting in a nonjudgemental, diplomatic manner • Provide proof of your findings – It will certainly be requested ...
... cybersecurity professional and inform them that their machine is generating copious beacons – Panic ensues! • Instead, approach reporting in a nonjudgemental, diplomatic manner • Provide proof of your findings – It will certainly be requested ...
Building an in-depth defense with Vectra and sandbox security
... command-and-control (C&C) servers that the attacker uses to remotely control each phase of the cyber attack. The attacker uses the C&C servers to send commands to and receive responses from hosts under his control as a result of downloading the exploit. Cyber attacks that are targeted differ from bo ...
... command-and-control (C&C) servers that the attacker uses to remotely control each phase of the cyber attack. The attacker uses the C&C servers to send commands to and receive responses from hosts under his control as a result of downloading the exploit. Cyber attacks that are targeted differ from bo ...
Cybersecurity for Asset Managers: Shielding Your Firm
... while reducing financial loss, customer harm and reputational damage. Businesses with cyber resiliencies in place have several characteristics in common: • Secure processes and systems • Strong controls with a strong control environment • Digitized and automated processes • An aggressive, proact ...
... while reducing financial loss, customer harm and reputational damage. Businesses with cyber resiliencies in place have several characteristics in common: • Secure processes and systems • Strong controls with a strong control environment • Digitized and automated processes • An aggressive, proact ...
17 September 2015
... Education – both in terms of businesses’ understanding of exposures and underwriting knowledge – must improve if insurers are to meet growing demand. In addition, as with any other emerging risk, insurers also face challenges around pricing, untested policy wordings, modelling and risk accumulation ...
... Education – both in terms of businesses’ understanding of exposures and underwriting knowledge – must improve if insurers are to meet growing demand. In addition, as with any other emerging risk, insurers also face challenges around pricing, untested policy wordings, modelling and risk accumulation ...
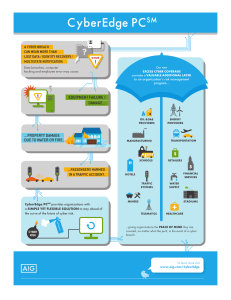
PDF Product Profile CyberEdge PC Overview
... cybersecurity failure. Where underlying insurance has cyber coverage gaps, CyberEdge PC’s difference-in-conditions features can fill in those gaps, and help organizations get the cyber risk protection they need. Additional Layer of Protection • Adds capacity above existing insurance programs solely ...
... cybersecurity failure. Where underlying insurance has cyber coverage gaps, CyberEdge PC’s difference-in-conditions features can fill in those gaps, and help organizations get the cyber risk protection they need. Additional Layer of Protection • Adds capacity above existing insurance programs solely ...
INTRODUCTION
... These challenges notwithstanding, governments should in the case of the idealists, fight them through education not law. It has been proven that they help big companies and government see security holes which career criminals or even cyber-terrorist could use to attack them in future. Most often, co ...
... These challenges notwithstanding, governments should in the case of the idealists, fight them through education not law. It has been proven that they help big companies and government see security holes which career criminals or even cyber-terrorist could use to attack them in future. Most often, co ...
slides - University of Cambridge Computer Laboratory
... • Auditing firms will follow old formulae until something compels change • But should the government regulate (as with NERC/FERC) or facilitate (as the UK)? • See ‘Security Economics and Critical National Infrastructure’, on my web page, and at the Workshop on the Economics of Information Security, ...
... • Auditing firms will follow old formulae until something compels change • But should the government regulate (as with NERC/FERC) or facilitate (as the UK)? • See ‘Security Economics and Critical National Infrastructure’, on my web page, and at the Workshop on the Economics of Information Security, ...
Introduction to management of Information Technologies
... 1) Distinguish between Tear-drop and ping-of-death attacks. 2) What is an illicit content attack? What is the difference between a virus, a worm, and a Trojan horse? How could a stand-alone computer or a network be a victim of an illicit content attack? 3) What is an Open Mail server? How could you ...
... 1) Distinguish between Tear-drop and ping-of-death attacks. 2) What is an illicit content attack? What is the difference between a virus, a worm, and a Trojan horse? How could a stand-alone computer or a network be a victim of an illicit content attack? 3) What is an Open Mail server? How could you ...
Computer GEEK - Ideas
... If it is at all possible, it is best to catch small problems before they become large problems. Systems are monitored for possible problems with storage, viruses, and security. ...
... If it is at all possible, it is best to catch small problems before they become large problems. Systems are monitored for possible problems with storage, viruses, and security. ...
Slide 1 - IITK - Indian Institute of Technology Kanpur
... • Section 66 of Information Technology Act:Whoever with the intent to cause or knowing that he is likely to cause wrongful loss or damage to the public or any person, destroys or deletes or alters any information residing in a computer resource or diminishes its value or utility or affects it injuri ...
... • Section 66 of Information Technology Act:Whoever with the intent to cause or knowing that he is likely to cause wrongful loss or damage to the public or any person, destroys or deletes or alters any information residing in a computer resource or diminishes its value or utility or affects it injuri ...
security_6
... It is a computer program that protects a computer or network from unauthorized access by hackers. ...
... It is a computer program that protects a computer or network from unauthorized access by hackers. ...
Insider Threat and the Dark Web: Cyber Response Mini
... managing the technical response, responding to massive incidents requires synchronizing business, legal, communications, as well as technical activities. Most companies would benefit from a pre-defined and dedicated Crisis Management Executive that has a broad enterprise view of the organization and ...
... managing the technical response, responding to massive incidents requires synchronizing business, legal, communications, as well as technical activities. Most companies would benefit from a pre-defined and dedicated Crisis Management Executive that has a broad enterprise view of the organization and ...
Open resource
... collaboration between industry and government, consists of standards, guidelines, and practices to promote the protection of critical infrastructure The prioritized, flexible, repeatable, and cost-effective approach of the Framework helps owners and operators of critical infrastructure to manage c ...
... collaboration between industry and government, consists of standards, guidelines, and practices to promote the protection of critical infrastructure The prioritized, flexible, repeatable, and cost-effective approach of the Framework helps owners and operators of critical infrastructure to manage c ...
Information Security - National University of Sciences and
... • Using large number of zombies, a person can send thousands of requests to web-Server effectively making it unavailable for legitimate users • Attack on availability ...
... • Using large number of zombies, a person can send thousands of requests to web-Server effectively making it unavailable for legitimate users • Attack on availability ...
D efe ns iv
... sophisticated backdoor techniques. Students will depart this course with an understanding of advanced techniques used by the most sophisticated attackers to maintain stealth and security while minimizing their footprint and identity. Locating the Cyber Ninja ...
... sophisticated backdoor techniques. Students will depart this course with an understanding of advanced techniques used by the most sophisticated attackers to maintain stealth and security while minimizing their footprint and identity. Locating the Cyber Ninja ...
Computer Systems Security
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...
... Originally, backdoors were used by developers as a legitimate way of accessing an application, but soon after they were implemented by attackers who would use backdoors to make changes to operating systems, websites, and network devices Quite often, it is installed via a Trojan horse ...