BIO-ELECTRO-INFO TECHNOLOGIES TO COMBAT TERRORISM
... when the U.S. would use cyber attacks, who would authorize it, what constitutes legitimate targets, and what kinds of attacks -- Denial of Service, hacking, worms -- could be used. ...
... when the U.S. would use cyber attacks, who would authorize it, what constitutes legitimate targets, and what kinds of attacks -- Denial of Service, hacking, worms -- could be used. ...
Why Cryptography is Harder Than It Looks
... – Motivation of attackers • Vast knowledge and free time • Few financial resources and / or vendetta ...
... – Motivation of attackers • Vast knowledge and free time • Few financial resources and / or vendetta ...
Junior Enlisted - Cyber Security
... and hardening overall network security posture of the Marine Corps by installing, configuring and maintaining software ...
... and hardening overall network security posture of the Marine Corps by installing, configuring and maintaining software ...
Chapter 2: Attackers and Their Attacks
... the network and computer infrastructure to cause panic Cyberterrorists’ motivation may be defined as ideology, or attacking for the sake of their principles or beliefs Targets that are high on the cyberterrorists list are: ...
... the network and computer infrastructure to cause panic Cyberterrorists’ motivation may be defined as ideology, or attacking for the sake of their principles or beliefs Targets that are high on the cyberterrorists list are: ...
SANDS CORP CYBER JOB
... cyber security program. This role is an entry level analyst that is responsible for monitoring various cyber security appliances to identify events that require escalated analysis. The SOC cyber security analyst, Level 1 reports to the Director of the US Security Operations Center. ...
... cyber security program. This role is an entry level analyst that is responsible for monitoring various cyber security appliances to identify events that require escalated analysis. The SOC cyber security analyst, Level 1 reports to the Director of the US Security Operations Center. ...
Neal Ziring Very Short Bio
... Mr. Neal Ziring is the Technical Director for the National Security Agency’s Capabilities Directorate, serving as a technical advisor to the Capabilities Director, Deputy Director, and other senior leadership. Mr. Ziring is responsible for setting the technical direction across many parts of the cap ...
... Mr. Neal Ziring is the Technical Director for the National Security Agency’s Capabilities Directorate, serving as a technical advisor to the Capabilities Director, Deputy Director, and other senior leadership. Mr. Ziring is responsible for setting the technical direction across many parts of the cap ...
chapter 5 – basic security
... Spam is a serious network threat that can overload ISPs, email servers and individual enduser systems. A person or organization responsible for sending spam is called a spammer. Spammers often make use of unsecured email servers to forward email. Spammers can use hacking techniques, such as vir ...
... Spam is a serious network threat that can overload ISPs, email servers and individual enduser systems. A person or organization responsible for sending spam is called a spammer. Spammers often make use of unsecured email servers to forward email. Spammers can use hacking techniques, such as vir ...
Malicious Cryptography : Exposing Cryptovirology
... Foreword Terms such as cryptovirology, malware, kleptogram, or kleptography may be unfamiliar to the reader, but the basic concepts associated with them certainly are familiar. Everyone knows—often from sad experience—about viruses, Trojan horses, and worms and many have had a password “harvested” b ...
... Foreword Terms such as cryptovirology, malware, kleptogram, or kleptography may be unfamiliar to the reader, but the basic concepts associated with them certainly are familiar. Everyone knows—often from sad experience—about viruses, Trojan horses, and worms and many have had a password “harvested” b ...
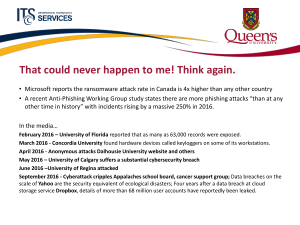
Cybersecurity - Queen`s Wiki
... That could never happen to me! Think again. • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in ...
... That could never happen to me! Think again. • Microsoft reports the ransomware attack rate in Canada is 4x higher than any other country • A recent Anti-Phishing Working Group study states there are more phishing attacks “than at any other time in history” with incidents rising by a massive 250% in ...
Power Point Slides - Organization of American States
... •Goal 1: Strengthen understanding of managerial officials at critical infrastructures of threats and mitigation strategies •Goal 2: Teach technicians and security engineers techniques to protection critical networks in the event of a national disaster ...
... •Goal 1: Strengthen understanding of managerial officials at critical infrastructures of threats and mitigation strategies •Goal 2: Teach technicians and security engineers techniques to protection critical networks in the event of a national disaster ...
john p. carlin - AFCEA International
... Mr. Carlin is an inaugural fellow of Harvard Kennedy School’s Belfer Center for Science and International Affairs’ Homeland Security Project, focused on the unique challenges and choices around protecting the American homeland. He also chairs the Aspen Institute’s Cybersecurity and Technology policy ...
... Mr. Carlin is an inaugural fellow of Harvard Kennedy School’s Belfer Center for Science and International Affairs’ Homeland Security Project, focused on the unique challenges and choices around protecting the American homeland. He also chairs the Aspen Institute’s Cybersecurity and Technology policy ...
Cyber Challenges
... • Perceived high cost with low benefit • A highly interactive environment • More powerful computing devices ...
... • Perceived high cost with low benefit • A highly interactive environment • More powerful computing devices ...
IEEE CONFERENCE ON COMMUNICATION TECHNOLOGIES
... planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Conference Co-Chair: Dr.Asif Masood DEADLINES ...
... planning to hold an International Conference on Communications Technologies (ComTech-2017), at its campus, in collaboration with IEEE and related industrial partners in April 2017. Conference Chair Dr.Abdul Rauf Conference Co-Chair: Dr.Asif Masood DEADLINES ...
INTRODUCTION TO INFORMATION SYSTEMS TECHNOLOGY
... A cracker is an intruder who breaks into a computer system to cause damage and/or to steal information ...
... A cracker is an intruder who breaks into a computer system to cause damage and/or to steal information ...
Attivo Networks Deception Platform Integrates with the Check Point
... and the resources needed to identify, block, and remediate threats inside the network. ...
... and the resources needed to identify, block, and remediate threats inside the network. ...
SE 4C03 Winter 2004
... Black hats are very skilled crackers who are not easily caught. They possess extensive knowledge in technology and use them to find more vulnerability of systems. White hats, on the other hand, use their skills in attacking computer systems and networks to improve existing defensive measures. System ...
... Black hats are very skilled crackers who are not easily caught. They possess extensive knowledge in technology and use them to find more vulnerability of systems. White hats, on the other hand, use their skills in attacking computer systems and networks to improve existing defensive measures. System ...
Beyond Data Breach Cyber Trends and Exposures â Mr. Jason Kelly
... Cyber threats are a growing concern for all companies ...
... Cyber threats are a growing concern for all companies ...
Cyber Risks of Manufacturers Limiting the Risk Factors of
... Recently, hackers have found ways to disrupt manufacturers’ daily operations by infiltrating their computer systems and taking control of manufacturing machinery. These attacks can result in property damage and can substantially interrupt supply chains. ...
... Recently, hackers have found ways to disrupt manufacturers’ daily operations by infiltrating their computer systems and taking control of manufacturing machinery. These attacks can result in property damage and can substantially interrupt supply chains. ...
file - ScholarSphere
... external intruders, and from both intentional or accidental disclosure or destruction? While network administrators take great pains to protect their networks from intruders from the outside, they frequently ignore or are unaware of the advantages possessed by intruders on the inside: Insiders have ...
... external intruders, and from both intentional or accidental disclosure or destruction? While network administrators take great pains to protect their networks from intruders from the outside, they frequently ignore or are unaware of the advantages possessed by intruders on the inside: Insiders have ...
attacks
... to compromise a controlled system. Accomplished by a threat agent that damages or steals information or ...
... to compromise a controlled system. Accomplished by a threat agent that damages or steals information or ...
Babu Madhav Institute of Information Technology, UTU 2017
... with respect to specific topic or subjects. 13. When a criminal uses someone else’s identity for his/her own illegal purposes is known as _______________. 14. ___________________ is the art of breaking into phone or other communication systems. 15. The goal of crimes targeted at individuals is to ex ...
... with respect to specific topic or subjects. 13. When a criminal uses someone else’s identity for his/her own illegal purposes is known as _______________. 14. ___________________ is the art of breaking into phone or other communication systems. 15. The goal of crimes targeted at individuals is to ex ...